
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
Prof


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
Prof
Raut D.B.1 , Harshada Gawade 2 , Jaydip Pawar3, Chandrakant Kumbhar4,Balu Gorad5
1Professor,Department of Computer Science, SVPM’s College Of Engineering, Malegaon(BK),Maharashtra, India 2,3,4,5Student,Department Of Computer Science, SVPM’s College Of Engineering, Malegaon(BK),Maharashtra, India
Abstract - This project presents a secure video steganographysystemcombiningAESencryptionandLSB substitution to hide messages in video frames. In the encoding phase, a secret message is encrypted using AES andembeddedintoaselectedframeusingLSB.Themodified frames generate a stego video. In the decoding phase, the encryptedmessageisextractedanddecryptedtorevealthe original text. This method ensures high security, imperceptibility,androbustness,makingitusefulforsecure communication, digital forensics, and watermarking. The system is implemented as a Tkinter-based desktop applicationforeasyuse.
Key Words: videosteganographysystem,AESencryption, encodingphase,imperceptibility,robustness,secretmessage
With the growing need for secure communication, video steganography offers an effective way to hide data within videos. This project combines Least Significant Bit (LSB) substitutionforembeddingmessagesandAESencryptionfor enhancedsecurity.
Intheencodingphase,asecretmessageisencryptedusing AESandembeddedintovideoframesusingLSB,generatinga stegovideo.Inthedecodingphase,theencryptedmessageis extracted and decrypted to reveal the original text. This method ensures high security, imperceptibility, and robustness, making it useful for secure communication, militaryapplications,anddigitalwatermarking.Thesystem isimplementedasaTkinter-baseddesktopapplicationfor easeofuse.
Secure Communication – Enables covert messagingbyhidingconfidentialdatainsidevideos topreventunauthorizedaccess.
Data Protection – Ensures sensitive information remains undetectable, reducing the risk of cyber threatsanddataleaks.
Avoiding Detection – Unlike encryption, which makes data unreadable but noticeable, steganography hides the existence ofdataitself.
Digital Watermarking – Protects intellectual property by embedding invisible watermarks in videostoverifyauthenticityandpreventpiracy.
Forensics & Intelligence –Usedin cybersecurity, military, and intelligence to hide critical data duringinvestigationsandsecuremissions.
Medical Data Security – Embeds confidential medicalrecordswithindiagnosticvideos,ensuring privacyintelemedicineapplications.
Secure Communication – Enables covert messagingbyhidingconfidentialdatainsidevideos topreventunauthorizedaccess.
Data Protection – Ensures sensitive information remains undetectable, reducing the risk of cyber threatsanddataleaks.
Avoiding Detection – Unlike encryption, which makes data unreadable but noticeable, steganography hides the existence ofdataitself.
Digital Watermarking – Protects intellectual property by embedding invisible watermarks in videostoverifyauthenticityandpreventpiracy.
Forensics & Intelligence –Usedin cybersecurity, military, and intelligence to hide critical data duringinvestigationsandsecuremissions.
Medical Data Security – Embeds confidential medicalrecordswithindiagnosticvideos,ensuring privacyintelemedicineapplications.
Withincreasingcybersecuritythreats,videosteganography provides a secure method for concealing sensitive data within digital media. It enables covert communication, ensuring privacy in military, intelligence, and journalism. Additionally,itplaysacrucialrolein digital watermarking to protect copyright and prevent piracy. As cyber-attacks and surveillance rise, advancements in steganographic techniques offer enhanced security solutions for data protection.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
To develop a secure and efficient method for hiding confidentialdatawithinvideofiles.
To integrate AES encryption with LSB-based steganography forenhancedsecurity.
To ensure data integrity and confidentiality by preventingunauthorizedaccess.
Tominimize visual distortion inthestego-videowhile maximizingembeddingcapacity.
To make the steganographic process resistant to steganalysis and cyber-attacks
To facilitate secure communication in sensitive domainslikemilitary,intelligence,anddigitalforensics.
The methodology for this video steganography project is divided into three main stages: data encryption, data embedding,anddataextraction.Eachstageisimplemented withacombinationofPythonprogrammingandtheTkinter library for interface design, providing users with a streamlinedprocessforsecurelyembeddingandretrieving hiddenmessagesinvideofiles.
Thefirststepinvolvessecuringthemessagetobehiddenby encryptingitwiththeAdvancedEncryptionStandard(AES) algorithm.AESisasymmetricencryptiontechniqueknown for its high security and efficiency, making it suitable for sensitivedataprotection.Theprocessisasfollows:
The user inputs a secret message and a secure key (password).
