




As organisations accelerate their digital transformation, one truth has become unavoidable. AI is not simply reshaping technology, but it is redefining the very nature of cybersecurity, governance, and operational resilience. From recent conversations with industry leaders across AI, Zero Trust, AIoT, sovereign intelligence, and exposure management, it is clear that enterprises are entering an era where the AI-driven intelligence of cybercriminals must be countered with defence that is just as intelligent and adaptive.
The cover story in this edition illustrates this shift. Security leaders emphasise that attackers no longer “break in” but they just log in, disguise themselves, and move laterally through hybrid networks that were never designed for such adversarial speed. This is why Zero Trust has evolved from a conceptual model to the operating system of modern security. Identity is the new perimeter, micro-segmentation is the new containment strategy, and continuous verification is the new normal.
Conversations with other industry experts reveal that AI is amplifying both sides of the equation. There are massive gains in real-time insights and workflows for Businesses with AI, and on the cybersecurity front with security automation. Platforms like Aleria’s sovereign AI stack show how enterprises can now unify data, build intelligent applications and derive real-time insights from video, IoT, and operational systems at unprecedented scale. Yet, this same automation and intelligence is also transforming cyber threats with AI-generated phishing, identity thefts, automated reconnaissance and more.
This battle between the intelligence we gain and the enhanced risk we are being exposed to defines the new landscape. Whether it is proactive exposure management, AIoT platforms converting physical spaces into sensing ecosystems, or cloud players enabling autonomous decisioning through GenAI agents, one message stands out that defence must evolve at the same speed as innovation.
For enterprises across the region, 2025 will be a year of convergence. Zero Trust will form the foundation, AI will become inseparable from both business and security, and sovereignty, of data, models, and infrastructure, will rise as a strategic priority.
R. Narayan Editor in Chief, CXO DX
RAMAN NARAYAN
Co-Founder & Editor in Chief narayan@leapmediallc.com Mob: +971-55-7802403
Ali Raza Designer
SAUMYADEEP HALDER
Co-Founder & MD
saumyadeep@leapmediallc.com Mob: +971-54-4458401
Nihal Shetty Webmaster
MALLIKA REGO
Co-Founder & Director Client Solutions mallika@leapmediallc.com Mob: +971-50-2489676
18 » ZERO TRUST AT THE FRONTLINE OF CYBERSECURITY
Identity, micro-segmentation, and AI-driven defence now define the future of cybersecurity
Neil Roseman, CEO of Invicti, explains how proof-based results, ASPM, and AI-enhanced DAST are helping organizations secure modern applications at scale, without slowing innovation.
Jérôme Freani, Chief Product Officer at Aleria, shares insights on the company’s sovereign intelligence vision and strategic partnerships with MBUZZ, NVIDIA, and DDN driving regional AI growth.
CRM today demands an AI-first approach that replaces traditional automation with intelligent, predictive, and proactive customer experiences writes William O’Neill, Area VP & General Manager – GCC at ServiceNow
Toshiba Storage Eyes the Future with Bigger Drives, Greener Tech, and a Strong Middle East Focus
Fady Richmany, Corporate VP & GM EMEA’ Emerging Markets -CEE, CIS, Middle East & META, Commvault discusses the company’s evolving approach to cyber resilience and the growing focus on securing AI workloads.
Tejas Lagad, Director – Asia, Middle-East, Africa for Digital Services at IN Groupe, shares strategic insights on how identity-first security, PKI modernization, and quantum readiness are shaping enterprise and government priorities in the region.
Michael Byrnes, Sr. Director of Solutions Engineering META at BeyondTrust outlines a series of essential security principles that every enterprise should adopt before integrating AI agents into production environments.
Nasri Nassereddine, Regional Vice President at Cumulocity, shares insights on AIoT adoption, challenges, and opportunities across the Middle East and Africa.
Power companies must adapt to thrive, says Gary Wong, Global Segment Leader of Power, Utilities, and Infrastructure at AVEVA

Partnership to accelerate the digitisation of Food Sector SMEsin UAE
Zoho and the UAE Food Cluster have announced a strategic partnership to support the digital transformation of small and medium-sized enterprises (SMEs) across the food manufacturing and trading ecosystem in the country.
The collaboration is a major step toward advancing the industry competitiveness through integration of digital tools for finance, operations, compliance, and performance management.
Leveraging Zoho’s enterprise-grade cloud technologies, the initiative brings scalable, secure, and AI-powered tools that were previously accessible mainly to large corporations within the reach of SMEs, helping them modernize their business functions with ease and affordability.
With the UAE’s growing emphasis on corporate tax compliance, operational efficiency, and data-driven competitiveness, the partnership between UAE Food Platform and Zoho aims to enable more than 300 eligible food SMEs to access digital solutions
that simplify business operations, improve process efficiency, and enhance traceability and compliance.
The program targets to digitisation over 300 companies in the next two years as part of a phased national rollout, with 100 companies to be onboarded in the first year. These SMEs will gain access to core digital modules designed to optimize operations in areas such as finance and accounting, inventory and supply chain, human resource management, and data analytics.
Each module is powered by Zoho’s enterprise technology stack, offering end-to-end integration, real-time insights, and AI-driven automation that enhance accuracy, reduce manual errors, and support smarter decision-making.
Participating SMEs will benefit from streamlined and compliant accounting and reporting systems, aligned with UAE corporate tax and VAT requirements. Improved operational efficiency through digital integration of production, inventory, and
10 Digital Workers ready equipped with 50 agentic skills now, 100+ skills available by December
IFS, the leading provider of Industrial AI software, announced the next evolution of its IFS Loops agent platform: 10 Digital Workers with 50 agentic skills, and a near-term roadmap for 100 skills designed for mission-critical workflows in manufacturing, energy, utilities, telecoms, construction, aerospace & defense, and service industries.
