NITECH
A New Era of NATO Innovation


A New Era of NATO Innovation















Specializing in NATO compliant Cross Domain Solutions, infodas supports the Alliance and its members in achieving Data Centric Security and executing Multi Domain Operations.


The most comprehensive product solution on the market, for connecting security domains of different classifications, according to the highest security standards.

Holistic consulting management for complex IT systems and AI-powered efficiency improvements.
Trustworthy IT Security Consulting according to highest certification standards with comprehensive service.
For more information about infodas solutions, please scan the QR-code. INFODAS GmbH / www.infodas.com
IT/A I/ C loud ConsultingEditors Lara Vincent-Young and Simon Michell
Project Manager Andrew Howard
Editorial Director Emily Eastman
Art Direction Errol Konat
Layout Billy Odell
ISSUE 9 | JULY 2023
Contributing Photographers Marcos Fernandez Marin, Conrad Dijkstra, Francesc Nogueras Sancho
Cover Image generated by Errol Konat and the NCI Agency Creative Media team using Midjourney (Artificial Intelligence) AI generator
Printed by Pensord Press Limited
Published by
On behalf of
Chantry House, Suite 10a High Street, Billericay, Essex CM12 9BQ United Kingdom
Tel: +44 (0) 1277 655100
NATO Communications and Information (NCI) Agency
Oude Waalsdorperweg 61, 2597 AK The Hague, Netherlands
© 2023. The views and opinions, expressed by independent (non-NATO) authors, contributors and commentators in this publication, are provided in their personal capacities and are their sole responsibility. Publication thereof, does not imply that they represent the views or opinions of the NCI Agency, NATO or Global Media Partners (GMP) and must neither be regarded as constituting advice on any matter whatsoever, nor be interpreted as such. References in this publication to any company or organization, as well as their products and services, do not constitute or imply any direct or indirect endorsement, recommendation or preference by the NCI Agency, NATO or GMP. Furthermore, the reproduction of advertisements in this publication does not in any way imply endorsement by the NCI Agency, NATO or GMP of products or services referred to therein.
Objective, Responsive, and Trusted Advisor to NATO for 25 Years.*
Objective, Responsive, and Trusted Advisor to NATO for 25 Years.*
Deep analysis leads to better decisions that save money and build capabilities.
Analysis of Alternatives of Major Weapon Systems
Cost Analysis of Platforms and IT Networks
Advanced Analytics


Wargaming
DevOps and Agile
Strategic Policy and Programme Support
Integrated Programme Management
Economic Security/ Supply Chain Analysis


Forewords and introduction
11 A turning point for NATO and the NCI Agency
Ludwig Decamps, General Manager, NCI Agency

17 Innovation and the digital transformation

Manfred Boudreaux-Dehmer, Chief Information Officer, NATO
22 DIANA and the NIF – NATO’s innovation milestone
Lara Vincent-Young and Simon Michell, Co-Editors, NITECH

A new era of innovation
26 Maintaining NATO’s innovation and technology advantage

David Van Weel, Assistant Secretary General for Emerging Security Challenges, NATO
32 A new era of accelerated NATO innovation
Barbara McQuiston, Chair, NATO’s Defence Innovation Accelerator for the North Atlantic (DIANA)
38 Alliance digital transformation for multi-domain operations
Brigadier General Didier Polomé, Allied Command Transformation (ACT) Digital Transformation Champion and Special Advisor, NATO
44 Allied JFC Naples
Admiral Stuart B. Munsch, Commander of Allied Joint Force Command, Naples
48 View from the Nations: United Kingdom, accelerating NATO defence innovation
Ben Wallace, Secretary of State for Defence, United Kingdom
52 View from the Nations: the Netherlands, fostering collaboration
Kajsa Ollongren, Minister of Defence, the Netherlands
55 Emerging space, convergence is key

Justin Hodges, Business Development Lead, BT Defence
96 Farewell to Ian West
Ian West, Chief, NATO Cyber Security Centre
99 DIGITAL #OneNATO: Evolving

NATO’s Digital Workplace
Jean-Paul Massart, Chief, NATO Digital Workplace Centre
102 DigitALL: How women are influencing the future of NATO’s technology
Diana DeVivo, Political Engagement Officer, NCI Agency
Guido
Mariano


Helping to keep the world a beautiful place, Airbus provides countries with military solutions to protect their citizens, values, and vital infrastructure. With advanced technology across the domains of land, sea, air, space, and cyber, it is our mission to pioneer sustainable aerospace for a safe and united world. That’s why protecting it is at the heart of all we do, ensuring frontline personnel and entire communities get the support they need, at the time they need it most.


The past year has been a turning point for NATO, with our continued support to Ukraine in the fight against Russia’s aggression, while also making strides to further bolster the security of our future. Last year bore witness to historic decisions such as the establishment of the Defence Innovation Accelerator for the North Atlantic (DIANA) as well as invitations to Finland and Sweden to join the Alliance.
Working at NATO’s technological frontier and as enablers of Alliance interoperability, the NCI Agency has had to adapt and prepare to ensure the seamless integration of these changes and keep pace with the speed of relevance. We take great pride in our responsibility to operate on behalf of our strategic sponsors and customers in order to meet their technological needs and support their future requirements. With NATO entering into a new era, we too embark on a journey of innovation. Thus, this edition of the NATO Innovation and Technology (NITECH) magazine focuses on just that.
At the NATO Summit in Madrid in June 2022, all Allies made the historic decision to invite Finland and Sweden to join our Alliance. Finland’s historic accession was the fastest in NATO history.
The NCI Agency has been preparing to enable these nations to operate as full members of the Alliance. Our experts have been working tirelessly to provide the necessary technology, communications and information systems needed for them to connect securely and integrate harmoniously from day one. In this way, we are contributing to strengthening NATO’s security.
What’s more, as we expand the NATO community, we also grow our knowledge base and level of expertise across the Alliance. I look forward to working with our new colleagues on driving NATO’s technological edge and innovation pipeline together.
The NCI Agency is playing its part towards achieving the objectives set in the ambitious NATO 2030 agenda. As I write this foreword, Heads of State and Government are soon to meet in Vilnius, Lithuania, to discuss the future of the Alliance at the 2023 NATO Summit.
Cyber will be an active topic of conversation and our experts are heavily involved in these initiatives, namely in supporting the longer-term contribution of cyber to NATO’s overall deterrence and defence posture, and enhancing the Cyber Defence Pledge. In addition, the
NCI Agency is a key player in NATO’s Digital Transformation Implementation Strategy and our day-to-day operations support the main dialogue of deterrence, defence and deepening partnerships.
I look forward to the outcomes and decisions of this historic meeting, and the NCI Agency will stand ready to provide our expertise and support to help advance NATO’s transformation agenda.

Earlier this year, the first regional office of DIANA was opened at the Imperial College London Innovation Hub. This is a main area of focus for us at the NCI Agency, as DIANA’s aim to harness dual-use commercial technologies for defence and security purposes, namely emerging and disruptive technologies, makes the Agency a key player in adopting and fielding new and innovative solutions.
The first DIANA pilot activities will start in the autumn of 2023; therefore the coming months will be critical as we gain momentum. For this edition of NITECH, we are fortunate to have the inaugural Chair of DIANA, Barbara McQuiston share how the project will support NATO’s innovation and
technology advantage. Also, don’t miss NATO Assistant Secretary General for Emerging Security Challenges, David Van Weel’s article, in which he details his involvement and views on the DIANA project.
A magazine about innovation would be amiss without a discussion on emerging and disruptive technologies. This edition features articles on initiatives using these revolutionary tools including an update on 5G, an overview of the NCI Agency’s work on testing Unmanned Air System (UAS) vulnerabilities and an interesting read on how we are transforming military operations with virtual reality. In addition, we bid farewell to Ian West, Chief of the NATO Cyber Security Centre, as we look back on his impressive NATO career. Finally, don’t miss the article discussing the United Nations theme for International Women’s Day, ‘DigitALL: Innovation and technology for gender equality’.
We have an exciting future ahead and this magazine just scrapes the surface of the critical work done by our experts and partners across the NATO enterprise. I hope this edition invokes thought-provoking discussion and pioneering thinking. Here’s to a new era of NATO innovation, enjoy!
The increasing turmoil worldwide is a stark reminder of the ever-changing landscape of warfare. To ensure the resilience of NATO and its member states, it is crucial to continuously innovate and improve capabilities. By embracing the power of the cloud, NATO can enhance its operational capabilities, enable efficient collaboration among member states, and ensure the secure and seamless exchange of information.
Salesforce’s key priorities and capabilities align well with NATO and the NCIA’s digital transformation efforts. By leveraging Salesforce’s cloud-based CRM solutions, military organisations can enhance data management, improve operational efficiency, and drive cost reductions.

NATO Digital 2030: Embracing the cloud and charting a course to digital transformation with Salesforce.

www.salesforce.com/eu/publicsector





Since taking on the role of NATO’s first Chief Information Officer (CIO) in 2021, things have progressed very well. There are two important factors at play. Firstly, this is a new role for NATO, and thus I have the honour of being the inaugural CIO for the Enterprise. This has the pleasant side effect that nobody can say to me, “What you do compared to your predecessor is terrible!” However, the newness of the function means that I have to build many interfaces with other organizations, and that requires a more granular definition of roles and responsibilities. Naturally, this entails building up a level of trust and it takes time for this to happen.
There is also the consideration that NATO has needed a CIO for a long time and there is an expectation that things will change fast. Therefore, we are driving change aggressively in the context of the wider process changes that NATO requires.
My priorities in light of my mandate are clear: increasing IT coherence across the NATO Enterprise in all areas – Enterprise architecture, technology use, cloud adoption, portfolio management and service delivery. NATO’s drive towards digital transformation is an important catalyst to harmonize all these efforts.
Innovation is tremendously important for speeding up NATO’s digital transformation. This is an exciting time for the Alliance. For me, digital transformation links back to one of our most basic requirements: how we best equip our military with capabilities that take all aspects of modern warfare into account.
These days, crisis and conflict situations are no longer neatly contained inside the military domains of air, land, sea, space and cyber. Our people, processes and systems must continuously evolve towards multi-domain operations and digital transformation is the driver for such an unrelenting convergence.
For maximum innovation, we need to overlap what we do in the public sector with academia and industry. Two tectonic shifts help us with this. The first is DIANA, the Defence Innovation Accelerator for the North Atlantic. The other is continued outreach to the private sector and research institutions by the NCI Agency, my office and many other players in the NATO Enterprise.
In my mind, stability comes from state-ofthe-art solutions that reside on technically sound platforms. We are shifting from a largely on-premise environment to incorporating the cloud where it makes sense. Our core competencies are consultation, deterrence and defence. We have an opportunity to harness the capabilities of cloud service providers (CSPs) to deal with rapid capacity needs, managing obsolescence and giving us efficiencies. Like many other organizations, we expect CSPs to provide us with a level of agility that we simply could not sustain by running everything in our own data centres. This is a big change for us – the shift from building IT capabilities to procuring services from industry in an agile fashion.
The second game-changer in this field is moving to ‘Zero Trust’ security. Here, we are turning our existing model on its side. Rather than primarily securing networks and systems, we advance towards data-centric
security. The criticality and the meaning of data must provide the answer to the question of data access. This has wideranging people, process and systems implications. Rather than simply ‘securing the house’, meaning the network perimeter, the user’s authorization level is carried forward to all lateral movements between rooms, cupboards and drawers. From a cyber security perspective, even if you ‘break through a window’, you are going to be stuck since every subsequent footstep requires (re-)authentication.
Artificial intelligence (AI) is at the forefront of many people’s minds at NATO. Firstly, there are clear guidelines that we adhere to and NATO has taken steps to set an example regarding the ethical use of data. We are also examining ways for AI to help us in furthering our goals. Conversely, we give thought to how we can strengthen our protection when it comes to adversaries who employ a different value set in the context of AI.

The TOUGHBOOK 40’s features and unique design make it the perfect device for tactical communications – tailored for defence-ready applications including situational awareness, military transportation, and platform maintenance.


EMDYN Platform is our bespoke geospatial intelligence fusion application. It draws together location intelligence data from an array of sources in a single application to provide unparalleled insights into situations, events or patterns of movement. The technology behind EMDYN Platform delivers exceptional analytic and artificial intelligence capabilities, rapidly facilitating detailed analysis of a raft of sources including commercial and non-commercial data feeds. Learn more about EMDYN Platform: emdyn.com

Say goodbye to intelligence silos
Handle multiple Intelligence Sources from a single pane of glass

Build from the ground up for the Big Data era and process trillions of records near real-time
Highly Extensible and Customisable


 Lara Vincent-Young and Simon Michell, Co-Editors, NITECH
Lara Vincent-Young and Simon Michell, Co-Editors, NITECH
Simon: The title of this issue of NITECH, ‘A New Era of Innovation’, captures a pivotal point in the Alliance’s innovation journey, and the cover being designed with the help of artificial intelligence (AI) really reflects that. The Alliance has always nurtured innovation, especially at the NCI Agency and NATO Alliance Command Transformation, and indeed NITECH has covered the topic in the past, but the progress in the effort to establish the Defence Innovation Accelerator for the North Atlantic (DIANA) has been spectacular in 2023.
Lara: Absolutely. As the Assistant Secretary General for Emerging Security Challenges, David Van Weel, points out in his interview, all the fundamentals are now in place. There is a Chair, Board of Directors and a central facility in London’s Imperial College.
Simon: And a further facility in Tallinn, Estonia is on the way.
Lara: The launch of the pilot challenge programmes in July will be a much-anticipated milestone for DIANA. It will be something that we should cover in the next issue of NITECH.
Simon: I agree. That is why it is so great to have DIANA’s inaugural Chair, Barbara McQuiston, add a little extra information about the pilot challenge programme. Potential participants will be interested to hear that these challenges will have multiple awards and be run competitively across the Alliance with grants to cover the costs of DIANA’s accelerator programme.
With the Regional Office now established at Imperial College in London, and Professor Deeph Chana in place as its Managing Director, the momentum is really starting to gather speed. The UK Secretary of Defence is very enthusiastic in his article. I Quote, “DIANA represents a game-changer for NATO, bringing together industry, government and academia from across the Alliance, leveraging a transatlantic network of accelerators and test centres to support the foundation, growth and success of start-ups working to bring the best of civilian innovation to Defence.”
Lara: DIANA is fundamental to another key topic in the issue – Multi-Domain Operations (MDO). The Alliance’s Digital Transformation Champion and Special Advisor, Brigadier General Didier Polomé, really captures how important this is for NATO operationally. Like Barbara McQuiston, he underlines that these sorts of
programmes are not just about technology, they are about people and processes too.
Simon: Very true, but technology still plays a central role. The Digital Workplace is a key supporting platform for MDO. Jean-Paul Massart explains this very well in his feature.
Lara: That is why the Digital Workplace shares the same timeframe for implementation – 2030.
Simon: Exactly, plus MDO has an internal Enterprise aspect to it as well. The Chief Information Officer, Manfred Boudreaux-Dehmer, stresses this in his foreword.
Lara: Another key technology that will also have an impact on MDO and DIANA is 5G. The NCI Agency is a key driving force for 5G, not just from an operational perspective, but from a technical and regulatory standpoint too. As Germano Capela points out, it is vital that the defence sector, and NATO in particular, make their voices heard in the international fora that are driving the implementation of 5G and even 6G. Like DIANA, 5G is a reminder that innovation is being driven by market forces more than defence investment.
Simon: Too true, there has been a real transformation in this area across so many dual-use sectors –telecommunications, space, unmanned systems. The Ukraine war has shone a massive spotlight on this.
Lara: One of the key goals of NITECH has always been to promote diversity, equity and inclusion, so it is great that this issue coincides with the UN’s DigitALL programme that aims to encourage women into the digital world. Our very own Diana DeVivo really gets to the bottom of why this is so important, especially for organizations such as NATO.
That said, let’s not forget that the NCI Agency is losing one of its prime innovators. Ian West will leave the Agency this year to follow new avenues and hopefully spend some quality time with friends and family. Ian has been at the NCI Agency since the beginning, having first joined NATO in 1996. Without doubt, he has been fundamental in ensuring that NATO and the Member States have been alerted to, and defended against, the scourge of the cyber threat that has become such an overwhelming danger to everyone in both their private and working lives. We wish him every success for the future and hope to see him again soon.
The prospect of capable, real-world quantum computers will soon be a reality – and BT is preparing for an evolving quantum environment

We’re now at a point where organizations and research institutions are announcing plans that make the prospect of capable, real-world quantum computers a near certainty. So, it’s time to talk about our own innovations, centred on quantum technology, that we’ve been working on since 2013.
At BT, our ambition is to be the world’s most trusted connector, and part of achieving that goal is taking an active role in determining the future of connections – be that secure communications among people, devices or machines. We’re also keeping a watching brief over all possible future scenarios, as well as determining the balance between hype versus reality. This way we’ll always be ready to turn challenger technologies into the next generation of connection, future-proofing our business as well as our customers.
We’re exploring a range of new solutions that address current and future cyber threats, and a secure
digital infrastructure is at the heart of our plan for quantum technologies. Our quantum technology approach brings together the best of UK and international collaboration and sees us working as a key contributor to the UK National Quantum Technologies Programme (NQTP).
At this point, quantum computing has significant potential for a broad range of sectors, no more so than the military given the importance of secure communication and information. Our focus now is on turning quantum innovation into services that secure data in the long term, to protect connections and digital communications.
With its immense processing power and ability to solve complex problems, quantum computing is likely to enable breakthroughs in a range of fields such as pharmaceuticals, energy security, national and international defence.
But, as with any technology, quantum computing could also be used for nefarious purposes. For example, it has the potential to be able to crack the mathematics that underpin much of the current cryptography that’s used to secure networks. The type of algorithms that are most affected are ‘asymmetric’ algorithms used in key exchange, digital signatures and Public Key Infrastructure (PKI) certificate-based authentication.
There’s a risk of ‘hack today, crack tomorrow’ attacks, where key exchanges and digital signatures made today could be at risk of retrospective attacks, even after the key has been used, or the certificate has expired, once capable quantum computers are available.
The threat of large-scale quantum computers is well understood and has been emphasized by many national cyber security and defence authorities. It’s high on the agenda
 Senior Manager, Optical Networks and Quantum Research, BT
Post-Quantum Cyber Security Lead, Research and Network Strategy, BT
Professor Andrew Lord Dr Ali Sajjad
Senior Manager, Optical Networks and Quantum Research, BT
Post-Quantum Cyber Security Lead, Research and Network Strategy, BT
Professor Andrew Lord Dr Ali Sajjad
of the National Cyber Security Centre, the Defence Science and Technology Laboratory (Dstl), and international governmental and standards organizations.
Many international standards organizations now have working programmes for post-quantum cryptography (PQC) standardization. Front-runner NIST plans to publicly release its standardized specifications for PQC algorithms by 2024.
Quantum key distribution (QKD) is the most secure key establishment technology available today, other than using a physical courier to move keys.
QKD provides a secure communication method for exchanging encryption keys only known between shared parties, across an authenticated but insecure channel. Its security relies on distributing information as quantum bits (or qubits, the basic unit of information in quantum computing) that can’t be read accurately without being disturbed. Once they’re disturbed, they can’t be measured or read without changing their quantum state, making it impossible to eavesdrop or intercept the message without being detected.
At BT, we deploy QKD in parallel with a standard classical mathematical key exchange, for dual resilience against any emergent cryptographic breaks.
We’ve been evaluating and incorporating some of the more promising PQC algorithms into our collaborative research projects.
In collaboration with the Nuclear Engineering Group at Imperial College, London, we extended a virtual private network (VPN) solution by adding two PQC alternative algorithms for authentication and key establishment. We successfully identified an algorithm that only caused a manageable increase in latency of 15% when establishing a VPN session, but with the advantage of quantum-safe authentication of the end nodes.
We designed and developed a private Public Key Infrastructure (PKI) solution with automated certificate management, creating a service that can be used to requisition postquantum digital certificates, as well as verification of these certificates and code signing services. The PQ certificates it issues can be used widely, including by web servers and VPN servers to verify the identities of users, devices or services. This significantly increases the security of a network by providing a quantumsafe, cryptographic foundation of trust for all devices, users and services using that network.
We’ve also worked with the Aquasec consortium and the UK Quantum Communications Hub to trial encrypted links. These links use QKD in combination with classical cryptography for key exchange.
In collaboration with government and industry, we opened a commercialgrade quantum test network link between the BT Labs, in Ipswich, and Cambridge University.
The link forms part of the UK Quantum Network, and is used for testing and demonstrating new quantum technologies, such as QKD. This includes trials of how these technologies can secure critical and sensitive data across vertical industry sectors, including defence.
In partnership with Toshiba Europe Ltd, we launched the London Quantum Secure Network – a trial London-area network able to deliver key material, used to encrypt customer data, to customer sites, incorporating high-speed, highperformance encryption and data transmission. The network is demonstrating how data secured using quantum key distribution can move between sites, in a way that’s future-proofed against the threat of an adversary equipped with a quantum computer.
The possibilities of quantum computing are, perhaps, beyond full comprehension right now, but the advances made so far have the potential to bring exciting new capabilities to the military. At BT, we’ll continue investing in quantum-based services as part of our ongoing commitment to innovation.

technology advantage and what role the newly established Defence Innovation Accelerator for the North Atlantic (DIANA) will play in supporting this effort