AESencryptionisappliedtoconverttheplaintextmessage intociphertext,producinganencryptedformofthemessage thatisunreadablewithoutthedecryptionkey.
Thisencryptedmessage(ciphertext)isthenpreparedfor embeddinginthevideo.
Afterencryption,theciphertextisembeddedintoselected framesofthevideofileusingtheLeastSignificantBit(LSB) technique:
The video is divided into frames, and each frame is representedasaseriesofpixelvalues.
Foreachpixel,theleastsignificantbitofthecolorchannels (typicallyred,green,orblue)isreplacedwithabitfromthe encryptedmessage.
Thisprocessisrepeatedacrossframesandpixelchannels until the entire message has been embedded. The LSB method ensures minimal alteration to the pixel values, preservingthevisual qualityofthevideoandkeepingthe hiddenmessageimperceptibletoviewers.
The modified video frames are then recombined to produce the steganographic video with the embedded, encryptedmessage.
To retrieve the hidden message, the following steps are performed:
The user provides the steganographic video file and the decryptionkey.
Theprogramreadseachframeofthevideoandextractsthe leastsignificantbitsfromtheselectedpixelstoreconstruct theembeddedciphertext.
Once the entire encrypted message is extracted, AES decryptionisappliedusingtheprovidedkeytoconvertthe ciphertextbacktoplaintext.
The original message is then displayed to the user, providedthecorrectdecryptionkeywasentered
1. AES Encryption & Decryption
Encrypt the secret message usingAES-256.
Decrypt the message afterextractionfromthe video.
2. LSB (Least Significant Bit) Encoding & Decoding
Convert message to binary.
Modify the least significant bit of pixel values tostoreencrypteddata.
Extract and reconstruct the binary message fromvideoframes.
3. Frame Processing
Extract frames from the video forembedding.
Modify specific pixels to hide data
Reconstructthe stego-video afterembedding.
Reconstructthe stego-video afterembedding.
4. User Interface (GUI)
Upload Video forembedding.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Enter Secret Message forencryptionandhiding.
