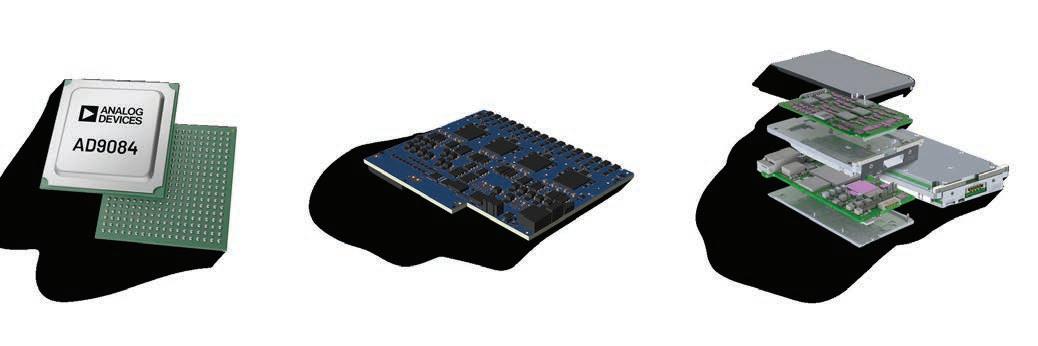
Analog Devices’ commercial off-the-shelf (COTS) software-defined radio (SDR) system-on-module (SOM) digitizers enable customers to deploy high performance distributed sensing techniques at the tactical edge, as quickly as possible.


31 Mission-critical modularity in embedded systems By Mark Benton, TE Connectivity

WEB RESOURCES
Subscribe to the magazine or E-letter Live industry news | Submit new products http://submit.opensystemsmedia.com
WHITE PAPERS – Read: https://militaryembedded.com/whitepapers
WHITE PAPERS – Submit: http://submit.opensystemsmedia.com


SPECIAL REPORT: Leveraging MOSA for cross-domain solutions
10 U.S. Navy investing in MOSA strategies
Q&A with Jason Thomas, Systems Engineering Lead for the Department of the Navy in the Office of the Assistant Secretary of the Navy for Research, Development, Test and Engineering
By John M. McHale III, Editorial Director
14 Unlocking the RF battlefield: Enabling modularity, speed, and interoperability
By Matt Sipe, To The King
18 Future-proofing military servers for AI advancements
By Jeffery Dixon, Crystal Group
MIL TECH TRENDS:
Leveraging the Sensor Open Systems Architecture (SOSA) for radar & EW applications
22 From black boxes to building blocks: SOSA’s push for faster radar and EW upgrades
By Dan Taylor, Technology Editor
25 PERSPECTIVE: MOSA is the conduit for commercial insertion … but there is a floor to commoditization
By Jonathan Cain, SOSA Consortium
INDUSTRY SPOTLIGHT: MOSA in space
26 Achieving high-reliability standards: best practices for adopting JANP-qualified components
To unsubscribe, email your name, address, and subscription number as it appears on the label to: subscriptions@opensysmedia.com
By Reece Byrne, Microchip Technology Published by:
The Arleigh Burke-class guided-missile destroyer USS Thomas Hudner (DDG 116) steams in the Caribbean Sea during January, 2026. U.S. Navy photo.




Flexible Mezzanine Sites for Expansion & Tailored Features
AMD Versal® Premium VP1502/VP1702/VP1552 Options
Up to 700Gb of Optical I/O SOSA-Aligned MACSEC & IPSEC Cybersecurity Features





2 Analog Devices, Inc. –Solutions for rapid deployment
3 Annapolis Micro Systems –64 GS/s Direct RF is at hand!
13 Behlman Electronics, Inc. –The race to open systems –Behlman leads the pack again!
17 Elma Electronic –Experts in rugged embedded computers enabling the warfighter
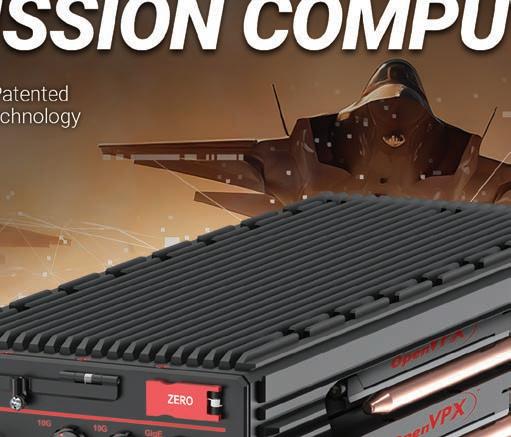
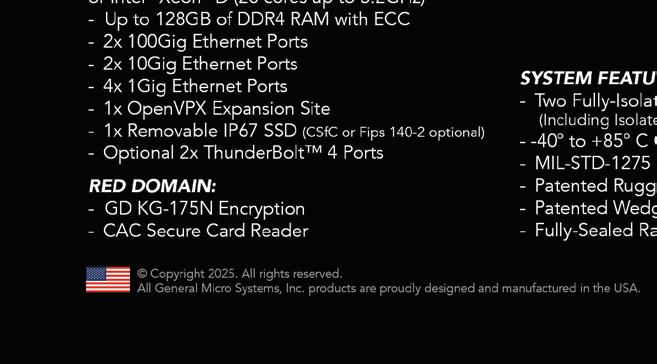
32 GMS – VIPER –the world's most advanced battlefield cross domain OpenVPX mission computer
29 LCR Embedded Systems, Inc. –All systems GO – VPX, CMOSS, and SOSA architectures in accordance with MOSA directives
5 New Wave Design –Solving your digital signal processing challenges
15 PICO Electronics Inc –Size does matter!
WEST 2026 (AFCEA)
February 10-12, 2026
San Diego, CA https://www.westconference.org/West26/ Public/enter.aspx
embedded world
March 10-12, 2026
Nuremburg, Germany https://www.embedded-world.de/en
Sea-Air-Space 2026
April 19-22, 2026
National Harbor, MD https://seaairspace.org/
AUVSI Xponential 2026
May 11-24, 2026
Detroit, MI
https://xponential.org
SOF Week 2026
May 18-21, 2026
Tampa, FL
https://sofweek.org/
GROUP EDITORIAL DIRECTOR John McHale john.mchale@opensysmedia.com
ASSISTANT MANAGING EDITOR Lisa Daigle lisa.daigle@opensysmedia.com
TECHNOLOGY EDITOR – WASHINGTON BUREAU Dan Taylor dan.taylor@opensysmedia.com
CREATIVE DIRECTOR Stephanie Sweet stephanie.sweet@opensysmedia.com
WEB DEVELOPER Paul Nelson paul.nelson@opensysmedia.com
EMAIL MARKETING SPECIALIST Drew Kaufman drew.kaufman@opensysmedia.com
WEBCAST MANAGER Marvin Augustyn marvin.augustyn@opensysmedia.com
VITA EDITORIAL DIRECTOR Jerry Gipper jerry.gipper@opensysmedia.com
DIRECTOR OF SALES Tom Varcie tom.varcie@opensysmedia.com (734) 748-9660
STRATEGIC ACCOUNT MANAGER Bill Barron bill.barron@opensysmedia.com (516) 376-9838
EAST COAST SALES MANAGER Bill Baumann bill.baumann@opensysmedia.com (609) 610-5400
SOUTHERN CAL REGIONAL SALES MANAGER Len Pettek len.pettek@opensysmedia.com (805) 231-9582
DIRECTOR OF SALES ENABLEMENT Barbara Quinlan barbara.quinlan@opensysmedia.com AND PRODUCT MARKETING (480) 236-8818
INSIDE SALES Amy Russell amy.russell@opensysmedia.com
STRATEGIC ACCOUNT MANAGER Lesley Harmoning lesley.harmoning@opensysmedia.com
EUROPEAN ACCOUNT MANAGER Jill Thibert jill.thibert@opensysmedia.com
EUROPEAN ACCOUNT MANAGER Michael O'Kane michael.okane@opensysmedia.com
TAIWAN SALES ACCOUNT MANAGER Patty Wu patty.wu@opensysmedia.com
CHINA SALES ACCOUNT MANAGER Judy Wang judywang2000@vip.126.com
CO-PRESIDENT Patrick Hopper patrick.hopper@opensysmedia.com
CO-PRESIDENT John McHale john.mchale@opensysmedia.com
DIRECTOR OF OPERATIONS AND CUSTOMER SUCCESS Gina Peter gina.peter@opensysmedia.com
GRAPHIC DESIGN MANAGER Kaitlyn Bellerson kaitlyn.bellerson@opensysmedia.com
FINANCIAL ASSISTANT Emily Verhoeks emily.verhoeks@opensysmedia.com
SUBSCRIPTION MANAGER subscriptions@opensysmedia.com
By John M. McHale III
For the fourth year running, we at Military Embedded Systems and the Shephard Group (U.K.) are producing the SOF Week 2026 Show Daily and print Show Guide, as we were once again named the official Media and Show Daily Partners for SOF Week.
The event – to be held in Tampa, Florida, May 18-21, 2026 –is jointly sponsored by U.S. Special Operations Command (USSOCOM) and the Global SOF Foundation and is expected to draw more than 20,000 attendees.
Each of the last three years, our SOF Week Show Daily team posted more than 80 pieces of content over four days consisting of videos, news, and blogs on the technology showcased at the event; news from the show; conference presentations from USSOCOM and industry leaders; and in-depth interviews with USSOCOM leaders. To view our coverage from last year, visit www.militaryembedded.com/sofweek.
This year’s event will have live capabilities demonstrations; these up-close demos are held every other year and are quite fun to watch. In the past, Special Operations personnel have performed HALO [high altitude, low opening] jumps, simulated hostage rescues, and one year showcased the Little Bird helicopter in action. If you make it to this year’s event, be sure to catch a live demo. To view our video coverage of the 2024 demo, visit https://tinyurl.com/4795jcd6.
To learn how you can participate editorially in Official SOF Week Show Daily newsletters – one deploys in the morning and one in the evening each day to all show attendees – email me at john.mchale@opensysmedia.com . If you are an exhibitor and want to learn about sponsorship opportunities in the Official SOF Week Daily, Official SOF Week Show Guide, and SOF Week TV channel, contact my colleague Patrick Hopper at patrick.hopper@opensysmedia.com.
The newsletters will reach not only all of the show attendees but also the additional combined SOF-related audiences of Military Embedded Systems and the Shephard Group.
Our coverage will also be featured on www.militaryembedded. com and on http://www.shephardgroup.com. Both sites will also feature updates on the opportunities mentioned above, or you can visit the show site at www.sofweek.org
Our most read story from the event last year was “SecDef: AI, counter-UAS tech are key focuses for rapid fielding efforts,” Technology Editor Dan Taylor’s coverage of Secretary of Defense (SecDef) Pete Hegseth’s surprise address during the SOF Week keynote session on May 6, 2025.
John.McHale@opensysmedia.com

