IMPACT REPORT
Networking Platform Sponsor
Networking Cocktail Sponsor
The rapid transition to the digital world caused by the pandemic has allowed cybercriminals to take advantage of companies’ security gaps, putting both businesses and clients at risk. In addition, criminals are exploiting inherent human behaviors to gain entry to business networks, while self-learning and increasingly sophisticated cybersecurity threats are forcing experts to reconceptualize security controls in consideration of known industry vulnerabilities and operational fluidity.
These sensitivities have created a need for niche industry solutions that led to the proliferation of specialized cybersecurity services and solutions. The booming cybersecurity field is now considered a fixed business expense regardless of industry or size. This seismic shift has had a direct impact on the role of company CIOs and CISOs, whose role has significantly expanded beyond their traditionally isolated information technology oversight and management role. The redirection of CIOs and CISOs’ responsibilities toward service and analysis speaks to risks and opportunities of a digitalfirst economy born from the limitations of the COVID-19 pandemic.
During Mexico Cybersecurity Summit 2022, industry leaders highlighted the importance of cybersecurity in consideration of such volatile digital architectures. Divergences in composition have created new cybersecurity needs that have yet to mature and stand to benefit from retroactive feedback between clients and experts. As the premier event of Mexico’s emerging cybersecurity sector, Mexico Cybersecurity Summit 2022 provided an ideal space for key decision-makers to share their perspective and build a discussion around the latest trends affecting all industries and sectors of the Mexican economy.
89 companies
278 conference participants
40 speakers
06 sponsors
1,104 visitors to the conference website
Mexico’s leading B2B conference organizer introduces the world’s leading event networking platform.
Breakdown by job title Conference social media impact
3,774 direct impressions during MCS 5,436 direct pre-conference LinkedIn impressions 3.958% click through rate during MCS 2.835% pre-conference click through rate

Delivering intent-based matchmaking powered by Artificial Intelligence that connects the right people. Network, no matter where you are.
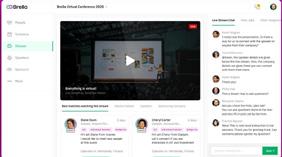


129 participants
236 matchmaking communications
22 1:1 meetings conducted
Matchmaking intentions
1,451
• A3Sec
• ACCIONA
• A e S MCAC
• Akza Advisors
• AMCHAM
• AM e XICOM
• Arista Technologies
• Astrazeneca
• Atlas Copco Mexicana
• BAN yAX
• Betterware
• BIVA
• Brella Ltd
• CB re
• Cisco Thousand eyes
• Coca Cola fe MSA
• Comercial city fresko
• Crowdstrike
• CyberIIoT
• Cybolt
• Darktrace
• DIGIX
• Disc IT Business Solutions
• DLC CO r PO r ATIVO
• DuPont
• e AS yS eC
• eGlobal
• e N e L G ree N POW er
• e nermex
• etek international
• femsa
• f ibra Uno
• f link
• G e
• General Motors
• GMX Seguros
• Grupo Aeroportuario del Pacifico
• Grupo Akron
• Grupo Autocom
• Grupo Bimbo
• Grupo La Moderna
• Grupo Salinas / Totalsec
• HCL Technologies
• HDI Seguros
• Huawei Mexico
• ICA f luor
• IC e , Israel Cybersecurity e nterprise
• IN ee L
• Instituto Tecnológico de Veracruz
• Inter
• Invex
• Israel Commercial Office in Mexico
• IV e MSA
• Kaspersky
• Klustera
• KPMG MX
• Laboratorios Sanfer
• Latino Seguros
• Majorel
• Mandiant
• Mexico View
• Mexico Business
• Microsoft
• minu
• MIT eC
• Molinos del fenix, S.A de C.V.
• NautechMX
• Netskope
• N e UBOX
• Nyx technology
• Pizarro Suárez & Bandala Abogados
• P r OSA
• Protectia
• Santander
• Scotiabank
• Shell & Quaker State México
• Siemens
• Tanium
• TCS México
• Telefónica México
• Terumo Latin America Corp
• T e ST
• Tokio Marine Mexico
• u-Storage
• Utilities
• Von Wobeser y Sierra, S.C.
• Womcy
• X Design
• Zacsoft
• Zenda.la
09:00 ADAPTING CYBERSECURITY THREATS
Moderator: Carlos Alanis, Banyax
Panelists: Luis Padilla, Crowdstrike
Felipe García Vivanco, Scotiabank
Alessandro García Álvarez, Tanium
Gustavo Adolfo García Arellano, Christus Muguerza
10:00 THE EVOLUTION OF DIGITAL INFRASTRUCTURES
Moderator: Erika Sánchez, ANUIeS - TIC
Panelists: Julia Urbina, CyberIIot
Brenda Zetina, Datadog
Manuel Diaz, Huawei Technologies Mexico
11:00 NETWORKING OPPORTUNITY
12:00 FINTECH & BANKING CYBERSECURITY VULNERABILITIES
Moderator: José Andrés Chávez, Bayonet
Panelists: Jorge Lozano, Mandiant
Valther Galván, Prosa
13:00 INDUSTRIAL CYBERSECURITY
Moderator: Vanessa Padua, Microsoft and WOMCy
Panelists: Patricia Fragoso Soto, Volkswagen Mexico
Alexandro Fernández, Coca-Cola feMSA
Oscar Jaramillo, enermex
Juan Gálvez, BIVA
14:00 NETWORKING OPPORTUNITY
15:00 UNIQUE SECURITY CHALLENGES IN THE CLOUD
Moderator: Juan Carlos Carrillo, PwC
Panelists: Arnulfo Espinosa Domínguez, IM ef, AreS and ISACA
Óscar Octavio Salgado Álvarez, AMIS
Francisco Carlos Martínez, Santander
Lorena Bravo, Oracle
09:00 CIO’S (CISO’S) & CYBERSECURITY
Moderator: Erik Moreno, Minsait
Panelists: Elvira Sánchez, DHL
Heriberto Landetta, GM México
Antonio Saracho, Grupo Coppel
10:00 ATTRACTING AND DEVELOPING CYBERSECURITY TALENT
Moderator: Aimed Pimentel, WOMCy Mexico
Panelists: Jenny Mercado, Betterware Mexico
José Arriaga, Tokio Marine
Valther Galván, Prosa
11:00 NETWORKING OPPORTUNITY
12:30 HUMAN BEHAVIOR’S ROLE IN SECURITY BREACHES
Moderator: Elizabeth Jáuregui, ericsson
Panelists: Bismarck Animas, feMSA
Erwin Campos, Bimbo
Miguel Porfirio Camacho, AMIS
13:30 NETWORKING OPPORTUNITY
15:00 AI & ML: DOUBLE EDGED SWORDS
Moderator: Israel Gutiérrez, A3Sec
Panelists: Alfredo Sastre Barraza, CSOf TMT y David Casillas, Nyx Technology and Pixframe Studios
Daniela Hernández, AM e XICOM
Pablo Carrillo, Darktrace
16:00 ISRAEL: NEWEST PARTNER IN MEXICO’S CYBERSECURITY ECOSYSTEM
Speaker: Sneer Rozenfled, Cyber 7 and Cyber 2.0
EVOLVING CYBERSECURITY THREATS CALLS FOR A RETURN TO BASICS
The digital transformation changed the playing field for cybercriminals, prompting them to adapt their strategies to navigate and exploit vulnerabilities. These interminable and increasingly sophisticated cybersecurity threats have forced companies to return to cybersecurity basics, reconsider security priorities and foment organizational communication, according to industr y experts.
“After the pandemic, the range of attack extended due to home office schemes and the migration to the cloud. The challenge is to adjust our security position in this new reality,” said Luis Padilla, Manager Mexico, Crowdstrike.