Extract and Decrypt hiddenmessagefromthe stego-video.
5. Security Measures
AESencryptionensures data confidentiality.
LSBembeddingmakes hidden data undetectable.
Secure key-based access preventsunauthorized extraction.
6. BLOCK DIAGRAM
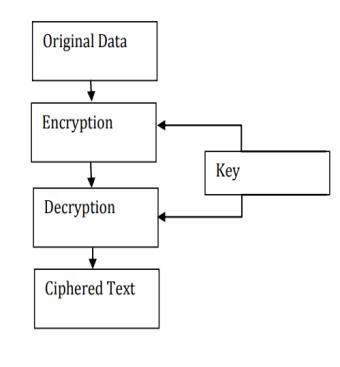
FIG.1.BLOCKDIAGRAM
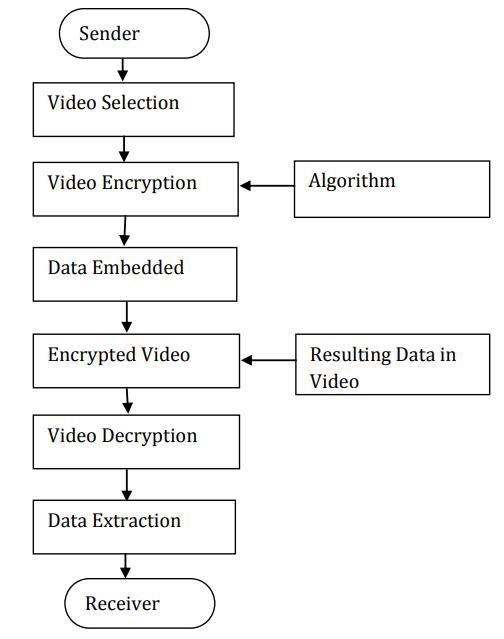
FIG.2FLOWDIAGRAM
7. SYSTEM ARCHITECTURE
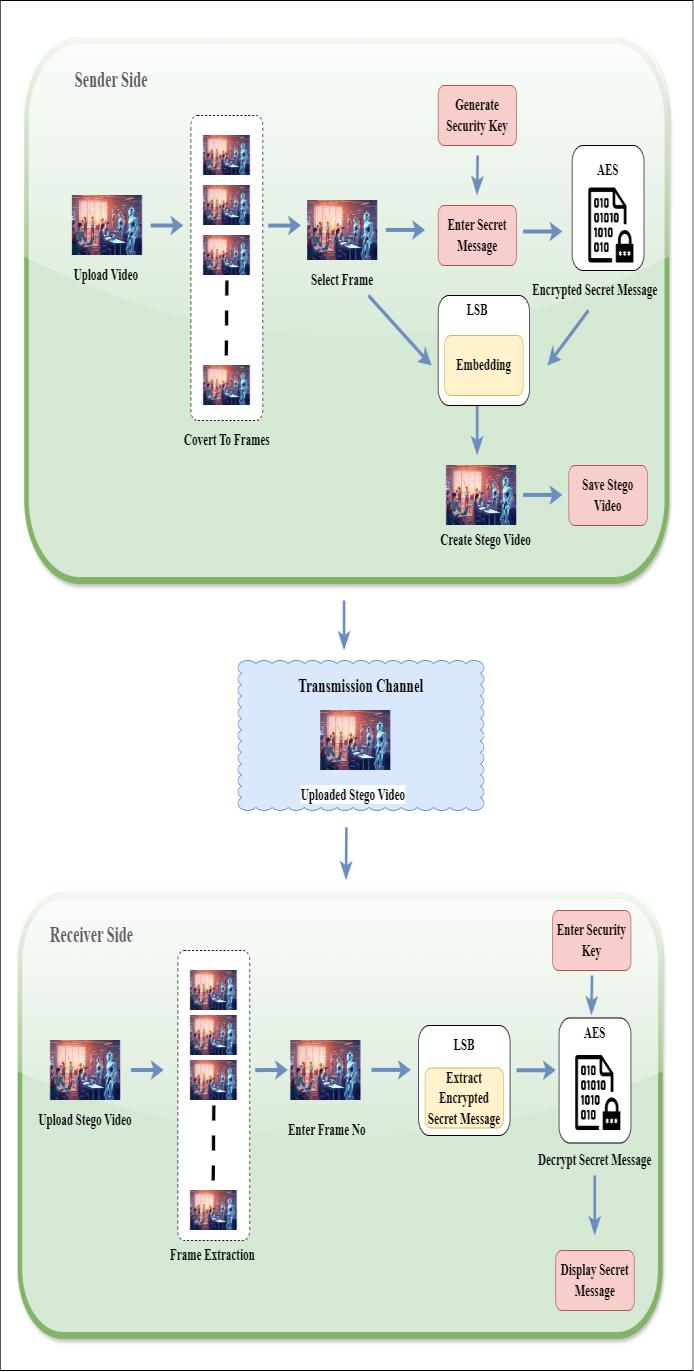
FIG.3.SYSTEMARCHITECTURE
8. RESULT
Successful Embedding – Secret message hidden withoutnoticeabledistortion.
High Security – AES encryption ensures data protection.
AccurateExtraction&Decryption –Messageretrieved anddecryptedcorrectly.
Minimal Impact on Video Quality – Stego-video appearsunchanged.
Fast Processing –Embedding&extractioncompletein 0.5 - 2 seconds
Steganalysis Resistance – Hidden data remains undetectable.
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072 © 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page1180

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
Parameter Value Example
Original Video Size 5MB(≈42 millionbits) sample_video.mp4
Secret Message Size
Encrypted Message Size
192 bits (24 bytes) "Confidential:ProjectXYZ"
256 bits (AES-256 encryption)
gH7@9sk#Lm0xYz... (Example of AES-256 ciphertext)
Security Key User-defined (AESKey) "MySecretKey123"
Stego-Video Size ≈ 5 MB (Minimal increase) stego_video.mp4
Embedding Time
0.5-2 seconds (dependson videosize)
Extraction Time 0.5 - 2 seconds
Decryption Accuracy 100% (if correctkeyis used)
9. CONCLUSION
1.2secondsfora5MBvideo
[3] M. Suresh and I. S. Sam, "Single level Discrete Wavelet Transform based Video Steganography on Horizontal and Verticalcoefficients,"20207thInternationalConferenceon SmartStructuresandSystems(ICSSS),Chennai,India,2020, pp.1-4,doi:10.1109/ICSSS49621.2020.9202110.
[4]R.BandN.MANJANAIK,"SecureVideoSteganography Technique using DWT and H.264," 2019 1st International ConferenceonAdvancesinInformationTechnology(ICAIT), Chikmagalur, India, 2019, pp. 19-23, doi: 10.1109/ICAIT47043.2019.8987403.