Taylor reported that Hegseth told the audience how the U.S. Department of Defense (DoD) would prioritize rapid acquisition going forward: “Our goal is to put the best systems in the hands of our warfighters,” he said. “We’re doing this by reviving our defense industrial base, reforming our acquisition process, and rapidly fielding emerging technologies,” he said.
Nothing has changed since that address last year, with the Trump administration making many moves to remove barriers to acquiring faster technology for the warfighter. Atop that list is a continued emphasis on programs and program managers leveraging modular open systems approach (MOSA) strategies in all new programs and technology refreshes.
We continue to cover MOSA’s momentum in every issue, including this one – our 2026 MOSA issue – which includes my interview with Jason Thomas, Systems Engineering Lead for the Department of the Navy. In our discussion, Thomas talked about how MOSA is benefiting the warfighter and fitting in with the administration’s acquisition reform plans:
“I can’t mention or comment in terms of policy or acquisition reform right now. I can speak to my observations and experience on this momentum shift. We’re seeing a big focus on warfighter response to rapidly evolving operational environments. Our ability to adapt quickly is directly tied to what capabilities, or modules, we can reliably field faster. Like any competition, the team that makes the right adjustments sooner and faster gives [itself] a better chance of winning.”
Thomas and I met at the MOSA Industry & Government Summit in August 2025, which featured excellent briefings on MOSA from many DoD leaders, including Jacob Glassman, Deputy Assistant Secretary of War for Science and Technology (DASW S&T). We are also excited to have Mr. Glassman as the keynote speaker for our own 2026 MOSA Virtual Summit, set to be held February 26.
In his current role, Mr. Glassman serves as the principal advisor to the Under Secretary of War for Research and Engineering (USW(R&E)) on matters related to S&T, developmental prototyping, and experimentation.
He also served as the Senior Technical Advisor to the Assistant Secretary of Defense for Research, Development and Acquisition (ASN RD&A), where he was responsible for implementation of MOSA and Artificial Intelligence (AI) as well as rapid acquisition in the Department of the Navy and the Marine Corps.
By Dan Taylor, Technology Editor

AI platform provider AIM wins $4.9 million Air Force contract
Artificial intelligence (AI) platform provider AIM announced the award of $4.9 million in contracts with the U.S. Air Force for remote base and airfield construction and repair, under which the AIM platform enables the fully autonomous operations needed for rapid airfield damage recovery (RADR) operations.
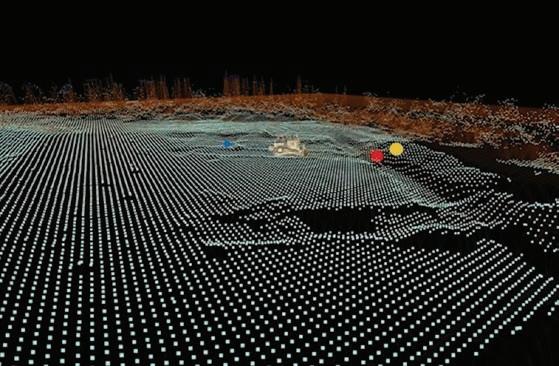
The company announcement states that its AI-powered platform for heavy machinery enables machines to operate without human oversight for repairs, construction, and maintenance of runways, terrains, and bases in the event of airfield damage. AIM also says that its technology enables real-time mapping of landscapes, automated navigation, GPS-enabled or -denied driving, gathering of detailed data and analytics, and intelligently linked vehicle operation. AIM officials say that when used for RADR operations, AIM-enabled machines first conduct a rapid damage assessment using a suite of high-tech sensors to create a 3D map of the airfield.
Leonardo DRS won a subcontract to provide infrared mission payloads for the Space Development Agency’s (SDA’s) Tracking Layer Tranche 3 (TRKT3) effort supporting missile defense. Under the terms of the agreement, Leonardo DRS said it will serve as the space-based mission payload provider for TRKT3 and will design, build, integrate, and test infrared payloads intended to support global detection, warning, and tracking of ballistic missiles and hypersonic weapons.
The company said the payloads are intended to provide infrared sensing from an adversary launch through interception, including data for fire-control sensing to support missile interceptors. The TRKT3 Infrared Mission Payload will undergo thermal vacuum and thermal balance testing in the Leonardo DRS Space Payload Lab in Cypress, California.
The HII Ingalls Shipbuilding division reports successful conclusion of builder’s sea trials for USS Zumwalt (DDG 1000) – the lead ship of the Zumwalt-class U.S. Navy destroyers – during which the Ingalls and Navy team conducted a series of at-sea tests following an extensive modernization availability as the Navy’s first Conventional Prompt Strike (CPS) platform.
HII notes that the Zumwalt, which arrived at the Pascagoula shipyard in mid-2023, has since undergone major technology upgrades, including the integration of the CPS weapon system and replacement of the original twin weapons systems with new missile tubes, plus additional preparations for operational readiness. The other two ships in the Zumwalt class are also either undergoing CPS weapons system integration or are scheduled to receive the CPS system.


Vertical launch of JAGM demonstrated from quad launcher for counter-UAS use
Lockheed Martin conducted a demonstration of a 90-degree vertical launch of a Joint Air-to-Ground Missile (JAGM) from its JAGM Quad Launcher (JQL) at China Lake, California, the company announced. During the event, the company says the missile was used in an engagement intended to show its ability to neutralize an uncrewed aerial system (UAS) threat. Lockheed Martin also used the demonstration to show the launcher’s configuration flexibility, with the JQL mounted on a Richard Childress Racing 6x6 “Mothership” vehicle.
Lockheed Martin stated that the test was aimed at validating full vertical-launch operation for JAGM from multiple platform types, including surface-combatant vessels, to enable a 360-degree engagement envelope.
L3 Harris delivers aircraft-based ISR platform to U.S. Air Force
L3Harris Technologies announced delivery of the first MC-55A aircraft to the U.S. Air Force following integration and mission system testing tied to Australia’s Peregrine fleet.
Australia is acquiring missionized business jets through a U.S. foreign military sales program intended to provide the Royal Australian air force with airborne electronic warfare (EW) and intelligence, surveillance, and reconnaissance (ISR) capabilities, according to the company statement. L3Harris noted that the first aircraft was delivered by the U.S. Air Force to Australia’s air force, while follow-on aircraft will remain in U.S. Air Force possession to support Australian air force training and predelivery activities. L3Harris said that it established a field service team in Australia and is working with local industry partners to provide in-country support.
Technology provider V2X wins spot on Golden Dome contract
Critical-technology provider V2X, Inc. was awarded a spot on the massive (reported to total as much as $151 billion) contract under the Missile Defense Agency (MDA) Scalable Homeland Innovative Enterprise Layered Defense (SHIELD) indefinite-delivery/indefinite-quantity (ID/IQ) contract vehicle, known colloquially as “Golden Dome.”
Under the terms of the V2X agreement, the company will partner with the MDA and industry to accelerate the delivery of innovative defense capabilities across a range of mission areas. V2X’s past and current government contracts include initiatives such as the COBRA DANE littoral radar and the COBRA KING shipboard radar platform, which the company says highlights the company’s expertise.
DARPA’s autonomous “Grand Challenge” program reaching endpoint
Following 20 years of high-level innovation and testing with U.S. Army and Marine Corps partners, the U.S. Defense Advanced Research Projects Agency (DARPA) Grand Challenge – a first-of-its-kind race to foster the development of self-driving ground vehicles – is nearing its conclusion as the Robotic Autonomy in Complex Environments with Resiliency (RACER) program gets ready to wrap up.
According to a recent update from DARPA, the RACER effort was never about building a single, specialized vehicle but was instead intended to develop an autonomy “stack” – a collection of algorithms, datasets, and neural network models that could be deployed on any ground vehicle. In a series of final tests, demonstrations, and experiments in the last quarter of 2025, RACER vehicles demonstrated the ability to navigate complex terrain without human intervention, thereby freeing up soldiers for other critical tasks. The effect of the RACER program extends beyond the battlefield, according to the DARPA update.