How has NATO traditionally maintained its innovation advantage over potential adversaries and why does this need changing?
Traditionally, a lot of dual-use technology was first developed and adopted by the military –think of the internet and GPS on the hi-tech side and duct tape at the lower end of the scale. This enabled the military to control how a lot of its innovations were made available to civil society for commercial applications. However, those days are mostly gone, and a lot of the innovation that NATO can benefit from is actually taking place within the private sector for commercial use.
A good example of this is the autonomous air systems (drones), which Amazon has begun to use to deliver products to some customers in the US. In fact, it’s not just the US. Starship Technologies in Estonia has developed a ground-based system using robots to deliver food and other items. Compare that to current military logistics operations, which are still heavily reliant on big, gas-guzzling trucks driven by humans and organized on spreadsheets. They’re worlds apart. So, the military needs to change the way it adopts emerging technologies to keep up with our adversaries.
In which areas of innovation and technology is NATO in danger of falling behind and why?
NATO uses the umbrella term of emerging and disruptive technologies (EDTs) to encapsulate the challenge. In a nutshell, these are: artificial intelligence (AI), autonomy, biotechnology, energy and propulsion,
hypersonic technologies, novel materials, quantumenabled technologies, novel communication technologies and space.
The example I just gave with regards to autonomous systems is just one of the areas we need to address, but we need to use things such as AI and quantum computing to innovate further. Imagine the impact that strong, lightweight, novel materials could have on armoured vehicles. If NATO could find a way of armouring a vehicle with a material that is as strong as steel but doesn’t weigh as much, it would have all kinds of dual-use benefits. When it comes to other novel materials, could we perhaps replace the existing constituents of batteries so that we are no longer dependent on others for those raw materials?
These are the sorts of things we need help with. However, time is running out, and we need to engage now before these innovations fully emerge and start to disrupt. You can guarantee that if they change the way things are done in the commercial world, they will have a commensurate impact on the defence sector as well.
What are the key tenets of NATO’s EDT strategy?
NATO’s EDT strategy is called ‘Foster and Protect’. On the one hand, NATO wants to foster its own ecosystems and promote the adoption of dual-use technology. On the other hand, we not only want to protect those ecosystems, but also ourselves against the use of EDTs by potential adversaries. That is why we
Simon Michell asks NATO Assistant Secretary General for Emerging Security Challenges, David Van Weel, how the Alliance is maintaining its innovation and
keep a close eye on what other nations are doing in this area. As you might expect, we monitor what China is doing with AI, big data and quantum communications/ computing, in particular, to get a feel for where NATO is in comparison.
How will the Defence Innovation Accelerator for the North Atlantic (DIANA) help to accelerate this challenge?
The traditional defence procurement process generally starts with a military organization asking in precise terms exactly what it wants for a specific system. It then expects developers to stick rigidly to that request in the development of the solution. However, with DIANA, NATO is going to pose a series of generic challenges without saying what technology developers should employ to solve them. In other words, DIANA is going to be technologically agnostic. The developers will have a free hand to solve the challenge using whatever processes, systems and technology they see fit. For example, DIANA might ask, how can two submarines communicate with each other underwater from a distance of more than 100 kilometres?
This concept will have two main benefits. First, it will reveal to developers that the defence sector may have a use case for their technology of which they were previously unaware. Secondly, it will prompt companies to reveal technology solutions that NATO had not previously considered.
The thing that makes DIANA unique and particularly attractive to start-ups is the fact that NATO combines 31 nations. This naturally offers a very
large potential market. Added to that, DIANA will offer participants access to the NATO Science and Technology Organization (STO), which has more than 5,000 top-class scientists. It will also provide access to the world’s best test centres across the entire Alliance.
DIANA will also be able to use its connections to provide mentoring by operational end users. Participants will be able to test whether their innovations actually work in the field, and, if not, they can go back to the drawing board and fix them. In terms of the dual-use sector this is an unprecedented opportunity.
When will NATO start to see the benefits of DIANA and what technology areas will it prioritize?
As DIANA’s interim Managing Director (MD), I have been working hard for almost a year with DIANA’s Chief of Staff, Kadi Silde, to prepare the groundwork for the accelerator to reach initial operating capability in time for the NATO Summit in Vilnius this July. On 31 March 2023, I visited London with the NATO Deputy Secretary General, Mircea Geoană, to open DIANA’s European office at Imperial College’s Innovation Hub (I-HUB). While there, I handed over the managing directorship to Professor Deeph Chana. So, the building blocks are now all in place. We have a board of directors with a chair, Barbara McQuiston, an MD in Deeph Chana and a location at Imperial College.
This June, DIANA will announce its first challenge programme based around the three areas of sensing and surveillance, secure information systems and energy resilience. These are all fields of applications rather than specific technologies, so they will be narrowed down when they are officially announced.

“The developers will have a free hand to solve the challenge using whatever processes, systems and technology they see fit”
How will NATO and the Member States fund DIANA?
We have come up with an innovative funding approach for DIANA called joint funding, which has the same cost-share concept as the existing NATO common-funding model into which all 31 members contribute, but it doesn’t source investments out of the common funding budget itself. Instead, funding comes directly from the nations. The advantage of this is that it enables each nation to decide which governmental department it wants to source the money from. Some countries might want to invest via their finance ministries, or their ministries of innovation or perhaps somewhere else. In essence, it gives each nation more freedom to choose how it wants to fund the accelerator.
We are also establishing a related funding source known as the NATO Innovation Fund (NIF), which is an ‘opt-in’ fund with 22 of the 31 NATO Member States currently participating. Over 15 years, they will invest more than €1 billion. The NIF is a classic venture capital fund with the participants as limited partners and an investment manager making the investments. This fund, however, is not specifically intended to support DIANA exclusively.

It can decide for itself what projects and organizations it wants to invest in across the entire Alliance territory.
The way we envisaged this working is that DIANA will award grants to start-ups to help them develop dual-use EDT technologies. Then, those with the most promising innovations might attract a venture capital investment from the NIF. They are not obliged to. This is just one possible route. Some start-ups may look for NATO contracts and others might be acquired by existing contractors. We want to keep everyone’s options open.

What is the relationship between DIANA and the NCI Agency?
There are a number of major players within the NATO Enterprise that deal with innovation. This includes STO, as I have just mentioned, CMRE (Centre for Maritime Research and Experimentation) as well as Allied Command Transformation (ACT) and its innovation hub. The NCI Agency definitely fits into this group, especially when it relates to the information and communications spheres. There will, therefore, be very close connections between the NCI Agency and DIANA as there is a clear role for the NCI Agency in terms of validation and testing.
By adopting innovative strategies and pioneering the use of emerging technologies now, NATO is well positioned to secure its digital vision of NATO for 2030
In an era marked by rapid technological advancements and evolving global threats, the need for complex government organizations to embark on a digital transformation journey has become imperative. The North Atlantic Treaty Organization (NATO), a key alliance formed for collective defence, finds itself at the crossroads of embracing the digital backbone and charting a course to digital transformation. By adopting innovative strategies and leveraging emerging technologies, NATO can position itself as a resilient and agile force in the face of evolving challenges.
The war in Ukraine serves as a stark reminder of the ever-changing landscape of warfare. To ensure the resilience of NATO and its Member States, it is crucial to foster an environment of continuous improvement and innovation. By building a digital backbone, NATO can establish a solid foundation that
enables rapid response and adaptation to emerging threats. Anecdotes from the war in Ukraine highlight the importance of creating resilience through advanced technological capabilities.

One key aspect of NATO’s digital transformation journey is the adoption of cloud computing. By harnessing the power of the cloud, NATO can enhance its operational capabilities, enable efficient collaboration among Member States, and ensure the secure and seamless exchange of information. The transition to the cloud also provides scalability, flexibility and cost efficiency, enabling NATO to optimise its resources and focus on mission-critical tasks.
Furthermore, NATO must shift its organizational mindset to become data-centric in decision-making processes. By leveraging data analytics and artificial intelligence, NATO can gain actionable insights and make informed decisions that drive strategic outcomes. Armed forces around the world have
successfully executed similar journeys, leveraging data to enhance operational efficiency, intelligence gathering, and situational awareness. By embracing data-centric decisionmaking, NATO can unlock its full potential and adapt to evolving challenges effectively.
Taking action now to secure the digital vision of NATO for 2030 is of paramount importance. The rapidly changing technological landscape requires proactive measures to ensure NATO’s continued relevance and effectiveness. By investing in digital capabilities, NATO can future-proof its operations, enhance interoperability and maintain a technological edge over adversaries. This will not only strengthen the Alliance, but also attract and retain the top talent of Member States who seek to contribute to cutting-edge digital initiatives.
A successful digital transformation journey starts small and generates momentum. NATO can identify pilot projects and initiatives that showcase the potential of digital technologies in
Vice President – EMEA Public Sector, NATO & European Defence Global Public Sector, Salesforce Jamison Braunenhancing operational effectiveness. By demonstrating tangible results, NATO can generate buy-in from stakeholders, build confidence in digital transformation efforts and secure necessary resources for scaling up. Starting small also allows NATO to learn from successes and failures, iterate on strategies and refine its approach towards a comprehensive digital transformation.
Rethinking every aspect of operations is essential in advancing NATO’s ability to respond swiftly to new challenges and opportunities. This includes modernizing infrastructure, streamlining processes and adopting agile methodologies. Embracing emerging technologies such as Internet of Things, edge computing and blockchain can revolutionize logistics, supply chain management and cyber security. By embracing innovation and agility, NATO can optimise its resources, enhance operational efficiency and adapt to a rapidly evolving threat landscape.

A robust customer relationship management (CRM) framework can play a pivotal role in executing NATO’s digital transformation. By implementing a centralized CRM system, NATO can effectively manage interactions and collaborations with Member States, partner organizations and stakeholders. A comprehensive CRM platform can provide a unified view of the Alliance’s relationships, facilitate knowledge sharing and enable effective decision making. It can also support NATO’s efforts in building strong partnerships, fostering collaboration and promoting interoperability. We are terribly proud of the strides we’re making in partnership with Amazon Web Services and our own Hyperforce infrastructure to deliver these innovative solutions for DIANA and the NATO education ecosystem.


In conclusion, NATO stands at a critical juncture, where embracing the
digital backbone and charting a course to digital transformation is crucial for its continued relevance and effectiveness. By adopting innovative strategies, leveraging emerging technologies and rethinking every aspect of operations, NATO can enhance its resilience, agility and operational capabilities. The digital transformation journey presents an opportunity to secure NATO’s digital vision for 2030 and attract and retain the top talent of Member States. By taking action now, NATO can position itself as a formidable force in the face of evolving global challenges. salesforce.com/eu/publicsector
The inaugural Chair of NATO’s Defence Innovation Accelerator for the North Atlantic (DIANA), Barbara McQuiston, tells NITECH how DIANA will support the effort to maintain NATO’s hard-won innovation and technology advantage


DIANA is part of the overall effort across the NATO Alliance to strengthen innovation capacity and rapidly bring dual-use solutions forward from new and emerging entrepreneurs, specifically to address security challenges. The overall goal is to create continuous innovation that can be rapidly adopted for our security market.
Innovation is not just about technology. Innovation is about technology, people and process. It is about engaging and inspiring our collective human capital, our best and brightest, in areas critical for enabling new outcomes to the most critical challenges facing our Member States and their economic security.
To do this, we must recognize the value of our innovators, look across technologies and build collaborative frameworks to leverage not only the expertise and ideas of our citizens, our entrepreneurs, but also seek collaborations with governments, non-profits, academia
and the private sectors to move solutions forward to tackle our needs now and into the future.
DIANA is developing a framework that serves to pull ideas forward and fund the stages of growth to test out solutions, learn from our failures and move solutions forward, helping to scale them to meet the demand. This requires building an ecosystem of opportunities; allowing start-up companies and entrepreneurs to engage the security market and the commercial market for these solutions and be supported in their development; and to provide the public and private capital necessary for these ideas to mature into commercial reality and meet the needs in the market.
This is the mission of DIANA. We seek to inspire the citizens in our Alliance by using challenge problems in areas such as energy resilience, sensing, digital security and others, seeking out new and innovative approaches and solutions. DIANA will support new ideas through competitive phases to test, experiment with and prototype solutions and, ultimately, to have better rapid
adoption and learn what impact these solutions can have in meeting NATO’s security challenges.
Innovation at NATO using dual-use technology is also about moving the NATO culture away from a cold-war acquisition posture to one of collaboration and rapid acquisition. The culture of innovation includes capitalizing on speed and rapid adoption, incorporating new knowledge and capability, and becoming more agile while modernizing — all the while accelerating our leading edge in technology within our Alliance and the entire industrial base.
Where will DIANA be based and what presence will it have across NATO Member States?



DIANA will bring NATO military personnel together with the Alliance’s best and brightest start-ups, scientific researchers and technology companies to solve critical defence and security challenges. Innovators, competitively chosen as a participant in DIANA’s programmes, will receive access to its network of dozens of accelerator sites and test centres across more than 20 Allies.
Just this last March, DIANA opened the first regional office at the Imperial College London Innovation Hub, located in the White City Innovation District as an independent NATO body in partnership with the United Kingdom. Regional hubs will be supported in Tallinn, Estonia, and a North American office in Canada to complement the DIANA organizational structure.
DIANA is pulling together a network of more than 100 deep-tech, start-up accelerators and laboratory test centres from across the Alliance, with the purpose of rapidly accelerating both technology solutions and entrepreneurial efforts to keep our technological edge and industrial strength.





DIANA is setting up this ecosystem to support and inspire our citizen inventors and entrepreneurs within the Alliance. It also provides the chance and tools to accelerate their ideas and solutions into a vibrant economic opportunity and solution for NATO’s security challenges. As such, DIANA is complemented by the NATO Innovation Fund (NIF), the world’s first multisovereign venture capital fund, which will invest €1 billion over 15 years in start-ups developing or adapting technologies to defence and security.
What key technologies will DIANA pursue and why?

DIANA will look at disruptive and emergent technology with the ability to harness dual-use commercial technologies for defence and security purposes. Based on the efforts from the NATO Emerging and Disruptive Technology Advisory Organization, which has been chaired for the past several years by Dr. Deeph Chana, DIANA will continue this focus on the nine emerging and disruptive technologies of priority to NATO in artificial intelligence (AI), data, autonomy, quantum-enabled technologies, biotechnology, hypersonics, space, novel materials and manufacturing, and energy and propulsion.

Key
Regional Offices
Regional Hub
Test Centres
Accelerators
GERMANY – 9 sites
AI, data, autonomy, space quantum hypersonics, secure communications, energy and propulsion, semiconductors
NETHERLANDS – 2 sites
AI, robotics autonomous systems, novel materials, energy quantum
BELGIUM – 14 sites AI, autonomy hypersonics manufacturing, cyber, nanoelectronics, ICT
UNITED KINGDOM operational testing
FRANCE – 10 sites
AI, autonomy, quantum, biotechnologies, energy and propulsion, novel materials, advanced manufacturing, hypersonics, space Test Centres in the United States across all emerging and disruptive technology areas
SPAIN – 5 sites
AI, maritime, neurotechnology, 5G, quantum communications, energy
PORTUGAL AI, data autonomy novel materials
DENMARK – 4 sites quantum nanotechnologies novel materials, optics, laser, metrology


NORWAY data, autonomy, robotics
ESTONIA – 6 sites
AI, data, autonomy, cyber robotics space quantum biotechnologies novel materials manufacturing, unmanned vehicles, aerospace
LATVIA
AI, data communication technology
LITHUANIA – 6 sites
AI, data, autonomy, cyber, greentech, biotechnology, space, novel materials, energy and propulsion
6 sites AI, data, autonomy, cyber, greentech, biotechnology, space, novel materials, energy and propulsion
ITALY – 2 sites data, maritime, ISR, air, space, materials

Looking at critical and emerging technology can hold transformational solutions for us and accelerate our ability to maintain our technological leadership. Through DIANA and the NIF, NATO can help create the next generation of industry capability for security. Just as semiconductors and the subsequent discovery of the transistor effect ushered in the age of microelectronics, there are transformational technologies in our future that will have a profound effect.
Biotechnology, AI and quantum science hold solutions in our energy and climate future, engine and transportation technology, medical advances, and food security and much more. Through proactive engagement with entrepreneurs developing nascent technology, NATO and our democratic Alliance can help responsibly drive these critical technologies to address our security future.
There are 31 countries that are part of our DIANA effort, all of which have voluntarily invested joint funds towards the project. We are currently in our pilot phase and launching the first three challenges in June. These challenges will have multiple awards and will be run competitively across the Alliance. Grants will cover the costs of DIANA’s accelerator programme, including mentoring from scientists, engineers, industry experts, end users and government procurement experts to accelerate both the technology solution and the business commercial maturity. There will also be an investor network for


POLAND – 7 sites
AI, data, autonomy, CBRN, cyber, communication technology quantum
SLOVAKIA – 6 sites
AI, data, autonomy, robotics cyber space aerospace biotechnology
HUNGARY – 2 sites
AI, autonomy, cyber
ROMANIA – 2 sites
AI, hypersonics
BULGARIA – 3 sites
AI, data, autonomy
technology quantum
6 sites data, autonomy, robotics cyber aerospace biotechnology
2 sites cyber
2 sites
3 sites data, autonomy

TURKEY – 2 sites
AI, data, autonomy, computing cyber biotechnology, space, hypersonics quantum
GREECE – 4 sites
TURKEY – 2 sites AI, data, autonomy, computing cyber biotechnology, space, hypersonics quantum
SLOVENIA – 3 Sites
AI, 5G, cybersecurity, critical infrastructure
AI, data, autonomy, space quantum, biotechnology, novel materials and manufacturing
GREECE – 4 sites ata, autonomy, space quantum, biotechnology, novel materials and manufacturing
secure third-party funding, anchored by the NATO Innovation Fund.
Subsequent grants will also provide competitive phasing, moving the technology quickly forward and de-risking the solution and commercial effort with opportunities to test, experiment and field technology in operational environments. By combining these grant opportunities along with rapid acquisition and pathways to the market within the NATO enterprise and 31 Allied markets, DIANA can have a transformational effect on both our territorial and economic security.
As DIANA’s first chair, what have been your immediate priorities?
Our immediate priority is standing up the DIANA organization and successfully launching the first challenges. We are actively engaged in identifying and recruiting talent across the Alliance to help establish this organization and to fill key positions. As we move to select performers and start the continual process of acceleration of dual-use technology, we will look to have 10 challenges a year advancing new companies and technologies competitively forward.
The Key to our success will be working on the rapid adoption of these technologies to strengthen NATO and the Alliance. Ultimately, this is the measure of success for NATO and will need to have an ‘all-of-NATO’ effort within our enterprise and Alliance to create innovative processes and directly support new ideas, new technology
accelerate the opportunity to transform
future.

With a focus on data protection in the quantum era, Nokia is providing a reliable solution for securing in-flight data against current and future threats
What is unique about Nokia’s Quantum-Safe Networks solution and how does it work?
Why do emerging quantum computers pose such a threat to mission-critical defence communications networks?
The threat posed to mission-critical defence communications networks by emerging quantum computers stems from their potential to break widely used encryption algorithms, compromising the confidentiality, integrity and long-term security of sensitive and classified information. Therefore, it is imperative to address this threat by investing in quantum-safe cryptography and adapting military communications systems accordingly.
• Breaking public-key cryptography: Public-key cryptography is often used in defence communications networks for secure key exchange, digital signatures and secure communication channels. However, common public-key algorithms, such as RSA and Elliptic Curve Cryptography (ECC),
are vulnerable to attack by quantum computers. If an adversary is able to intercept encrypted defence communications during transmission, or gains access to stored data, they could subsequently use a quantum computer to break the encryption and compromise the confidentiality and integrity of the data and/or communication.

• Longevity of encrypted data: Defence communications networks often require long-term security for classified information, which means that cryptographic systems need to be designed to protect the confidentiality and integrity of data for extended periods. However, if an adversary captures encrypted data and stores it for future decryption with a quantum computer, the security of that data could be compromised once a powerful quantum computer becomes available.
Nokia’s Quantum-Safe Networks (QSN) solution offers a comprehensive and robust framework that encompasses multi-networks, including wireless, wireline, terrestrial and subsea connectivity. With a focus on data protection in the quantum era, our solution provides a reliable transport solution for securing data in-flight against today’s and future quantum-computer threats. These solutions leverage existing encryption standards and are able to incorporate future standards once available and ratified, such as those based on the NIST PQC activity.
Nokia’s Quantum-Safe Networks solution encrypts and decrypts data in-flight in the many connectivity domains of our rich portfolio, including optical terrestrial and subsea, IP, microwave and even mobile. We achieve this in-flight data protection via the quantum-safe AES-256 block cipher.
When it comes to quantum-safe keys, Nokia uses two types and two different methods to obtain them: physics-based keys and mathematics-based keys via symmetrical and asymmetrical encryption. In symmetrical cryptography, we use pre-shared keys (PSK), so the same PSK is used for encryption and decryption of the in-flight data at both endpoints. Such cryptography is foreseen to be used with engineered connections, such as:
Head of Emerging Markets, Optical Networks, Nokia Head of Defence Vertical, Nokia Martin Charbonneau Philippe Agard• Optical networking: optical transport network (OTN) data container encryption
• IP networking: line-rate, silicon-based MACsec (Ethernet, VLANs) and extension of MACsec standards to support native, line-rate encryption of Segment Routing, MPLS and IP (ANYsec)
Our solution will also extend to public key infrastructure (PKI) cryptography, also known as asymmetrical cryptography, once the post-quantum computing (PQC) algorithms are available. In asymmetric cryptography, both endpoints exchange their unique public keys, and, via mathematical calculations using their own private key, will derive the same secret key. Such cryptography is foreseen to be used with dynamic connections at the message and application level over the following networking:
• IP Networking: IPsec, TLS, SSH
• Microwave Networking: IPsec, TLS, SSH
• Mobile Networking: IPsec, TLS, SSH
Hence, Nokia’s vision allows for infrastructure providers and builders to architect an evolving defence-in-depth strategy, ensuring that their critical infrastructure becomes a backbone for quantum-safe communications using complementary quantumsafe cryptography.