“After the pandemic, the range of attack extended due to home office schemes and the migration to the cloud. The challenge is to adjust our security position in this new reality”
learning and adaptation process to lead the charge against cybersecurit y threats.
| Crowdstrike
Luis Padilla Country Manager Mexico
The limitations imposed by the COVID-19 pandemic left companies with little recourse other than to adopt and implement new technologies, often without the usual strategic and security preparation. The accelerated migration towards cloud and edge computing services effectively erased the infrastructure limitations that companies were used to monitoring, thereby inadvertently creating risk opportunities for cybercriminals to exploit. The shifting nature of digital infrastructures have therefore “changed the security objectives that companies should consider when formulating security controls,” said felipe Garcia, CISO, Scotiabank. Consequently, companies should understand that security controls will need to continuously adapt in response to evolving cybersecurity threats. This requires an unrelenting
To do so, companies need to be fully cognizant of their digital infrastructure, a callback to a cybersecurity fundamental: infrastructure audits. The traditional security protocols have become outdated in part because digital infrastructures have changed, effectively compromising the visibility companies need to protect against cybersecurity threats. This recomposition has not only introduced new access points, it has also changed internal organizational and consumer-facing processes. This reorientation has introduced a new layer of complexity that has made previous organization security protocols obsolete. In response, companies were obligated to take a step back and conduct inventory audits to achieve the “full spectrum visibility they needed to identify gaps and update security protocols accordingly,” said Alessandro Garcia Álvarez, Technical Solutions Director, Tanium. The added element of organizational process has introduced a new element to cybersecurity coordination, which has led to more holistic security controls and protocols.
Cybercriminals have reacted in turn, adapting their tools to reflect a new digital reality, consequently “forcing cybersecurity professionals to reassess their understanding of how these threats function,” said Gustavo Garcia Arellano, Chief Information Security Officer, Christus Muguerza. furthermore, cyberthreats have become increasingly sophisticated, learning to appear and mimic the appearance of professional services that are particularly hard for non-specialists to identify. This points to a growing trend among cybercriminals to target end-users; which in turn requires companies to implement awareness and education campaigns, said Garcia Álvarez. Compounding this concern is the known investments cybercriminals have been allocating toward AI and robotics
to augment the apparent legitimacy of disguised security threats. More troubling yet, this is only one application of the many that have extrapolated from adversarial AI.
Another preoccupation for cybersecurity professionals concerns the apparent independent mutation of malware enabled by artificial intelligence and machine learning. Malware now presents the ability to hide its identity in the face of detection efforts, in turn forcing security experts to double their efforts towards the identification of system anomalies, said Garcia Álvarez. An added aspect of this ability implies that this threat is able to wait, embedded within a system, and activate when it seen most opportune. This is forcing security experts to keep records of all retrospective analyses so if necessary, when a threat is flagged by
the cybersecurity community, experts know exactly where in their infrastructure to check for dormant threats in their system. This is a saliently important ability considering the norm of disaggregated digital infrastructures.
To augment the effectiveness of threat campaigns, cybercriminals have also begun to deviate from their modus operandi concerning their strategic approach to entry. Most recently, experts have observed the fragmentation of threats, which are capable of bypassing security checks as individual components and then rejoining once inside the digital infrastructure. This challenge was resolved with the register of individual components of a greater threat, information that was shared with a larger cybersecurity community.
THE SAFE EVOLUTION OF DIGITAL INFRASTRUCTURES REQUIRES EDUCATION
Companies have moved away from singular on-premise networks, as evidenced by increasingly disaggregated digital infrastructures that use multicloud and edge deployments. This evolution is only starting, with digital infrastructures responding and adapting to the introduction of new technologies and cybersecurity protocols. This growing digitalization will open businesses to more complex cybersecurity threats, which will only be mitigated through new and innovative security s trategies.