By John M. McHale III, Editorial Director
Jason Thomas, Systems Engineering Lead for the Department of the Navy in the Office of the Assistant Secretary of the Navy for Research, Development, Test and Engineering

The modular open systems approach (MOSA) mandated by the U.S. Department of Defense (DoD) in 2019 for all new programs and upgrades has been embraced by all the services, including the U.S. Navy, which produced a MOSA Guidebook on how and why to implement MOSA. In this interview I conducted with Jason Thomas, Systems Engineering Lead for the Department of the Navy in the Office of the Assistant Secretary of the Navy for Research, Development, Test and Engineering, at the September 2025 MOSA Industry & Government Summit, we discussed the guidebook, the current momentum of MOSA strategies, and the benefits of MOSA from a systems-engineering perspective. We also explored common misconceptions regarding MOSA, metrics for measuring MOSA success, and what Thomas would like to see from industry regarding MOSA. Edited excerpts follow
MCHALE: Can you please share your experience in the defense industry and your role and responsibilities for the Navy?
THOMAS: I’m responsible for the posture of systems engineering for all naval systems. [When] I say Navy, that’s Navy and Marine Corps, naval. The naval port-folio really looks at air, surface, subsurface, C4I [command, control, communications, computers, and intelligence] systems, land, tactical communications system. System engineering [in the Navy] encompasses MOSA [modular open systems approach] architectures and digital engineering work, and I’m responsible for ensuring our policies, procedures, and guidance are aligned and supported across all those domains.
MCHALE: We are here at the MOSA Industry and Government Summit. So, let’s chat about MOSA. Why does MOSA have so much momentum in the defense community right now? How does it benefit the warfighter and how does it fit in with DoD leadership plans for acquisition reform?
THOMAS: I can’t mention or a comment in terms of policy or acquisition reform right now. I can speak to my observations and experience on this momentum shift. We’re seeing a big focus on warfighter response to rapidly evolving operational environments. Our ability to adapt quickly is directly tied to what capabilities, or modules, we can reliably field faster. Like any competition, the team that makes the right adjustments sooner and faster gives [itself] a better chance of winning. We’re seeing that with what modular open systems approaches can provide. We’re also seeing a lot of guidance from SECNAV [Secretary of the Navy], from CNO [Chief of Naval Operations], and others on this impetus and this drive for fielding capabilities faster, leveraging commercial technologies, and broadening the
industrial base to leverage big primes, traditional vendors, and nontraditional vendors to really deliver what our warfighters need.
MCHALE: I’ve heard discussions about a product your team is involved with in the Navy MOSA guidebook. What is the goal of the guidebook, and what are your plans for the next edition?
THOMAS: The goal of the guidebook is to really provide information to programs and some guidance where we saw a gap between what higher-level policy and intent [is], and at the execution level, “How do I do MOSA? What does that mean to me, and what do I need to consider?” Iteration 1 of the guidebook was released in January of 2025. [The guidebook was] necessary to really provide guidance to programs, PEOs, the workforce, and industry on how the DoN [Department of the Navy] is approaching MOSA implementation. The need was immediate; and our team did an incredible job coming together and delivering Version 1.
Version 2, which is set to release in early 2026, builds upon that effort and delivers more content and guidance to help programs, implement MOSA strategies, and realize what this type of approach can yield in terms of value for the warfighter and for the taxpayer.
Version 2 of the guidebook is going to include more guidance on contract language, specific information for program managers, details on the system-engineering technical reviews, acquisition gate reviews, different acquisition pathways, and [information] across the life cycle with all disciplines and domains represented to ensure that everybody can see themselves in MOSA. It’s not just for new programs or for mission systems – it shows a broad applicability and strategic approach to deliver lethal, ready warfighting capabilities.
MCHALE: I’m a publisher, so I want to know: What’s your distribution [strategy] on that? Do you send it to everybody when it’s done?
THOMAS: We send to Distribution A, which is for full public distribution.
MCHALE: MOSA is often talked about from a long-term, life cycle cost perspective, as it will enable more commercial innovation to leverage more quickly, thus reducing down times and upgrade costs. But what is your view of MOSA from a system-engineering perspective?
THOMAS: From my perspective, it’s really all about system engineering, and system engineering is really all about total life cycle performance and support. System engineering hits on architectures, requirements, and mission needs when and where we need them. How do we define and decompose our systems into modules or components? How do we select products or solutions that fulfill needs? How do we verify and field those functions and capabilities? Additionally, how do we insert new technologies, and how do we do all that with a bounded trade space of cost, schedule, performance (i.e. delivery need dates)? We also have to consider those elements for today as well as the evolving threat environment that we’re dealt.
So really, MOSA helps you address readiness. It helps you address lethality by inserting technologies, commercial or otherwise, faster at the point of need, when our warfighters need it. It also allows us to then take additional benefits of cost savings and other areas of reuse that we want to proliferate and promulgate elsewhere.
So again, MOSA is an approach that ties in the technical and the business aspects. What’s important for planning MOSA, or planning a MOSA strategy, is understanding your current needs of today, what may occur tomorrow, or what you’re looking at tomorrow, and what potentially may happen in the future so you can make the best decisions you can earlier, be more adjustable and adaptable.
MCHALE: What are some of the common misconceptions of MOSA that you come across?
THOMAS: From my experience, it’s approach versus architecture. Architecture is a fundamental and important part of your MOSA. Your architecture helps you define the system that you’re building, the capability that you can deliver.
The approach is really everything within data rights, tech data packages, contracting strategies, and much more. What work is organic? What work [needs to] leverage commercial best-of-breed technologies? What are my refresh rates, my update rates? How do I orchestrate a strategy that fuses the business and technical pieces together to deliver an effect?
Then leveraging various standards that are out there, some that are called out explicitly, like the FACE [Future Airborne Capability Environment] and SOSA [Sensor Open Systems Architecture] Technical Standards. Those standards help us with quality. Having good standards helps you define what quality you expect of those capabilities that are being fielded. I also don’t see enough conversations integrating our procurement brethren, our sustainment brethren, into those conversations. We really have to facilitate the value and the importance and stake they have in that. It’s not solely driven by architecture or standards, or, frankly, from engineering. And I say that as an engineer. It’s truly a team effort.
MCHALE: Some DoD leaders have called for more metrics on most of success to combat the naysayers. How would you describe or measure the success of a MOSA initiative?
THOMAS: Anything we do should provide value that helps the DoN advance in delivering for our sailors and Marines. One of the things I’ve noticed in conversations is
"I think, between the high-level defense guidance that we’re all seeing, the priorities that are out there, the evolving threat environment, the economic landscape, all things that are happening globally, I think MOSA is going to be a key enabler to help address what the warfighter response is, as well as humanitarian responses to those activities that may occur."
the focus on cost. I’ve also heard some people talk about speed. I would suggest we focus the conversation on business value. This way it gives programs more flexibility to establish the MOSA strategy that best fits their needs, while our guidebook offers a multitude of things to consider to realize that vision.
[It starts with] understanding your value proposition for your weapon system or your system that you’re providing to the Joint Force with the DoN. Some things are legacy [and will need] to be sunset. So, it’s not smart or wise to adopt a MOSA strategy at that point. But you could still do rapid prototyping and rapid experimentation, and take advantage of those opportunities where it makes sense through those programs. They now become players that contribute at the strategic level instead of being neglected or minimized.
On the other side, if you’re a brand-new weapon system that’s being conceptualized or developed, that’s not your final state. It may be your final state when you deliver an IOC [initial operating capability], but it surely won’t be your final state. The first day after IOC, a program may start a modernization effort based on what’s been discussed or learned. You’ll have evolving threats, supply-chain issues that may arise, new technologies [that] will mature and present new opportunities, new algorithms that you want to take advantage of, and more. The program will have to pivot or adjust to meet new or evolving needs; some things were planned for while others were unforeseen. Systems engineers must consider these things for any system they support.
All that work, all that activity to produce a product and value still requires time and investment of resources to deliver. Having MOSA up front and early allows you to shorten those later evolutions and later activities. [Let’s say] your development for your acquisition program from conceptual to IOC is 10 years. Then you have an engineering exchange proposal, a modernization effort that’s going to be five years from the time that you define it and release a contract or RFI to when it’s fielded. That’s [now] 15 years from the start. If your MOSA is baked in early, potentially your modernization is going to be fielded at year 12 or year 13, or earlier if you can pivot before IOC. So, how we look at time has to be really well-understood in its totality. Same thing with budgets, cost, personnel, and skill sets.
Once we understand really the full life cycle and the full totality of what we’re talking about in terms of a MOSA, then you can start looking at those modules of activity, modules of work, modules of progress, modules of capability differently, and start decomposing and saying, where do I really get efficiencies? And that’s for a single program. When you start looking at portfolios and larger strategic efforts, you can get significant return in terms of data, sharing, testing, a myriad of other benefits on development, fielding, potentially again, defense industrial base, with other sources of repair, other sources of material that you don’t necessarily focus on or think about as a single program manager for a single program.
MCHALE: How do you look to further industry engagement and feedback for what you do at the Navy?
THOMAS: How do we become better partners in a multitude of areas: For example, in IP, data rights, technical data packages, different options for only releasing an RFI or an RFP. We (the government) may have something in our mind, predisposed to belief, structure, or approach that worked in the past, or didn’t work in the past. We may just not know any better that’s where we want to have better engagements and learn.
If there’s better approaches that are out there that we can take advantage of, different designs, different architectures, different technology, different business strategies, incentive structures, that may appear we’re not in alignment with industry, but it’s only because we’re not informed. Help us understand better what we can do on that front. That’s just my personal opinion.
MCHALE: Looking forward, how do you see MOSA impacting DoD procurement five years from now, or even longer? Predict the future.
THOMAS: I think, between the highlevel defense guidance that we’re all seeing, the priorities that are out there, the evolving threat environment, the economic landscape, all things that are happening globally, I think MOSA is going to be a key enabler to help address what the warfighter response is, as well as humanitarian responses to those activities that may occur.
But if we all look at it and say, I want a new app on my phone, okay, here you go. Now, I have different options for weather apps or finding a parking spot, or whatever it is, I have different opportunities. Why? Because of the standards that help you build to a particular capability or expectation, set of expectations, that you're looking for. It’s the business and technical sides coming together seamlessly.
I think MOSA is a foundation of building blocks for all that we want to do going forward to be adaptable, responsive, lethal, and that strengthen the industrial base. It truly is a strategic imperative. MES