The IFS Loops agentic platform delivers templated Digital Workers that autonomously manage high-volume operational tasks, including field dispatch, supplier coordination, customer order manager and inventory replenishment, across enterprise systems with real-time intelligence, audit-ready compliance, and domain-specific understanding.
Unlike traditional automation, RPA, and Generative AI, IFS Loops Digital Workers manage complex workflows, make con-
text-driven decisions, and continuously improve operational performance while working right alongside employees to reduce manual tasks and amplify their impact. Whether embedded in IFS Cloud or running alongside legacy systems, these digital workers provide immediate ROI and operational impact.
Somya Kapoor, CEO of IFS Loops, commented, “The pace of operational change is faster than ever, with complexity growing faster than human teams or legacy systems can handle. Operations leaders and CIOs can’t wait for months of IT rollout to benefit from new capabilities. IFS Loops gives companies a digital workforce they can deploy today, orchestrating complex industrial workflows reliably, securely, and contextually, allowing skilled teams to focus on higher-value tasks. For many, this is their first step into agentic AI and a natural entry point into the broader IFS Cloud ecosystem.”

workforce management, with training and support from Zoho to ensure successful implementation and long-term adoption.
Signing an MoU at the Global Food Week (GFW), Saleh Lootah, Chairman of UAE Food Cluster, "SMEs are the backbone of the UAE's food ecosystem. This partnership with Zoho will help us create a unified, digitally empowered sector capable of competing on efficiency and compliance, both locally and globally.”

Somya Kapoor CEO, IFS Loops
IFS is scaling its agentic AI capabilities with a roadmap of 50 additional agentic skills available in December 2025, ensuring that Digital Workers continue to evolve alongside operational complexity and emerging industrial challenges. IFS Loops Studio, coming Q1 2026, will enable customers to create their own digital workers as needs arise, with rapid workflow customization.
Xponential to enable leaders deploy AI with speed, quality, and scale
DXC Technology has announced Xponential, a next-generation AI orchestration blueprint. Already a proven framework utilized by leading global enterprises, Xponential simplifies the complexity that often stalls large-scale AI adoption. The architecture seamlessly integrates people, processes, and technology to deliver measurable results, accelerate modernization, and helps enable businesses to operationalize AI securely and responsibly.
“Business leaders are eager to capture the promise of AI, but too often they get stuck in pilots or struggle to scale,” said Raul Fernandez, President and CEO of DXC. “DXC is uniquely positioned to help, with deep industry expertise, proven AI capabilities, and a track record of transforming complex operations. Xponential provides a blueprint that combines human expertise with AI, embeds governance and security from day one, and continuously evolves as AI matures -- helping enterprises move from vision to value with speed and confidence.”
As enterprises navigate a transitional AI era, many still lack a cohesive strategy connecting AI to their people and processes. Xponential provides a structured, repeatable blueprint for orchestrating AI across technology, embedding governance from day one, and delivering early wins that help organizations scale with speed and confidence.
At the heart of Xponential are five interdependent pillars. Insight embeds governance, compliance, and observability to ensure responsible AI. Accelerators include proprietary and partner-built tools that speed up deployment and increase efficiency. Automation brings agentic frameworks and protocols that optimize AI across processes. Approach focuses on Human+ collaboration, combining skilled professionals and AI to amplify outcomes. Finally, Process provides a delivery methodology with the flexibility to start small, achieve early wins, and scale rapidly across the enterprise.

President and CEO, DXC
DXC is helping global enterprises adopt AI through its Xponential framework, delivering measurable impact across industries. It reduced Textron’s service tickets by 20%, built ESA’s unified AI research platform, enabled Singapore General Hospital’s AI-driven infectious disease decision support with 90% accuracy, and developed Ferrovial’s AI Workbench with 30+ real-time AI agents supporting over 25,500 employees.
The implementation enables Select Group with enhanced global cash visibility and treasury control

Finesse, a leader in system integration and digital transformation, has successfully implemented Kyriba’s cloud-based Treasury, Risk Management, and Payments platform for Select Group, a renowned real estate developer and investor. This collaboration has empowered Select Group with enhanced global cash visibility and treasury control, enabling them to make predictive, strategic decisions backed by real-time data while reducing financial risk.
Select Group faced a common challenge among large, geographically diverse enterprises – obtaining consolidated, real-time visibility into their global bank balances
and cash positions. This fragmented view hindered optimal decision-making and created inefficiencies in treasury operations. Select Group sought a robust solution to centralize its treasury operations and gain real-time insights into its liquidity. Finesse was chosen as the implementation partner due to its deep expertise in financial technology and proven track record in delivering complex digital transformation projects across the region.
To address these issues, Finesse implemented Kyriba’s state-of-the-art treasury modules, integrating seamlessly with Select Group’s global banking network while
ensuring smooth extraction of critical financial data from the company’s existing business intelligence (BI) tools. This transformation has provided Select Group with unparalleled oversight of their liquidity and cash flow operations.
The implementation included a comprehensive suite of modules tailored to Select Group's specific requirements, such as Core Bank & Cash Management, Bank Account Management, In-House Banking, Payments, Debt & Investment Position Keeping & Financial Accounting, and Fraud Detection. These modules have streamlined cash management and forecasting processes, centralized treasury operations, and enhanced security with robust fraud prevention capabilities
Megha Shastri, Vice President – Enterprise Accounts Finesse, said, “When we first connected with Select Group, it was clear they needed a robust Treasury Management Solution. With the successful implementation of Kyriba — the world’s leading TMS — Select Group is empowered to manage their treasury operations like true champions.”