“Companies can base their risk assessment through a NIST Cybersecurity Framework, which has five core functions; identification, protection, detection, response and recovery, and can be used from SMEs to governments to analyze their tangible and non-tangible assets under one profile”
Julia Urbina CISO | CyberIIot
After the COVID-19 pandemic, 47 percent of IT decision makers said their organizations had accelerated their digital transformation initiatives, while 60 percent said the pandemic forced them to revisit and revise their IT strategy, according to the results of the e quinix 2020-21 Global Tech Trends Survey (GTTS).
There are five main risks that can arise when evolving the digital infrastructure. “The first one arises when companies try to digitize what is not digitizable or should not be digitalized. The second one comes as a result of an accelerated process that skips tools and processes for this digitization. The third is an inadequate integration, the fourth is the acquisition of products that do not necessarily benefit the environment and the last one is failing to comply with privacy and security regulations,” said Julia Urbina, CISO, CyberIIot.
The right processes for a digital infrastructure evolution enable organizations to adapt to technology

trends dynamically so that when the need arises, they can rapidly assemble and reassemble the right building blocks and resources. In many ways, the ability to interconnect with partner and customer ecosystems is key to helping organizations realize the true value of their digital infras tructures.
“Companies have now realized the value of cybersecurity and how they use it to evolve their organizations and achieve business continuity in a better way than they could achieve it without tech. Now, the IT team reports to the Security team and not the other way around. This is already bringing benefits to companies and final users,” said Brenda Zetina, Territory Director, Datadog.
This transition needs integrated planning to be organized. All facets of the business, such as customer service, H r , IT, sales and management, must work together to review their current systems and the data generated as part of their daily operations, explained Manuel Diaz, Director of Cybersecurity and Privacy Protection, Huawei Technologies México. Using that information, companies should define a path to connect their data, break information silos and share their knowledge to become smarter. Integration planning can improve the experiences of customers, employees, business partners and every other player involved in th e company.
Through integration, companies can define corporate priorities, develop
functions and responsibilities in all areas of the company, have a clear and updated corporate legislation and ensure they comply with national regulations to avoid being penalized for legal breaches.
In this integrated ecosystem, cybersecurity must be a priority, especially as no one is exempt from risks in these rapidly evolving environments, said Zetina. Thus, companies need to have a unique source of information on what is happening to reduce risks with end customers and the company itself. Communication and training are also essential. “Training and awareness for employees in security areas is also fundamental as they can also be a target of threats,” said Diaz.
Other effective ways to reduce risks include incorporating multifactor recognition and ensuring the clarity of connection processes from network to users and physical security mechanisms because “not all people work from the office and many companies have third parties where information is shared,” said Diaz.
Cybersecurity in the cloud is also key, said Urbina. In the past year, companies have struggled to secure their cloud infrastructure given that their inherent disaggregated design has introduced multiple entry points for cybercriminals to exploit, MBN reported.
These security gaps, which normally form during the initial onboarding process and more commonly during changes between different cloud service providers, constitute
the leading cause of cloud data breaches. Companies lack the know-how and the security tools to protect their public cloud infrastructure even as they are considering the addition of other cloud services. “Thus, authentication is also fundamental in this step, not just for our direct collaborators but also for our third parties and cloud providers,” Urbina said.
Nonetheless, “there are systems that can help companies achieve a safe digital space and infrastructure at all levels,” said erika Sánchez, Coordinator, Women’s ANUI e S ICT Network Mexico. These measures
include making cybersecurity part of the basic culture of companies, establishing a collaborative relationship with providers, regulatory clients and academia and investing in the r &D of further tools that can support the company.
“Companies can base their risk assessment through a NIST Cybersecurity framework, which has five core functions; identification, protection, detection, response and recovery, and can be used from SM e s to governments to analyze their tangible and non-tangible assets under one profile,” said Urbina.
SPOTTING VULNERABILITIES IS CRUCIAL FOR FINTECH, BANKING SECURITY
financial transactions are a natural target for cybercriminals. fintech companies and traditional banks are governed by strict cybersecurity regulations and must be careful when exchanging data due to the risks and vulnerabilities involved in the process, agreed industr y experts.