Behlman introduces the first test-proven VPX power supplies developed in alignment with the SOSA Technical Standard. Like all Behlman VPXtra® power supplies, these 3U and 6U COTS DC-to-DC high-power dual output units feature Xtra-reliable design and Xtra-rugged construction to stand up to the rigors of all mission-critical airborne, shipboard, ground and mobile applications.
> 6U power module developed in alignment with the SOSA Technical Standard
> Delivers 1050W DC power via two outputs
> VITA 46.11 IPMC for integration with system management

> 3U power module developed in alignment with the SOSA Technical Standard
> Delivers 800W DC power via two outputs
> VITA 46.11 IPMC for integration with system management
Leveraging MOSA for cross-domain solutions

By Matt Sipe
The radio-frequency (RF) battlespace will continue to grow more complex. Even so, with the right architectural foundations – backed by empowered governance, industrial engagement, and cross-service alignment – the U.S. Department of Defense (DoD) can build modular, adaptive, and resilient spectrum systems capable of dominating this domain for decades to come. The Modular Open RF Architecture (MORA) stands as a foundational element of the larger modular open systems approach (MOSA) transformation underway across the services.
The electromagnetic spectrum has rapidly transformed from a supporting function of warfare into a primary battlespace – one that is congested, contested, and evolving at a pace that traditional acquisition systems struggle to match. Modern military operations depend on agility in communications, sensing, electronic attack, and spectrum maneuver. Yet for decades, the U.S. Department of Defense (DoD) and its partners have been burdened by RF systems that are vertically integrated, difficult to upgrade, and expensive to sustain.
Recognizing this challenge early, the U.S. Army’s C5ISR [Command, Control, Communications, Computers, Cyber, Intelligence, Surveillance and Reconnaissance] Center began systematically addressing the underlying architectural issues that plagued RF modernization efforts and contributed to runaway SWaP-C [size, weight, power,
and cost] problems across platforms. Their answer was the Modular Open RF Architecture (MORA) – a bold attempt to fundamentally rearchitect how RF subsystems are designed, integrated, and maintained. Now at Version 2.5, with the community closely watching for the anticipated 3.0 release, MORA stands as a foundational element of the larger modular open systems approach (MOSA) transformation underway across the services.
Why MORA matters more than ever
At its core, MORA is about modularity and abstraction – breaking monolithic RF systems into discoverable, reusable, and interoperable components. It defines a clean, open architecture for RF building blocks such as receivers, transmitters, tuners, converters, and digital processors. Through well-defined interfaces and the MORA Data Message (MDM) protocol, the architecture separates hardware from software, control from processing, and mission applications from the physical RF chain.
This structural decoupling is powerful, shifting RF modernization from hardware-first, vendor-locked stovepipes to software-driven, platform-agnostic modularity, enabling:
› Rapid integration of new sensors, payloads, and waveforms
› Reuse of RF resources across communications, signals intelligence (SIGINT), and electronic warfare (EW) missions
› Healthy competition among vendors at the module level, not the system level
› Technology refresh cycles measured in months, not decades
In other words: MORA enables the DoD to bring speed and competition back into RF modernization – areas historically dominated by inflexible designs and proprietary implementations.
MORA in communications and EW: a true cross-domain enabler
Modern communications systems rely on increasingly dynamic environments – multiband, multi-access solutions spanning tactical voice, satellite communications, resilient mesh networks, 5G, and beyond. MORA enables these capabilities by abstracting RF front-end components so that software-defined radios (SDRs) can evolve through software updates rather than repeated hardware procurements. An SDR built around MORA can migrate waveforms, upgrade tuning ranges, or expand mission sets without replacing the entire radio stack.
In EW and spectrum operations, the benefits are equally transformative. MORA’s open interfaces enable rapid insertion of digital receivers, advanced jamming modules, adaptive beamforming cards, and artificial intelligence (AI)-accelerated processors. Since the architecture includes support for high-speed, low-latency pathways (e.g., MORA low-latency bus, VITA 49.2, IEEE 802.1Q), its devices can participate in time-critical RF loops that legacy systems simply cannot achieve without proprietary integration.
EW has long suffered from vendor-unique RF chains that inhibit rapid innovation. MORA flips that model: It enables a shared framework where government, primes, nontraditionals, and allies all build against the same architectural substrate, accelerating development while protecting the government’s long-term flexibility.
The interoperability challenge: variation without governance
Across the DoD, nearly every service and major program has attempted to create or adopt its own RF or open architecture. These attempts were often undertaken in good faith, responding to their mission-specific needs. But the cumulative effect has been counterproductive: Instead of converging on shared, synergistic interfaces, these attempts have created a patchwork of unmanaged variation points, resulting in unique implementations of standards, dialects of architectures, and incompatible interpretations of open interfaces.
This proliferation of “butterfly variants” is not the fault of engineers. It is a symptom of a bureaucracy that lacks a unified architectural strategy and does not incentivize cross-program synergy. Program offices are understaffed, overloaded, and frequently rewarded for delivering their program’s solution instead of for making solutions reusable across other services or mission families.



This situation creates a downward spiral:
1. Programs innovate in isolation.
2. Variants emerge with no feedback loop to the originating standard.
3. Other programs cannot reuse the work because the “open” standard is now fragmented.
4. The community fails to converge, and stovepipes reemerge under a new name.
This is not an argument for one MOSA standard for all of DoD. Instead, it is a call for intelligent governance of variation – where architecture owners receive feedback, integrate lessons learned, enforce compliance where appropriate, and reduce divergence where harmful.
Without this level of coordination, MORA and other open standards risk becoming yet another set of siloed, incompatible solutions.
Where synergies should – and must – be found
Multiple architectures and standards intersect across the C5ISR, aviation, EW, and comms domains. Many already address overlapping problem sets and could be harmonized:
› VITA and OpenVPX (hardware profiles and backplane connectivity)
› MORA (RF modularity and signal transport abstraction)
› CMOSS (Army implementation of modular open systems)
› SOSA Technical Standard (tri-service sensor architecture and slot profiles)
› VICTORY (platform data bus and network abstraction)
› OMS/UCI and AMS-GRA (Air Force mission systems interoperability)
› Big Iron (high-performance EW systems)
› COARPs (radar processing systems)
› Aviation Mission Computing Environment and comms/datalinks/controls
› HOST (interoperable computing hardware)
The real opportunity is not to pick winners, but to define how these standards interoperate along the RF-processing-compute chain. MORA plays a critical role here –bridging RF hardware with digital signal-processing pipelines, enabling both Sensor Open Systems Architecture, or SOSA, Technical Standard aligned hardware and higher-level OMS/UCI applications.
Catalyzing commercial innovation through openness
Historically, the RF world – especially in EW – has been dominated by proprietary implementations. Companies often delivered closed “whole systems,” making waveform migration, hardware refresh, and mission reconfiguration costly and slow.
MORA disrupts this dynamic. By aligning with widely adopted commercial standards such as IPv6, high-speed Ethernet, and field-programmable gate array (FPGA)optimized interfaces, MORA enables direct integration of commercial FPGAs and RF systems-on-chip (RFSoCs), 5G chipsets, AI/ML [machine learning] signal-processing accelerators, and GPU-based Big Iron compute nodes.
This point isn’t trivial: It means the government can now acquire best-of-breed RF modules, integrate them rapidly, and refresh them frequently – without locking into a single OEM’s ecosystem.
This approach directly supports the vision of RF-as-a-service, under which platforms dynamically scale RF capability, adapt to mission changes, and evolve over time while maintaining interoperability with coalition partners.
This approach directly supports the vision of RF-as-a-service, under which platforms dynamically scale RF capability, adapt to mission changes, and evolve over time while maintaining interoperability with coalition partners.
Global momentum: The international community is moving too International military organizations are experiencing the same limitations the U.S. faces: vendor-locked RF systems that are expensive to refresh and slow to adapt. Many allied nations have begun adopting modular open RF architectures – sometimes aligned to MORA, sometimes independently developed, but with the same ambition: to break vendor lock and accelerate modernization.
This growing alignment could unlock unprecedented coalition interoperability:
› Shared waveforms
› Common RF payloads
› Interchangeable SDR modules
› Unified training and sustainment footprints
Equally important, it enables a healthier global industrial base. Vendors would no longer need to deliver full end-toend systems. They would compete in module-specific markets, encouraging innovation, lowering cost, and creating survivable, diversified supply chains.
The future: MORA as an enabler of acquisition transformation
The November 2025 Acquisition Transformation Directive from the Pentagon underscores the urgency for scalable production, module-level competition, and leveraging commercial qualification processes. This directive aligns perfectly with MORA’s architectural philosophy.
MORA directly supports the directive by enabling:
1. Scalable production: Complex, proprietary RF systems are difficult to scale. Modular architectures simplify supply chains, isolate component risk, and allow the government to certify modules independently.
2. Module-level competition: Program offices can now compete SDRs, tuners, beamformers, filters, or DSP engines separately, dramatically increasing competition and reducing cost.
3. Recertification of modules: With well-defined boundaries and severable components, modules can be qualified using commercial processes (e.g., DO-297) and reused across platforms without full-system requalification.
4. Industry investment in focused capabilities: By reducing the scope vendors must deliver to participate, MORA encourages small businesses to enter the market, primes to focus on integration and architecture, and nontraditional suppliers to deliver high-impact modules.
These moves shift RF modernization toward the commercial technology curve –faster, cheaper, more innovative.
The RF backbone of tomorrow’s joint force
As near-peer adversaries evolve at software speed, the U.S. and its allies must field RF systems that can evolve just as fast. MORA provides the blueprint. It decouples hardware and software, enables competition, fosters innovation, and ensures that the government – not vendors – controls its technical destiny.
When paired with complementary standards like SOSA, CMOSS, VICTORY, OMS/ UCI, AMS-GRA, and emerging compute frameworks, MORA establishes a unified foundation for RF modernization across the joint force.
Nevertheless, the RF battlespace will only continue to grow more complex. But with the right architectural foundations –backed by empowered governance, industrial engagement, and cross-service alignment – the DoD can build modular,
adaptive, resilient spectrum systems capable of dominating this domain for decades to come. Lastly, if so much opportunity exists for just the RF domain, consider the synergies that could be achieved if the services looked at all domains similarly. MES

Matt Sipe is a defense technology strategist specializing in open architectures, modular design, and digital engineering. He is the founder of To The King, a company that advises government and industry on acquisition transformation, MOSA, and defense strategies. He previously served as the Chief Engineer for U.S. Army Aviation, during which he supported defense programs in reducing vendor lock and accelerating delivery through open architectures.
To The King • https://ttkllc.com/







As the leader in Open Standards-based Solutions, Elma can take you rapidly from development to deployment. Find out how we work with our customers through every stage in the process.