We have devised a blueprint-based approach, which enables all stakeholders to engage in the context of a structured framework, and via this engagement, find optimal ways to realize their specific quantum-safe networks journey. So far, we have defined six blueprints.
Of course, Nokia is not doing this alone. To deliver our QSN vision, we bring customers and partners into an ecosystem, which allows for:
• pooling expertise and experience,
• leveraging collective knowledge, and,
• solutionizing today for a better tomorrow.
How can Nokia’s quantum-safe optical networking solution protect defence wide area networks?
As defence organizations increase the momentum for digital transformation, the availability of a resilient, secured digital backbone that extends from the strategic echelon to the tactical edge is a prerequisite. NATO has highlighted next-generation communications, big data, artificial intelligence (AI) and quantum as key emerging and disruptive technologies, and therefore, each NATO Member State should be prepared to leverage this digital backbone as a key enabler to achieve the next level of information superiority. Organizations will generate ever more data from the future ‘Internet of Battle Things’, and will want to move this data instantly for AI-based analytics to improve situational awareness and decision-making.
Nokia has deployed its wide area networks (WAN) technologies across many defence ministries. This often encompasses a combination of optical transport and IP/MPLS routing. Consequently, these organizations can combine encryptions at several layers of the communication stacks using a defence-in-depth approach – L1 with advanced QSN encryption in the optical transport domain, and in the L2/L2.5/L3 domains with MACsec and ANYsec.
What other technologies can Nokia combine with the quantum-safe solution to further enhance defence capability and data security?
Nokia has introduced Cyber Dome, which is an advanced extended detection and response platform embracing radio, core and backbone and leveraging AI to detect and respond to the threats that may appear on the 5G E2E network. This solution complements the WAN quantum-safe encryption to better protect defence communications from cyber attacks.
Nokia is heavily involved in the various ‘5G for Defence’ initiatives happening across numerous NATO Nations, as well as at the NATO level through the works of NATO IST 187 and its associated 5G use case demonstrations. Nokia is also participating in 5G Communication for Peacekeeping and Defence (5G COMPAD) – a programme funded by the European Union via the European Defence Fund.
Defence organizations know that deploying 5G on military bases will scale up their digital transformation by exploiting the extreme broadband and low latency of 5G. This will facilitate the increased use of augmented and virtual reality to support maintenance, repair and overhaul and training tasks for example and improve efficiency across disciplines. 5G will also facilitate the implementation of digital twins in the life cycle of defence platforms by leveraging local edge computing as well as connecting to private data centres and remote experts via an advanced 5G-ready digital backbone. Moreover, evidence suggests that 5G can enhance the ‘operative’ echelon in mobile command posts as well as at the tactical edge, thus contributing to additional defence information superiority.
5G is a reliable and trusted radio technology and, combined with the QSN backbone, 5G networks form the end-to-end (E2E) foundational capability and key enabler of defence digital transformation. Nokia.ly/defence

What is NATO’s overarching vision and implementation strategy for multidomain operations as an element of NATO’s digital transformation?
By 2030, the NATO digital transformation will enable the Alliance to conduct MultiDomain Operations (MDO), ensure interoperability across all domains, enhance situational awareness and facilitate political consultation and data-driven decision-making. This transformational journey will address political and military requirements set out in NATO’s guiding policy documents, including the Strategic Concept, the NATO Military Strategy and subordinate elements.
The overarching NATO Digital Transformation Vision will be implemented through the Digital Transformation Implementation Strategy (DTIS), which will guide ongoing and future efforts towards a digitally effective Alliance. To this end, NATO’s digital transformation encompasses three fundamental pillars – people, processes and technology – designed to align cross-cutting efforts and provide a digital-ready workforce, agile and digitally-enabled processes as well as advanced technological solutions.
Digital transformation efforts must leverage the best digital technologies and best practices to guide the future employment of the Military Instrument of Power (MIoP). In the process, they must ensure the necessary technologies are identified, acquired and secured; and,
at the same time, facilitate harmonization across Allies’ national efforts. A balance between work strands must be achieved complementarily to maximize interoperability and efficiency gains.
Strong commitment and continuous support from the Alliance Member States is crucial to shape and advance transformation. Therefore, success will be predicated on the contributions of Allies and the implementation of a new paradigm for cooperation, which also extends to industry, civil society and academia.
How can NATO’s digital transformation support multi-domain operations?
Digital transformation is currently being embraced as a NATO strategic priority to prepare the Alliance’s MIoP to effectively address future military challenges across all domains and environments. To achieve MDO, the NATO Bilateral Strategic Command’s (Bi-SC) efforts have identified six foundational elements of digital transformation:

• Enhancing situational awareness through synthetic environments;
• Orchestrating operational effects;
• Embedding risk management and digital mission assurance;
• Adopting new capabilities;
• Aggregating data; and,
• Bolstering security and protection of personal data.
The Alliance’s Digital Transformation Champion and Special Advisor, Brigadier General Didier Polomé, explains how digital transformation and new technologies are being implemented into multi-domain operations for NATO
In order to achieve these, NATO’s digital transformation must foster a digital-ready workforce, including a culture shift which encourages and rewards innovation, experimentation, data-sharing and calculated and informed risk-taking. Moreover, Allies need to approve new mechanisms for collaboration, supported by appropriate standardized processes and policies for automation and digital environments. An agreed enterprise digital architecture will enable a coherent, orchestrated effort and inform governance on transformation priorities. Lastly, the NATO digital environment needs to be modernized for the vast data management and exploitation approaches required for transformation, which will be achieved through a resilient digital backbone.
Ultimately, these efforts must securely connect sensors, operators and decision makers –enabling digital interoperability across all domains. They must also connect the NATO Enterprise to Allies’ national digital capacities to share and employ data securely and effectively in both directions, maximize information flow, increase military effectiveness and enhance political decision-making.
What sorts of activities are you undertaking as NATO ACT’s Digital Transformation Champion and Special Advisor to SACT to promote digital transformation and multi-domain operations?

Our first priority is to achieve a full understanding of the digital transformation field quickly and effectively through a whole-ofsystem approach. This is a vast and complex effort which requires extensive outreach and engagement with internal and external stakeholders. Not only is it crucial to ascertain the cross-functional efforts required to enact digital transformation within the NATO Enterprise, but to further examine the disparate initiatives emerging
at the national level. This is because, in parallel to NATO’s efforts, Allies are developing their own national digital strategies and pursuing state-ofthe-art technology adoption.
In order to achieve MDO, our efforts must both enact transformation within the NATO Enterprise and bi-directionally connect the enterprise to the Allies’ varying national digital capacities. However, merely acquiring an understanding of NATO’s digital transformation would be insufficient. It soon became evident that engagement and consultation with partners in industry, civil society and academia were key to achieving our strategic objectives. Therefore, in compliance with the NATO Framework For Collaborative Interaction, my team initiated intensive, regular engagements with partners from across a wide spectrum of backgrounds. The initiative recently culminated in an Allied Command Transformation (ACT)-led digital transformation in support of a multi-domain operations workshop, producing exhaustive feedback which continues to provide added value to our efforts.
Once we achieved a comprehensive overview of the NATO digital transformation landscape and established a dedicated Community of Interest, our main focus shifted towards providing best military advice to support our warfighters; assuming ownership and oversight of implementation activities of the Alliance’s digital transformation; and supporting Supreme Allied Command Transformation (SACT) in the fulfilment of this mission.
Q Q
A A
What work strands are already underway to achieve digital transformation support to multi-domain operations?
The NATO Digital Transformation Vision was endorsed in October 2022 by the Consultation, Command and Control Board (C3B) and the Military Committee. The Vision will be
“The three fundamental pillars are people, processes and technology”
implemented through the NATO Digital Transformation Implementation Strategy, which is currently being finalized by the C3B and will be presented for approval at the June 2023 Defence Ministers meeting.

The DTIS provides a complete breakdown of strategic deliverables into Lines of Effort from the medium to long term, offering an overview of the relationships of digital transformation endeavours. It has been designed to align cross-cutting work strands in the pursuit of a digital-ready workforce, digitally-enabled processes and advanced technological solutions. Its associated implementation effort is expected to bring coherence across the currently fragmented digital landscape and be enacted through a continuous, multifaceted process addressing the digital transformation pillars of people, processes and technology.
Within this context, ACT and Allied Command Operations (ACO) have additionally produced the Bi-SC’s inputs to NATO’s Digital Transformation Gap Analysis (December 2022) and the Bi-SC’s inputs to the NATO DTIS (March 2023) in support of MDO. Following these efforts, both Commands will continue to jointly lead the military aspects of digital transformation across NATO.

How does the NCI Agency support ACT’s efforts on digital transformation and multi-domain operations?
The NCI Agency is in full support of NATO’s digital transformation agenda. The Agency has been working in an integrated fashion– specifically within the Chief Technology Office, Chief Information Office and Chief Operations Office portfolios. Their contributions to the Programme of Work with ACT directly reflect this ambition in the development of the digital backbone. This is a critical pillar for digital transformation, which requires close coordination between NATO entities to continuously deliver on the current IT Modernization project and the conceptual development of future capability.
Regarding digital transformation in support of MDO, the NCI Agency is currently exploring the use of emerging technologies (5G, autonomy and quantum) and advancing cloud and artificial intelligence for military use, efforts which provide tangible support to ACT. In parallel, the NCI Agency is also examining its internal business processes to ensure delivery at the speed of relevance, as well as piloting new acquisition methods.
With deep and well-founded knowledge of military needs, Panasonic Connect offers a range of ready-to-use mobile products designed to endure and perform in tough conditions
including MIL-STD-810H and MIL-STD461G. In addition, a wide range of modular configurations for the TOUGHBOOK, as well as tailor-made solutions, can be realized in cooperation with other sector specialists. The TOUGHBOOK characteristics and unique design make it the perfect device for tactical communications – tailored for defence-ready applications including command and control, military transportation and platform maintenance.
What military capabilities does Panasonic Connect offer?
Panasonic Connect has manufactured rugged computers of the highest quality for more than 27 years. Our military-specific solutions are available worldwide, and offer flexible, future-oriented use cases for mobile IT security and defence applications. Thanks to decades of close cooperation between Panasonic and various systems integrators and armed forces in Europe and the US, Panasonic Connect has a deep and well-founded knowledge of military needs.
For military users in particular, it is critical to have 100% reliable technology. Panasonic develops and provides ready-to-use mobile devices under the TOUGHBOOK brand. They are trusted by international defence organizations and tested for ruggedness and reliability according to the strictest military standards,
When was the TOUGHBOOK range of products developed and what applications does it serve?
TOUGHBOOK is a Panasonic Corporation brand that refers to its line of rugged computers. Introduced in 1996 with the CF-25 model, the TOUGHBOOK was engineered to easily withstand external forces that would normally damage or destroy normal laptops.
TOUGHBOOK mobile computers are used in a variety of sectors and industries including defence, emergency services, government, construction and the utilities. All models feature a magnesium alloy chassis that offers durability without significant weight. All ‘Full Rugged’ TOUGHBOOK models have been developed in such a way that the devices can be used in rain, snow, strong sunlight, hot and cold temperatures as well as dirty and dusty environments. Operating temperatures range from -29° to +63°C. The devices can be operated
via a keyboard or directly on the display, which has a multi-touch capability. They can also be operated with a pen and with gloves.
TOUGHBOOK tablets and notebooks have a long, predictable and stable life-cycle as successor devices maintain the same form factor so that accessories can be re-used and operators don’t have to adapt or change the whole solution regularly, and can keep it in operation continuously over many years.
How can Panasonic Connect support NATO in its daily operations?

Panasonic Connect supports NATO with products of the highest reliability and security levels. Our TOUGHBOOK products are Microsoft Secured-Core-PC certified and therefore have a secure operating system, secure BIOS and secure identity. Smart card readers, fingerprint readers, HF-RFID and face recognition with ‘Windows Hello’ can also be added. In addition, the TOUGHBOOK has an easily removable OPAL SSD.
Safety-relevant data is not only protected by the rugged design, but also optionally by TEMPEST radiation protection in accordance with the national zone model (BSI) and the international SDIP 27. Moreover, modules such as the VIASAT SSD can be integrated to increase data security with encryption. In Germany, for example, we rely on the BSI and NATO-certified security solutions from our partner Rohde & Schwarz Cybersecurity. All
Regional Sector Manager for Public – DACH, CEE and Türkiye, Panasonic Connect Patrick Muffour Toughbooks have been tested and certified by R&S with trusted disk, browser in the box and trusted VPN.
How flexible is the Panasonic TOUGHBOOK range in terms of operations?
The extensive range of accessories enables TOUGHBOOKs to be easily installed and connected into any vehicle. Moreover, the wide selection of carrying solutions enables the TOUGHBOOK to be utilized on any application or mission.

Thanks to strategic partnerships, flexible configurations and our own development departments in Japan and the UK, special requests or bespoke customer developments are possible at any time. This enables solutions that are not available on the market and gives our customers an opportunity to save costs.
Our partnership with roda computer in Germany for example, is taking such developments in the military sector to a new level.
How is Panasonic developing customized mobile IT solutions to support military applications?
The TOUGHBOOK 55, G2 and 40 are designed to provide flexibility and long-term stability thanks to the unique modular concept including expansion slots where user-exchangeable gadgets can be
clicked in. This enables users to add in features as needs change without having to overhaul the entire ecosystem. Individual parts can also be repaired or replaced in isolation without affecting the unit as a whole reducing downtime, carbon footprint and budget spend.
Panasonic Connect offers a huge array of flexible configuration options, making it easier for customers to have the exact device they want. On top of a user replaceable battery, RAM and SSD, for example the TOUGHBOOK 40 notebook also has four expansion areas for modules such as smart cards and fingerprint readers, including a multi-user authentication.
In addition, by working closely with Intel and Microsoft and adopting the standard Windows operating system interfaces, the TOUGHBOOK range is very well positioned to enable all current and future AI and AR innovations.
What is Panasonic Connect Europe’s sustainability philosophy and how do you put it into practice?
Notably, the first product launched by Panasonic’s founder, Konosuke Matsushita, in 1918 was a plug-in lightbulb adapter made of 100% recycled materials. At that time, nobody was talking about sustainability. Mr Matsushita was a
visionary who foresaw resource scarcity early on. Sustainability is in the genes at Panasonic Connect and is lived on a daily basis.
TOUGHBOOK Revive is our new sustainable take-back scheme that supports circularity. It encourages customers to donate their retired TOUGHBOOK devices to us so we can revive and refurbish them before finding a second home for them.
Sustainability is paramount for Panasonic Connect and its TOUGHBOOK product range. That’s why Panasonic Connect has entered into a cooperation with circular computing to completely recycle TOUGHBOOK devices of different types after the first cycle of use. In this way, the company breathes a useful second life into old TOUGHBOOK devices, thereby reducing carbon emissions. With the fundamentally remanufactured devices, the second life cycle is expected to save 316kg of carbon emissions per device.
At Group level, our ambition is to achieve net-zero CO₂ emissions in all business activities of all operating Group companies by 2030.
David Hayhurst asks the Commander of Allied Joint Force Command, Naples, Admiral Stuart B. Munsch , how his organization plans, prepares and undertakes missions across the Supreme Allied Commander’s area of responsibility

Operationally, NATO’s three standing Allied Joint Force Commands (JFCs) in Naples, Italy, Brunssum, Netherlands and Norfolk, Virginia, in the United States, have identical responsibilities within the Command Structure. All three must fully demonstrate the ability to plan, conduct and sustain major NATO operations –including joint operations – from either static or deployed headquarters, when engaged in any theatre of operation within, or even beyond, the Supreme Allied Commander Europe’s (SACEUR’s) declared Area of Responsibility.
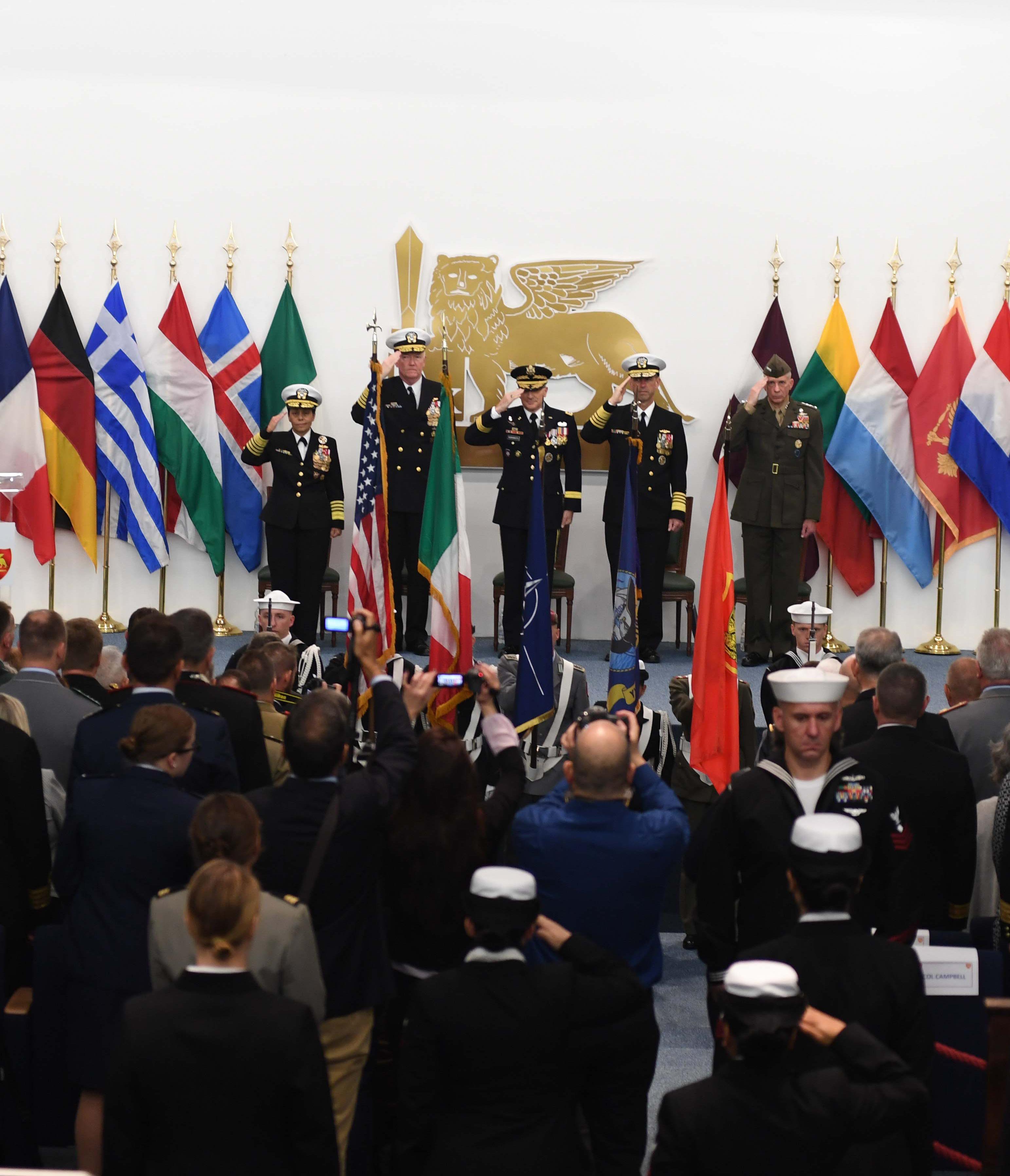
Allied JFC Naples’ designated Area of Operations extends from Portugal to Romania – encompassing NATO’s newest, easternmost members – and across the entire Mediterranean and Black Sea region. A range of other ongoing activities involve non-Alliance nations in North Africa and the Middle East.
In support of the NATO Mission, the JFCs also engage –often in close mutual collaboration – with a vast array of regional partners and multinational entities, often to help prepare current non-Member States for eventual NATO membership. Since the end of the Cold War, for Allied JFC Naples and its predecessor, Allied Forces Southern Europe (AFSOUTH), this has consistently involved intense multilateral engagement with erstwhile belligerents in the former Yugoslavia, as well as supporting NATO missions in Albania, Iraq and Afghanistan.
In the view of Allied JFC Naples Commander Admiral Stuart B. Munsch, US Navy, the war in Ukraine “has been significant in terms of how it’s changed JFC Naples, and really all of NATO, shifting from the missions that were outside of NATO territory, including Iraq and Afghanistan, and getting back to the territorial defence of NATO”.
Admiral Munsch states three prime objectives for fulfilling his command duties, both within and beyond JFC Naples’ Area of Responsibility.
First is the paramount importance of achieving and maintaining warfighting advantage over all potential adversaries. “We have to be able to defeat Russia, and defeat violent extremists, in order to be able to deter them and defend our territory,” Munsch says. In furtherance of these goals, securing warfighting advantage requires “the planning efforts that are ongoing now”, including activities beyond NATO’s territory.