“Whether it is a third-party provider or not, you will always need someone in-house to manage those third parties. It does not have to be a large team, but there should be a person that can
coordinate all the security efforts and has enough expertise”
Jorge Lozano Information Security Manager | Mandiant
“Companies operating in financial services are targets of various forms of crime and fraud. Now, in the post-pandemic era, we have learned that data is necessary. The exchange of information between financial institutions is key. However, there are important risks to take into account too,” said Valther Galván, CISO, Prosa.
fintech companies handle the same types of financial data as banks, including account information, balances, cash flow data, budgets and contact information. These
companies aim to store as much specific and useful data as possible due to the high value of this information, particularly for AI and machine learning (ML) projects. However, storing large volumes of data makes these companies a more valuable target for cybercriminals.
When it comes to exchanging data, involved players must decide which information they will share, said Galván: “We have a filter according to regulations and global standards that forces us to have a very clear scope of what data will be shared. f or large amounts of data, it is important to implement AI and au tomation.”
While it became more popular after the pandemic, data exchange is nothing new, said Jorge Lozano, Information Security Manager, Mandiant. f inancial service companies leverage data to manage risks and position their brands, and the main challenge for these organizations is to work jointly to properly manage the risk scenarios they might face, he added.
Whether it is a traditional bank or a fintech company, the cost of a breach includes both direct and indirect costs, such as reputation damage and fines. A single breach could also drive
thousands of customers away. In the case of fintech startups or companies that are experiencing hypergrowth, loss of customer trust and reputational damage may be the costliest aspect of a breach.
r eputation plays an essential role within the fintech and banking environments.
“ r eputation, or the public opinion about somebody or something, is a concept we take in consideration for most decisions in society,” wrote for MBN José Andrés Chávez, Co- founder and C eO, Bayonet.
Among other cybersecurity best practices, organizations must be committed with securing customers’ data and be prepared to handle possible breaches when they happen, said Lozano: “It is not a matter of whether it will happen to me or not, but when it happens to me, how will I react?” Assertive, transparent and clear communication is a crucial part of crisis management, he added.
The establishment of appropriate controls and policies to reduce cybersecurity risks is both a matter of organizational culture and deploying the right toolset, according to IBM. Building a strong cybersecurity stance provides insight into threats and helps ensure regulatory compliance. “We test our processes through plans. We do
exercises, cyberattack simulations to prove that our processes work,” sa id Galván.
When it comes to data exchange and there are two or more involved players, they must work as a team to map the security architecture of all companies involved, said Lozano. Creating a collaborative environment for all organizations involved is crucial, he added.
The pandemic helped companies across all industries to realize the importance of cybersecurity and invest accordingly, said Galván. The main keys for companies to successfully implement cybersecurity include the implementation of a holistic and clear strengths, weaknesses, opportunities and threats (SWOT) vision in terms of data security, avoiding investments directed to projects intended only for parts of the entire security infrastructure and remaining aware of the global situation, he added.
On the other hand, companies must take care of their teams working on cybersecurity, said Lozano: “Whether it is a third-party provider or not, you will always need someone inhouse to manage those third parties. It does not have to be a large team, but there should be a person that can coordinate all the security efforts and has enough expertise.”
HELPING OT CYBERSECURITY MATURE: AN INDUSTRIAL CONCERN
While company leaders look forward to the applications and the increase in productive capacity promised by the operational
technology of Industry 4.0, companies need to consider how they will protect these assets from cybersecurity threats.

The central challenge industry experts will confront during this experimental phase concerns bridging operational technology (OT) cybersecurity preparedness to that of more mature IT departments, according to industr y experts.
“Dependence on technology has potentiated new risks that go hand in hand with technology development. New challenges will probably arise,” said Juan Gálvez, CISO, BIVA.
Until recently, OT assets had been protected from cybersecurity threats by an isolated, “air-gapped” network environment. This operational model became obsolete overnight with the rise of smart devices that require direct network connectivity to generate data about operational productivity. This migration has created a convergence between OT and IT, thereby creating added concerns about cybersecurity preparedness between these technology assets and managing departments.
This knowledge gap has created a sense of urgency among industrial field experts who only have to look to the Colonial Pipeline Hack and others to understand the potentially devastating impact of a potential breach. This learning process has only begun, however, with many companies trying to “identify and formulate a security baseline in consideration of independent operation needs,” said Oscar Jaramillo CIO, enermex.
The reigning concern and focus of industrial companies is trying to precipitate
the identification of vulnerabilities and developing security controls in response. This effort is complicated by the parallel “transformation industrial companies are undergoing with the addition of new technologies and digital infrastructure reconfiguration,” said Alexandro fernández, Head of Cybersecurity OT, Coca-Cola feMSA.
This metamorphosis implies a seismic transformation and calls for education among industries that were previously sheltered from cybersecurity threats, requiring OT and IT departments to work side by side to “develop transparent security controls in consideration of both operational fluidness and security compliance standards,” said Gálvez. This is an all-new process for industrial companies and cybersecurity companies alike, a transformation that also stands to bring these parties closer so horizontal security needs can be developed at the same pace.
So far, the top priority for companies concerns establishing the variable constant removed by Industry 4.0: network security. e stablishing controls and monitoring network security help strengthen the network perimeter and “should be the primary concern of industrial companies,” said fernández. furthermore, as companies work to reconfigure their digital infrastructures, they should also consider recognized best practices such as layering independent networks, one for OT and another for IT so that in the worstcase scenario companies can control the blast radius of a security breach to one network segment. While conceptually this

sounds straightforward, it is highly complex to implement in practice because it also requires the simultaneous implementation of security controls. This implementation process must also consider the formation of “robust security protocols at the point of interconnection between OT and IT networks”, said Jaramillo.
Other practices considering network security concerns the adoption of Zero
Trust protocols, as a means of circumventing malicious data access from anywhere as enabled by cloud and edge computing. This is particularly relevant for industry sectors that routinely receive petitions for updates and support from public IP addresses, said Jaramillo. Companies should also consider contingency plans to protect data assets either through direct, cloud or disaggregated storage practices, said Patricia fragoso Soto, Manager IT, Volkswagen Mexico.
CLOUD PROVIDERS, USERS SHARE SECURITY RESPONSIBILITIES
While cloud computing services have been celebrated for enabling the digital transformation, their rapid assimilation has inadvertently created unique opportunities for cybercriminals to exploit. Protecting against these threats is a responsibility equally shared by the cloud provider and the customer, agreed industr y experts.