Latest innovations to Intelligent Data Management Cloud will power the era of Agentic AI with trusted, AI-ready data
Informatica, a leader in enterprise AIpowered cloud data management, announced the latest innovations to its Intelligent Data Management Cloud (IDMC), introducing new capabilities designed to power the next generation of AI-driven enterprises. The new capabilities are designed to help customers unlock productivity, strengthen data security and build trust in AI-powered decision-making.
“The world is entering the era of agentic AI where autonomous agents collaborate with humans to solve complex business challenges,” said Krish Vitaldevara, CPO, Informatica. “With this launch, Informatica empowers every organization to connect trusted, AI-ready data to these intelligent agents helping them innovate faster, operate smarter and build AI systems their businesses can trust.”
The latest release introduces CLAIRE Agents, a major step forward in autonomous data management. These AI-pow-
ered assistants, ranging from Data Exploration Agents to Product Experience Agents, can now handle complex data management tasks such as data discovery, quality assurance, and pipeline creation through natural language commands.
The enhanced CLAIRE GPT further improves planning, automation and natural language understanding, allowing users to design and optimize data workflows conversationally. This is complimented by CLAIRE Copilot for Master Data Management (MDM) which simplifies access to trusted master data, providing context-aware insights directly within business applications.
To support enterprises building their own intelligent systems, Informatica has introduced a new framework that allows organizations to build, connect and orchestrate customizable Informatica AI agents without code. With built-in validation, observability and governance, teams can scale

Krish Vitaldevara CPO, Informatica
AI initiatives faster while maintaining compliance and security. Complementing this, the AI Agent Hub (Private Preview) provides pre-built, domain-specific agents and automation recipes that integrate seamlessly with tools such as Salesforce, Jira, Microsoft Teams and Snowflake.
Recognizing the growing focus on responsible AI, the release also expands AI governance and privacy capabilities.
Newest WSO2 Identity Server and Asgardeo IDaaS versions speed the deployment of secure AI Agents via new agentic IAM features
Enterprise software developers need to ensure that today’s digital experiences are secure—whether delivered via applications or artificial intelligence (AI) agents. WSO2 empowers developers to deliver this demand with the latest releases of its identity and access management (IAM) products: WSO2 Identity Server opensource software (OSS) and Asgardeo identity as a service (IDaaS). The products offer new agentic IAM capabilities that accelerate the deployment of secure AI agents by treating these agents as firstclass entities and supporting authorization of the model context protocol (MCP). Additionally, they extend AI functionality designed to maximize developers’ productivity.
The latest WSO2 Identity Server and Asgardeo releases also extend WSO2’s leadership delivering comprehensive functionality for complex business-to-business (B2B) customer IAM (CIAM) scenarios, including more fine-grained access con-
trol to applications and support for additional organizational structures. Other new and enhanced capabilities include real-time event publishing, advanced account linking, and post-quantum security, among others.
“Developers are being tasked to deliver an expanding range of secure, intelligent digital experiences across multiple consumer and business scenarios,” said Geethika Cooray, vice president and general manager of identity and access management at WSO2. “With our latest WSO2 Identity Server and Asgardeo releases, we’re simplifying developers’ experience while empowering them to deliver secure AI-driven applications and agents that serve today’s advanced B2B and consumer demands.”
The new product versions build on the proven IAM capabilities of WSO2 Identity Server open-source software and Asgardeo, which is available in both multitenant and private SaaS versions.

Geethika Cooray
VP & GM identity and access management at WSO2
Together, they manage more than 1 billion identities worldwide and support a range of scenarios, CIAM, B2B CIAM, and government-to-citizen (G2C) IAM, among others. Because the products share the same code base and user interface (UI), WSO2 customers have unprecedented flexibility to migrate between cloud, on-premises and hybrid deployments while delivering a consistent, best-in-class user experience for developers, consumers, and other users.
The agreement builds on prior global collaborations
Dell Technologies and Perpetuuiti Technosoft DMCC, a leading provider of AI and automation-driven resilience solutions, announced the signing of a Memorandum of Understanding (MoU) to enhance Cyber Resilience and IT Continuity for organizations across the Middle East and beyond.
The MoU signed during GITEX Global 2025 by Walid Yehia, Managing Director – South Gulf, Dell Technologies and Rohil Sharma, Co-Founder and CEO, Perpetuuiti, aims to address critical resilience and security challenges faced by businesses, focusing on compliance, continuity, and recovery, while elevating the overall efficiency of digital operations.
The agreement builds on prior global collaborations where both organizations have successfully delivered impactful solutions that enhance operational resilience and create substantial value for customers. Together, Dell and Perpetuuiti will further strengthen their collaboration to expand
the adoption of innovative resilience and security solutions that align with global best practices and meet evolving regulatory requirements. By integrating Perpetuuiti’s AI-enabled Operational Resiliency Automation Platform with Dell’s consulting expertise, the partnership aims to deliver a comprehensive portfolio of resilience and security solutions designed to reduce operational risk and accelerate enterprise recovery.
As part of this collaboration, Perpetuuiti brings its AI-first innovation powered by Susan, the world’s first BCM-certified AI Business Continuity Consultant, and Lisa and Dave, the Generative AI Duo Agents within its Operational Resilience Automation Platform. Together, these agents enable autonomous continuity planning, resilience orchestration, and recovery automation— driving assured, adaptive, and intelligent resilience outcomes. Their integration with Dell’s infrastructure and consulting expertise will help enterprises achieve faster

recovery, stronger compliance alignment, and greater operational efficiency across hybrid environments.