Secondly, but of equal importance, is having the capability to “fold in Member Nations’ individual capabilities to make them a coherent whole. And a third piece, that I focus on heavily, is the interoperability among the nations. That’s what I can mostly affect in my time in command.”
In the Admiral’s assessment, achieving this “is based on trust. You have to have a willingness and trust to work together to get to that interoperability.” Likewise, achieving as seamless a level of interoperability as possible with the other two Allied Joint Force Commands is always of utmost importance.
Obviously, the ability to fully exploit the vast array of emerging technologies being developed by various entities within the Alliance – whether in the realms of space-based warfare, cyber security or elsewhere – is at the heart of all three of the Admiral’s stated top priorities. “Much of the innovation comes from the individual countries, as they develop their capabilities. We then bring them in as a higher headquarters, organizing them in a way to achieve a greater warfighting advantage against the adversary.”
In emerging areas such as cyber and space, “many nations have caveats on those capabilities in terms of the amount of sharing that can occur,” explains Munsch. “But we do have internal procedures to allow the sharing of some of that, so that we can get to what we call ‘all-domain warfare’. We use the traditional domains of maritime, land and air, and then add cyber and space. The idea here is to leverage
wherever we have advantages in each of those domains, to fight whatever advantage the adversary might have in other domains.”
Admiral Munsch is also keen to call attention to the indispensable role that the NCI Agency has long played in enabling Allied JFC Naples to further its mission.
“As I’ve said, the foundation of everything we do is trust. Currently that takes personal interaction and working together, but we can’t always be together in this modern world. So what connects us and perpetuates that trust are the communications that the NCI Agency enables. I want to stress the importance of the NCI Agency in maintaining trust in our command and the other commands we work with. Our ability to knit together the different capabilities that go on is due to the essential and irreplaceable communications channels the Agency provides,” Munsch notes.
Moreover, in the Admiral’s view, the Agency has “a defensive capability of its own, because we are reliant on our communications. The adversary knows that this could be something they could go after to weaken us. And so the defensive capabilities of the NCI Agency in maintaining our communications are also quite critical. The Admiral adds, “Everything they do to maintain our systems is absolutely critical to our ability to deter and defend.”
“The idea is to leverage wherever we have advantages in each domain, to fight whatever advantage the adversary might have in other domains”
Digital reality solutions company Hexagon is working to liberate the power of data, supporting organizations to extract key information from the large volumes of data they receive automatically and autonomously – and turn it into competitive advantage

Hexagon is a global leader in digital reality solutions, combining sensor, software and autonomous technologies. We serve a range of sectors and industries, including agriculture, defence, governments, manufacturing and mining. My own division, Safety, Infrastructure and Geospatial focuses on public safety command and control (C2) for blue light services and utilities network management. Our government, transportation and defence teams develop software solutions for capturing, managing, analysing and delivering digital data autonomously. That covers mapping data, including visualizing and enhancing satellite imagery. In essence, we are a digital company that liberates the power of data to support digital transformation and improve workflows.
Surprisingly, defence agencies and supporting organizations have large volumes of data they are unaware of, which means they are not getting any benefit from it. When it comes to geographic data, for example, if you know when something happened and where it happened in relation to other events in other places at the same time, that gives you a greater situational awareness you didn’t know you had. That is where Hexagon comes in; we can help organizations discover their data, analyse it, manage it and distribute it effectively. Hexagon systems and software do a lot of this automatically and autonomously, such as validating a data file on receipt and returning it if it is not valid, thus preventing any disruption to production.
Organizations, especially in the defence community, have gone from not having enough data to having too

much. Even if they can find it all, they do not have the resources to analyse it and extract the value. Hexagon embeds artificial intelligence and machine learning into its software to support the efforts of organizations to find and act on their data. This helps specialists concentrate on the tasks requiring their expertise. But it doesn’t have to be complicated. Automating simple things to shorten workflows can be extremely powerful. This can be as simple as alerting analysts there is new data available they can analyse and extract value from. We can automate the process of sorting and validating data integrity and then deliver it.
We manage data so that users can find it, analyse it and interrogate it to come up with relevant answers to decision challenges quickly, thus gaining competitive advantage. This data analysis can encompass different sources in the defence IoT, via no-code data workflows that can be
EMEA defence lead, Hexagon’s Safety, Infrastructure and Geospatial divisionautomated, such as using standardized web services that enable users to create, modify and query spatial data on the web. Moreover, with our geospatial expertise, we can visualize data by combining sources from a variety of devices and make it available on different platforms – from HQs to deployed forces. Commanders can then make decisions based on the latest data and information.
End users then receive the information they need in the right format at the right time – that might be a map, a visualisation, a report or a ‘turn left’ instruction.
Some things that immediately come to mind include data capture and management. Hexagon has recently
developed a handheld laser scanner that can also be installed on an autonomous drone. The Leica BLK2FLY captures real-world data including photographic imagery to create a point cloud. In terms of defence applications, this is particularly useful for investigating things such as improvised explosive devices workshops and arms factories.
Another innovation is our HxDR cloud-based storage, visualization and collaboration platform. HxDR automatically uploads geospatial data that is then processed to build a point cloud and a textured 3D mesh – the same as you might see on commercial mapping systems. This gives the user incredibly realistic textured buildings with all the external facades embedded on each building and is perfect for
classifying objects and vegetation on the ground and creating digital twins.
This year, Hexagon introduced LuciadCPillar for Android, a platform for developing mobile applications for dismounted soldiers in the field, where situational awareness is critical. It enables developers to build applications with 2D/3D views, featuring military symbology and supporting many geospatial data types, including vector data, raster data, elevation data, point clouds and 3D meshes.

The United Kingdom, partnered with Estonia, is hosting the European Office of the Defence Innovation Accelerator for the North Atlantic (DIANA), a new mechanism for NATO Allies to accelerate the development of dual-use deep-tech solutions that address critical defence challenges and contribute to Alliance deterrence. We ask Ben Wallace , Secretary of State for Defence, to explain why innovation matters to Allies, and why this is a game-changing moment

The UK and our allies are clear that innovation is critical to maintaining strategic advantage as the rapid advancement of technology brings both opportunities and threats.
NATO is launching the ambitious Defence Innovation Accelerator for the North Atlantic (DIANA) initiative, as well as the NATO Innovation Fund (NIF), at a critical moment for
Euro-Atlantic security. Russia’s illegal invasion of Ukraine has shattered peace in Europe, but it has also shown how committed and united the international community is in supporting Ukraine to defend its sovereignty and territorial integrity. We stand with them in the face of Russian aggression, and are inspired by their heroism and resilience –particularly Ukraine’s adaptability, which is core to maintaining advantage. Whether this is the use of 3D printing to create stabilizing fins for grenades aiding deployment from drones, or the rapid development of phone apps to support trusted reporting of crowd-sourced intelligence, their actions have further demonstrated the importance of innovation and the rapid integration of civilian and military technologies to deliver military effect. We must follow this example and ensure that we can
invent, prototype and integrate new capabilities at the pace of relevance.
Dual-use technology is vital for this innovation revolution. Defence is no longer the technological driver, and most disruptive solutions now come from the civil sector. It is critical that defence gains access to the widest possible network of innovators –especially those who have not worked with defence before – to develop and deliver solutions.
Ukraine has shown that with a clear demand signal, defence, the private sector and the public can unite around a common goal. We must be clear to industry about our problems, outlining the capabilities we need and are looking to invest in, to encourage private investment in these areas. In the UK, the Defence and Security Accelerator (DASA) does this through setting out clear problem statements for industry to
put forward their ideas. We believe DIANA will replicate and enhance this approach through Alliance-wide challenge statements.
It is no good supporting innovators if we can’t adopt their ideas in time. Making it easier for innovators to engage with defence must be a critical priority for Allies, and ensuring we have agile frameworks that support rapid acquisition is key to success. I’m deeply encouraged to see the priority that NATO is giving to agile acquisition in the ‘DIANA Rapid Adoption Service’. Allies need to build towards integration and interchangeability, working together seamlessly to ensure that we can outpace adversaries; support
training of each other’s forces on shared platforms and technology (as we have done with Ukraine); and increasing the adoption of new technologies across NATO.

It is for these reasons – the need for timely adaptability and innovation, to provide clarity on our demands of the private sector, and to harness dual-use technology – that we, here in the UK, are proud to be playing such a key role in DIANA and the NIF.
On 30 March, the first DIANA Regional Office opened in London, with a further hub in Tallinn, Estonia, opening later this year. DIANA represents a game-changer for NATO, bringing together industry,
government and academia from across the Alliance, leveraging a transatlantic network of accelerators and test centres to support the foundation, growth and success of start-ups working to bring the best of civilian innovation to defence. In uniting the best and brightest innovators across the Alliance, DIANA will ensure that we are well-prepared to protect the Alliance’s nearly one billion citizens. After the launch of its pilot activities in June 2023, DIANA (complemented by the NIF) will become essential to delivering NATO 2030, helping the Alliance develop the capabilities needed to deter and defend against existing and future threats, enhancing security within the Alliance and beyond.
“It is critical that defence gains access to the widest possible network of innovators – especially those who have not worked with defence before – to develop and deliver solutions”
Sectra has been active in the field of information security for 45 years, and its crypto equipment is in service with the Dutch Armed Forces and most other EU nations. Here’s how Sectra enhances information and data security
since 2004 and supports both military and civil users in the protection of their information. The company’s security products are also currently used by government authorities and defence departments in most EU member states. NATO has been using Sectra’s solutions for secure communications since 2018.

Can you describe the origins and utility of Sectra’s Tiger solutions range?
IP networks, including satellite, fixed and mobile networks, for all types of communications.
What, in your opinion, is the core of information security?
Managing Director, Sectra Communications BVWhat types of sectors does Sectra operate in and what does it offer each of them?
Sectra helps governments, defence forces, the public sector and multilateral organizations such as NATO and the EU to secure their communications against eavesdropping. The company offers high-assurance communication systems for secure voice and data communications. These solutions are certified by security authorities in various nations, including the Netherlands as well as by NATO and the EU.
How long, and for whom, has Sectra been enhancing communications security in the Defence sector?
Sectra has 45 years of experience working with high-assurance communication systems, specialized for the defence sector. The company has been a market leader in secure communication in the Netherlands

The high-assurance mobile encryption solution, Sectra Tiger, was approved for the SECRET classification level in 2007 by the Dutch security authorities, and has since enabled the Dutch defence forces to use the solution for communicating highly classified information. Today, the quantumresilient Sectra Tiger is approved up to the classification levels NATO SECRET and EU SECRET. It also has several national approvals. The phone enables the user to share classified information through encrypted speech, messaging and data transfer. It also offers high availability as it can utilize a variety of
The cornerstone of information security is cryptography, and the reason is simple: if sensitive information falls into the wrong hands, it can have serious consequences. Cryptographic algorithms provide the ‘recipe’ for making information unreadable for anyone but the intended recipients. The security of today’s cryptographic algorithms is based on mathematical problems that we assume are difficult to solve. Put simply, if the mathematical problem is difficult to solve, the encryption is difficult to break.
Why is it important to have a quantum-resilient solution?
Nowadays, defence organizations demand quantum-resilient solutions because they need to uphold their digital sovereignty not only today, but also in the future. Crucially, in the future, quantum computers will have the capability to perform
Jeroen de Muijnckcertain types of calculations much more efficiently than today’s computers. Consequently, these quantum computers could pose a threat to current encryption methods, and quantum-resilient solutions are therefore perceived to be one of the key traits of futureproof confidentiality.
What challenges does Sectra foresee for defence organizations in the future?
The increasing adoption of digital technologies will lead to a new level of operational capabilities and effectiveness among defence organizations. There will undoubtedly be a major increase in the amount of data that needs to be communicated, stored and processed – partly because of a growing use of sensors and the huge amount of information they will produce. In addition, there will be challenges in keeping all of this data confidential while still ensuring low latency and high availability. It will also be crucial for an efficient operational organization to be able to trust the information they receive.
Secure communications will therefore be critical for these challenges and for improved interoperability and autonomy, which in turn are vital when it comes to building relationships between different organizations, systems and allies. As defence organizations become more reliant on digital technologies, the need for secure and robust communication systems with high availability will be more important than ever.
What is Sectra’s innovation philosophy and how does it keep its products and services ahead of the evolving threats?

At Sectra, we are proud of our academic heritage and continue to nurture our relationships with research institutes, working together on research projects, sharing resources and tapping into the wealth of knowledge that these institutions possess. This partnership with academia ensures we have access to the latest development and findings in our field. Our strategy is also based on allowing customers’ needs, combined with Sectra’s knowledge of trends and technology, to influence the progress and renewal in our customer offering. We firmly believe that combining research, close cooperation with customers and employee development is the key to staying ahead in a rapidly changing world. In short, by fostering a culture of continuous learning, we ensure that our collective expertise remains
at the forefront of the secure communications industry, enabling us to anticipate and counter emerging threats effectively.
Our commitment to working closely with our customers, alongside our academic partnerships and our employee development culture, forms the cornerstone of Sectra’s innovation philosophy. Our corporate culture encourages us to constantly seek improvement and innovation in every part of the organization. By maintaining strong ties with academia and promoting a culture of learning, we ensure that our products and services are always one step ahead, providing our customers with the most efficient and reliable solutions to safeguard their interests.

Kajsa Ollongren, Minister of Defence of the Netherlands, highlights the efforts under way to drive innovation and underlines the need for collaboration on both a national and international level

NATO is facing and will continue to face multiple threats. The war in Ukraine is a stark reminder of that. In the coming decades, technological developments will fundamentally change military capabilities and the way they are employed. We therefore have to ensure that our armed forces remain technologically advanced and operationally relevant. This requires major investments in research and technology (R&T) and an acceleration of military innovation.
The ultimate purpose of these investments is to ensure that our armed forces have the very best military capabilities in 10 to 15 years’
time. Simultaneously, we want to ensure that we can implement dual-use technologies in the military domain much faster than is currently the case. Our Defence White Paper (DWP) stresses the need for the swifter introduction of dual-use technologies in the military domain through concept development and experimentation (CD&E), with our innovation centres leading the way. The defence sector, which includes R&T organizations, the defence industry and non-traditional knowledge and innovation partners, is indispensable for achieving this goal. Against this backdrop, we are developing and strengthening
knowledge and innovation ecosystems in close collaboration with public and private partners, and are focusing on critical technologies.
The ecosystem approach is already being applied with regard to data science and artificial intelligence (AI), key technologies that are central to numerous innovations and are broadly applicable. Data science and AI make high-tech warfare possible and offer numerous opportunities for optimising military and business operations through the processing of huge amounts of data into
“The ecosystem approach is already being applied with regard to data science and artificial intelligence”
relevant information. However, these technologies also raise challenges with regard to ethical, legal and societal aspects, such as discrimination and bias. To address these challenges, the Netherlands organized the first ever summit on Responsible AI in the Military Domain last February where we started an international dialogue with academia, civil society and industry on the responsible use of AI in the military domain. The concept of meaningful human control is crucial to ensure the responsible use of data science and AI by the military. Soon we will publish our Data Science and AI Strategy in which these ethical, legal and societal aspects are a key objective. For both research and development on both
technological developments and ethical, legal and societal dilemmas, we work with partners from industry and knowledge institutes in a balanced ecosystem. A prime example is the Netherlands AI Coalition, a public-private partnership consisting of 800 organizations, of which 80 specifically focus on defence. On the basis of this partnership, we recently launched ELSA Lab Defence, a co-creation environment in which public and private parties will focus on academic research on ethical, legal and societal aspects of AI within the military domain with the main goal of furthering the debate.
Our military innovation centres are playing a key role in solidifying the
ecosystem approach. The measures set out in the DWP have given them the capacity and the means to extend their collaboration with public and private innovation partners. This has enabled them to develop a substantial innovation portfolio that consists of individual CD&E projects and activities that aim to develop and strengthen collaboration with leading Dutch innovation hubs, including Brightlands and Brainport. By investing in new technologies, these hubs strive to develop new high-tech innovations in continuous collaboration with companies, research and development (R&D) organizations, schools, universities and start-ups. These hubs therefore provide early access to new

ecosystems, high-tech development, knowledge and talent.
Close collaboration with the military is a unique opportunity for their partners. In addition to contributing to public safety, innovation in a military environment provides unique development opportunities, a solid partnership and possibilities for experimentation in a highly operational military context. This intensive collaboration is key to essential new solutions and sustainable innovation.
The implementation of our Defence Space Agenda (2022) also builds on the ecosystem approach. With this agenda as a guideline, Dutch military space capabilities will be further developed over the next 15 years. Partners work closely together to implement the agenda, focusing on three niches that we are good at: constellations of small satellites with payloads for various missions, space situational awareness via the further development of our Smart-L Multi-Mission radars, and laser satellite communications. With the implementation of the Defence

Space Agenda, we also support the development of the European space agenda as well as the development of space as the fifth NATO operational domain.
The push for closer collaboration does not stop at the national level. This has to be a joint effort. Innovation and international collaboration, including in the research, technology and innovation domains are crucial. The challenges ahead of us are much too big to face alone. We have to work together much more closely to maintain our technological edge. That is why we actively support EU and NATO initiatives that will help us to provide our armed forces with the superior capabilities that they need.
We are a strong contributor to the European Defence Fund (EDF). Dutch research and technology institutes and companies are already participating in 56 EDF projects. Furthermore, we strongly support
other European initiatives, including the recent establishment of the Hub for EU Defence Innovation (HEDI). These initiatives strengthen the European Defence Technological and Industrial Base and therefore increase European strategic autonomy. European defence materiel collaboration, the scope of which includes manned and unmanned systems, combat vehicles and helicopters, is also high on the Dutch agenda. We actively support the Defence Innovation Accelerator for the North Atlantic (DIANA), a NATO innovation initiative.
DIANA will include two Dutch defence test centres as well as high-tech ecosystems, companies, universities and other parties that focus on Emerging and Disruptive Technologies (EDTs). Moreover, we have joined the NATO Innovation Fund (NIF), which will invest in high-tech companies that focus on EDTs and deliver capabilities for the defence domain. In 2022, the Netherlands was listed in the top five of the global innovation index. The headquarters of the NIF will be established in the Netherlands. This is very much in keeping with tradition in that, for decades, our scientists have closely collaborated with counterparts from other Member States in the NATO Science and Technology Programme of Work.
Our perspective is clear. Maintaining the technological edge requires long-term commitment to innovation. This means investing in defence R&T and bringing dual-use technologies into the military domain with greater speed, while acknowledging the critical and growing role of EDTs. First and foremost, however, we have to work with our public and private partners in ecosystems at the national and international levels.

After more than 30 years in the British Army’s Royal Corps of Signals, including active service in Afghanistan, Justin Hodges, Business Development Lead at BT Defence, understands the importance of resilient networks and reliable command and control. He reveals how BT’s efforts to create a converged network utilizing terrestrial and space-based technologies such as 5G, quantum technologies and artificial intelligence, could offer the reliability the military is seeking

Adastral Park, BT’s cluster of high-tech telecommunication and technology companies based in Suffolk, is at the heart of the UK’s digital ecosystem. It combines a national operation centre, test facilities and a global research and development (R&D) unit, all set among a thriving community of collaborative technological innovators. The park is home to BT’s innovation labs and Innovation Martlesham (an established and growing cluster of circa 150 high-tech ICT companies), as well as educational initiatives such as the Tommy Flowers Network. For us,
R&D is all about enabling and nurturing robust supply chains through the judicious and precise use of patents and licensing. We don’t manufacture, instead we try to stimulate innovation, development and production within our supply chains.
BT has been in space since the very beginning. We worked with NASA on their Telstar 1 satellite programme in the early 1960s. Back then, BT was part of the General Post Office (GPO), and through the GPO we were one of the founding members of the Intelsat organization, which was
established in 1964 to develop global satellite communications.
As part of my role as defence space lead, I helped BT develop a six-pillar space strategy to promote the company as a global thought leader in space. The strategy is built around the belief that terrestrial and non-terrestrial convergence will be a key factor. As you might expect, innovation sits at the heart of this strategy, focused on collaboration to provide ubiquitous connectivity, flexible and ultraresilient services as well as to enable the creation of new
downstream applications, services and business models. Our strategy is based on the understanding that there is no single technology that can meet our customers’ total needs and requirements. You have to have a blend.
Perhaps one of the key things is the convergence of 5G with space technology. BT has been collaborating with OneWeb to demonstrate the convergence of Low Earth Orbit (LEO) satellite

constellations and infrastructure into 5G architectures. It is early days, but initially, the role of LEO might be to support remote locations and low-latency use cases, such as autonomous machine-to-machine applications. It is also likely that we will see emerging trends in direct device technologies, for instance the Internet of Things (IoT) and along the lines of Apple’s satellite phone functionalities.
Dual use is key. Commercial markets will create the impetus for the
adoption of those sorts of innovations. The wider market volumes are going to establish the availability of novel devices and services that defence can benefit from within their increasingly constrained budgets. That is one of the strengths a large organization such as BT has, in that we operate across different industry sectors and understand how new technologies can be adopted not just technically, but also at the prices that provide the best value for money for defence organizations across the NATO Alliance.
Not surprisingly, due to my background in military communications, one focus is on command and control. At its core, it is the connection of people with people, upon which military organizations tend to concentrate. However, what is not yet really getting the attention it deserves is massive machine-to-machine communication, such as IoT communications and timesensitive, mission-critical
“AI, quantum and 5G are without doubt going to disrupt and revolutionize telecommunications, not just on Earth but in and from space as well”
applications. Network convergence, including 5G, Satcom and a combination of both will inevitably play a large role in solving these challenges.