“Companies will need to explain and recommend what to do with the leaked information. These companies should also have a crisis group ready to mitigate the impacts of the leak. Doing nothing greatly affects their image”
Óscar
Octavio
Salgado Álvarez
CIO | GMX
“There are responsibilities of providers and of clients. Although the cloud is softwareas-a-service (SaaS), about 85 percent of the settings to control it belong to customers and depend on them to be configured,” said Arnulfo e spinosa Domínguez, President of Tech and Cybersecurity, CT IM ef, and President, A re S Alliance.
Cloud security involves a broad set of technologies, policies, controls and services that protect cloud data, applications and infrastructure from threats. The security responsibilities that always belong to the cloud providers pertain to safeguarding the infrastructure itself. They also involve measures necessary while providing access, patching and configuring the
physical hosts and networks on which the computer instances run, according to Checkpoint. The customer’s security responsibilities include managing users and their access privileges (identity and access management), safeguarding of cloud accounts from unauthorized access, encrypting and protecting cloudbased data assets and managing their securit y posture.
Under this model, each player is responsible for what is under their control. “If you can configure various privacy and security settings, you have to do it and also back up the data that is in the cloud because it can also be lost. Thus, it is important for companies to generate cyber resilience,” said Oscar Salgado, CIO, Grupo Mexicano de Seguros, and President, Tech Committee, AMIS.
Companies must also be aware that in the cloud there is no perimeter to protect like on a premise. “On-site systems allow companies to know the number of computer equipment present on premise, their configuration and the physical space they use, but in the cloud there is no perimeter, the infrastructure is shared with other users unless it is private,” said Salgado.
The new hybrid cloud model is causing further challenges. for that reason, a homogeneous strategy and a coherent infrastructure are fundamental and can be achieved by documenting each cloud a company has and developing a personalized treatment and approach for each, said espinosa.

To have a clear sense of shared responsibility, companies must ensure they have clear control objectives, explained f rancisco Carlos Martínez, Head of Security Architecture, Santander. “The cloud is an extension of the data center and it is also an infrastructure of different actors and services. Thus, assuming responsibility for safety is implied. Nonetheless, regulations still have to be clear on the responsibility between cloud provider and customer in case of breaches,” said Martínez. f urthermore, contracts should include a clause with security requirements and compliance with standards, he added.
While a fast response is key, security should be implemented from the ground up. “We must not forget that there is a fundamental step that can set the ground for a much safer cloud and this is its configuration from the very beginning,” said Lorena Bravo, CTO, Oracle. Bravo said that 65 percent of breaches in cloud were caused by poor configuration, 43 percent of those by the use of unencrypted bases. “Companies do not identify the catalog of sensitive data, so they cannot create the perimeter to protect it nor create a security strategy to prevent [attacks],” said Bravo.
The Privacy by Design (PbD) concept holistically aims to embed privacy into the earliest phase of the development lifecycle. “Data protection through technology design will protect data processing procedures and will help these processes to best integrate to the technology,” said Juan Carlos Carrillo,
Director Cybersecurity, Privacy & forensic Services, PwC. However, in the worse-case scenario in which a company suffers from a data breach, transparency with its clients is the best policy, according to Carrillo.
Transparency with those affected will damage the final user’s confidence less than keeping the data breach secret, said Salgado. Preparedness is also key. “Companies will need to explain and recommend what to do with the leaked information. These companies should also have a crisis group ready to mitigate the impacts of the leak. Doing nothing greatly affects their image,” said Salgado. Also essential is reporting data breaches to other cybersecurity companies to avoid similar attacks, said Carrillo.
Many companies are unprepared and slow to react to cybersecurity attacks. “When a cyberattack is successful, it takes 2.5 weeks for the affected company to notice the breach and it takes it three more weeks to mitigate it,” said Bravo. This slow response calls for a more proactive approach to cybersecurity. “We can no longer have reactive cybersecurity models. Instead, we need continuity plans,” s aid Bravo.
f or companies to have a safe cloud, “shared responsibility, transparency, best practices and sticking to regulatory processes are to be the fundamental steps to follow after a company has integrated PbD on its cloud,” said Martinez.
CIOS, CISOS ROLE IS SHIFTING TO SERVICE ANALYSIS, CYB ERSECURITY
The COVID-19 pandemic accelerated the digital transformation across most industries, giving greater visibility to the work done by the Chief Information Officer (CIO) and the Chief Information Security Officer (CISO) executives. With new technologies propelling the digital disruption, the focus of the CIO has shifted to service analysis, market reach and cybersecurity rather than running the IT department, agreed industr y experts.