Walid Yehia, Managing Director - South Gulf, Dell Technologies, said, “The MoU with Perpetuuiti represents a step forward in Dell’s mission to deliver integrated and scalable solutions that address the evolving needs of modern enterprises. The collaboration not only strengthens our commitment to advancing resilience in enterprise recovery automation but also reinforces our ability to empower organizations to address complex security and regulatory challenges.”
Expands Sophos SecOps Portfolio, Delivering Faster Detection of Identity Risks and Exposure of Compromised Credentials
Sophos, a global leader of innovative security solutions for defeating cyberattacks, today announced the launch of Sophos Identity Threat Detection and Response (ITDR). This new solution for Sophos XDR and Sophos MDR continuously monitors customer environments for identity risks and misconfigurations and scans the dark web for compromised credentials. It enables organizations to detect and respond to identity-based attacks rapidly and identify risky user behavior that could pose a threat to their business.
This launch is a significant milestone building on the Secureworks acquisition, broadening Sophos’ portfolio and is the first Secureworks solution that has been fully integrated into the Sophos Central platform, further enabling comprehensive security operations outcomes for its 600,000 customers.
Sophos ITDR addresses identity-based attacks, one of the fastest-growing threat
vectors globallySophos X-Ops observed a 106 percent increase in stolen credentials for sale on the dark web between June 2024 and June 2025, underscoring the growing risk.The Sophos Active Adversary Report further found that compromised credentials were the number-one root cause of attacks across MDR and incident response cases for the second year in a row, with 56 percent of incidents involving attackers logging into external remote services with valid accounts.
“Cloud and remote work have expanded the identity attack surface and created new opportunities for attackers,” said Rob Harrison, SVP, Product Management, Sophos. “Complex identity and access management systems with constantly changing settings and policies create gaps that attackers target. Sophos ITDR helps close those gaps by giving customers faster visibility into identity risks, monitoring for compromised credentials, and integrating with Sophos XDR and Sophos MDR for

Rob Harrison SVP, Product Management, Sophos
rapid, analyst-led response.”
Sophos ITDR uncovers identity risks and is designed to protect and detect against all known MITRE ATT&CK Credential Access techniques with detection rules for all of the techniques.
Veeam Software has signed a definitive agreement to acquire Securiti AI, a recognized leader in Data Security Posture Management (DSPM) that also spans privacy, governance, access, and AI trust across hybrid, multi-cloud, and SaaS platforms, for $1.725 billion. Veeam and Securiti AI unify data resilience with DSPM, privacy, governance, and AI trust spanning production and secondary data. Together, they will help customers understand their full data estate, while providing security, along with recovery and rollback, to unleash the value of their data for AI.
With the acquisition of Securiti AI, Veeam eliminates the challenge of managing fragmented data across apps, clouds, SaaS, endpoints, and backups. CIOs, CISOs, and CDOs will have a unified command center to fully control and understand all their data, as well as secure it with near-zero data loss or business downtime, recover and roll-
back data and AI with precision, and safely unleash AI innovation. This single control plane across production and secondary data enables enterprises to uniformly command their entire data estate – combining Veeam’s trusted data resilience capabilities with Securiti AI’s leading DSPM, data privacy, and AI trust capabilities.
Traditional approaches, which involve siloed tools for data security and management, don’t reflect new AI threats and force teams into constant trade-offs between security, risk management, and business agility. The combination of Veeam and Securiti AI dramatically mitigates these trade-offs with a single command center for all data.
“We’ve entered a new era for data. It’s no longer about just protecting data from cyber threats and unforeseen disasters; it’s also about identifying all your data, ensuring it’s governed and trusted to power AI
Partners with SAS and DataScience ME to boost enterprise-wide fraud detection and prevention

SAS, a market leader in data and AI; DataScience Middle East, an official SAS partner in the UAE, Middle East, Turkey and Africa and Ajman Bank PJSC, a leading financial institution in the UAE, have joined forces, leveraging SAS’s expertise to enhance the Ajman Bank’s enterprise-wide fraud detection and prevention capabilities. This milestone symbolizes Ajman Bank’s strong roadmap into a digital transformation journey, reinforcing its commitment to safeguarding customer assets and main-
taining the highest standards of financial integrity.
By leveraging SAS’s cutting-edge Fraud Management and decisioning platform, Ajman Bank will be able to monitor transactions in real time, detect anomalies, and respond swiftly to emerging threats across multiple channels.
“Our partnership with SAS and DataScience ME reflects our commitment to

transparently,” said Anand Eswaran, CEO at Veeam. “This is the single most critical factor in failed AI initiatives. By combining the market-leading strengths of Veeam and Securiti AI, we bring those capabilities together in a single solution to help customers understand, secure, recover, and rollback, and unleash their data to drive new business value.”
adopting world-class technologies that protect our customers and ensure the integrity of our banking operations. This is a major step forward in our journey toward smarter, safer banking,” said Abhishek Sharma, Chief Risk Officer at Ajman Bank.
The SAS Fraud Management solution utilizes advanced machine learning and decisioning capabilities to score transactions in real time, significantly reducing false positives and improving operational efficiency.
“We’ve been heavily investing on securing a strong partner ecosystem that will be able serve our clients locally and regionally. SAS, in partnership with DataScience ME, have been diligently collaborating to better understand the Ajman Bank’s challenges and vision, accordingly we’ve built a customer centric model that’s tailored to Ajman Bank’s needs, said “Samer Naguib, META Channel & Alliances Director, at SAS.