Leveraging MOSA for cross-domain

By Jeffery Dixon
Defense organizations must balance long-term durability with rapid artificial intelligence (AI) innovation. While military servers are built for decades of service, AI processors evolve on cycles measured in years, risking premature obsolescence. Future-proofing requires modular, scalable architectures that allow component upgrades without redesigning ruggedized chassis. Thermal and power challenges grow as next-generation central processing units (CPU) and graphics processing units (GPUs) exceed 600 watts, demanding adaptive cooling and power systems within strict military-standard limits. Close vendor partnerships and alignment with technology road maps are essential to ensure longevity. By combining modular design, scalable cooling, and vendor collaboration, defense programs can sustain mission-ready AI performance across evolving hardware generations.
Defense organizations face an artificial intelligence (AI) race that will keep pushing the limits of military server performance. They must field ruggedized computing systems that last for decades, yet those systems must also keep pace with AI technologies that evolve on refresh cycles measured in months. While commercial data centers can replace servers every two to three years, military programs require stability, long-term support, and proven reliability under extreme conditions.
As AI becomes central to modern defense, powering everything from autonomous vehicles to real-time threat detection, the challenge intensifies. AI processors and graphics processing units (GPUs) are advancing so rapidly that hardware often
becomes commercially obsolete in less than five years.
Future-proofing ruggedized servers is no longer just about physical survivability. It requires designing modular, flexible, scalable architectures that can absorb generational shifts in hardware without compromising security, mission readiness, or environmental resilience.
AI’s rapid evolution versus defense life cycles
AI is reshaping both battlefield operations and the design criteria for militarygrade computing. Faster CPUs, more powerful GPUs, and increasingly complex AI models drive compute demands to unprecedented levels. However, the defense industry’s procurement model is fundamentally different from the commercial sector.
Commercial applications typically face two- to three-year refresh cycles that are driven by cost-performance optimization. In contrast, defense applications are usually designed for 10- to 20-year deployments and require ruggedization, strict certification, and life cycle support. Long-term component availability is a key consideration. If a key CPU or GPU becomes unavailable, mission readiness is threatened. In addition, military AI deployments must adhere to rigorous compliance and security standards, which complicates frequent upgrades.
Designing for longevity requires chassis modularity
Designing modular, scalable architectures is one of the most effective ways to ensure long-term capability. Chassis design should remain constant across multiple hardware generations. This approach makes it possible for systems to transition from legacy Intel and AMD processors to the newest Intel Xeon 6 and AMD EPYC 9005 processors, without requiring a new chassis design. Internal rearrangements may be needed, but the overall mechanical footprint stays consistent. Since the form factor remains PCIe-compliant, the same chassis can support newer generations with minor thermal modifications.
The PCIe slots remain an industry standard. Cooling may need to adapt, but the chassis doesn’t need to change. This strategy enables defense systems to accommodate multigeneration upgrades while maintaining physical ruggedization and environmental certification.
Thermal management is the biggest engineering hurdle
While physical form factors remain relatively stable, thermal and power requirements are scaling dramatically:

Earlier-generation processors operated at 105 to 150 watts, but today’s AI-class CPUs and GPUs consume 350 to 600 watts each. That trend continues to accelerate.
Maintaining military-standard (MIL-STD) thermal compliance (often -40 °C to +55 °C) in sealed, rugged enclosures is a challenge. The systems must provide quiet operation in acoustic-sensitive applications while balancing thermal performance with power availability in constrained environments like ships, armored vehicles, or remote bases.
Solutions to the heat issue include:
› Using custom ducting and heat pipe technologies to spread loads.
› Reducing GPU clock speeds to lower thermal design power (TDP) in exchange for quieter operation.
› Designing scalable cooling systems that can adapt to future higher-wattage processors.
Today, it’s common to see 350-watt CPUs and 600-watt GPUs. Engineers need to identify a sweet spot of rugged performance without compromising mission requirements.
Leveraging vendor partnerships for road map alignment
Future-proofing depends heavily on vendor alignment. Close relationships with Intel, NVIDIA, Supermicro, AMD, and Micron can provide early access to product road maps. This road map integration steers defense customers toward hardware that will remain supported for years. Every system is customized to the customers’ requirements.
Another cornerstone of future-proofing is designing servers with headroom for future expansion. For instance, unused expansion slots enable customers to add accelerators later. Rack-mounted servers maintain consistent faceplate and chassis dimensions, even as internal layouts shift and embedded rugged servers are becoming more popular for deployed, sealed environments, expanding design options beyond traditional racks.
Future-proofing ensures defense teams can integrate new GPUs, field-programmable gate arrays (FPGAs), or application-specific integrated circuits (ASICs) as requirements evolve without needing to redesign the entire system. Instead of mass-producing chassis in bulk, an approach that builds systems aligned with the road maps of key technology vendors and the specific needs of defense integrators has proven successful. (Figure 1.)
Dynamic chassis design enables the chassis depth and architecture to be adjusted for each customer’s compute density and cooling requirements. Predictive adaptation for
power requirements and thermal subsystems comes about by aligning with vendor road maps, which enables military users to stay current with AI advancements while still fielding rugged systems with long-term operational stability.
Balancing power, heat, and acoustic constraints
The three greatest engineering challenges in AI-driven military servers are power, thermal load, and acoustic requirements. These factors intersect in complex ways.
More powerful chips require larger power supplies and generate more heat. The resulting high thermal loads require faster fans or liquid cooling, which can increase acoustic signatures or add. However, quiet operation is critical in many military applications, limiting how aggressively systems can be cooled.
Engineers must strike compromises that include power-limiting GPUs when full performance isn’t required, designing modular power distribution boards to handle future high-wattage components and trading slight acoustic increases for thermal reliability.
These problems all run into each other – more power, more heat, and the need for quiet operation. Balancing those factors is where engineering expertise comes in.
Future-proofing in practice
To illustrate, consider a rugged 2U server fielded with NVIDIA V100 GPUs. Within a few years, the program requirements will shift toward Blackwell GPUs. Thanks to consistent PCIe form factors, the new accelerators can be integrated without changing the chassis – only cooling ducts and power supplies need to be adjusted.
Meanwhile, Intel’s Xeon processors can be upgraded across generations while retaining the same socket packaging, ensuring that defense agencies can refresh compute power without a complete redesign.
This combination of consistent packaging, modular chassis, and scalable thermal designs enables systems to evolve across decades without premature obsolescence.
Looking ahead: what future-proofing means for defense
Future-proofing military servers is an ongoing process, shaped by both AI’s exponential growth and the unique demands of ruggedized deployments. The path forward will require:
› Advanced cooling innovations to manage greater than 1,000-watt accelerators in sealed environments.
› Edge-computing architectures to reduce dependence on centralized data centers.
› Close vendor collaboration to ensure defense programs align with technology road maps.
The McHale Report, by militaryembedded.com
Editorial Director John McHale, covers technology and procurement trends in the defense electronics community.
Future-proofing military servers is no longer a matter of ruggedization: In the AI age, it means designing for adaptability. By integrating modular chassis, scalable power/cooling, and vendor road map alignment, defense organizations can deploy servers that not only survive harsh environments but also evolve along AI technology for decades. MES

Jeffery Dixon, systems architect at Crystal Group, is a retired Marine Corps Reserve Lt. Col. with more than 25 years of service in defense systems engineering and leadership. He has held senior engineering roles with major defense contractors and holds an M.S. in systems engineering from the Naval Postgraduate School and a BSEE from the Virginia Military Institute.
Crystal Group www.crystalrugged.com



Military Embedded Systems focuses on embedded electronics – hardware and software – for military applications through technical coverage of all parts of the design process. The website, e-mags, newsletters, podcasts, virtual events, annual Resource Guide, and print editions cover topics including radar and electronic warfare, artificial intelligence/machine learning, uncrewed systems, C5ISR, avionics, and cybersecurity. Don’t miss any of it!
Military Embedded Systems is also the largest source for coverage of the Sensor Open Systems Architecture, or SOSA, Technical Standard and the Future Airborne Capability Environment, or FACE, Technical Standard. We exclusively produce the once-yearly SOSA Special Edition and FACE Special Edition. militaryembedded.com