“With cloud solutions available, the cost is more affordable for companies, including SMEs. At GM, we are developing a cybersecurity strategy that includes our dealership network and suppliers. We want to raise the bar for them.”
Heriberto Landetta IT Senior Manager | GM México
Digital consumption habits have changed in Mexico, with the massive migration to digital, online shopping and communication in a hyperconnected world, said e lvira Sánchez, CIO, DHL: “ ensuring the security of operations is vital and has become the main challenge for CIOs and CISOs. With the growth of cybercriminals, we invest strongly in technology, shipment protection and protection of personal data of clients and collaborators. One of the main challenges is developing cybersecurity systems for the unknown because it requires constant understanding and training of the entire organization. It is not enough to install hardware and software; you have to detect and address the true vulnerabilities of the company.”
CIO is a C-suite job title given to the executive in charge of information technology initiatives and strategy. The CIO role, which was established in the 1980s, oversees the computer systems required to support the organization’s unique objectives and goals, according to TechTarget. Initially, the CIO
focused on managing technical projects and systems, leveraging technology to increase efficiency and cut costs. As storage and analysis of data grew in importance for companies, the job has evolved and CIOs now lead digital transformation initiatives, forging closer ties with the business side of their organizations.
The pandemic accelerated the transformation of retail and e-commerce businesses. f or example, nationwide department store Coppel took a leap into omnichannel sales. “The challenge for digital transformation here is large. We are moving from controlled, physical environments to different channels that are public. r egarding omnichannel sales, we already do transactions via WhatsApp, mobile applications and webpages,” said Antonio Saracho, CIO, Grupo Coppel. While these systems offer greater sales opportunities to companies, these transactions become very complex and challenging for both CIOs and CISOs, he added.
The CISO is a senior-level executive responsible for developing and implementing an information security program, including procedures and policies to protect company communications, systems and assets from both internal and external threats, according to TechTarget. Besides responding to data breaches and security incidents, CISOs must anticipate new and emerging threats and work with other executives across the company to align security initiatives with broader business objectives.
“We work together with the CISO on indepth analysis to assess risks and to carry out intelligent monitoring to understand patterns. Current challenges demand a preventive approach to problems, not just a reactive one. Cybersecurity has become a very complex career and collaboration is crucial,” sai d Saracho.
Cybercriminals continuously expand their capabilities to take advantage of limited
security awareness among companies. With multiple attack vectors, “attackers have become more sophisticated and target victims’ weaknesses, forcing CIOs and CISOs to change strategies to face them,” said e rik Moreno, Head of Cybersecurity Advisory Services , Minsait.
The sophistication and expansion of capabilities of cybercriminals force companies to make larger investments to strengthen their cybersecurity strategies, said Heriberto Landetta, IT Vehicle Sales Marketing and Aftersales Manager, GM México: “There are two main pillars to build a robust security strategy. f irst, the technical elements, which include hardware, software and firewalls to face attacks. Second, training for internal staff to handle certain emails, avoid phishing, ransomware and staying firm in the face of uncertainty. It is important that we make people see that information is the company’s most importa nt asset.”
With the emergence of new technologies and the acceleration of the digital transformation, CIOs have had to develop skills that go beyond traditional technology management. Although responsibilities of CIOs vary according to their organizations, industry and region, these executives are in charge of innovation and collaboration. They must also balance the IT budget and the motivation of th eir staff.
It is essential to have a robust security system that guarantees the security of data
of clients, employees, third-party companies and suppliers, said Sánchez: “Nowadays, we have almost everything in the cloud and at DHL we are very strict with regulatory compliance. The protection of sensitive data is crucial to a trusting relationship with our clients. forty-five percent of organizations have experienced some sort of attack on supply chain software.”
Cloud Computing Is Key to Democratize Innovation
Cloud computing transformed the way software is built and who gets to build it. Before the cloud, only big companies had access to the highly skilled talent and the massive hardware infrastructure required to build software products, as reported by f orbes. Cloud computing tools like Amazon Web Services, Microsoft Azure and Google Cloud Platform, among others, have democratized software development, which has become available for companies of any size and budget.
While Coppel focuses on omnichannel sales and the cybersecurity challenges around them and DHL reinforces its sensitive data protection and supply chain software security, GM is working on a 360-degree cybersecurity strategy, said Landetta: “With cloud solutions available, the cost is more affordable for companies, including SM e s. At GM, we are developing a cybersecurity strategy that includes our dealership network and suppliers. We want to raise the bar for them.”

As the digital transformation continues expanding among businesses, the joint work done by CISOs and CIOs is no longer delimited to regulatory compliance, said
Saracho: “The digital transformation continues changing business lines and these executives are now part of the strategic teams of companies.”
INTERNAL DEVELOPMENT KEY TO MINIMIZE TECH TALENT SCARCITY
The accelerated adoption of technology applications and solutions in the emerging digital-first economy has created a pronounced demand for cybersecurity talent in Mexico. The labor pool for this specialized talent is limited, however. Companies should consider the internal development of cybersecurity talent through career programs to proactively bridge urgent security needs in the increasingly hostile digital ecosystem, suggest industr y experts.
“By sourcing and training talent from within their own organizations, companies have the opportunity to generate cybersecurity talent that already understands organizational processes and objectives,” said Valther Galván, CISO, Prosa.