For Ajman bank, the AI-powered solution strengthens its compliance framework by minimizing false alerts and ensuring that genuine threats are prioritized. This reduces operational inefficiencies and helps risk teams focus on high-risk cases. With built-in case management and automated reporting, Ajman bank can more efficiently investigate financial crimes, ensuring adherence to both local and global regulations while mitigating legal and financial risks.
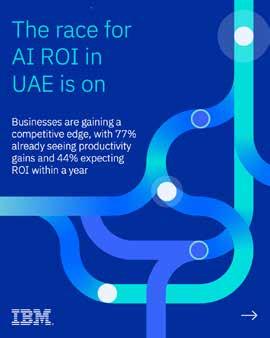
77% of UAE senior leaders report significant productivity improvements from AI, well above the EMEA average of 66%
A new study from IBM reveals enterprises across the United Arab Emirates (UAE) are reporting some of the strongest productivity gains from AI in the Europe Middle East and Africa (EMEA) region, with many expecting returns on their investments (ROI) within the next year.
“The Race for ROI,” a new IBM report produced in partnership with Censuswide, surveyed 3,500 senior executives across ten countries, including 500 in the UAE. The findings show that 77% of UAE respondents said their organizations have achieved significant operational productivity improvements using AI, well above the regional average of 66%.
In addition, approximately one in five respondents said their organization has already realized ROI goals from AI-driven productivity initiatives, with a over 44% on average expecting to achieve ROI within 12 months across cost reduction (40%); time savings (49%); increased revenue (41%); employee satisfaction (47%) and increased Net Promoter Score (43%).
Further productivity benefits are expected from the introduction of AI Agents, with 93% of UAE leaders expecting that agentic AI will deliver measurable ROI within two years.
According to the study, business areas achieving the biggest AI-driven productivity gains in the UAE are software development and IT (34%), advertising and marketing (33%), account management (30%), customer service (28%) and procurement (29%). At the same time, executives reported the top three benefits of enhanced productivity as greater operational efficiency (55%), enhanced decision-making (56%), and augmented workforce capabilities such as automating repetitive tasks (55%).
Across the UAE, the data shows that leaders are increasingly using AI to en-
able strategic business transformation. Of those who reported significant productivity gains, nearly a quarter (26%) credit AI with fundamentally changing their business models. Around a third of respondents are already using AI to change their operations in ways such as accelerating innovation timelines (36%); shifting to continuous AI-driven decision-making instead of periodic planning cycles (29%); and redesigning value streams around AI rather than automating existing steps (33%), while a further 2 in 5 intend to do so across all these areas.
More than half of all senior leaders surveyed (55%) said that AI is augmenting workforce capabilities. For example, with the time saved from greater productivity, executives said employees are spending more time on developing new ideas (44%), upskilling and professional development (44%), improving sustainability and advancing ESG initiatives (43%), strategic decision-making and planning (41%), and engaging in creative work (37%).
A greater proportion of senior leaders in UAE (47%) said they are prioritising inclusive AI workforce transformation: e.g. ensuring upskilling programs are accessible to all employees regardless of role, age, or technical proficiency to build an AI-enabled workforce, compared to EMEA average (36.5%).
The study found that openness, interoperability, and choice are critical priorities for organizations adopting AI. In the UAE, 77% emphasized the importance of transparency in AI systems and models ensuring that the technology operates ethically and responsibly. Similarly, 78% stressed the need for interoperability, enabling seamless integration of AI tools into IT systems to maximize efficiency and adaptability.
A further 80% said they valued flexibil-
ity to choose and adapt AI solutions or providers as needs evolve, underscoring strong demand for technological autonomy.
tation
While the findings suggest companies are progressing towards greater ROI from AI, UAE respondents also identified the following as top barriers to scaling successful AI pilots: inadequate data infrastructure or data fragmentation (67%), security, privacy, and ethical concerns (65%), IT complexity challenges (64%), high upfront costs and reluctance to invest in AI and automation initiatives (63%).
To accelerate ROI from AI, the report outlines five priorities for enterprise leaders: establishing an effective AI operating model; cultivating AI literacy and a culture of innovation; embracing rapid change; understanding risk through strong governance; and creating a cross-company “AI Board” to oversee ethical use.
Toshiba Storage Eyes the Future with Bigger Drives, Greener Tech, and a Strong Middle East Focus
Toshiba’s storage division is preparing for the next wave of exponential data growth with a roadmap of higher-capacity hard drives, greener designs, and a sharpened focus on Middle East markets. Company executives outlined the legacy that shapes their strategy, the technology innovations driving their portfolio, and the go-to-market approach for the region.
Peter Lieberwirth, President and CEO of Toshiba Electronics Europe GmbH, elaborates on Toshiba’s long history to the present day.
“We are very proud of our 150-year legacy. When we think back to 1875, that was before the electric light bulb was invented. Toshiba didn’t invent the light bulb, but was the first to bring it to Japan. One of our founders said, We bring the light into people’s homes. That thought of contributing to society through innovation is still in our DNA.”
That ethos extends to storage.
“Our hard disk drives are used to preserve people’s memories, the
photos and music they love. Today, the market is shifting toward industrial and enterprise environments. Toshiba has expanded its portfolio for 24/7 operation and high reliability in data centers, surveillance, and mass-storage systems. With AI generating unprecedented amounts of data, the requirement for storage is strongly increasing.”
On the company’s organizational changes,Peter says, “Toshiba was privatized two and a half years ago. In that context, the corporation restructured its footprint. Toshiba Gulf was closed, and activities were reorganized. Toshiba Electronics Europe now manages shipments and orders, while a new entity, Tosh Next Technologies, provides local customer contact. The brand remains Toshiba, but Tosh Next ensures continuity with the same team and familiar faces.”