By Dan Taylor
Radar and electronic warfare (EW) teams face a growing mismatch: Threats in the electromagnetic spectrum change quickly, but many fielded systems are still built in ways that make upgrades slow and costly. The Sensor Open Systems Architecture, or SOSA, Technical Standard is intended to reduce that gap by standardizing how radar and EW hardware and software fit together, making it easier to insert new processing and replace components without major chassis redesign. This feature explains what problems the SOSA approach is solving for radar and EW programs, why implementation can be difficult in practice, how the SOSA Technical Standard supports faster tech insertion to keep pace with emerging threats, and what obstacles remain as the ecosystem matures.
A strike package pushes into contested airspace and the threat picture changes midmission: A new emitter lights up, the jamming pattern shifts, and the warning tones in the cockpit start coming sooner than they should. The aircraft barely makes it out of a hairy situation, and the debrief is blunt: There’s a gap in the radar/electronic warfare (EW) chain, and it could take months or even years to fix. But that timeline is starting to shorten.
In the past, fixing gaps in radar and EW coverage meant inserting new processing and new hardware, all of this often on a legacy architecture that can turn into chassis rework, custom wiring, and painful requalification while the threat keeps evolving. The industry is pushing to break that cycle by standardizing how sensor systems are built so that upgrades can be inserted as building blocks instead of rebuilding the box.
That’s where the Sensor Open Systems Architecture, or SOSA, Technical Standard is aimed. Instead of custom backplanes and vendor-specific interfaces that lock a program into a single design path, the SOSA Technical Standard makes radar and EW systems easier to update by defining how hardware and software pieces fit together.
The goal is to simplify upgrades: Swap in better processing, add capability, or
replace a weak link without redesigning the chassis from scratch.
The promise of SOSA alignment Radar and EW programs have often paid for the same integration work again and again. Small differences in how boards connect – or how data moves between them – can turn every refresh into a redesign. The SOSA Technical Standard is meant to cut that friction, setting a shared blueprint by defining the architecture itself.
“SOSA provides a reference architecture model to support various mission threads,” says Ken Grob, director of embedded technologies at Elma Electronic (Fremont, California). “The standard addresses SOSA modules that describe the logical building blocks used to implement a specific sensor type.”
One practical pain point SOSA alignment targets is backplane variation, where “almost the same” pinouts keep parts from being truly interchangeable. Jay Grandin, vice president of product development at Annapolis Micro Systems (Annapolis, Maryland), says aligning with SOSA tightens that up: “SOSA has chosen board slot profiles without userdefined pins which increases interoperability between different modules as there is no variation in backplane interface pinout.” (Figure 1.)
The benefit is long-term upgradeability, Grandin adds. “This allows for fielded systems to be more reliably upgraded without chassis redesign, ensuring longer lifetime, and more frequent hardware upgrades to enhance capability.”
The big value of the SOSA standard when it comes to radar and EW systems is how quickly technology can evolve as a result, allowing industry to keep pace with the threat, says Dinesh Jain, FPGA product manager for Abaco Systems (Huntsville, Alabama).
“There’s a renewed sense of urgency as AI [artificial intelligence] models are being trained to identify vulnerabilities in radar and EW systems to both stresstest the limits of its capabilities and areas for improvement,” Jain says. “When vulnerabilities are identified, it becomes a high priority to resolve them as quickly

Figure 1 | Annapolis Micro Systems’ WP3H20 3U OpenVPX switch combines UltraScale+ processing and an Intel SBC with high-density VITA 91 backplane connectivity, designed for low-latency EW, jamming, and radar. Image via Annapolis Micro Systems.
as possible. A system designed to SOSA open standards allows programs to quickly implement upgrades with the best solution while minimizing impact to the system architecture.”
That promise – faster upgrades with less disruption – sets the bar for what comes next: making SOSA aligned upgrades work in systems that are already operating near their limits.
The culture change
Making SOSA upgrades work is easier said than done, however: Because SOSA upgrades ask teams to commit to a stricter framework up front, it can feel like a culture change in an industry that has long worked a different way.
The standard rewards teams that accept guardrails early: SOSA alignment calls for consistent interfaces, defined profiles, and a more disciplined approach to how hardware and software are put together. That work style can feel restrictive to engineers used to optimizing every connection for a single platform. It also comes with a practical ramp-up, Grob says.
“Initially there is a learning curve associated with implementation of a new design using the SOSA Reference Architecture, and in obtaining SOSA aligned hardware elements, chassis, and power supplies,” he notes.
For radar and EW, the tougher issue is planning for growth, Jain asserts. Designs that look fine at first can hit a wall when the spectrum expands and the data load spikes.
“In my opinion, the biggest technical challenge is building in resource overhead to the initial set of program requirements, especially when it relates

Figure 2 | The Abaco Systems SBC3801 is a SOSA aligned 3U VPX secure single-board computer with SecurShield technology, providing a programmable hardware root of trust for mission systems such as SDRs, sensors, and crypto processing. Image via Abaco Systems.
to EW and radar,” Jain says. “The frontend spectrum of interest is rapidly expanding.
“It was only a few years ago where the upper limit of the spectrum of interest was 8 GHz,” he continues. “Now, nextgen EW systems are requiring 18 GHz and beyond across many RF channels.”
Aligning with the SOSA standard can make upgrades easier, but it can’t rescue a platform that runs out of capacity.
“This is not a SOSA shortcoming but rather about planning as far ahead as possible and building resource headroom into the system,” Jain says. (Figure 2.)
But if planning is done right, SOSA offers a huge value to helping industry keep up with threats that continue to rapidly evolve.
“In order to keep pace with threats, systems need to be built so that they can be implemented quickly and can be upgraded,” Grob says, noting that SOSA aligned upgrades support an ecosystem where programs can draw from proven modules instead of starting from zero. “Available building blocks like SDRs [software-defined radios], Ethernet switches, CPUs, and data-acquisition cards help by allowing designers to pull standard hardware that is SOSA aligned off the shelf.”
Grandin connects the same idea to faster refresh cycles in the field: “By allowing more frequent hardware upgrade cycles due to standardization, SOSA ensures that systems can take advantage of
the latest available hardware as quickly as possible to tackle evolving threats with enhanced capabilities.”
SOSA also changes how suppliers invest in future parts, especially as EW pushes higher in frequency. “Using the push towards 18 GHz as an example, the development resources to bring such a product to market is quite high and requires a substantial resource investment,” Jain says.
SOSA gives vendors more confidence that the market will be there, he notes: “Knowing that the product is being designed to SOSA, and knowing that new programs are embracing SOSA, multiple different developers can invest with confidence that their product have multiple opportunities to procure design wins.”
That combination – easier insertion plus stronger supplier investment – also shows up in two places program managers care about every day: cost and schedule.
On time and on budget
Radar and EW systems are expensive partly because integration is expensive. When every program has to wire up its own set of interfaces and prove every connection from scratch, cost rises and schedules stretch. SOSA aims to reduce that custom work by pushing reuse.
With SOSA, “costs can be lowered through the availability and re-use of standard components provided by an ecosystem of suppliers that produce standard hardware elements (PICs),” Grob says. “This also extends to software that runs on standard SOSA aligned hardware and API framework.” (Figure 3.)
He adds that a modular approach supports smaller upgrade steps: “The approach supports incremental upgrades to be developed and tested to quickly support rapid upgrade and deployment.”
Grandin says standardization improves plug-and-play integration, which directly cuts time and labor. “By limiting options and standardizing existing options across hardware, interface protocols, and software interfaces, plug-and-play capability is drastically improved. This significantly reduces integration cost and time.”
Jain maintains that market pressure also speeds delivery. “With multiple developers investing to deliver a SOSA [aligned] solution, there’s a ‘time-to-market’ mentality which means program sponsors can have access to the latest technology earlier and quickly qualify them to counter evolving threats,” he says.
Those benefits only matter if the SOSA approach continues to spread across radar and EW programs.
Growing adoption
Fortunately for advocates, adoption of the SOSA Technical Standard has accelerated, especially in new programs. At the same time, older systems remain widely deployed, and the ecosystem still needs clearer ways to prove compliance and handle systemwide needs like security and management.
Grob says the effort has been underway for “about a decade,” and the vendor base has broadened across the hardware stack.
“The hardware ecosystem has developed with many companies now designing embedded board-level products that are aligned with the SOSA standards,” he says. “Other companies are designing backplanes, chassis managers, power supplies, and chassis that are SOSA aligned.”
(SOSA) for

From Grandin’s company’s view, the SOSA approach is already the default for new work – and it is starting to pull older programs forward, too.
“Nearly all new projects we see now are SOSA aligned and all of our new products are SOSA aligned,” he says. “Even older programs are starting to upgrade backplanes to take advantage of the SOSA ecosystem.”
Jain has also noticed the transition is showing up more often in program requirements, even while legacy systems remain common. “The transition from legacy to SOSA is real,” Jain notes. “It is common to see SOSA [alignment] as a requirement in RFPs for new programs.”
On the supply side, Jain says that new product roadmaps are tracking toward SOSA aligned building blocks. He adds that work is also continuing on RF-focused interoperability: “In addition to SOSA, we are seeing more interest in MORA [Modular Open RF Architecture], which standardizes low-latency RF data communication between boards from different vendors.”
Taken together, the message is straightforward: Aligning with the SOSA Technical Standard is becoming the common baseline for radar and EW upgrades, with growing supplier support. The remaining work is less about selling the idea and more about making alignment easier to prove – and making the full system stack, including security and management, as repeatable as the hardware building blocks the SOSA approach is built on. MES
By Jonathan Cain, SOSA Consortium
The insertion of commercial products into military acquisitions is critical for the future strategic advantage of the U.S. and allied nations; the recent acquisition reforms put forward by the U.S. Department of Defense (DoD) and Secretary Hegseth put this certainty front and center. The reasons are obvious: The continued conflict in Ukraine, the rapid increase in Chinese production capability, and technological advancement in artificial intelligence (AI).
But when we talk about commercial products, there is an implied value proposition that tips toward large-volume, horizontal markets, where commoditization drives down costs per unit. Quality is often not sacrificed, but rather refined: While commercial customer requirements change with the increasing standards of living, technological design tends toward pursuing efficiencies in production capability, rather than more performance.
I live in Tucson, Arizona, an arid desert with summer highs topping 100 °F. It’s only a minor inconvenience when my iPhone won’t turn on because I accidentally leave it outside too long. Even as the phone protects itself from overheating, it still gives the option to make emergency phone calls. There are also times when it crashes, but again, that’s just an inconvenience. But what happens when military equipment fails or decides to not turn on when service members need it most?
Absolute reliability and peak performance have been the largest driving forces behind the defense industry over the last 80 years. We have created a system that is completely riskaverse. The size and scope of the industry that delivers these reliable, well-performing products has swelled to ensure that every unknown unknown is understood prior to fielding.
Systems engineering focuses on quality attributes – the “-ilities” like reliability, availability, or securability. Getting each of these into a new system causes a significant increase in cost and schedule, but they also ensure that reliable system performance is met wherever it’s needed, no matter what.
Secretary Hegseth’s “Acquisition Transformation Strategy” emphasizes speed for system deployment and fielding even an 80% solution with an expectation of upgrading as soon as practical. This is where MOSA [modular open systems approach] comes in: Within this context, MOSA is an approach to finding the right areas at which pre-existing performance surplus of components does not drive down overall system quality. MOSA uses open systems architectures or government reference