“By sourcing and training talent from within their own organizations, companies have the opportunity to generate cybersecurity talent that already understands organizational processes and objectives”
Valther Galván CISO | Prosa
The digital transformation inadvertently expanded the risk surface of companies, increasing the need for cybersecurity talent across all of Mexico’s industrial sectors. The observed and tangible implications of cybersecurity breaches over the past two years have clearly demonstrated that businesses’ budgets must now include cybersecurity investments. While Mexican companies have been proactive about their recruitment and retention efforts, companies are reporting that despite those efforts they are still having a difficult time sourcing talent. f urthermore, domestic companies are increasingly having to
compete with international corporations that are beginning to nearshore cybersecurity jobs, as they too have a limited talent pool. As such, to appease current cybersecurity needs, companies stand to benefit from upskilling their existing employees, who already understand their organization’s digital infrastructure, processes and objectives.
Preceding this initiative, companies need to first conduct an “internal audit of talent skills, measuring their abilities against cybersecurity needs so that they can easily identify individuals with highpotential,” said José Arraiga, CIO, Tokio Marine. Nevertheless, there should be genuine interest on behalf of candidates to continuously learn and build a career out of this investment opportunity, said Galván. In other words, technical and soft skills can be developed and nurtured over time, but personal attitude cannot. Thus, attitude should play a decisive role in the selection of candidates, who must also demonstrate the ability to communicate effectively with executives and contributors alike so, when necessary, they can provide insights regarding risks for strategic business decisions and create security controls. Moreover, candidates must also display a natural ability to lead considering that “cybersecurity is a strategy that needs to be implemented under well-defined controls and strategies,” said Jenny Mercado, CISO, Betterware Mexico.
This implementation initiative should also consider the “coordination between Human r esources departments and Information Technology departments, so they can create added-value career development programs,” said Arraiga. This is crucial for the development of naturally progressive career pathways in line with cybersecurity
needs and for the increase of talent retention rates, allowing the company to retain the employees it is investing so heavily to develop. The primary objective is to create incentives that will make contributors want to stay committed to the organization, something that cannot be overlooked considering that talent-poaching is at an all-time high. That said, companies should acknowledge that they are always at risk of losing their cybersecurity talent to competitors, lifestyle changes and sickness. As a result, companies should prepare
“contingency plans such as training multiple candidates and have succession plans in place,” said Arriaga.
Looking towards the future, companies should also consider partnerships with universities and technical schools to accelerate the generation of cybersecurity talent in line with immediate skills they will need. This would be replicating an initiative currently observed by Mexico’s aerospace industry, which has proved to be fruitful for this sector.
HUMAN BEHAVIOR: AN OVERLOOKED ASPECT OF CYB ERSECURITY
Businesses and cybersecurity experts have been incessantly challenged to continuously develop and implement preventive protocols in response to increasingly sophisticated, coordinated and longer lasting threats. To strengthen cybersecurity, industry leaders must secure the weakest link in the chain: users.
Human behavior is one of the largest risks to a secure network and vital to identify anomalies and prevent cyberattacks. While understanding the technical processes of network security is important for a successful performance, expertise in behavioral analysis is increasingly indemand and becoming an aspect of cybersecurity education programs.
“While the user may be the greatest vulnerability of companies, users can learn and be aware of threats they cannot
see, which cost them their jobs and cause unquantifiable losses for the company,” said Miguel Porfirio Camacho, Vice President IT, AMIS. To prepare the user for potential cyberattacks, AMIS provides education regarding antiviruses, malware, phishing and other examples to help users identify threats. “With the home office modality, it is as if companies had many branches, only without security or security that depends on the user. Thus, users need to independently know how to avoid an attack,” said Camacho.
Physiological processes can lead humans to have different responses to similar situations, said Bismarck Animas, Incident r esponse Manager, fe MSA. So, cybersecurity teams must familiarize themselves with various pain points. “It is important for cybersecurity professionals to study human behavior,

because cyberattackers do. They know exactly where to enter,” said Animas. Thus, companies need to educate and train their employees to avoid these mistakes, he added. This can be done by making training accessible and relevant and implementing security controls that are both effective and easy to use without disrupting workflows.

“While the user may be the greatest vulnerability of companies, users can learn and be aware of threats they cannot see, which cost them their jobs and cause unquantifiable losses for the company”
Miguel Porfirio Camacho Vice President IT | AMIS
“Behaviors can change, but responses must be standardized with processes and procedures for a conscious response on each occasion. for example, food chains have solid processes that allow them to have business continuity in branches in different countries. Cybersecurity processes can be equally successful,” said e rwin Campos, Cybersecurity Global Leader, Bimbo.
It is fundamental to differentiate valid human behavior from machine behavior, said Campos. Correctly identifying fraud is also key but companies also have a responsibility to provide tools to reduce human weaknesses and exposure to different attacks.
Humans are the easiest target because manipulating people is easier and faster than trying to violate a simple system, Campos said. This is why training and security awareness are the best tools to identify threats and allow users to easily report them.
Social engineering attacks, which are becoming more common, can also be highly personalized. A perpetrator first studies the intended victim to gather necessary background information, such as potential
points of entry and weak security protocols to proceed with the attack. Then, the attacker moves to gain the victim’s trust and provide stimuli for subsequent actions that break security practices, such as revealing sensitive information or granting access to critical resources. Attackers also take advantage of popular topics or current events. During the COVID-19 pandemic, Animas explained, attackers lured victims with the promise of news about the virus, vaccine and treatment. When users are home, these attacks can take the form of payroll emails.
“There is even a software that is dedicated to social engineering, which is why we are strict even with streaming services in work computers. Users might think we exaggerate but it is better to do so,” said Camacho.
The use of friendly language has greatly helped experts to raise awareness and train people more effectively, said Animas: “We had to lower our IT ego and begin to listen to collaborators and the business itself to learn how to communicate that the point is to defend the business so that it operates safely.” Being flexible with other collaborators helps them feel comfortable raising their voice in case of a suspected attack.
“Also sensitize bosses and go as far as to simulate a cyberattack to see how people react to know what needs to be improved,” said Camacho. Providers would also benefit from investing in machine learning and AI to facilitate processes for customers because “these tools learn for users’ behaviors. Investing in security will avoid losses in other areas,” said Camacho.
Through training and education users can “understand that they are also responsible for the company’s security, but also of their own private security. This way, they can avoid falling for personal or professional attacks,” said e lizabeth Peña Jauregui, Head of Government and Industry relations, ericsson LATAM North.
LEVERAGING AI, MACHINE LEARNING FOR CYBERSECURITY DEFENSE
New technologies like artificial intelligence (AI) and machine learning (ML) are transforming all industries, including technology and cybersecurity. While AI and ML have become important tools for companies to defend their systems, they are also used by cybercriminals, opening the door to an automated fight between machines. Under these circumstances, it is crucial to use the right tools and technologies to fight intelligence with intelligence, agreed industr y experts.
“AI and ML have revolutionized all industries. The possibility to predict events transforms a sector in every possible way. The cybersecurity and cybercrime industries are not the exception. On both sides, there are people who understand how AI and ML work and leverage them for their purposes. Companies must use these tools to build a cybersecurity culture,” said David Casillas, f ounder and C e O, Nyx Technology and Pixframe Studios.