Toshiba is investing heavily in next-generation HDD technology to keep pace with hyperscale data center demands.
“We are working on two parallel paths to increase capacity,” says Daisuke Hara, GM, EMEA Storage Products Business Market-
ing at Toshiba Electronics Europe GmbH. “One is improving the number of platters in a drive. The other is advancing HAMR (heat-assisted magnetic recording). By 2027, HAMR will enable drives larger than 40 terabytes. Before that, we plan an 11-platter product and expect to launch 28 terabyte drives in 2026.”
For now, hyperscalers are buying 24 TB drives, but Middle East demand remains centered on 16 TB to 18 TB models because of unit cost considerations.
Energy efficiency is a major design goal.
“Current drives consume around nine to ten watts,” Daisuke notes. “Our latest 24 TB product reduces this to 0.4 watts per terabyte, down from one watt per terabyte on earlier 10 TB models. Future products will continue to lower watt-per-terabyte ratios.” He added that Toshiba uses helium-filled enterprise drives to cut friction and power draw.
“Helium is only one-seventh the density of oxygen, allowing the platters to spin with less resistance and generate less heat.”
While AI workloads require fast compute, Toshiba executives emphasized that HDDs remain indispensable for cost-efficient storage.
“In the datacenter space, HDDs and SSDs are not competing technologies,” says Larry Martinez-Palamo, VP and Head of EMEA Storage Products Division at Toshiba Electronics Europe GmbH. “SSDs are faster and suited for operations requiring very fast random reads and writes. HDDs deliver a much lower cost per terabyte and are ideal for sequential storage. For pure data storage it would be a waste of resources to buy SSDs. AI generates huge volumes of data that ultimately must be stored, so SSDs handle the processing while HDDs handle the archiving.”
According to Larry, the HDD market continues to expand despite consumer slowdown.
“IDC ( International Data Corporation) estimates that about 10 zettabytes of data will be stored globally in 2025, and that figure will nearly double over the next five years. Roughly 60% of that data will remain on HDD technology well past 2030. Enterprise storage is growing at around 15% per year, while surveillance markets show about 10% growth. Consumer sales are declining in units but trending toward higher capacities.”
On Toshiba’s strategic priorities within its storage portfolio, Larry highlights the company’s focus on addressing diverse market segments while strengthening its enterprise footprint.
“At Toshiba’s Storage Products Division, we operate across four
main business areas — surveillance, NAS, consumer, and enterprise. Among these, enterprise and data center storage stand out as the most strategic and fastest-growing segments. As data centers continue to expand globally, their appetite for storage capacity remains insatiable.”
For the region, Santosh Varghese, MD at Tosh Nxt Tech Ventures highlights a channel-driven growth model.
He says, “The Middle East and Africa are critical markets in our EMEA footprint. Despite the restructuring, it’s business as usual with the same team managing the market. We operate an in-country distribution model with most distributors based in Dubai but covering the Gulf and Africa."
“Our strategy is to go wide and go deep—expanding retail, system integrators, and dealer networks. For Africa, our Go Africa initiative focuses on building and training local channels rather than running operations from Dubai. Programs like Build Your Own Data Center (BYODC) teach enterprises to take their data seriously and create on-premises or hybrid solutions at roughly 30% of the cost of ready-made storage boxes,” adds Santosh.
While enterprise is the growth engine, Toshiba continues to serve the consumer segment.
Jeff Briggs, GM, Distribution Sales Dept – EMEA Storage Products Division at Toshiba Electronics Europe GmbH says, “Our lineup of external hard drives is primarily designed for consumers, catering to their need to store personal data — whether photos, games, movies, or other content. We offer a broad range of products, from basic models to high-end, high-capacity drives of up to 4 TB in a compact 2.5-inch format. One product we always like to highlight is our Canvio Flex, a truly unique offering in the market. It’s the only drive compatible across all major platforms — PC, Mac, and smartphones, both Android and iPhone — allowing users to store and access their data seamlessly without the need for formatting. That’s why we call it the Canvio Flex — it’s the most flexible hard drive on the market.”
Despite the rise of cloud services and SSDs, Toshiba sees a long runway for HDD growth.
Jeff says, “Data is being generated exponentially and must be stored somewhere. HDD technology will continue to handle the majority of the world’s exabytes for years to come.”
With its heritage of innovation, expanding capacity roadmap, and regional strategies to deepen channel engagement, Toshiba aims to stay at the center of the world’s insatiable demand for data storage.
Mohannad Abuissa, Managing Director of Solutions Engineering and CTO for Cisco Middle East, Africa, Türkiye, Romania, and CIS, spoke to CXO DX at GITEX about how Cisco is evolving its portfolio to power the new wave of AI, from secure infrastructure to next-generation observability and quantum networking.
How is Cisco evolving its portfolio to be AI-driven?
We are witnessing a new wave of AI today. Two or three years ago, we saw the advent of generative models like ChatGPT. Cisco has been providing secure networking for enabling that phase, and now, with the whole world moving toward agentic AI, Cisco has been pioneering in providing the critical infrastructure that empowers this new phase as well.
We always say there is no AI without secure networking and that’s where Cisco excels. Beyond infrastructure, we are also making AI foundational in the way we design our products. It’s not something we bolt on later; we build new solutions with AI embedded from the start.
Today’s data centers can no longer cater to AI workloads without being redesigned. Cisco is rethinking how data centers are built optimizing for low latency, high throughput, and power efficiency to handle AI’s demanding compute needs while maintaining sustainability and reducing carbon emissions.
But AI is only as good as it is trustworthy. That’s why Cisco focuses heavily on AI safety and security, offering innovations like AI Defense to ensure that models don’t suffer from toxicity, hallucinations, or prompt injections. Our solution provides model validation and guardrails before deployment and continuous protection once in production.