Artificial intelligence (AI) will also be vital. In fact, we are already using AI in our infrastructure and architectures. Networks have been able to reroute themselves to solve outages for some time now, but we see AI being able to create selfhealing networks that can not only spot threats, but can actually predict failures before they manifest themselves. Although we have also been using AI to enhance cyber security, and some of our cyber applications are well advanced, in truth, we are still at the beginning of understanding how AI will be able to deliver a more resilient network. From a defence perspective, it is really important to learn how to apply those sorts of technologies as they are another way of delivering cyber and electro-magnetic resilience.
While we have been progressing our understanding of AI, we have also been collaborating at BT and Toshiba to build the world’s first commercial quantum-secured metro network across London. Following on from a successful research quantum key distribution (QKD) project with partners, we have installed a network into existing exchanges and switches in the London area. The aim of the first commercially operational quantum-secured metro network is to understand the practicalities of bringing a quantum-secured network into a live service. And, in terms of space and quantum, we have been working with an Adastral partner company, Arqit, on QKD, which we see as being highly applicable in the LEO technology arena.
Just below LEO, within the Earth’s atmosphere at about 60,000 ft (18,288m) there is another layer that BT sees as having enormous potential for dual-use communications applications, and
that is via high-altitude pseudo satellites (HAPS). BT, along with another Adastral partner, Stratospheric Platforms, is investigating the installation of 5G technologies on HAPS with potential applications for a wide range of sectors, including agriculture, disaster relief, military maritime and remote locations. We are very excited by this as we think there are certain types of HAPS capable of exploiting 5G, which are entirely feasible and economically viable.
These emerging technologies –AI, quantum and 5G – are without doubt going to disrupt and revolutionize telecommunications, not just on Earth but in and from space as well. Most of the development will stem from the research and development work in which commercial companies will invest, but the military will also benefit from this effort. The key for them is understanding what is available and then being able to adopt it efficiently, effectively and quickly.
Thinking in terms of digital transformation is a critical mindset in the pursuit of Multi-Domain Operations (MDO)
A data-centric approach is key. Improved data interconnectivity and interoperability across all the operating domains (air, land, sea, cyber and space) are key elements for the successful adaptation towards MDO. Successful MDO will enable the synchronization of military activities to achieve effects across all warfighting domains and throughout the various levels of command.
and will increasingly be, a key enabler for defence systems.
Airbus is paying a lot of attention to AI from both a technological and an ethical perspective. Creating a common understanding around AI is a priority we share with our customers. An Airbus-led consortium has been contracted to undertake the so-called Air Combat Management System (ACMS) project specifically to address that issue. In this study, we are analyzing how AI-enabled systems will support and speed up air operations along the full command and control (C2) cycle.
Digital Transformation has long ceased to be a novelty, but there is a huge difference between knowing how important digital transformation is and understanding why we need to do it, let alone how to implement it.
For NATO and the Alliance forces, the integration of emerging and disruptive technology will be extremely difficult without a digital military industry. Delivery of ever more complex solutions through cooperation with military and civil industry will take ages if armed forces do not push themselves towards digitalization.
This is not about replacing old technologies with new ones, nor is it solely about high volumes of data, or hiring data scientists, or even trying to copy Silicon Valley. It is about ensuring that key decisions, actions and processes are strongly influenced by data-driven insights. That means thinking ‘digitally’ from the outset –even in a defence context.
At the moment, most of the raw data that emanates from a host of different sources and sensors are not fully exploited. This is due in part to the fact that legacy technologies focused only on the prime purpose they were installed for, and only for a limited number of users. However, digital transformation drastically changes the volume of available data as well as their potential and the number of users that can access them. This, therefore, offers new challenges relating to the data: processing, fusion, transmission, storage and exploitation among other things. That said, the potential to get relevant information from the data increases as the processes to manage them from end to end are digitalized.
AI is a topic of growing importance in our daily lives and in our business activities. With significant technological leaps expected in the coming years and decades, AI is also,
We must not forget that AI solutions are only as good as the data fed into the system. That is why it is essential to implement developments together with our armed forces colleagues so that we can create and grow sufficient trust in AI-supported decision-making.
At Airbus we have established an IT infrastructure architecture that enables the onboarding of new technologies (AI, quantum, cloud) in an open-system environment.
Our Combat Cloud (CC) is not a monolithic stove pipe – it brings together and connects different domains and their corresponding combat clouds with regards to information flow and decision support within and across the domains. We are imagining an Air CC where all air assets are orchestrated and seamlessly connected to the
 SVP Head of Intelligence, Head of Connected Intelligence Germany, Airbus Defence and Space
Harald Mannheim
SVP Head of Intelligence, Head of Connected Intelligence Germany, Airbus Defence and Space
Harald Mannheim
other domains and their respective combat clouds through the Multi Domain Combat Cloud (MDCC) system of systems. MDCC acts and behaves as ‘the brain’ of this IT organism managing the user/ provider relationships.
End-to-end security and cyber resilience are essential in this collaborative engagement. Only a fully securely connected cloud environment can enable all actors to get real-time updates of the situation and decide on the actions to follow.
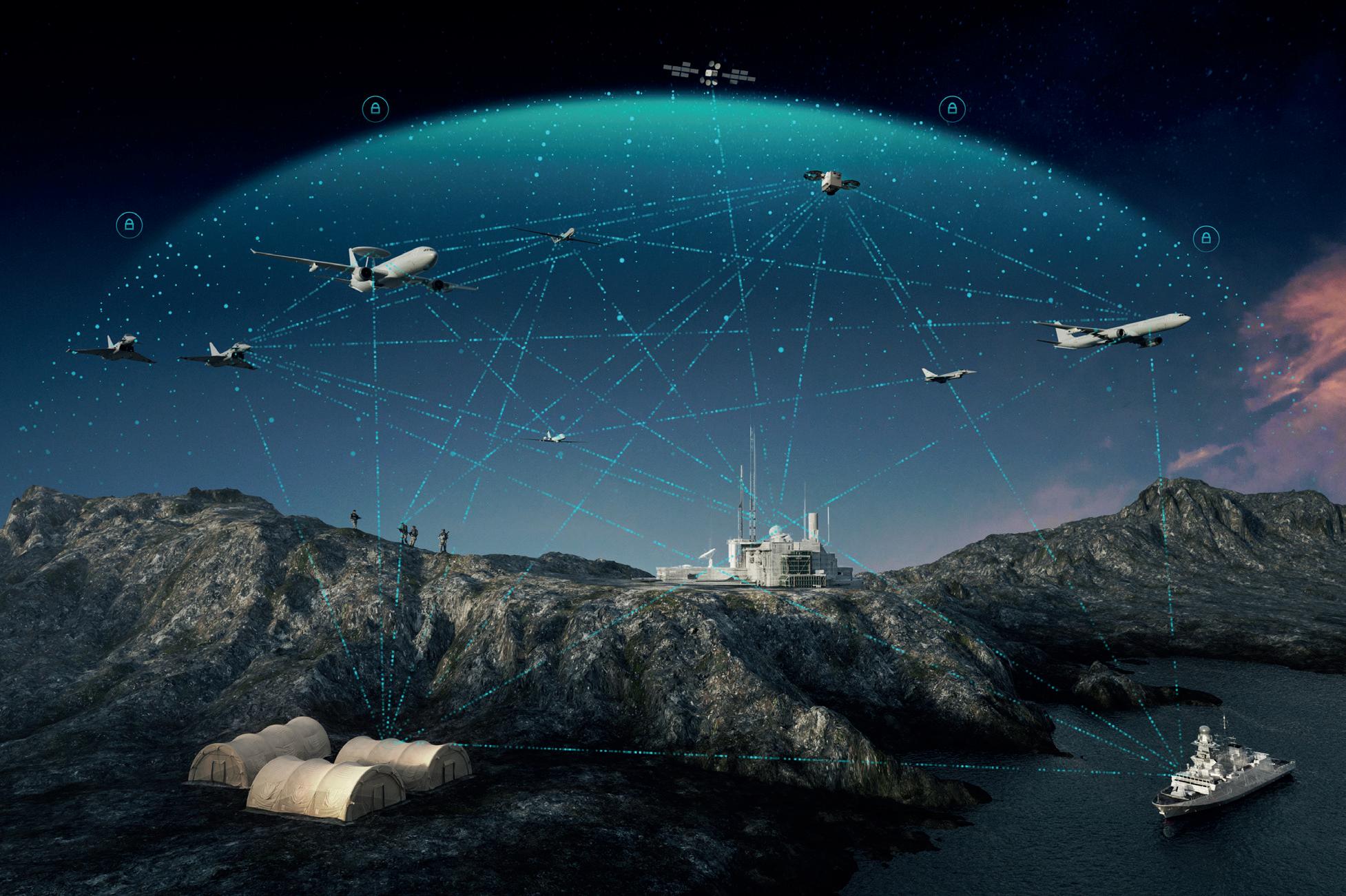
When it comes to implementing new technologies, we must be aware that we need to tackle operational challenges with a system-of-systems design which requires, on the one hand, a broad common technical baseline while keeping, on the other hand, sufficient flexibility to fulfil domain-specific requirements.
Airbus teams are already working jointly with customers to bring
operational systems to the next level of interoperability: collaboration. With today’s state-of-the-art technology, it is possible to network existing systems and, therefore, improve coordination and cooperation. The next level of technology will be a service-oriented architecture. Existing processes and structures will be fundamentally impacted, since many procedural steps – that are currently executed consecutively – will be carried out in parallel in the future. By enriching various methods of AI, the warfighter will be supported through the reduction of workload, not replaced.
For example, edge-to-edge sharing of data/information is made possible thanks to a neural network of different systems capable of exchanging data/information with diverse entities. This will result in enhanced collaboration by the provision of services between each system and entity. With our ready-fordemonstration IT infrastructure we have realized a fully transparent operational picture that is available at
all levels of command and fully tailored to the mission.
Our way forward is to adapt current systems in a progressive manner to the cloud environment to make them ‘cloud ready’, and then develop them natively into this cloud environment so they become ‘cloud native’.
With Airbus being part of programmes and studies such as Alliance Future Surveillance and Control for NATO, Future Combat Air System for EU nations and Air Combat Management System for Germany, it’s a good example of the diverse capabilities for the development of system of systems where national and NATO C2 demands need to be balanced. There is no final answer to an ideal level of technology, but we are confident we have arrived at what is needed for a logical and workable solution.
www.airbus.com/en/products-services/ defence/multi-domain-superiority/ multi-domain-combat-cloud
The TOPFAS–BMD scope of work includes analysis, design, development, implementation, maintenance and support for a new, enhanced, NATO-owned TOPFAS Application Suite that can support the expansion of NATO’s Ballistic Missile Defence (BMD) capabilities.
Simon Michell asks the NCI Agency’s TOPFAS team all about it

The objective of the TOPFAS Application Suite is to provide NATO operations planners with software tools to support their planning and assessment activities. Can you describe the TOPFAS Application Suite in more detail?
The TOPFAS acronym stands for Tools for Operational Planning Functional Area Service. In other words, the data and planning support tools for NATO operational planning. It is a suite of software applications (or apps) consisting of desktop, serverhosted and web applications. Together, these can be employed to support the management, analysis, planning, execution and assessment of NATO operations.
TOPFAS includes six application areas, each supported by one or more TOPFAS application. The apps are complemented with general-purpose or common applications as well as configuration and management applications.
As you would expect, TOPFAS includes modern user interfaces that are appealing and user-friendly with the incorporation of advanced graphical user interface commercial libraries. The entire suite currently comprises a collection of desktop apps known as TOPFAS Desktop. These are an assortment of web applications referred to as TOPFAS Online, as well as the most applicable Microsoft Office utilities (Excel, PowerPoint and Word) and a range of system administrator applications for data, user/configuration management and service monitoring.
How has TOPFAS already enhanced NATO capabilities?
The TOPFAS Application Suite has been designed to cover a range of apps within the NATO Crisis Management Process domain, including war, peacekeeping and humanitarian aid. As you know, the NATO Crisis Management Process is a

six-phase consultation and decision-making process that can be adapted to any crisis situation. This streamlined process enables the relevant staff and NATO Committees to coordinate their work and, crucially, to submit comprehensive advice to the North Atlantic Council (NAC) in a timely and compelling way.
Within the NATO Crisis Response Process domain, the TOPFAS Application Suite serves multiple, distinct communities of interest simultaneously. To do this, each app within the Suite achieves a distinct objective and offers specific capabilities for the tasks at hand.
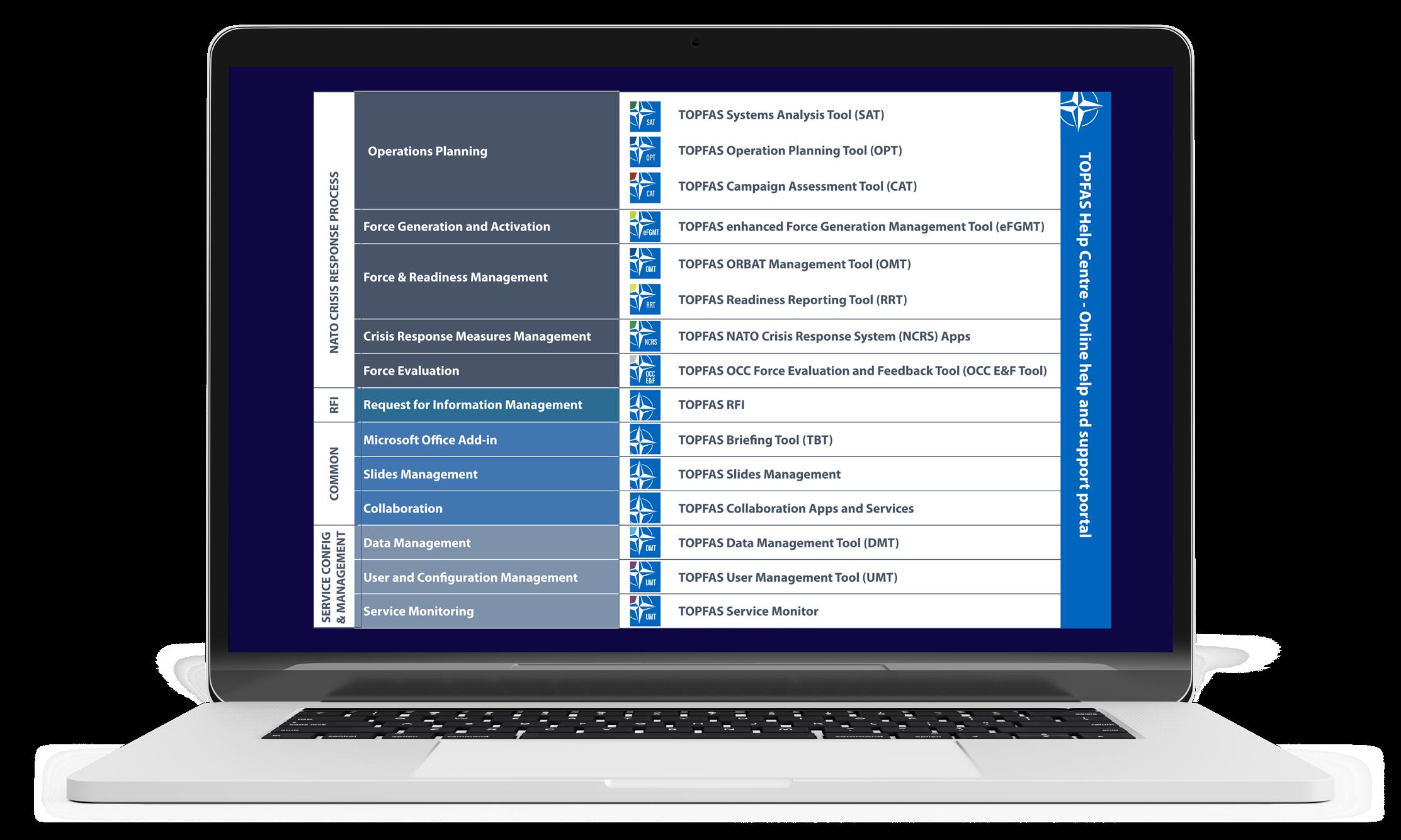
How does TOPFAS help NATO operators support NATO operations?
TOPFAS enables real-time collaboration on a set of required products between HQs, with information updated instantaneously. The suite of applications directly supports the Allied Command Operations Comprehensive Operations Planning Directive process. To help explain this more clearly, I can offer up these two use cases.
In the first use case, the ‘Operations Planning’ (OP) application area consists of apps providing an integrated environment to represent and model the engagement space (area of operations). This helps to plan potential response options, develop and implement adequate operational strategies and solutions as well as assess their progress over time.
In the second example, the ‘Force Generation’ process is initiated once the OP process has defined its operational requirements expressed through the
Combined Joint Statement of Requirements. The process continues for the whole duration of the operation and consists of generating and managing the capabilities for follow-on rotations. It is critical in ensuring adequate resources for a particular mission.
The recently announced BMD Increments 1 and 2 will add new BMD capabilities and enhance the current baseline of the TOPFAS Application Suite. Once complete, how will the TOPFAS-BMD scope of work enhance the Alliance’s ability to defend its territory?
The key functional areas for this expansion cover the support for the information exchange between the political and military organizations in relation to BMD activities, the so-called Pol-Mil consultation process, which takes place between the strategic commands, the NAC and the Military Committee. Increments 1 and 2 will also enhance protection of the military and civilians.
Training and exercises are key to NATO’s success and so the increments will support education and training, as well as exercises and Evaluation Functional Services for the BMD capability. They will also provide interfaces and integration with Intelligence Functional Services. The enhanced TOPFAS will also facilitate integration with the NATO platform and other functional and core services.
When will the TOPFAS Application Suite be implemented with the NATO BMD infrastructure?
The TOPFAS suite itself has been operational since 2010. The BMD specific enhancements you refer to will be delivered in three work packages (WPs). If all goes according to plan, the capabilities developed under the first WP are projected to become available in 2025. The second WP, which will extend and evolve these capabilities, will be released in 2027. The third optional WP comprises all activities and services for the maintenance and support of the TOPFAS Application Suite baseline from Final System Acceptance up to five years.
“The TOPFAS Application Suite has been designed to cover a range of apps within the NATO Crisis Management Process domain, including war, peacekeeping and humanitarian aid”
Security and connectivity should not be mutually exclusive, and infodas is on a mission to ensure the security features of a product are accurately communicated
environment. CDS, which are also known as Boundary Protection Devices, are intended for sectors where you need to be rigorous about protecting classified data. That is why, in these high-security situations, it’s crucial for users to understand the meaning and implication of every label on a datasheet and in product presentations. Even the most experienced users can get a bit lost when they see labels such as “Certified up to EALx” or “approved up to”. These labels can hide a whole world of misleading information. This is where my team and I get to work; we help users to successfully navigate this context.
As an applied maths and computer science graduate, I always wanted to fulfil my academic interests while contributing to society in a meaningful way. Therefore, I entered the world of IT security, as a way to develop solutions that ensure the defence of sensitive information and systems, while exploring the affinity between cryptic analysis for IT security products and mathematics.
At infodas, I have been Lead on the Product Certification Team for the past four years, a role that enables me to help companies navigate the world of certifications and approvals, particularly with Cross Domain Solutions (CDS).

How do you combine your passion for mathematics with certifications and approvals in the world of CDS?
CDS are all about keeping top-secret information in a controlled and secure
The main difference between a mandatory Type Approval and a Common Criteria (CC) certification isn’t so much about what they actually examine, but more about their purpose. If you want to protect classified government data, you have to go through the Type Approval process for that country or indeed for NATO/EU applications. However, if you’re using it in the private sector, the ISO 15408 Common Criteria is the internationally recognized standard to confirm the security of our products, backed by assessments from independent experts.
A successful CC certification can also help other countries secure their classified data. Experts worldwide can read the certification report and see if the product’s evaluated security functions meet their own needs. The report includes all sorts of information, such as whether the source code was
looked at, how deep the independent tests went, and the extent of vulnerability analysis done by independent testing labs.
There are lots of names and certifications out there. How is it possible to know you are looking at the right information?
When it comes to CC certifications and Type Approvals, it’s important to understand the Target of Evaluation (TOE) and the Objectives of the Operational Environment, which support the security behavior of the TOE. Let’s break it down. Imagine a CDS claiming to be ‘Certified CC EAL7’. Sounds like it has the highest level of security on the CC EAL scale, right?
Well, the reality is a bit more complicated. This claim can only refer to a specific hardware component, likely an optical separator within the CDS. As soon as software is involved, mathematical proof of security will no longer be possible as software can always have unknown vulnerabilities. Therefore, any components outside of this optical separator, especially software implementations, are most likely not included in the certification activities. So, even though the perceived level of security (EAL7) is indicated, it only applies to that one component. Other subsystems like the operating system, proxies and filters are not covered and are not even mentioned as Objectives of the Operational Environment of the TOE. Ideally, during the certification process, the Objectives of the Operational Environment of the TOE should have been checked for plausibility by an independent lab.
Lead Product Certification, infodas Hanns Benigno GroeschkeThe devil is in the details, isn’t it? Indeed, and this ‘devil’ can change depending on the scenario. Consider two types of CDS: Data Diodes and Security Gateways. The majority of Data Diodes (also known as unidirectional CDS) use optical separation to allow data to flow in one direction only. However, this technology has limitations; it only supports one-way protocols, so there is no return channel. It also has speed and throughput limitations.
The optical separator inside a hardware diode is easy to certify because it’s a simple component. However, in CDS optical components are part of a more complex architecture that includes an operating environment and proxies. Sometimes, these proxies are implemented outside the diode box, which means they are separate systems not covered by the certification. It’s important to understand that the security of the entire architecture depends on the weakest link in the system. Remember, a high-certification of one component doesn’t define the security level of the whole system; a vaulted door doesn’t hold any value if your room has thin crystal windows.
Bidirectional CDS (aka Security Gateways) are an evolution of Data Diodes and are designed to support bidirectional protocols, opposed to the one-way nature of the diode. However, enabling bidirectional data flow introduces new challenges. This requires validation and filtering of the data that comes out of the high-security domain to
enforce security policies and prevent accidental leakage of high classification information. Filtering plays a crucial role in this process, as it inspects each piece of transmitted data; However, optical separators cannot perform filtering, so a different approach is needed. Some optical-based CDS implement bidirectional features by stacking two unidirectional Data Diodes in opposite directions. But, we at infodas strongly discourage this architecture for several reasons.
Firstly, filtering capabilities are allocated externally, potentially on systems outside the CDS box which were not part of the security evaluation. Secondly, having two diodes in opposite directions with communication between them introduces potential leakage through external components. Simply stacking two data diodes and hoping for secure communication between them doesn’t guarantee security.
Additionally, some CDS claim EAL certification because they are based on a certified data diode. However, combining two Data Diodes and adding other components for bidirectional functionality doesn’t impact the security requirements beyond the original unidirectional solution. It’s like saying a car is roadworthy because one of its safety belts is certified.
It’s crucial for professionals working in high-security domains like CDS to accurately communicate the security features of their products. Writing clear and informative claims is a responsibility that shouldn’t be taken lightly.
How important is raising awareness of this issue?
Very. At infodas, we decided to do away with the hardware separation and to make our CDS secure by design in a holistic approach, embracing the hardware, operating system and software. This approach is of course much more challenging than the ‘fibre-optic–based one’, but we are convinced that this is the right way to go, and we have confirmed it through the numerous Type Approvals and certification processes that our products achieve and have maintained over our more than 40 years. We work daily to make our motto, ‘Connect more. Be secure’, a reality for our customers because security and connectivity should not be mutually exclusive. We work constantly to improve awareness about the potential for CDS and we see the results in the satisfaction of our customers. That is what I am passionate about. That is what makes it all worthwhile. Scan



Every year the NATO Cooperative Cyber Defence Centre of Excellence holds one of the largest cyber security training exercises in the world – Locked Shields. Lara Vincent-Young asks NCI Agency Exercises and Awareness Staff Officer, Jean-Sebastien Dorne about this year’s iteration of the exercise and why it is important for the NCI Agency to participate

Locked Shields is a Blue Team versus Red Team international live-fire cyber defence exercise. It involves a near-reality scenario in which 24 Blue Teams, made up of Allied and Partner Nations and NATO staff, compete to defend networked systems that are under attack by highly skilled hackers who comprise the Red Team.
The exercise is a unique and formidable opportunity for national cyber defenders and crisis response specialists to practice protecting IT systems and critical infrastructure such as 5G, satellite communications and industrial control systems. The Blue Teams are also tasked with executing strategic decisions, solving forensic, legal and media challenges and reporting incidents. Jean-Sebastien Dorne, NCI Agency Exercises and Awareness Staff Officer, offers an insight into this year’s gruelling episode.
The level of ambition for this exercise has increased exponentially since its first iteration in 2010. It started with Blue Teams of 10 people and now we are required to have at least 60 to 70 people, with some teams reaching 130 people. This year there
were more than 3,000 participants from across 38 Allied and Partner Nations.