[5]M.A.Alia,K.A.Maria,M.A.Alsarayreh,E.A.MariaandS. Almanasra, "An Improved Video Steganography: Using Random Key-Dependent," 2019 IEEE Jordan International JointConferenceonElectricalEngineeringandInformation Technology(JEEIT),Amman,Jordan,2019,pp.234-237,doi: 10.1109/JEEIT.2019.8717368
1.1secondsfora5MBvideo
✅ Original Message: "Confidential:ProjectXYZ"
TABLE1.RESULT
Video steganography using AES encryption and LSB substitution provides a secure and efficient method for hidingsensitivedatawithinvideofiles.Byintegrating AES encryption,evenifthehiddendataisdetected,itremains protected from unauthorized access. The LSB technique ensures that the embedded data is imperceptible, maintaining the original video quality. This approach enhances data security, confidentiality, and privacy, making it useful for secure communication, digital watermarking, and cybersecurity applications. Future advancementscanfocuson improving robustnessagainst steganalysis and optimizing embedding capacity for highersecurity.
[1] N. Manohar and P. V. Kumar, "Data Encryption & Decryption Using Steganography," 2020 4th International ConferenceonIntelligentComputingand Control Systems (ICICCS), Madurai, India, 2020, pp. 697-702, doi: 10.1109/ICICCS48265.2020.9120935.
[2]K.J.VelmuruganandS.Hemavathi,"VideoSteganography by Neural Networks Using Hash Function," 2019 Fifth InternationalConferenceonScienceTechnologyEngineering andMathematics(ICONSTEM),Chennai,India,2019,pp.5558,doi:10.1109/ICONSTEM.2019.8918877.
[6]J.Wang,X.Jia,X.KangandY.-Q.Shi,"ACoverSelection HEVCVideoSteganographyBasedonIntraPredictionMode," in IEEE Access, vol. 7, pp. 119393-119402, 2019, doi: 10.1109/ACCESS.2019.2936614.
[7] R. Poovendran, M. Sangeetha, G. S. Saranya and G. Vennila,"AvideosteganographyusingHammingTechnique for image Processing using optimized algorithm," 2020 International Conference on System, Computation, AutomationandNetworking(ICSCAN),Pondicherry,India, 2020,pp.1-5,doi:10.1109/ICSCAN49426.2020.9262341.
[8] N. Kanwal et al., "Chain-of-Evidence in Secured Surveillance Videos using Steganography and Hashing," 2020IEEEIntlConfonDependable,AutonomicandSecure Computing, Intl Conf on Pervasive Intelligence and Computing,IntlConfonCloudandBigDataComputing,Intl Conf on Cyber Science and Technology Congress (DASC/PiCom/CBDCom/CyberSciTech),Calgary,AB,Canada, 2020, pp. 257-264, doi: 10.1109/DASC-PICom-CBDComCyberSciTech49142.2020.00053.
[9]R.Indrayani,"HumanPerceptionEvaluationtowardEnd of File Steganography Method’s Implementation Using Multimedia File (Image, Audio, and Video)," 2019 4th International Conference on Information Technology, InformationSystemsandElectricalEngineering(ICITISEE), Yogyakarta, Indonesia, 2019, pp. 200-204, doi: 10.1109/ICITISEE48480.2019.9003759.
[10] H. Zhao, Y. Liu, Y. Wang, S. Liu and C. Feng, "A Video SteganographyMethodBasedonTransformBlockDecision forH.265/HEVC,"inIEEEAccess,vol.9,pp.55506-55521, 2021,doi:10.1109/ACCESS.2021.3059654.
[11] S. Kumar, S. Kumar, N. K. Singh, A. Majumder and S. Changder, "A Novel Approach to Hide Text Data in Colour Image," 2018 7th International Conference on Reliability, InfocomTechnologiesandOptimization(TrendsandFuture
© 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page1181

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 03 | Mar 2025 www.irjet.net p-ISSN: 2395-0072
Directions)(ICRITO),Noida,India,2018,pp.577-581,doi: 10.1109/ICRITO.2018.8748390.
[12] S. Chavan and Y. B. Gurav, "Lossless Tagged Visual Cryptography Scheme Using Bit Plane Slicing for Image Processing," 2018 International Conference on Inventive ResearchinComputingApplications(ICIRCA),Coimbatore, India, 2018, pp. 1168-1172, doi: 10.1109/ICIRCA.2018.8596778.
© 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page1182