“The cybersecurity environment within companies is complex. In some cases, they operate through silos, with a lack of knowhow. AI and ML tools help mitigate threats and even prevent them. Companies must become more proactive and analytic regarding their cybersecurity strategies”
Alfredo Sastre Barraza President | CSOFTMTY
The space for cyberattacks is vast and continues to grow and evolve rapidly. In response to this challenge, AI-based tools for cybersecurity help information security teams to reduce breach risk and improve their security. AI and ML have become critical technologies in information security, as they quickly analyze millions of events and identify several types of threats, from malware to risky behavior that may lead to a phishing attack. These technologies learn and improve over time, utilizing data from the past to identify new types of attacks now.
“There are many cybersecurity tools that leverage AI for more robust detection. The idea is precisely to detect anomalous behavior, compared with normal user behavior. We cross-check these behavioral metrics with hundreds of breach models to detect unusual activity,” said Pablo Carrillo, Account e xecutive, Darktrace. It is not efficient to bring a human into a battle between machines, since not even the greatest expert can always respond in time, he added.
Although AI and ML seem futuristic, they are already playing an important role across several industries, said Israel Gutiérrez, Chief Technology Officer, A3Sec. Attackers are increasingly becoming more professional, robust organizations, forcing companies to invest in cybersecurity, he added.
With the proliferation and evolution of cyberattacks, ML and AI enable companies to keep up with attackers, automating threat detection and responding more efficiently than traditional software-driven approaches, according to Balbix. These technologies help cybersecurity teams due to the unique challenges they face, such as hundreds of attack vectors and masses of data that have moved beyond a humanscale problem.
As AI’s popularity increases, there are several offerings that do not meet the AI test, as reported by forbes. Pure AI is not only a technology that analyzes data and lets results drive certain outcomes, it is about reproducing cognitive abilities to automate tasks. AI systems get smarter the more data they analyze; they learn from experience and become increasingly capable. “The foundation of AI is data. you have to collect the right data to generate effective algorithms. The more data these systems have, the smarter they become,” said Casillas.
The COVID-19 pandemic accelerated the digital transformation across the
world. In Mexico, several companies were forced to implement teleworking, adding new cybersecurity risks. Cyberattacks in Mexico increased by 600 percent during the pandemic, according to TotalPlay empresarial. While attacks become increasingly prevalent in the country, only four out of every 10 companies have a plan to strengthen their cybersecurity, reported e l e conomista. f ifty percent of companies that suffered a cyberattack were reportedly unable to identify its origin.
“The cybersecurity environment within companies is complex. In some cases, they operate through silos, with a lack of knowhow. AI and ML tools help mitigate threats and even prevent them. Companies must become more proactive and analytic regarding their cybersecurity strategies,” said Alfredo Sastre Barraza, President, CSOf TMT y
f ully avoiding cybercriminals is almost impossible so a company should not try to become impenetrable, which would be the ideal situation; its focus must be to become resilient, said Daniela Hernández, CISO, Grupo Converse de México, and Vice President of Cybersecurity, AM e XICOM: “Attackers can easily predict what we will do and for us it is not that simple. AI and ML can be our weapon to fight this cyber war.”
Beyond all the benefits that AI and ML bring to information security teams, these technologies also help to face the pronounced demand for cybersecurity talent in Mexico, which has considerable training gaps. “The automation of certain functions reduces human errors. Beyond the technical aspects, training is crucial. In addition, synergy between IT and cybersecurity teams is important. AI and ML are new IT assets that must be administered under a new focus, security,” said Hernández.

DISRUPTING REACTIVE CYBERSECURITY MODELS WITH CHAOS
The traditional, signature-based threat identification approach to cybersecurity leaves companies at a reactionary disadvantage. The Mathematical Chaos model breaks with the classical detection and response approach to cybersecurity, pushing forward a highly sensitive zerotrust model that is continuously reacting to anomalies in real-time, said Sneer r ozenfled, C eO, Cyber 2.0.
“The cybersecurity world is based on a vulnerable biological model that
intrinsically always places hackers one step ahead,” said r ozenfled.
e xisting cybersecurity solutions that concentrate singularly on detection and response will always fail eventually because 100 percent detection is not possible given the continuous innovation of malicious software. Although this field has made significant progress with anomaly detection through behavioral analysis and deep-packet inspection, these tools fundamentally rely on the identification of
malicious software before preventing its spread throughout an organization. In other words, the traditional reactionary approach is designed to fail in the face of an everevolving cybersecurity landscape, which is churning out increasingly sophisticated cybersecurity threats on a daily basis.
“The overarching objective of Cyber 2.0 is to shift the primary focus of cybersecurity from detection to containment, shutting down an invasion before it can spread an exact greater damage,” said rozenfled.
The Mathematical Chaos model is based on the Zero Trust security model, which operates under the assumption it does not know where the next cybersecurity threat will emerge from. This algorithm essentially verifies every software that requests to
interact with a system’s network, even when Cyber 2.0 is removed from the system. This model is more adept to protect computers, which function and communicate based on numbers “rather than the biological approach that attempts to protect them as a human body,” said r ozenfled. This approach is complemented with over capacities including network obscurement, security operation centers and forensic capabilities, but these are all secondary to the chaos algorithm that does most of the heav y lifting.
To prove the validity of its cybersecurity approach, Cyber 2.0 has invited over 5,500 white-hat hackers over four years from 30 countries to attack its system, giving them administrator passwords as a starting point. All of them have failed so far.