Because the NCI Agency is customer funded, it has become increasingly difficult not only to justify, but also to find enough cyber experts to have a fully fledged team that could be up to the task of participating in Locked Shields as a single entity. Consequently, for the first time ever, the NCI Agency joined forces with Denmark and the United Kingdom’s Ministries of Defence to form a joint team. We brought together the best of each team to make up the required capabilities.
In addition, Locked Shields is very comprehensive and has moved away from the purely technical exercise it once was. In recent years, it has also included strategic and operational inputs with a variety of activities involving media and legal experts. They are posed realistic challenges coherent with the ongoing attacks targeting the Blue Teams and the overarching geopolitical strategic concept that is feeding the exercise. Not all Blue Teams can afford to have a media and/or legal team, but we were lucky enough to have some colleagues from the NCI Agency Communications
Office and Legal Office join us in person. This facilitated efficient collaboration and it was refreshing to work together so closely.
What makes Locked Shields a great training opportunity for the Agency?
Locked Shields is technically very challenging, so it is a really valuable environment for the NCI Agency to train in. This was our first time participating as part of a joint team so we learnt a lot from one another and benefited from each other’s best practices. We had all the ingredients for the team to manage stress and resource scarcity, prioritize and address problems, and come up with solutions under pressure. In this way, I think there are very few, if any, cyber exercises that compare to the calibre of training you receive at Locked Shields; it is the perfect opportunity to train together during a cyber crisis.
At the same time, building a team with people who do not usually work together can be challenging. Interoperability is a key facet of NATO operations and it is important to continually engage with our allies. You have strong, highly skilled individuals working towards one objective, so you have to adapt very quickly to create a beneficial environment for people to work together. That was brilliantly done by our team leader, who had the skill and patience to command our team, resulting in effective synergy and a positive atmosphere. Next year, we will definitely use the same concept of teaming up with other entities.
How does Locked Shields help the Alliance prepare for crises?
These exercises are very important for the Alliance because we learn to defend our networks together – together being the operative word here. This is not an easy task to do with recently formed teams, as it takes time to adapt, learn and align the processes.

The highly complex and diversified conditions mirror what you would have in a modern environment, mixing civilian and military assets that you have to protect. To put it into perspective, there is a very high pace of cyber incidents, about 9,000 over two days. It is extremely demanding and very easy to get lost if you fail to keep up with the pace. Therefore, prioritization is imperative. We cannot deal with all the cyber incidents as well as the misinformation and legal concerns. Thus, we learn how to differentiate between random and targeted cyber attacks and identify the most pressing matters.
The overwhelming feedback was that everyone was very happy with the exercise and ready for the next one. I think it is important that people want to go back; it proves the appetite and quality of the exercise.
On a personal level, I really enjoyed the challenge. Locked Shields is increasingly recognized within the cyber community as a ‘must do’ activity to improve your cyber and crisis response skills. You feel proud to wear the Locked Shields T-shirt because it means you have invested yourself. This was my first time taking part and I was honoured to be selected. Overall, it was a very positive experience.

In light of extensive UAS attacks on Ukraine, the NCI Agency collaborated with the Royal Netherlands Aerospace Centre (Royal NLR) to see how scientific research, particularly advanced mathematics, can be a valuable asset in uncovering vulnerabilities in adversary UAS operations. Chris Aaron asks the NCI Agency’s Maarten van den Oever and his counterpart in the Royal NLR about the project and its value to NATO and its Member States
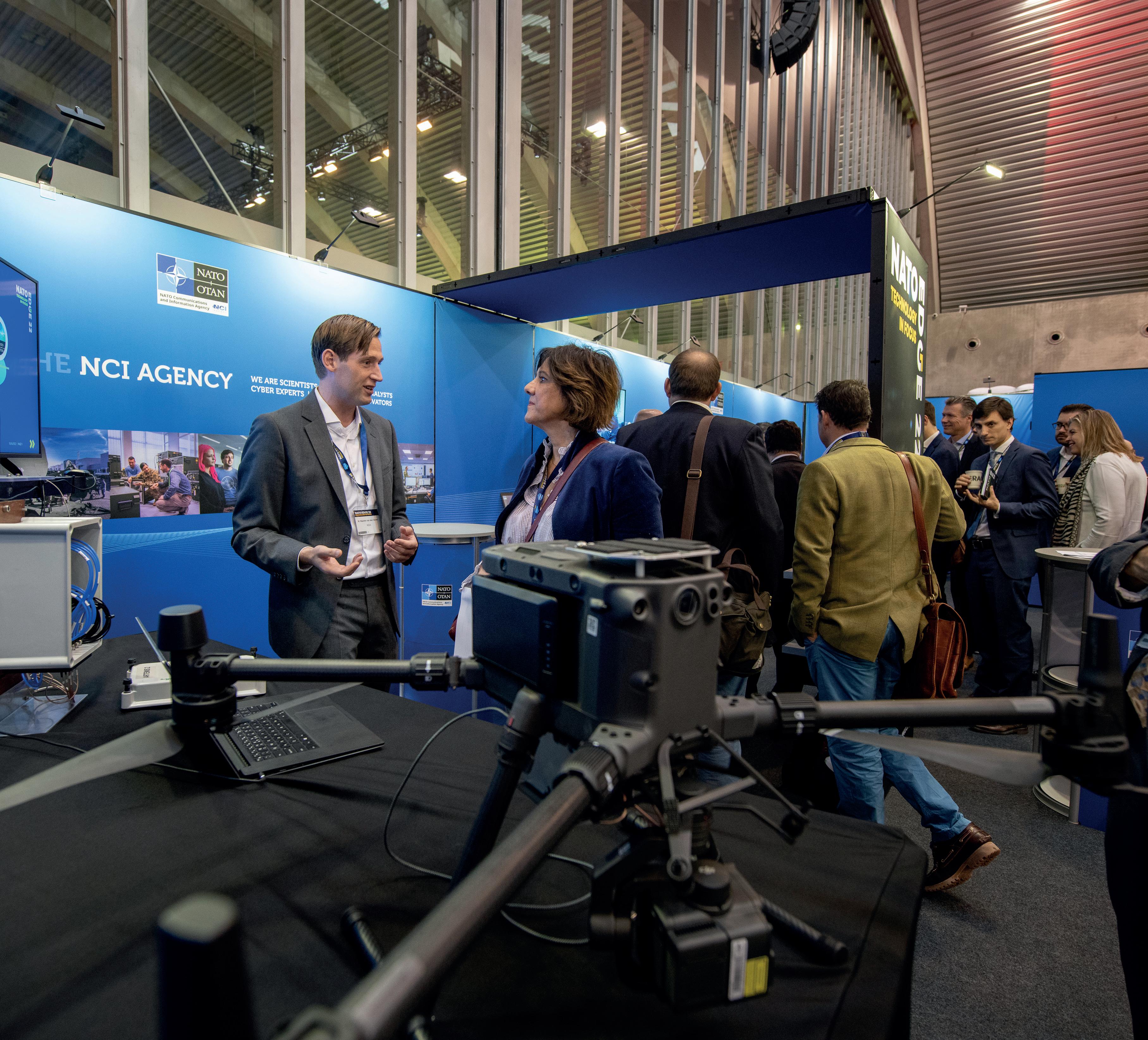
Undisclosed Location, November 2022: Two men stare out over the flat landscape, waiting for the wind to fall and the rain to stop. An array of control stations and monitors sit idle, and a fleet of Unmanned Air Systems (UAS) wait in storage, protected from the elements. A trained eye might spot the antennae of tripod-mounted transmitters and receiver arrays sprouting over the fields.
Finally, the clouds disperse and the two men turn to their control stations. The first UAS is carried to a launch position. This is a ‘friendly’ rotorcraft adapted to carry a Software-Defined Radio Jammer. The UAS jammer ascends and takes station, hovering at a few hundred feet. A second, target UAS is launched and performs a circuit, flying underneath the jammer at various heights and angles. Back at the control station, data flows into
the computer, telling the two men how effective their jamming system is from all different directions. One after the other, a variety of target UASs are sent round the circuit, with more and more data being gathered on each flight.
Part way through the day, a rather different craft is launched. This is a mock-up of an adversary UAS. The mock-up includes facsimiles of the navigation systems and sensors used in the real thing. This UAS gets special treatment. Not only do the two men on the ground measure the impact of their jamming signal on the target’s systems, they also record how the target’s own anti-jamming system responds to a jamming attempt. As the jamming signal comes in from a certain angle, the two men and their colleagues from the NCI Agency and Royal NLR can see how the target UAS reconfigures its global
navigation satellite system (GNSS) receiving antenna to minimize the jamming signal.
NCI Agency scientist, Maarten van den Oever, explains that “to meet a requirement to assist in the procurement of counter-UAS capability, we needed to create a model of the electromagnetic environment during UAS jamming operations”.
The measurements taken of the mocked-up target UAS, and its response to jamming, was perhaps the most scientifically interesting of the tests, says Maarten. The target used an array antenna with patches distributed across the body of the aircraft. By measuring any highpowered incoming signals, the receiver could identify the incoming direction of the jamming wave, and attenuate the undesired signals by cleverly combining
“The NCI Agency and Royal NLR teams worked really well together, collaborating closely through the planning, testing and evaluation stages and drafting the final report”
information from all the patches while still continuing to receive the GNSS positioning signal. Measuring and modelling this response has enabled the NCI Agency to define the number and disposition of jammers that would be required to completely block the positioning ability of a target drone.
Maarten’s counterpart from the Royal NLR says the project came together very quickly. “The NCI Agency and Royal NLR teams worked really well together, collaborating closely through the planning, testing and evaluation stages and drafting the final report. We were both very quick on our feet; we had everything sorted out
in three or four weeks. That was a fantastic aspect of the project.
“Together the NCI Agency and Royal NLR created a mathematical signal processing model using in-house software, and based on that we identified some angles and power ratings that looked like they might be effective. In that way, we narrowed down the range of possible configurations to test in the field. We built the model and, based on that, the joint team came up with a test plan. The November tests gave us the measurements from the field that we needed to fine-tune the model for practical use,” the Royal NLR specialist explains.
“The nice thing about the model is you can put in as many jamming
signals as you want, but what is more interesting is analyzing when the drone starts being affected; it may ignore one or two jammers, but at some point its reception will start collapsing. The model is also modular; we can put any UAS into the model and get out a strategy on how to jam it, or we can use it on our own systems, as a resilience tool, to see how our own systems perform against potential jamming.”
The rapid fulfilment of the original urgent requirement means that NATO now has a model that can be shared with partners to help design new jamming systems, develop targeting strategies for jamming adversary drones and detect vulnerabilities in its own UAS systems.
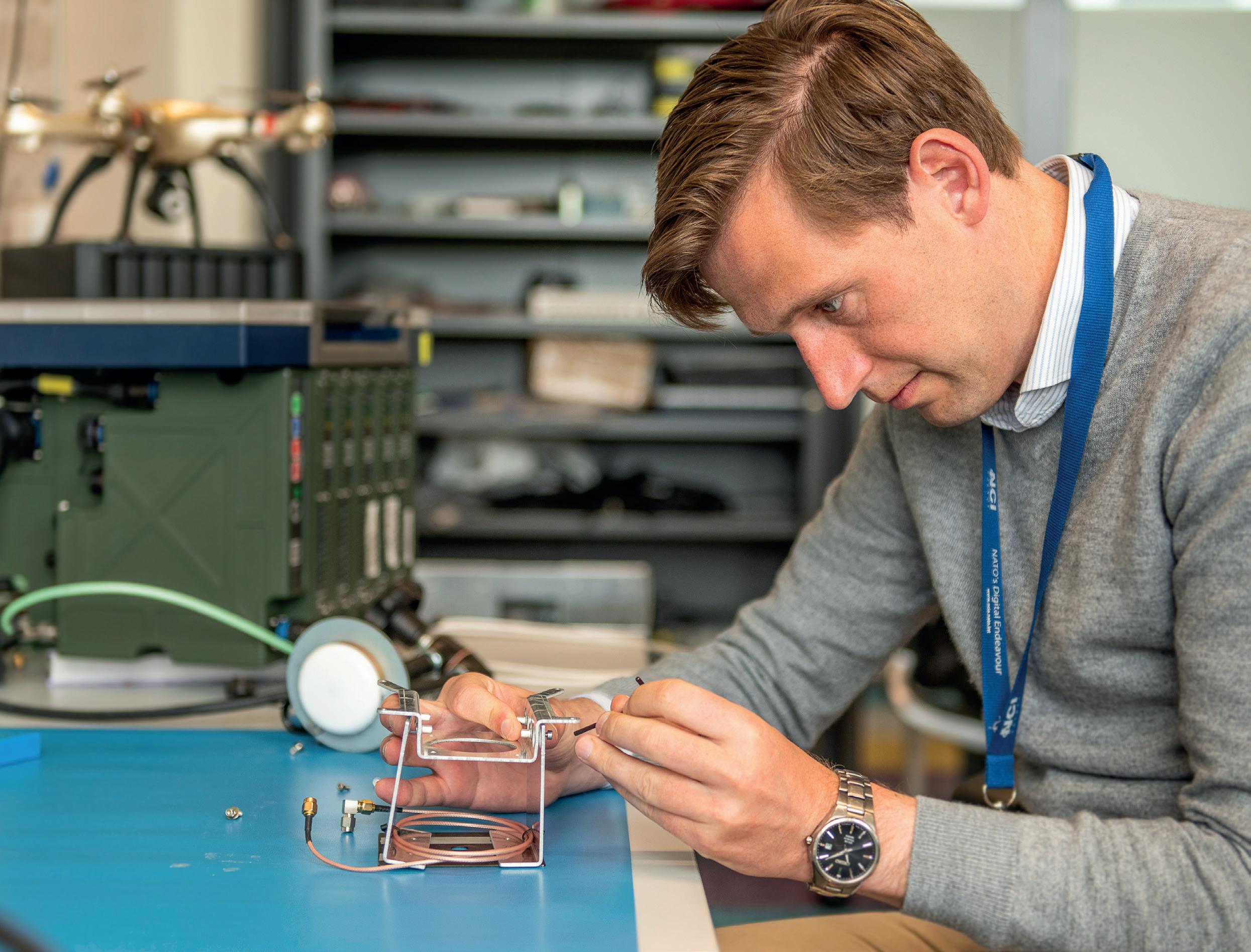
As quantum computing threatens to break conventional, widely used encryption algorithms, Fortinet is delivering quantum-safe security
Carl WindsorHow do current encryption methods protect internet and web-based data?
Modern encryption used, for example, on the internet and in browsers to connect to HTTPS encrypted websites commonly consists of two main components:
• public key infrastructure (PKI), which uses asymmetric key exchange to select a shared key,
• symmetric encryption, which encrypts the data transport using the shared key.
These have been a core part of the internet for years. However quantum computing has the potential in the future to break conventional, widely used encryption algorithms such as RSA, AES and elliptic curve.
Although this is a challenge to be faced in the future as there are no known quantum computers close to
being able to crack these encryption algorithms at the moment, there is still a problem due to the fact that valuable data can be stored for later decryption once these systems become available. So steps to protect them need to be taken soon.
For symmetric encryption such as AES, the algorithms can be attacked by quantum computers using Grover’s algorithm. However, this can be generally addressed by increasing the key length, so for now, we have a solution to put this quantum risk out of reach.
However, key exchange protocols such as Diffie-Hellman key exchanges, which rely on
mathematical concepts based on the fact it is extremely difficult to factor a value into its constituent prime factors and others, are at high risk because Shor’s algorithm can run so efficiently in a quantum computer. This is due to the fact that Shor’s algorithm takes advantage of the weird quantum properties of superposition and entanglement allowing for massive parallelism and hugely efficient computation.
The encryption algorithms in use today are probably safe from attack – at least in the near term. Furthermore, increasing the key size is enough to push the problem
 Senior Vice President, Product Technology and Solutions, Fortinet
Senior Vice President, Product Technology and Solutions, Fortinet
“Quantum computing has the potential in the future to break conventional, widely used encryption algorithms”
further down the line. However, because of the efficiency of Shor’s algorithm, the key exchange algorithms are at a much higher risk, with 62% of industry experts optimistic that a cryptographically relevant quantum computer will be available within the next 15 years.
How does Fortinet see the need for quantum, and in what timeframe?

Fortinet is clear that this is not an issue today as there are no known quantum computers close to being able to crack current encryption algorithms. The issue lies in the fact that valuable data can be stored for later decryption once these systems inevitably become available. Added to this is the reality that we don’t know whether this timeframe will be accelerated. So, if long-term secrecy of data is required, organizations need to ensure that they take action now to protect their data from both current and future threats.
How has Fortinet addressed the challenge?
As the world leader in network firewalls, Fortinet must continue to provide the highest levels of security through innovation to its customer base and help prepare our
customers for what technological innovations are on the horizon.
For those customers requiring an immediate solution, Fortinet has implemented the ETSI 014 Interface specification allowing immediate integration into Fabric-Ready partners such as ID Quantique (IDQ) and Quantum Exchange for Quantum Key Distribution and Arqit NetworkSecure™ for symmetric key agreement.
Does Fortinet already have examples of solutions tested and/or deployed using quantum proof encryption?
As part of the European OPENQKD project, Telefonica, Fortinet and ID Quantique have successfully demonstrated the combined
solution of FortiGate IP Virtual Private Network (IP-VPN) service and IDQ’s Cerberis Quantum Key Distribution (QKD) system, using a standardized ETSI interface, to provide a quantum-safe IP encryption solution over a real deployment scenario consisting of a 20km span.
Another example is with Fortinet and Quantum Xchange when they deployed a five-link transatlantic network with a global US Service Provider as part of an executive briefing centre showcase.
“Organizations need to ensure that they take action now to protect their data from both current and future threats”


Guido Brenne, Principal Scientist in the NCI Agency’s Command and Control Service Centre, tells NCI Agency Communications Intern, Paula Izquierdo Labayen, how he and his team are developing a Virtual Joint Operations Centre that could transform future military operations
Virtual Reality (VR) stopped being solely for gamers and entertainment enthusiasts a long time ago. Its potential extends far beyond those realms and now, as the NCI Agency is leading NATO´s digital innovation endeavour, it is leveraging this technology to explore the possibilities it offers. The Command and Control (C2) Service Centre is leading an innovative project known as the Virtual Joint Operations Centre (vJOC), that aims at creating a virtual and dispersed operations centre for military operations. The intention of the vJOC is to gather commanders and staff to plan, execute and monitor operations in real-time using the virtual space as its headquarters. Guido Brenne, Principal Analyst at the C2 Centre, is part of the team working on the research stage of this project.
The vJOC project was developed to take advantage of the numerous benefits offered by VR technology. Unlike physical architecture projects, where compromises are often made between what is needed and what can be delivered, VR offers almost limitless possibilities to design, organize and even frequently reconfigure a space. This results in significant cost savings in terms of infrastructure. “However, because the opportunities can be endless, things could get lost in translation [from physical to virtual], and one way to ground this effort is based on exploring and defining interaction patterns,” Brenne explains. In the context of the vJOC, interaction patterns provide a framework to determine how people will work together and how they will use the virtual space to accomplish their tasks.


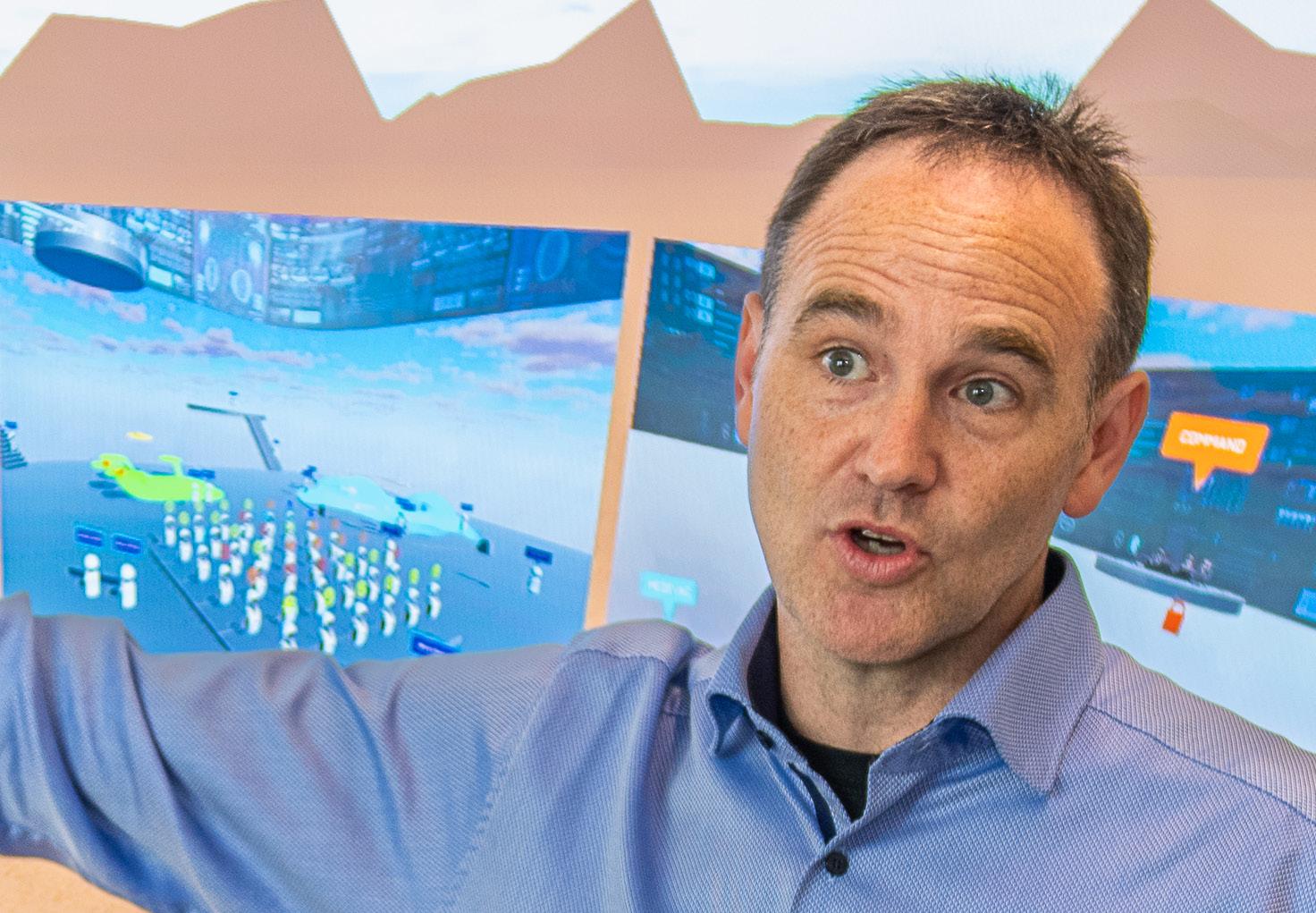
To ensure that the vJOC is effective for its intended purpose, Brenne’s work involves considering a range of factors, such as levels of communication, alerting, notifications and even how to draw someone’s attention in a virtual space. For example, a discussion in a physical JOC may involve interaction patterns such as pointing at a screen, discussing operational objects by whispering in a corner, sharing information with the back office and so on. In a virtual world, certain interactions can be made easier. One interesting example is the selective display of information, which enables classified content to be shared during a briefing with a select group of the audience. By identifying different implementations of these patterns in the virtual environment, Brenne is ensuring that the vJOC would be optimised for effective communication and collaboration once it is operational, just like a physical JOC.
Other, less obvious, interaction patterns that Brenne explores include peripheral awareness and implicit communications. Peripheral awareness refers to the ability to perceive information or activity in one’s surroundings without actively focusing on it. “If something suddenly turns red on a map, it would draw my attention and indicate that something has happened. However, in a virtual space, non-intrusively drawing someone’s attention when they are not actively looking in a certain direction can be a challenge,” Brenne admits. “Same thing goes for implicit communications, like the battle drills that are planned and executed from the JOC.” Brenne mentions the battle drills as they are pre-planned responses to certain scenarios, such as an attack or emergency situation, that are designed to be executed fairly automatically without the need for
explicit communication or direction (even though they will trigger explicit communication). In a vJOC, these implicit communication patterns – which are a much broader concept than just the battle drills – must be considered as they involve conveying important military information through non-verbal cues or context.
The team is exploring different design options for the VR space as the project is still in its experimental stage. The current look of the vJOC features avatars in a wide-open space with different platforms for various interactions, including informal chatting around a virtual fireplace or screens for operations demonstrations. The designs of the user interface have resulted in an array of proposals going from futuristic graphics and environments to a more down-to-earth conventional working space. “The possibilities of VR are endless and that gives us the opportunity to question everything – and removing chairs and tables or changing the room layout is just the start. For people who have never seen a JOC in action, Apollo 13 could be an inspiring movie!” Brenne jokes.