We also integrate security directly into the fabric of the data center through our Smart Switch solutions, embedding data processing units (DPUs) for inline security at the rack level. This eliminates bottlenecks and makes security intrinsic to every AI workload. In addition, Cisco’s Universal Zero Trust Network Access (ZTNA) architecture ensures least-privilege access to AI models, extending zero-trust principles across all environments.
Elaborate on how you refreshed your product line with AI? We have done that particularly in the data center, where AI workloads demand ultra-low latency and high throughput. Over the past 18–24 months, we’ve been systematically refreshing our portfolio to support the new generation of AI infrastructure. Every month, there’s a wave of innovation being announced, especially around networking, compute, and security.
At the same time, we’re preparing for the integration of humans and AI agents across work environments, from the data center to the campus and the branch. We’re redesigning campus infrastruc-

Mohannad Abuissa MD of Solutions Engineering and CTO for Cisco Middle East, Africa, Türkiye, Romania, and CIS
ture to handle new types of traffic like agent-to-agent communications, which traditional systems weren’t built for.
We’ve even extended the Smart Switch concept from the data center to the campus, embedding dedicated logical areas for security. Because AI-driven connectivity won’t be limited to the office, it’s everywhere: in factories, hotels, coffee shops, or branches. So, we must ensure secure and consistent networking experiences across all locations. As I often say, you cannot deliver AI without security.
How are regional customers approaching AI adoption and investment?
In a global study covering over 8,000 customers, we found that a
majority of IT leaders plan to increase their investment in AI over the next 12–18 months. Many believe that not adopting AI soon could mean losing their competitive advantage.
Interestingly, while globally only about 13% of organizations said they were ready for AI, in the Middle East, that figure rises to around 16% of enterprises. This shows that our region is ahead of the global curve. Many flagship projects in Saudi Arabia, the UAE, and Qatar are leading in AI adoption, and Cisco is proud to provide the critical infrastructure enabling these national and enterprise-scale transformations.
What is Cisco’s approach to end-to-end visibility and resilience across hybrid environments?
Cisco has long been focused on hybrid and multicloud environments, but our acquisition of Splunk has taken our observability capabilities to an entirely new level. Splunk is a powerful data platform, and when combined with Cisco’s infrastructure, it enables full-stack visibility, from silicon up to the AI model.
Our integrated Cisco Data Platform powered by Splunk allows customers to track performance metrics across every layer. For example, it can quantify how much each token generated by an AI model costs, enabling a new level of cost and operational transparency. This combination not only enhances observability but also introduces predictive intelligence, detecting issues before they occur and giving enterprises complete visibility into their AI workloads.
What role do you see AI playing in cybersecurity?
AI is indeed a double-edged sword; it can protect, but it can also attack. That’s why Cisco’s AI Defense solutions focus on defending against AI-driven threats and ensuring that AI models themselves remain secure.
We’ve applied AI-driven red teaming, where AI systems continuously test and probe other models to identify weaknesses at scale, something humans alone cannot do efficiently. Through this approach, we ensure protection against issues like model hallucination, toxicity, and malicious prompt injections. AI Defense builds resilience and integrity directly into the AI lifecycle.
How is Cisco progressing in the area of quantum networking?
Cisco is investing heavily in quantum technologies through our internal incubation arm, Outshift. We recently announced our first network prototype chips capable of generating entangled photons, enabling instantaneous quantum connectivity. This milestone was achieved by our Cisco Quantum Lab in California.
We’ve also introduced a quantum software stack, including a quantum compiler, quantum alert (for preventing eavesdropping), and other tools to connect quantum computers securely and efficiently. These developments will help bridge the gap between classical and quantum computing over the next decade.
We don’t see quantum replacing classical networks entirely; rather, both will coexist. Quantum systems are extremely sensitive to temperature and noise, so they’ll be used for high-precision and cybersecurity-intensive use cases, while classical systems will continue to handle cost-efficient workloads.
Cisco is ensuring that our next-generation routers and switches are quantum-ready, especially in encryption because once quantum computing matures, it will challenge today’s encryption standards. Our goal is to stay ahead by developing quantum-resilient infrastructure.
What are your key priorities in the region following GITEX? GITEX has always been a major platform for Cisco, but this year’s edition is particularly special. We’re working closely with public and private sector partners to prepare them for the AI wave. Every digital transformation starts with the network, and we see Cisco as the critical infrastructure provider enabling this transition.
We’re also continuing our commitment to education and skilling through initiatives like the Cisco Networking Academy, raising AI awareness and readiness across the region. Our goal is clear, and that is to ensure enterprises, governments, and partners are fully equipped to harness AI securely and sustainably, driving innovation and societal progress.
"But AI is only as good as it is trustworthy. That’s why Cisco focuses heavily on AI safety and security, offering innovations like AI
Defense to ensure that models don’t suffer from toxicity, hallucinations, or prompt injections."
Jaafar AlHashmi, Acting VP – Government Sector at Core42, discusses how the company’s breakthroughs in sovereign cloud, AI infrastructure, and strategic partnerships are enabling a secure, scalable, and future-ready digital ecosystem for the nation and beyond.
Core42 has been at the forefront of enabling AI-powered transformation across the UAE. What are some of the key innovations solutions Core42 showcased at GITEX this year?