So, as industry drives towards commercial insertion, MOSA is the conduit to maintain focus on protecting service members everywhere, every time, while also driving down cost and increasing production readiness.
architectures to rigorously define open interfaces and the component functionality in-between them. This architectural decomposition facilitates the understanding of a component’s risk relative to the overall system, especially with respect to quality, and provides a low-cost, rapid path to upgradability. In this way, we see that MOSA is the conduit for commercial insertion: A system that performs with defense-grade quality that realizes the cost and production-readiness benefits of commercial products.
However, even within the components, there is still likely a floor to commoditization. Consider, for example, a plug-in card (PIC) that is aligned with the Sensor Open Systems Architecture, or SOSA, Technical Standard. The PIC could include a state-ofthe-art, embedded GPU enabling AI at the edge. However, a commercially available GPU chip that was designed for use in pristine air-conditioned data centers must be “hardened” to reliably perform in a desert summer even after operating for seven hours. This is a realistic example of the floor to the cost benefit of commercial insertion.
As the DoD continues to disrupt old acquisition strategies, MOSA will continue to be pivotal for understanding and mitigating risks to quality due to commercial insertion. The MOSA acquisition strategy creates new and strengthens existing horizontal markets that economically find the right level of commoditization for military equipment. So, as industry drives towards commercial insertion, MOSA is the conduit to maintain focus on protecting service members everywhere, every time, while also driving down cost and increasing production readiness.
Jonathan Cain is Steering Vice-Chair of the SOSA Consortium.
SOSA Consortium • https://www.opengroup.org/sosa

By Reece Byrne
For organizations and engineers in the defense, aerospace, and other mission-critical sectors, upgrading from commercialgrade to JANP [Joint Army-Navy Plastic]-qualified components is a strategic decision that enhances reliability, traceability, and regulatory compliance. A thorough understanding of the distinctions between these component types, as well as the critical factors involved in the transition, is essential to ensuring long-term system performance and safety.
The JANP [Joint Army-Navy Plastic] designation is assigned to military-grade components that comply with JAN standards but are encapsulated in plastic packages instead of traditional hermetic (metal or ceramic) enclosures. JANP-qualified components are engineered and tested to meet the most rigorous industry standards. While commercial-grade parts are suitable for general consumer or industrial use, JANP components undergo extensive electrical, mechanical, and environmental testing, including temperature cycling, vibration, humidity and mechanical shock, to ensure they can withstand the demanding conditions typical of defense and/or space applications. (Table 1.)
Overview: key differences of JANP components
1. Testing rigor: JANP components are subjected to military-grade testing protocols, whereas commercial-grade parts are tested to standard industry requirements.
Feature JAN/JANP Qualification (e.g., MIL-PRF-19500) MIL-PRF-38535 Qualification
Product Type
Qualification Prefix
Standard Reference
Application
Testing & Traceability
Standard Type
Focus
Testing
Discrete semiconductors (TVS, diodes, rectifiers)
JAN, JANTX, JANTXV, JANS
MIL-PRF-19500 (for discretes)
Military, aerospace, high-reliability
Extensive, per discrete device standards
Legacy procurement standard
Traceability, procurement
Standardized, less comprehensive
Certification Not always required
Current Usage Legacy, less common
Table 1 | Comparison of JANP and MIL-PRF-38535 Qualification.
2. Quality assurance: JANP parts offer strict quality controls and consistent lot-to-lot uniformity; commercial-grade components may exhibit greater variability.
3. Traceability: Comprehensive documentation and traceability are mandatory for JANP parts, supporting counterfeit prevention and efficient issue resolution.
4. Regulatory compliance: JANP components meet military and aerospace standards, streamlining certification processes; commercial-grade parts may not.
5. Cost and availability: JANP parts generally have higher costs and longer lead times but deliver superior reliability.
Shift toward enhanced reliability and radiation tolerance
The market is increasingly demanding components that meet higher reliability and radiation tolerance standards, especially for space and rigorous defense applications. Parts that are qualified to military standards such as MIL-PRF19500 – which cover general performance requirements for semiconductor devices – and enhanced low-dose radiation sensitivity (ELDRS) requirements ensure that components can operate reliably in radiation-rich environments. These parts qualifications include both traditional hermetic (ceramic/metal) and high-reliability plastic packages, but the focus is on meeting stringent reliability and radiation requirements rather than on legacy JANP standards alone.
Integrated circuits (ICs, microcircuits)
QML (Qualified Manufacturer List)
MIL-PRF-38535 (for ICs)
Military, aerospace, high-reliability
Extensive, per IC standards
Modern performance specification
Manufacturing, testing, quality
Rigorous, ongoing, updated
Manufacturer certification required
Widely used for new designs
JANP parts, which refer to plastic-packaged components with Joint Army-Navy qualification, are considered legacy. The industry is moving toward more modern qualification standards and performance specifications, such as MIL-PRF-38535 for microcircuits and MIL-PRF-19500 for discrete semiconductors. These newer standards emphasize ongoing quality, traceability and rigorous testing, which are increasingly required for new designs and procurement.
While JANP parts are less common in new designs, they may still be used in legacy systems or where cost and procurement considerations outweigh the need for the highest reliability or radiation tolerance. However, the trend is toward replacing these with parts that meet more current standards, especially as mission-critical and harshenvironment applications become more prevalent.
Many suppliers are expanding their portfolios to include a wide range of high-reliability solutions, including those listed on the Qualified Products List (QPL) for military and aerospace applications. This includes both plastic and hermetic packages, but the emphasis is on meeting the latest qualification and reliability requirements. (Figure 1.)
Transitioning to JANP-qualified components requires careful planning and several critical adjustments.
When transitioning to JANP-qualified components, organizations must make careful design and engineering adjustments, which may include evaluating system designs for compatibility, as JANP components may differ in specifications or form factors compared to commercial alternatives. Additionally, it is important to ensure that the enhanced reliability and environmental resilience offered by JANP parts align with the specific performance requirements and objectives of the project.
Qualification and testing are critical steps when integrating JANP components into a system. Systems may require requalification through additional testing to validate performance and ensure that the new components meet all necessary standards. Furthermore, organizations should be prepared for more comprehensive recordkeeping, as JANP parts necessitate detailed traceability and compliance documentation to support ongoing quality-assurance and regulatory requirements.
Supply-chain and procurement considerations are essential when adopting JANPqualified components. Organizations must carefully vet suppliers to ensure the authenticity of JANP-qualified parts and minimize the risk of counterfeit components entering the supply chain. Additionally, it is important to anticipate longer lead times
and potential availability challenges, as JANP-qualified components may not be as readily available as their commercial-grade counterparts.
Cost implications are also important when integrating JANP-qualified components. Organizations should plan for higher upfront costs, as these components require rigorous testing and certification processes. Total cost of ownership must also be considered, as the investment in JANP-qualified parts can lead to long-term savings through reduced maintenance needs, fewer failures, and increased system reliability.
Regulatory and certification requirements play a critical role when implementing JANP-qualified components. Organizations must ensure strict adherence to all documentation, testing, and traceability requirements to meet military, aerospace, or other relevant standards. Additionally, potential users should be prepared for more stringent audits and regulatory reviews, as certification processes for JANP-qualified components are typically more rigorous than those for commercial-grade parts.
Training and process changes are essential when transitioning to JANP-qualified components. Organizations should provide targeted training for staff to ensure teams are well-versed in handling documentation and compliance procedures specific to JANP components. Additionally, internal processes must be updated to accommodate stricter controls and enhanced traceability requirements, supporting ongoing compliance and quality assurance.
Rigorous environmental testing and traceability
JANP qualification is characterized by demanding environmental tests, including temperature cycling, thermal shock, vibration, humidity, salt spray, mechanical shock, altitude, and life cycle testing. These measures ensure that components can endure the operational stresses encountered in space and other high-reliability applications.
Traceability is another fundamental aspect of JANP qualification. Each component is accompanied by comprehensive documentation, enabling manufacturers to track its origin, batch, and testing history. This step supports quality assurance, counterfeit prevention, efficient issue resolution, and effective life cycle management.
Obtaining and maintaining JANP qualification means integrating quality assurance
To achieve JANP qualification, manufacturers must identify and acquire the relevant, applicable JANP standards. Compliance with these standards typically requires the implementation of a robust quality-management system, such as ISO 9001, that ensures consistent product quality and process control. The qualification process involves both inhouse and third-party testing to verify that products meet JANP specifications. Manufacturers are required to compile comprehensive technical documentation – including test reports, process controls, and traceability records – and submit these materials to the appropriate Japanese certification body.
A critical component of the qualification process is the factory audit, during which auditors assess the manufacturer’s adherence to JANP requirements and quality-management practices. Any nonconformities identified during the audit must be promptly addressed through corrective and preventive actions (CAPA). Upon successful evaluation, manufacturers are granted JANP qualification and are authorized to mark their products accordingly.