As with any emerging technology, the vJOC project is not without its challenges. Bridging the gap between existing C2 systems that do not necessarily use 3D technology and the JOC virtual interface is one such hurdle when it comes to translating the operational concepts that the project developers want in the VR space. However, as technology continues to advance, new possibilities may arise, and old obstacles may disappear. As Brenne puts it: “Our ultimate goal is to help users understand and work in a vJOC because it has the potential to transform the way we approach military operations in the future.”

“VR offers almost limitless possibilities to design, organize and reconfigure a space”

Having a deep commercial understanding of defence customer needs has enabled Viasat to innovate at the crossroads of simple and complex ideas – and push the boundaries of what is possible
mission requirements. This requires listening carefully to customers and asking them what challenges they are facing and what problem areas they are dealing with. Once you really understand the customer’s needs, you can start to draw out the roadmap to solving the problem.
more closely with the commercial sector to enable a stronger joint force communications capability.
As you think about technology innovation and military communication needs, how does Viasat approach its development roadmap?
Viasat has a long history of product development and innovation. Without a doubt, the key to our approach is we take a market-led position to ensure we are focused on solving real-world problems. Innovation comes in many different forms. It can be complex and it can also be simple, but we find that the simplest solutions are sometimes the best. It may seem obvious, but when you start to develop a roadmap, you need to understand the problem before you start to innovate and develop the solution.
To innovate well, you also really have to understand the customer’s concept of operations (CONOPS) and the
Innovation and product development roadmaps should be living documents. That means they need to be agile and open to dynamic change to mirror the changes to operational requirements. Having an agile, adaptable roadmap enables the team to avoid the so-called ‘valley of death’ where a solution never manages to achieve a technology readiness level (TRL) that will ensure success in terms of final approval and introduction into the market.
What are the objectives that military/government and the commercial sector must align on to enable a stronger joint force communications capability?
Nowadays, the commercial sector is often leading the military/ government when it comes to innovation and product development. Perhaps nowhere is this more clearly true than in the communications field, including satellite communications. The primary reason for this is simply that the commercial sector now has far greater resources to undertake technology development and the flexibility to move quickly. Consequently, the military/ government customer should align
There are perhaps five key areas where this is most notable. The first is the notion that it is OK to fail, as long as you fail quickly. An environment where failure is automatically a bad thing and agility is not promoted can, and likely will, limit innovation and dampen enthusiasm. When you are willing to take risks to drive innovation by mixing simple and complex approaches you can really start to push the boundaries of what is possible.
Being at ease with failure leads to my second point. There is a need for the military/government to adopt faster development cycles generally used in the commercial sector. In the commercial world, customers drive the demand for constant innovation. They want technology that is cheaper, faster, easier to use and requires less power. Commercial companies accept this and satisfy this demand by taking a holistic approach to development. This leads to my next point, that it is better to accept a solution that meets 90% of the requirement quickly than spend years striving for a solution that meets every specification. Why not look for other processes and tools to bridge the remaining 10% gap?
In addition, the military should align with the commercial sector to create a resilient and reliable communications service ecosystem. Commercial customers have a
Managing Director, Viasat UK Hisham Awadseamless mix of networks and bearers – Wi-Fi, cellular, Bluetooth – which they move through seamlessly without even realizing their device is doing it. Achieving this type of hybrid, multi-network resilient communications architecture is a key objective for many military leaders today, particularly as countries such as the United States pursue a Joint All-Domain Command and Control (JADC2) environment and others are following with similar initiatives, such as the UK MOD’s Multi-Domain Integration (MDI).
And finally, embracing zero trust is going to be important going forward. The key is how to take a zero-trust solution and add the appropriate security on top of it as and when required. Why use a fully encrypted solution if you don’t need to?
Viasat has been developing and enabling dual-use technology from its inception more than 35 years ago. It is one of the main things that attracted me to the company. Not only does this open up larger markets for the technology, it also enables us to bring a commercial mindset to problem-solving in the defence arena. Viasat is able to use its understanding of real-world problems in networking and experience creating a large network ecosystem for users comprised of Viasat-operated and partner networks, and then bring that expertise to the military and adapt it to operations. Viasat has a long heritage of working in the defence sector across the UK, US and Australia and therefore can drive innovation through agile roadmap alignment. The dual-use approach helps the government to accelerate bringing in best-of-breed technology and capabilities from the commercial and defence sectors, as well as foster closer relationships from academia all the way through to end users.
Moreover, our dual-use vision enables us to take the very best in commercial technologies and missionize it to fit defence needs. An example of this concept might be a narrowband technology, based on a commercial system that has had cyber protection added to it. Viasat can then adapt that cyber protection to the specific needs of any particular customer or the needs of a specific time and location. Our commercial and defence mindset also means we have developed user interfaces that are easy to understand and navigate, which is critical because non-technical warfighters on the ground need to be able to operate much of this technology. This is often in stark contrast to some traditional and older military interfaces that are complicated and sometimes extremely hard to use.
Viasat has been listening very carefully to our customers while developing the ViaSat-3 roadmap. The constellation of three terabit-class high-throughput satellites is expected to provide near-global coverage with satellites over the
Americas, EMEA and APAC regions. The first satellite covering the Americas was launched on 30 April 2023. This ViaSat-3 network was designed to deliver substantial capacity – just one of the satellites will provide 2.3 times the capacity we had on-orbit before – and services to support residential, commercial and defence communications across the globe. In terms of our dual-use vision, the satellite was designed from the beginning with features that not only support the residential/commercial applications, but also features that will especially benefit military users.
For example, the ViaSat-3 satellites were designed to provide very strong anti-jam and LPI/LPD capabilities, as this was a key part of the customer feedback we saw and heard during development. The satellites are designed to provide additional encryption, as well as enable access to dedicated bandwidth for military users through military Ka-band (Mil-Ka). Once in service, ViaSat-3 will be dynamic, with the ability to flexibly move capacity and provide specific bandwidth directly into areas of high demand such as conflict hotspots while maintaining its global coverage. Much of this is enabled by the ViaSat-3 satellite design, which leverages smaller beams and specific frequencies to deliver concentrated bandwidth in a very focused area.
Ultimately, ViaSat-3 is an example of how commercial understanding of defence customer needs can lead to integration of specific design features that offer solutions. This is our dual-use approach in action, but I can guarantee that our dynamic development roadmap is already moving forwards too.






The NCI Agency’s Branch Head of Exercises, Anthony Moore , explains how new technology solutions are tested during NATO exercises and how this helps to improve NATO capabilities. Christina Mackenzie reports







Nowadays, new technologies seem to emerge on a constant basis. They’re not all destined to have a huge impact, but some will. It is therefore critical that NATO understands them to figure out whether they should be integrated into NATO’s future operations, and, if so, how.
As the world’s most successful alliance, NATO has always been a technology leader. Over its 70 years it has been engaged in, and helped to develop, a vast spectrum of state-of-the-art technologies across all operational domains – air, land, sea, cyber and space. So, it is no surprise that the Alliance has identified nine priority technology areas for further development. Some of these are already well publicized as Emerging and Disruptive Technologies (EDTs) – artificial intelligence, autonomy and quantum-enabled technologies, for example. There are, however a further six technology areas: biotechnology, data, hypersonic technologies, space, novel materials and manufacturing, and energy and propulsion, that NATO has added to its priority list and which will be developed further by the newly established Defence Innovation Accelerator for the North Atlantic (DIANA).
As these technologies start to mature, and it becomes clear that they have operational potential, one of the best ways to put them through their paces and prove
that they actually work in the field is through NATO’s comprehensive Exercise programme.
Anthony Moore, the NCI Agency’s Branch Head of Exercises, points out that the Agency itself doesn’t independently introduce technologies into the exercise programme as there is a tried and trusted process to follow. Each NATO exercise goes through a meticulous planning cycle with multiple planning conferences: initial, main and final. It can take as long as 18 months to get everything prepared. “New technologies are introduced by the ‘customer’ through these conferences,” Moore explains. “Our role is to make sure that if a customer says they want to use a new technology in an upcoming exercise, then we’ll take that technology back to our engineers to make an assessment.” Moore’s team will then confirm whether the technology can be introduced in the exercise of choice or not. Occasionally, the NCI Agency team will need more time. “We will explain that we can’t do it for this exercise, but we can try it in a later one. So, let’s talk about it next year,” he says. But, he adds, “In the exercise branch we don’t really advocate or put forth any type of new technology or decide whether or not to integrate that technology or new network. We concentrate on our job, which is to coordinate the exercise.”
“Our role is to make sure that if a customer says they want to use a new technology in an upcoming exercise, then we’ll take that technology back to our engineers to make an assessment”
Moore does however reveal that in some cases the leadership might push for a particular technology to be tried in a specific exercise, “so we try to support the customer the best we can”. In addition, he explains, “We have to make sure that what we’re doing is in line with the mission and goals of the Supreme Allied Commander Europe (SACEUR), and his intent and overall mission.”
Integrating Finland and Sweden will be an important task in the future, according to Moore, notably in the framework of eVA (enhanced Vigilant Activities), which refers to the deployment of multinational battle groups in Bulgaria, Hungary, Romania and Slovakia, each led by a framework nation complementary to the forces of the host countries. The idea was launched by the Agency’s Service Management Authority (SMA) at the Madrid Summit in June 2022 when, in the wake of Russia’s war against Ukraine, they agreed to strengthen the Alliance’s eastern border, upgrade Battle Groups in the eastern part
of the Alliance to brigade level, transform the NATO Response Force and increase the number of High Readiness Forces to more than 300,000, with the additional establishment of four more multinational Battle Groups in Bulgaria, Hungary, Romania and Slovakia.
NATO’s cyber-posture, technology for cloud computing and strengthening the resilience of NATO networks to enhance information security are also some of the technologies being integrated into exercises. But within the NCI Agency itself, Moore says they are “trying to enhance the mobility and agility of our digital workforce”. This means finding answers to questions such as: “How do we ensure we can extend our tactical and strategic network away from static locations? Do we create mobility training teams? Do we design specific packages? Do we create cloud computing we can access from various locations as long as we have an internet source and different encryption devices built into our laptops? Those are some of the newer technologies we’re currently working on.”

Cisco has expanded its performance monitoring to provide a better and contextualized view on IT performance – significantly enhancing observability
Hugues De Pra
Chief Technology and Transformation Officer, CiscoNow that organizations have widely adopted hybrid work, we rely on high-quality service provision to accomplish our tasks, whether remotely or in the office. However, we often encounter disruptions in video calls, email connectivity issues or faulty applications, regardless of whether they are hosted in the cloud or in our own data centres. When end users experience such problems, they turn to their IT departments for solutions. However, these departments often lack a comprehensive view to accurately identify the root cause. Fortunately, the concept of observability has evolved and now encompasses the entire path, from end-user devices to applications and their data across home or corporate networks, the internet and public clouds.
Full-Stack Observability (FSO) consolidates data from multiple operational domains to provide a unified visibility, real-time insights and actionable recommendations. It
focuses on what matters most: user experience, critical operations, risk and costs, while reducing the time to resolve incidents and performance issues. Additionally, FSO breaks down silos and reduces friction among teams, including infrastructure, security, applications, networking and cloud.
FSO represents an exhaustive approach to managing and monitoring IT, moving away from the old and limited observability provided by a few subsequent checks. With the increasing reliance on applications, IT teams face pressure to ensure that network or application layer issues do not result in security or performance problems down the line. Users are increasingly remote, and applications are more distributed than ever.

Computers now connect to resources that organizations do not manage, such as public Wi-Fi, the internet, public clouds and software as a service. We need to be able to work around these constraints.
In response, performance monitoring has evolved to encompass more comprehensive concepts of visibility and assurance. Modern network and data centre technologies now include built-in controllers that enable the aggregation of telemetry data related to application health and accessibility. Cisco has expanded its portfolio over the years, incorporating ThousandEyes to provide a closer examination of the user’s digital experience and AppDynamics for application
“Cisco has expanded its portfolio over the years, incorporating ThousandEyes to provide a closer examination of the user’s digital experience and AppDynamics for application performance monitoring in the data centre”
performance monitoring in the data centre. This expansion has significantly enhanced observability.
As part of our Full-Stack Observability (FSO) integration strategy, we have established a new bidirectional integration between AppDynamics and ThousandEyes, effectively closing observability gaps between users and applications. This integration offers rapid actionable recommendations and insights. Additionally, we integrate third-party data with OpenTelemetry, providing valuable business context to better understand data streams and make informed decisions. Clear visualizations from the platform enable proactive action planning even before problems arise.
According to industry assessment tool IDC, teams often utilize between 10 to 100 different monitoring and observability tools, resulting in tool sprawl and causing delays in issue resolution, including the detection and mitigation of threats. With our
vendor-agnostic FSO solution, the network itself has become a powerful sensor. Through integration and visualization tools, teams gain increased visibility into applications, infrastructure and users, leading to reduced mean time to resolution and minimized business risk. Insights and automation will both play a crucial role in future performance, competitiveness and resilience.
Conceptually, instead of installing multiple sensors to generate telemetry, the network itself delivers the necessary visibility and sufficient data to describe changes occurring on the network to a collector. Our solution provides contextual, correlated and predictive insights, enabling organizations to quickly resolve issues and optimise experiences.
Furthermore, observability serves as a way to reduce friction between teams by unifying data, analysis, actions and practices. It promotes operational efficiency, ensures an
excellent user experience and mitigates business risk. As per IDC, observability is gaining recognition as a key tactical and strategic function, offering significant benefits, executive support and increased budgets.
Cisco has developed a vision that focuses on the individual user experience, providing contextualized and real-time insights. FSO offers a comprehensive 360° view of the user’s path to the applications they are using, including the status and health of the application data. Partners can unlock even greater value for themselves and their customers through the extensibility of our platform.



The advent of the 5th Generation (5G) of International Mobile Telecommunications (IMT) offers numerous technology opportunities for the military communications community. It’s also a chance to structure an industry vertical to represent common interests and requirements for a relevant voice in IMT technology standardization processes and outcomes for the military. As a significant component of NATO’s infrastructures and capabilities, 5G is important in the pursuit of its military ambitions, but it equally represents an opportunity to maintain NATO’s technological edge and revive its industrial relevance and influence.
In this context, the NCI Agency has been supporting NATO Headquarters C3 (Consultation, Command and Control) staff and Allied Command Transformation in common efforts to:
• Consolidate a strategy towards creating awareness and exercising influence on the 5G civilian-led ecosystem;
• Investigate the benefits and enablers of 5G for military operations as well as develop and validate concepts for NATO capabilities.
While the first set of activities focuses on catering for a coordinated effort towards leveraging and influencing international 5G standardization, the second focuses on the innovative aspects that may represent a significant leap in NATO’s digital transformation ambitions and have an impact on NATO capabilities.
As a complex organization, NATO has different bodies and agencies with different levels of expertise and understanding about the 5G ecosystem, as well as diverse motivations and approaches towards its use in military contexts. From users, technology and capability planners to policymakers and standardization specialists, different communities are providing different contributions to this effort, but mostly in an uncoordinated manner. It is therefore perceived that a coherent transatlantic voice and harmonized positions and strategies for leveraging 5G civilian technologies would benefit the military, technological and industrial interests of NATO Members.
We are contributing to the development of a NATO 5G strategy, which envisages the use of standardized and interoperable 5G technologies providing a secure, robust, resilient and ubiquitous capability to NATO. The following key areas of action are being addressed:
• Encourage innovation – identify, monitor and experiment with key 5G technologies;
• Lead the development of reference use cases and requirements – the reference groundwork for all decision-making processes;
• Promote interoperability – engage with standardization fora, industry communities and participate in standardization activities;

• Ensure security and resiliency – safeguard the use of civilian technologies in military contexts and networks;
• Enable technology use – drive spectrum policy, develop reference architectures and promote technology profiling.
On the technology and innovation side, the NCI Agency has been investigating key 5G technology enablers, their implementation/adoption challenges and related concepts applied to military scenarios. The initial scenarios address the well-experienced and well-understood Deployable Communications and Information Systems (DCIS) and Maritime Communications capabilities. These are the scenarios where 5G use cases and concepts can be more easily leveraged through mature and commercially available products, with reduced risk and implementation time. 5G should increase the economies of scale, security, robustness and resilience of such military networks, further contributing to the digital transformation of the battlefield.
The Agency has also been looking at the potential of 5G open-source and Open Radio Access Network (Open RAN) frameworks. Notably, 5G open-source frameworks democratize access to the technology, which has been mostly restricted to carrier operators. Open source enables the Agency to set up reference systems and testbeds to validate early concepts and novel features. For its part, Open RAN unlocks the flexibility of the Radio 87
NCI Agency Senior Radio Engineer, Germano Capela, offers an insight into how the Agency is supporting the incorporation of 5G into NATO
Access Network (RAN) – which has been a proprietary component of the IMT ecosystem – and creates new innovation opportunities around the 5G RAN. We have recently published a scientific paper entitled ‘5G O-RAN Potential for Military Communications’ at the 2023 International Conference on Military Communications and Information Systems (ICMCIS), which addresses the O-RAN enablers, use cases and challenges for military applications.
In order to pursue the opportunities enabled by open source and Open RAN, we are laying the first stones of NATO’s 5G Testbed, using off-the-shelf hardware and open-source software components. The NATO 5G Testbed will be Open RAN-compliant and enable the development/implementation of a roadmap of features and use cases of military interest. Among other things, the NATO 5G Testbed should enable experimentation with features such as Sidelink, Integrated Access and Backhaul (IAB) and Dynamic Spectrum Sharing (DSS). These require extensive conceptual and technical validation, as the military is one of the few user communities interested in having these features and use cases developed. Initial results from this activity are expected in early 2024.
On a more forward-looking note, NCI Agency subject-matter experts are currently taking an advisory role in a multinational project, Horizon Europe 6G-NTN, which is investigating Non-Terrestrial Networking (NTN) evolutions for the upcoming IMT generation. 6G-NTN has been formally part of the IMT ecosystem since 2022 and is expected to become commercially available from 2025. 5G-NTN enables the extension of terrestrial 5G over satellite, providing ubiquitous coverage capabilities without the limitation of terrain and infrastructure. 5G-NTN uses 5G’s New Radio interface technology (5G NR) and 5G’s Next Generation RAN – the waveform, control and networking functionalities – to enable smartphones, satellite terminals and Internet of Things devices to be directly connected to satellites and provide data and voice services.
6G-NTN is looking at the evolution of NTN for 2030 and beyond. The project aims to design and validate advances in NTN, namely their key technical, regulatory and standardization enablers. In 6G, NTN will address increased robustness and resilience, focusing on multidimensional network infrastructure, multi-constraint RANs and multi-user terminals. NTN will significantly impact many economic sectors and defence is no exception. For this reason, the Agency team will be advising the project team with an educated view on the defence vertical, focusing on the target use cases and requirements for 6G NTNs when applied to military scenarios. This activity not only enables first-hand contact with long-term IMT developments, it also provides good insights on the early stages of the standardization process.


Amazon Web Services’ (AWS) approach to security ensures mission advantage, making it a leading choice for defence organizations around the world
It can be tempting to focus on the technology, but many defence customers are also leveraging our expertise in organizational transformation. We have seen NSD organizations successfully transform their whole organization including budgeting, procurement, contracts, security and legal, going well beyond only using the cloud as a digital foundation.
I joined Amazon Web Services (AWS) in 2014 following a 30-year career in the defence industry. At AWS, I initially led the US National Security team where we pioneered classified hyper-scale cloud. I now lead our Global National Security and Defence (NSD) team. We work closely with NSD organizations around the world, helping them to understand AWS and how it securely provides mission advantage, whether in the cloud or at the edge.
AWS is unwavering in its support for strong defence. We are a global organization with engagements predominantly across the Five Eyes nations and NATO Member States. Although we have learned a lot from our years of operating in classified environments in the US, we understand that our European allies have different needs and we work in accordance.
Transformation can be a daunting task; therefore, we work closely with NSD organizations in partnership to build their digital leadership, skills, policies and culture that are critical for change. For example, this year Amazon signed an MOU with the UK Ministry of Defence to scale up and accelerate work on advancing digital skills development, while the Government of Greece and AWS signed a Statement of Strategic Intent to accelerate the formation of a regional space hub.
The move to the cloud benefits defence organizations in many ways. These include the need to scale capacity to meet mission needs, analyze vast amounts of data, accelerate pace of innovation or collaborate securely with partners. Sometimes organizations are also just seeking to reduce IT costs to reinvest elsewhere in mission.

The cloud enables defence organizations to respond at speed and scale to the rapidly changing world. AWS enables instant access to thousands of servers and the ability to
store and analyze petabytes of data on demand. The speed of Ukraine’s digital response to the Russian invasion is an example. Using AWS, the Ukrainian government migrated more than 10 petabytes of critical data to the cloud from 42 Ukrainian government authorities and central institutions, which enabled the government to continue serving its citizens despite the physical destruction of many institutions, damaged data centres and unreliable power.
NSD organizations need large-scale data and the latest tools to use data to make critical decisions. Those tools are now ranging from big-data solutions to artificial intelligence (AI) and now foundational models and generative AI. With hyper-scale cloud, the capacity and tools are always available for immediate mission impact. Today, NSD organizations are also creating environments to share data and tools more effectively with mission partners. The cloud makes it simple to create sharing environments that might be permanent, for a special purpose mission or for a temporary instant coalition. Two common solution areas are multi-domain operations and open-source intelligence – both requiring resiliency and scale. Without the cloud, organizations are left choosing between a large reserve compute capacity or turning off less critical missions. Hyper-scale cloud is critical to NSD.
Innovation is accelerated in many ways with hyper-scale cloud. There is a constant flow of new capabilities in
General Manager, Global National Security and Defence at Amazon Web Services (AWS) Chris Baileythe AWS cloud, innovation enabled for NSD organizations and our always growing partner network.
Innovation is in our DNA at AWS and we are continually innovating on behalf of our customers; in 2022 we released more than 3,300 new features and services. These innovations range from optimised compute and storage to advanced services such as serverless, machine learning, quantum computing and generative AI. This breadth and depth of capability means NSD organizations can rapidly create in the cloud.
Secondly, access to the cloud means engineering and mission teams can experiment, innovate and frequently iterate with very little cost. We have seen defence customers develop new solutions in days that have had profound mission impact. Another innovation driver is that the undifferentiated technical burden for infrastructure is owned by AWS – freeing up people and funds to focus on new capability.
Thirdly, beyond AWS services, we have a network of more than 100,000 partners who are innovating on AWS every day. These include global organizations such as Salesforce, Palantir, Maxar and Splunk, and also an array of smaller organizations building specialist capabilities such as
Preligins, who enhance operational decision-making with algorithms that detect military observables.

Security is our highest priority and a primary reason that many organizations move to AWS. AWS is architected to be the most secure cloud computing environment available today, designed and built to satisfy the security requirements of a range of highly sensitive and regulated industries, including NSD.
However, we know that trust must continue to be earned through transparency and assurances, and we work in partnership with defence organizations to dive deep on how we secure their data. We also continually undergo third-party audits supporting 98 security standards and compliance certifications to empower customer assurance and accreditation processes. For example, NCC Group recently published an independent report validating that the AWS Nitro System has no mechanism for any operator at AWS to access customer data, a critical requirement for many NSD organizations.
More broadly, the AWS core architecture is backed by a deep set of security tools, with 300 security, compliance and governance services
and features. Examples include how AWS offers extensive logging of every platform API call (more than a quadrillion events per month) and how vulnerabilities are automatically detected and patched at scale. As a result of these controls, the majority of national cyber security organizations recommend the cloud as the most secure place to operate. For example, the UK’s Head of Defence Digital Services at the Ministry of Defence said in 2020, “In most circumstances we can do a better job of security in the cloud than we can do on-premises.”
Our approach to security is at the heart of why NSD organizations choose AWS as their cloud service provider for their most sensitive workloads.
NSD organizations need hyper-scale cloud and the associated advantages to stay ahead of the ever-changing threat landscape. AWS believes in strong government, the protection of individual rights and the need to keep the world safe. Our experience, experts and technical capability are here to help support the mission needs of NATO and NATO Member States.
aws.amazon.com/blogs/publicsector/


Principal Service Engineer (Cloud) at the NCI Agency, Mariano Valle, explains to Alan Dron why the NATO Enterprise Cloud Operating Model (NECOM) will be at the heart of NATO’s digital transformation


Cloud computing is described as the foundation of the rapidly approaching digital revolution, or more precisely, the fundamental enabler of that revolution. So, what does the NCI Agency need to do to make it a reality as it continues its digital transformation?

NATO has been operating cloud computing for several years, but not always in a coherent way. Like many other organizations, it has been slowed down by the absence of all the necessary processes and sufficient numbers of appropriately trained people. NATO has been making progress though, and the Cloud Operating Model was introduced with the NATO Cloud Computing Directive, which took into account all known roadblocks and pain points in the organization at that time. However, the model did not develop further, in part because certain key roles accountable for governance were missing and the Office of the Chief Information Officer (OCIO) itself did not exist.
Consequently, NATO’s rate of cloud adoption has been significantly slower than planned with unclear and inconsistent governance highlighted as the primary factor. This will all change with the arrival of the NATO Enterprise Cloud Operating Model (NECOM), which seeks to bring the practice under new governance and operating rules. The momentum is gathering pace and an action plan to put
NECOM in place has now gone to the OCIO.
NECOM will be a permanent organization and so will require support and funding for both mobilization and subsequent operation phases. An important factor in NECOM is the establishment of the Cloud Service Broker (CSB) – a role most likely to be played by the NCI Agency. The CSB will be responsible for the cloud architecture and engineering. “This is the core of the operating model,” says Mariano Valle, Principal Service Engineer (Cloud) at the NCI Agency. It will however need assistance in the pursuance of some of its activities. For example, when drafting contracts, the CSB may call upon others within the Agency, especially experts within the Acquisition, Finance and Legal functional areas.
The lead of this function will probably be the Agency’s Chief Technology Officer. The intention is to activate the CSB “as soon as possible”, although it will require more resources to get the system up and running. NECOM will deliver cloud adoption governance at three levels:
• Strategic: operating at the NATO Alliance level,
• Operational: focused on the NATO Enterprise level,
• Tactical: the CSB supporting business leaders/application owners in addressing business, architectural and engineering aspects. This will enable
candidate workloads to be fully compliant with governance criteria in order to transition to the cloud quickly.
NATO has already established cloud computing principles as part of a policy that mandated the use of the cloud for new IT implementations, once security considerations allowed them. Those uses are currently limited to business applications, as moving to the public cloud can improve factors such as user experience, governance and, potentially, cost if properly implemented.
Operational IT – NATO Restricted category and above – will, at present, remain outside the public cloud for obvious security reasons. However, an ongoing effort is under way to write a technical security directive that will enable NATO Restricted data to be deployed into the public cloud.
One benefit of moving business IT to the cloud is that it shifts the security risk from NATO to cloud service providers and becomes a shared responsibility, Valle points out.
The Agency has embraced the operating model, although it has still to be operationalized. When it is, personnel will benefit from a system that will offer greater efficiency and be more scalable: “It’s much more dynamic and agile,” says Valle.
“Cloud adoption has been significantly slower than planned”
The operationalization of NECOM will address the following problems:
• Accountability for governance regarding cloud architecture, roadmap, deployment and operation;
• Buy-in from the Executive;
• Clarity on cloud brokerage (cloud operating model) to manage adoption;
• Incoherent and stove-piped approaches to cloud computing IT adoption for services;
• Projects and programmes within the NATO Enterprise;
• Lack of guardrails.
Until now, NATO’s experience with cloud computing has suffered

from a stove-piped approach, with different parts of the organization working independently. “NECOM will solve that problem, because we will be able to exercise governance and management of cloud computing through the entire enterprise.” This will enable it to be operated on a ‘One NATO’ basis.
The potential level of collaboration among individual teams and organizational elements can be enhanced
tremendously by the use of public cloud IT solutions. Many procurement projects are about to start to acquire cloud services for the Agency’s business requirements. In terms of timelines, NECOM will most likely be launched this year as part of NATO Allied Command Transformation’s Protected Business Network Capability Programme Plan, which itself is an element of NATO’s Information Technology Modernization project launched in 2015.
“Operational
Ian West has been responsible for cyber security at the NCI Agency since 2012. After more than a decade in charge, he is set to retire from NATO at the end of this year. Mike Bryant looks back on West’s challenging, fulfilling and very successful time with NATO and the NCI Agency


Ian West first joined NATO in 1996, when he was a serving officer with the Royal Air Force. At that time, he worked for the J2 Intelligence Directorate at SHAPE (Supreme Headquarters Allied Powers Europe), helping with security policy, accreditation and inspections. On leaving the RAF in March 2000, he became a NATO civilian and continued performing that same security function.
He remained in that role for another four years, before becoming Director of the NATO Computer Incident Response Capability Technical Centre in 2004. He headed up this operational team of 20, which formed part of the NATO Communications and Information Systems Services Agency, or NCSA, until it merged into the NCI Agency on 1 July 2012.

On the establishment of the NCI Agency, West became Chief of the Cyber Security Service Line, responsible for a team of 120. This was reformed in 2020 into the NATO Cyber Security Centre (NCSC). Ever since, West has been responsible for all the cyber security elements scattered throughout the NCI Agency –becoming, he notes, “responsible for
NATO’s whole-life cyber security”. Today, West’s Cyber Security Centre has a complement of almost 250, testament to the importance and complexity of the Centre’s mission. That mission is, in part: “To provide and operate effective, agile and resilient cyber defences in order to enable the secure execution of the Agency’s Mission and NATO’s consultation, operations and missions, enhancing the Alliance’s collective cyber defence,” West explains.
To achieve that goal, West’s team comprises military and civilian cyber experts across a vast range of
disciplines. This spans from specific project-related experts and front-line analysts tasked with identifying and assessing risks to NATO’s cyber defences on a day-to-day basis, to incident response specialists and forensic analysts. Not surprisingly, it also includes cryptographers as well as NATO IT system experts responsible for NATO’s ‘cyber hygiene’ – tech speak for reducing the vulnerability of the Alliance’s computer systems to cyber threats.
To support all these cyber defenders, West’s team also has a complement of human resources, business and project management and other support staff – as well as an Executive
“West has been responsible for all the cyber security elements scattered throughout the NCI Agency – becoming, he notes, ‘responsible for NATO’s whole-life cyber security”
Office to manage the Centre on a day-to-day basis. Across the whole of the NCI Agency, there are few teams that can boast such a wide span of responsibilities and skills.
Together as a team, the NCSC manages all the issues relating to cyber defence holistically. In West’s words, “We work closely with industry to benefit from its know-how, capabilities and threat intelligence, while of course also working with NATO Allies and partners. This enables us to inform and educate NATO bodies on issues pertaining to cyber defence.”
West points to two particular highlights of his time with NATO and the Cyber Security Centre. The first is his pride in having responsibility for managing such an important role as protecting NATO and its systems against cyberattack. This has been an immense task as the threat level of these daily cyberattacks has risen considerably.
Furthermore, the attacks are far more sophisticated these days.
Second is his pride in leading a team that does such an amazing job each and every day. “Their passion is at the centre of their efforts, and it is very humbling to lead such a passionate, experienced and effective team,” he says.

In 2016, West and his team achieved global recognition for their achievements when experts from government, industry and academia voted in SC Magazine’s annual awards to present the NCI Agency’s cyber team with a ‘Highly Commended’ trophy. Their three Winner’s trophies for Exercise Locked Shields, the world’s largest attack/defend cyber exercise, attest to the NCI Agency’s worldclass status. The experts also named West Chief Information Security Officer (CISO) of the Year

from a field of thousands of cyber teams and leaders.
Furthermore, having become Chief Cyber Security for NATO a decade ago, building a much reinforced team that he will be proud to hand over to his successor on 31 December this year will be a real highlight, West says. That team is, for example, currently responsible for some €300 million worth of cyber-related projects and defending the vast majority of NATO’s Enterprise networks.
So, what might West do after 31 December? “A nice balance of work and play,” he says. He hopes there will be more time to spend with his family and more time available for private pursuits, but he also wants to give something back to the cyber community, perhaps by helping industry start-ups with how to navigate the complex cyber security landscape, or assisting those who want to work with NATO. Watch this space.

Since its creation on 1 January 2022, the NATO Digital Workplace Centre (NDWC) has been building a digital and hybrid workplace that enables NATO employees to perform by connecting, communicating and collaborating with others regardless of their location. Simon Michell asks its Chief, Jean-Paul Massart, why the NDWC was created, the challenges the Centre has faced and the progress it has made

When the Covid-19 pandemic hit at the end of 2019, it forced almost every office-bound employee throughout the world to work from home. As you can imagine, this had a massive impact on NATO’s business continuity. Instead of working from purpose-built NATO offices and Commands, most of NATO’s 22,000 employees were forced to set up ad-hoc home offices and connect as best they could to do their work with their teams. Like many organizations, if not all, we very quickly realized that we were not well enough organized to deal with this sort of massive disruption.

To address this new reality, the NCI Agency’s General Manager decided to bring together all specialists from various different departments across the Agency, who were connected with digital collaboration in some way to form a new unified team, creating a NATO Digital Workplace Programme.






Thankfully, we weathered the Covid-19 storm. But, more than that, we highlighted that remote and hybrid working was a very viable option and one that was here to stay. Upon the completion of the Programme, the NATO Digital Workplace Centre (NDWC) was formed on 1 January 2022 with approximately 150 people on board, and it became a permanent Business Area in the NCI Agency structure. In short, the NDWC was formed to elevate the initially established consultation and collaboration services into a coherent NATO Digital Toolbox. The services are organized into four categories: Workstream Collaboration Services, Content Platforms Services, Digital Events Services and Workspace Services.
Generally speaking, we can identify five key aspects of the NATO Digital Workplace (NDW); Collaboration (staff enablement and productivity), Leadership (governance), Culture and Socialization, and Technology and Space. This clearly shows that our scope is more complex and it is not only the delivery of electronic devices such as laptops, tablets, mobile phones, printers or video teleconference (VTC) systems. The focus is much broader than just technology only. Our attention is on enabling staff to work differently than in today’s
context and build initiatives around Culture and Socialization (staff engagement), as these are an essential part of ensuring that technology will actually lead to better Collaboration.
From another perspective, the NDW differs from a corporate version of digital workplaces due to the nature of NATO’s composition and the types of sensitive work that NATO undertakes. Apart from that, it caters to the 31 Member States, including military and civilian users. It also operates over multiple classifications and security domains (unclassified, classified and secret). That makes our IT challenge very different to that of a standard corporation.

How has the NATO Digital Workplace Centre evolved since its inception in January 2022?


I like to see this as a three-phase process: survive, revive, thrive.
Survive: When we were set up as the NATO Digital Programme our overriding priority was to help NATO survive the pandemic. This entailed searching for and implementing quick wins, adaptations and solutions to help NATO continue its day-to-day activities. However, it soon became apparent that there was a huge range of ad-hoc solutions put in place by different groups across the entire NATO Enterprise. In other words, the IT environment was becoming more and more fragmented. So, one of the key tasks we gave ourselves was ‘defragmentation’. We had to take control and whittle down the various different ad-hoc solutions into a set of unified enterprise solutions.
Revive: The revive phase relates to the creation of a Digital Toolbox that contains the digital tools we need to ensure business-as-normal functionality alongside business continuity. At the moment we have managed to create the Digital Toolbox 1.0 model, but as we add more and better tools to help us add capabilities and solve challenges, we will evolve it into Digital Toolbox 2.0 and then 3.0. For example, our current default platform for large internet-based conferences is Cisco Webex. That works well, but we want to add Microsoft Teams so we have access to even more collaboration tools that are well suited to team-level cooperation.
Thrive: This is the process of evolving our digital roadmap to support NATO’s digital transformation in reaching a digital-ready workforce.

The NATO Digital Workplace Centre is accountable to the General Manager for the consolidated Agency consultation and collaboration services that comprise the current Digital Workplace, covering the operational NATO services, across all content classifications and security domains, for desktop computing, mail, instant messaging, VTC, content services platforms, telephony, printing and mobility services.


Responsibilities also cover the organization and support of all digital events, meetings and large-scale conferences for both the Agency and NATO stakeholders. Furthermore, the NDWC has the responsibility for driving the future roadmaps of these services across the NATO Enterprise to enable a NATO Digital Workplace through new services based on evolving requirements.
What have been the hardest challenges to solve?

Our biggest challenge is not technology –the technology we need already exists commercially. All we have to do is figure out what we need, buy it and then implement it. The biggest problem, by far, is what we call ‘digital dexterity’. In other words, developing the digital-ready workforce that will be able to benefit from NATO’s digital transformation by using the tools it has at its disposal to the maximum extent. That is why we are going to create a NATO Digital Workplace Experience Centre at the NCI Agency. This will be a ‘show and tell’ immersive experience of the art of the digitally possible.
A digital #OneNATO is the realization of the NATO Enterprise by providing simple yet innovative tools to promote the culture of collaboration, enabling NATO to work in a hybrid environment where people can connect, communicate and collaborate regardless of their location.









However, that is not enough. Digital dexterity also relates to leadership, culture, mindset and process. It means having leaders who understand the digital world and are willing to change outdated processes – things like the introduction of digital signatures and not printing copies of everything. We know we have to tackle this issue because, last year, we undertook a survey of more than 1,400 personnel from across the NATO Enterprise in cooperation with the Office of the NATO Chief Information Officer. Analysis of the key findings indicated that efforts to overcome the main challenges need to be framed around initiatives that will improve Collaboration through change in Culture and Socialization with the support of existing technology.
What will the NATO Digital Workplace look like in 10 years’ time?

We will have implemented a seamless connect, communicate and collaborate environment where people are willing to share digitally. For that to happen, we will need all five key aspects of the Digital Workplace to be addressed with initiatives that will enable such a hybrid environment to be established.
Once we have those enhancements, they will enable us to make a paradigm shift from working asynchronously to working synchronously. That is our aspiration and we hope to get there in fewer than 10 years. We are using 2030 as our horizon as that aligns with NATO’s digital transformation vision. That’s when we will have truly transformed NATO to be able to digitally connect, communicate and collaborate at any classification level in every location.

This year’s United Nations theme for International Women’s Day was ‘DigitALL: Innovation and technology for gender equality’.
Mariana Antunes asks Diana DeVivo, the NCI Agency’s Political Engagement Officer and expert in Gender and Terrorism, how integrating women into technology results in a more inclusive future with greater potential for innovation and creative solutions

What does the theme ‘DigitALL: Innovation and technology for gender equality’ mean to you?
Technology has become the backbone supporting nearly everything we do, and this will only continue to increase in the future. The most crucial challenges to address, therefore, are how to ensure everyone has equal access to technology and how to prevent technology from exacerbating the sorts of inequalities that are already evident offline. Promoting women’s rights in this area has not been properly addressed in the past, but this is a topic that is very close to my heart.
I work in this field to integrate women and diverse and marginalized groups who are left behind by technological progress. The UN’s Women, Peace and Security agenda has predominantly focused on peacebuilding and conflict prevention, and with technology being our future, women need to participate equally in these discussions.
The theme, DigitALL, means that we are finally looking into technology and innovation as areas that may potentially lead to inequality in the
future and figuring out how we can avoid this by integrating a gender perspective into these areas.
How is NATO promoting gender equality and tackling the gender gap in these male-dominated fields?
There has definitely been a shift in the past decade. There is now a bigger focus on training women and girls in tech and cyber fields to enable them to be powerful and equal actors in these technology disciplines. However, this is only made possible by working with those who are leading NATO’s innovation plans so that we can help them to define an effective way to achieve it.
NATO is implementing a very comprehensive Women, Peace and Security action plan that looks at all areas – cyber, innovation, defence planning, defence investment and more – to outline and define actions that better integrate a gender perspective into each area of work.
As a member of the taskforce, I have witnessed the NCI Agency being very involved with several outputs in the action plan. We are making strenuous efforts to integrate a gender perspective in

every aspect of our work – from promoting better awareness and collaborating with other NATO stakeholders to providing practical cyber training to women and girls.
However, we are still a long way from where we should be. Despite the increased focus on technology, and the fact that the NCI Agency is the largest NATO tech body, women still only make up 13.9% of our techrelated service lines. More generally, women only account for 22% of artificial intelligence workers and 25% of cyber security employees worldwide. Moreover, women are only engaged in 20% of computer and maths-based professions and 15.9% of jobs in engineering and architecture. The progress is there, but it is still very slow.
Women make up more than half of the population. If technology is designed for and represents less than half of the population, we cannot thrive as an equal society. Therefore, it is impossible to advance women’s rights without looking at
technology. Technology is a part of all our lives, and this will only increase. So, women will need to play a bigger role in this area because everything we do in the future will include technology. From everyday tasks to doctors performing surgery in the metaverse, technology will transform every aspect of our lives, so women need to be involved in the discussion from the start.
We also know that tech-related threats can impact women differently, from cyberbullying to women being specifically targeted by disinformation – the brutal Russian invasion of Ukraine has highlighted this. It is therefore an urgent necessity to examine gender and technology together and integrate it into the Women, Peace and Security agenda.
How can NATO hire and bring more women and other marginalized groups into technology?
NATO is often, quite rightly, associated with the military and defence, which are predominantly male-dominated environments. This is a message that does not necessarily resonate with women, so we need to ensure
that, as an Alliance, we are promoting a message that attracts women more effectively. For example, we should promote the work that NATO does beyond the military and defence-related aspects. This is something we focus on a lot at the NCI Agency. We work on several campaigns to highlight our female engineers, the women in our space team, data scientists, intelligence teams and much more – to tell women outside of NATO that this is a field they belong in and that we want their expertise and knowledge.
I also believe it is important to work with different levels of academia to show the variety of positions available at NATO and promote roles in science, technology, engineering and mathematics (STEM). We need to think ahead to what our desired future workforce should look like and interact with these sectors. NATO has female experts in different tech fields, so let’s leverage them to build a dialogue and pipeline to attract more women to work in these areas. By integrating women and implementing these changes now, NATO can reach its innovation goals by including diverse perspectives and avoiding groupthink.

The NCI Academy is committed to reinforcing NATO’s technological edge through excellence in cyberspace learning. We deliver essential technical, operational and managerial learning solutions. Check out our new courses in the NCI Academy catalogue!