JANP-qualified products are subject to ongoing, rigorous quality-assurance requirements to ensure their continued reliability and safety. Manufacturers must strictly adhere to the relevant Japanese Industrial Standards (JIS) for their product category, maintaining detailed documentation for traceability and process control. Supplier quality is managed through the use of approved suppliers and regular audits, ensuring that all materials and components meet JANP requirements. Products must be clearly marked with the JANP symbol and identification codes for traceability.
Quality assurance encompasses stringent testing at multiple stages, including incoming material inspection, in-process testing, and final product testing. Ongoing surveillance, including periodic audits and requalification testing, is essential to ensure continued compliance with JANP standards. In the event of failures or nonconformities, thorough failure analysis and CAPA must be implemented to prevent recurrence. Manufacturers then maintain compliance through regular audits and a commitment to continuous improvement, with these steps ensuring that JANP-qualified products consistently meet the highest standards of quality and safety.
By adopting JANP-qualified components, organizations gain significant advantages, including reduced breakdowns and maintenance requirements that lead to increased system uptime. The use of these components also streamlines regulatory approval and certification processes, making compliance more efficient and straightforward. Additionally, JANP-qualified components enhance organizational responsiveness and issue resolution capabilities, as robust trace ability ensures that any problems can be quickly identified and addressed. Collectively, these benefits contribute to greater reliability, operational efficiency, and regulatory confidence in high-stakes environments.
differences and addressing key considerations – including design compatibility, qualification, supply-chain management, cost analysis, regulatory compliance, and staff training – engineers can facilitate a successful transition and fully realize the benefits of JANP-qualified components in high-reliability projects. MES

Reece Byrne is the senior digital marketing specialist for Microchip Technology’s High-Reliability and RF (HRR) business unit. He leads digital marketing campaigns for a wide range of powermanagement solutions including high-reliability, discretes, integrated power solutions, as well as radio-frequency and microwave technologies. He holds a BS degree in strategic marketing communications from Saint Cloud State University (Minnesota).
Microchip Technology https://www.microchip.com/




Transitioning from commercial-grade to JANP-qualified components is a strategic decision for organizations seeking to maximize reliability, safety, and compliance. By understanding the


By Editorial Staff

Each issue, the editorial staff of Military Embedded Systems will highlight a different organization that benefits the military, veterans, and their families. We are honored to cover the technology that protects those who protect us every day.
This issue we are highlighting the Yellow Ribbon Fund (YRF), a nationwide charity that helps returning U.S. service personnel injured during active duty, most of whom are recovering at Walter Reed Army Medical Center and Bethesda Naval Hospital. The 501(c)(3) charity – which recently marked its 20th year of serving military veterans – has as its stated aim to enhance the lives of military families facing medical crisis and recognize the importance of keeping returning service members’ families together during the critical recuperation phase.
The organization was founded in 2005 by a group of business owners near Walter Reed and Bethesda Medical Center who realized that families of service members at the facilities needed shelter, caregiver support, and other resources. Over the next few years, the YRF expanded nationwide to 10 chapters; the organization runs various events and programs, arranged by staff and volunteers, aimed at helping patients and their families stay together and begin to heal. The YRF runs parties for personnel and families, outings and trips, and even weddings.
Two of the major YRF programs are Crossroads and Keystone: Crossroads provides practical support to post 9/11 active-duty and disabled veterans by offering rental cars, hotel stays, and fully-furnished apartments at no cost to the families while the personnel are receiving medical treatment. Keystone takes that concept a bit further, offering families the chance to participate in recreational and respite events, fitness and wellness activities, life-skills training and educational classes, networking, and peerto-peer support, all of which the organization says work to boost morale, promote self-care and resilience, and foster friendships and family bonding.
For more information, visit https://yellowribbonfund.org/.
Time-Sensitive Networking for Modular Open Systems: A Low-Risk Path to Integration
Sponsored by Dorner Works and Wind River
As the U.S. Department of Defense (DoD) accelerates adoption of modular open systems approach (MOSA) architectures, programs must solve the challenge of unifying mixedcriticality systems and next-generation digital backbones without increasing integration risk. Time-sensitive networking (TSN) has emerged as a key enabler – delivering deterministic, low-latency Ethernet that unifies legacy and modern systems on a common digital bus. Yet deploying the Aerospace TSN Profile in safety-critical, resource-constrained, and multi-vendor environments introduces real hurdles in certification, interoperability, and compliance. In this webcast, attendees will learn how the companies’ combined approach to solving these problems not only accelerates MOSA adoption but also directly supports risk reduction in modernization and new start acquisition programs. (This is an archived event.)
View this webcast at https://tinyurl.com/3bdwnk23
View more webcasts at https://militaryembedded.com/webcasts.
By Anritsu
Submarine optical cables form the backbone of global communications, carry ing the majority of the world’s rapidly expanding internet traffic that is driven by cloud computing, Internet of Things, and artificial intelligence (AI) tasks. As cable systems grow in scale and complexity, accurate testing and fault identification become essential to ensure reliability. This white paper provides an overview of submarine cable architecture, the need for precise diagnostics, and the role of Coherent Optical Time Domain Reflectometry (C-OTDR) in long-distance fault location. By leveraging coherent detection and submarine repeater return paths,C-OTDR enables highly sensitive measurements at practical DWDM [dense wavelength division multiplexing] wavelengths, even across extremely long spans that can exceed 20,000 km (12,427 miles). The white paper also highlights the effectiveness of advanced C-OTDR solutions – including Anritsu’s MW90010B – in enabling rapid, accurate fault detection and full characterization of submarine fiber infrastructure.
To view this white paper: https://tinyurl.com/mr2bhsnw
To view more white papers: https://militaryembedded.com/whitepapers.
By Mark Benton, TE Connectivity
Modular optical transceiver platforms are essential for modern military embedded systems, offering flexibility, scalability, and robustness. Technologies such as VPX, LEP, MULTIGIG RT, and CBOT provide adaptable solutions that meet the stringent demands of defense applications.
Modularity is a crucial aspect of signal processing and communication in modern military embedded systems, especially in environments where adaptability, durability, and performance are nonnegotiable.
Fiber-optic-rich systems – such as avionics displays, radar, command and control, secure network communications, and surveillance –require modularity to adapt to varying mission requirements and operational environments. These systems must accommodate rapid upgrades and repairs, often in harsh conditions.
A modular setup of rugged fiber optics (RFO) and other components can deliver a strong solution to these challenges. This approach offers the flexibility for components to be more easily upgraded, repaired, or replaced without the need for complete system overhauls or putting overall system integrity at risk.
Systems based on VPX (VITA 65) standards for real-time data processing, high-speed data transfer, and reliable connectivity can especially benefit from modular designs. Common examples of modular designs built to VPX standards include software-defined radio (SDR) systems and Ethernet communication systems; and radar, cameras, and other imaging for surveillance systems, which could include analog-to-digital conversion and artificial intelligence (AI)-trained post-processing analyzers. Modularity within each of these systems pairs well with VPX standards to enable rapid integration of new high-performance technologies and functionalities.
RFO transceivers in embedded systems
RFO transceivers enable reliable communication in embedded systems through high-speed data transmission. Rates currently go up to 28 G, with 56 G PAM 4 on the development horizon. They are durably designed to provide consistent performance and withstand temperature extremes, vibration, and moisture.
Here are two examples of RFO solutions offering modularity today:
› Ruggedized parallel mid-board transceiver technology: Mid-board transceiver (TRx) technologies offer scalable, high-density RFO solutions for military systems within a miniaturized physical footprint. Parallel optical channels also allow high data throughput directly on the printed

circuit board (PCB), which greatly cuts down on signal loss. Within the mid-board quad TRx are quad verticalcavity surface-emitting laser (VCSEL) arrays, VCSEL drivers, quad photo diode arrays, transimpedance amplifiers (TIA), and limiting amplifier application-specific integrated circuit (ASICs), which are similar to those found in many data communication modules operating at similar speeds. These transceivers support modular integration, enabling easy upgrades and maintenance in the field.
› Modular RFO options with chiclet-based optical transceivers: Chiclet-based optical transceivers (CBOT) enable a modular approach that allows the combination of different fiber optic transceiver functionalities within a single platform. These platforms integrate seamlessly into existing VPX systems, providing flexible and scalable optical communication solutions. CBOT modules also offer a range of data processing rates, fiber types, and custom configurations.
Light engine platform: a fingertip-size 10G transceiver Instead of separate transmitters and receivers in fiber optic networks, defense systems can benefit from designing complete transceivers directly into the optical link. One such solution is light engine platform (LEP) optical subassembly.
This approach to optical transceivers features the power of 10G packaged to the size of a fingertip. For example, four commercial off-the-shelf (COTS) datacom-style dual receivers can be replaced with eight CBOT Rx blades. That leads to an area savings of approximately 70% on the printed circuit board (PCB), resulting in simpler fiber-optic harnesses. At the system level, this move frees up space to add other functionality to the PCBA. These solutions include both the CBOT assembly and the required VITA 66.4 connector, simplifying procurement and system assembly.
of modularity
The advantages of modularity in military embedded systems address several technical challenges, including signal integrity, thermal management, electromagnetic compatibility, and dataprocessing rates. These advancements, along with ongoing research and development to address signal-processing and communications-system connectivity challenges, further enhance the modularity and performance of rugged optical transceivers in the ever-evolving defense industry.
Mark Benton is Senior Principal Development Engineer, Rugged Fiber Optics, TE Connectivity.
TE Connectivity • https://www.te.com/