At GITEX Global 2025, Core42 demonstrated the progress we’re making in advancing sovereign cloud and AI infrastructure across the UAE and beyond. This year, we took centre stage within the G42 District in AI Hall 6, highlighting our role as the digital infrastructure arm of the G42 ecosystem. G42’s Intelligence Grid vision is redefining how nations can build AI-native societies by connecting infrastructure, intelligence, and innovation within one cohesive framework. Together with our sister companies, we showcased how our technologies translate into tangible outcomes that strengthen the UAE’s AI leadership and set new benchmarks for secure, globally competitive digital infrastructure.
A major highlight of our showcase was our AI Cloud, a high-performance, scalable, and sovereign platform that brings every leading accelerator together under one roof and provides a unified solution for all training, fine-tuning, and inference needs. We have already announced the introduction of self-service capabilities within our AI Cloud that allow users to access NVIDIA accelerated compute resources within minutes, bringing unprecedented speed, flexibility and accessibility to large-scale AI development. We will continue to announce new partnerships designed to extend the UAE’s technological leadership globally, as we simultaneously demonstrate key offerings such as our Sovereign Public Cloud, our Signature Private Cloud - which is currently in Customer Preview, and our Compass generative AI platform.
Could you elaborate on how your partnerships drive secure, scalable, and sovereign digital transformation?
Partnerships are at the heart of Core42’s strategy to scale digital transformation and strengthen the UAE’s position as a global hub for AI innovation. We believe progress happens through collaboration, and our work with government entities and leading technology partners is creating the infrastructure, ecosystems, and capabilities that make AI accessible, secure, and impactful across the region.
As part of the G42 ecosystem, we play a central role in advancing the Intelligence Grid vision, which connects infrastructure, intelligence, and innovation into a unified national framework. Our collaboration with the Abu Dhabi Department of Government Enablement is a strong example, where we are helping to process more than 11 million daily digital interactions through a sovereign cloud system that supports the UAE’s goal of becoming the world’s first fully AI-native government by 2027.

Jaafar AlHashmi Acting VP – Government Sector, Core42
On the global stage, our partnership with Microsoft reflects how we are bringing world-class innovation to the UAE while ensuring it aligns with local data and compliance priorities. As part of G42’s broader landmark collaboration with Microsoft, we have built the Sovereign Public Cloud on Microsoft Azure, and integrated Core42’s Insight controls platform to combine hyperscale capabilities with national data assurance. This has given UAE organizations access to the scalability and features of a global hyperscaler, while still maintaining full sovereignty over their data, workloads, and AI models.
We are also expanding our international footprint through strategic collaborations across Europe. Together with our partners, we are creating the foundations of a trusted, AI-enabled future that positions the UAE and the wider Middle East at the centre of global AI progress.
How does Core42 ensure its sovereign cloud infrastructure meets the highest standards of security and trust required by regulated industries?
Security, compliance, and trust are central to Core42’s value proposition. Our entire cloud and AI infrastructure is sovereign by design, meaning that data protection, governance, and regulatory alignment are built into every layer of our technology. This approach ensures that organizations operating in regulated industries such as government, healthcare, finance, and energy can innovate confidently while maintaining full control over their data. Our Sovereign Public Cloud meets the highest standards of assurance, with all workloads, models, and data processed within the UAE under national jurisdiction. It is governed by Insight, Core42’s compliance and controls platform, which provides complete visibility and policy enforcement across every environment. For industries that require the highest levels of protection such as defense and national security, we are introducing the Signature Private Cloud, which offers an isolated and secure environment for classified or top-secret workloads.
We work closely with regulators and policymakers to ensure our platforms meet and often exceed national and international standards for data security and privacy. By embedding compliance into the foundation of our infrastructure rather than treating it as an add-on, Core42 enables regulated industries to modernize securely, accelerate innovation, and uphold the highest levels of public trust.
How would you describe the growth journey so far, and what have been some defining milestones for the government sector?
The past year has indeed been transformative for Core42. We have strengthened our position as the region’s leading provider of sovereign cloud and AI infrastructure, and deepened our partnerships with both government entities and global technology leaders. Our growth has been driven by a clear mission to deliver the infrastructure, intelligence, and innovation that enable nations to build AI-ready economies.
In the government sector, one of our most significant milestones has been our collaboration with the Abu Dhabi Department of Government Enablement to establish a sovereign cloud system capable of processing more than 11 million digital interactions every day. This initiative supports Abu Dhabi’s ambition to become the world’s first AI-native government by 2027 and stands as a model for how AI can improve the speed, quality, and transparency of public services. We also signed a landmark agreement with the UAE Accountability Authority to advance governance and transparency in AI adoption. This partnership reflects a shared commitment to embedding trust and accountability at the core of digital transformation. Beyond the UAE, we have continued to expand our collaborations internationally, including partnerships in Europe that are extending the reach of sovereign AI infrastructure to new markets.
These milestones reflect how Core42’s growth journey is closely aligned with the UAE’s national vision. As we look ahead, our goal is to continue supporting governments in building secure, data-driven, and AI-enabled public services that set new global standards for innovation and trust.
Looking ahead, what are Core42’s strategic priorities for the next five years, particularly in advancing the UAE’s ambition to become a global leader in sovereign AI and digital innovation?
Over the next five years, our strategic focus is on playing our part to accelerate the UAE’s vision to become a global leader in sovereign AI and digital innovation. We see this as both a national responsibility and a regional opportunity. Core42 will continue to build the infrastructure, partnerships, and AI capabilities that enable governments and enterprises to innovate securely, sustainably, and at scale.
Our top priority is to expand the reach of our sovereign cloud and AI platforms. The Sovereign Public Cloud will continue to evolve to meet the needs of regulated industries, while the Signature Private Cloud will provide secure environments for the most sensitive and classified workloads. The AI Cloud will remain a cornerstone of our innovation strategy, offering high-performance compute and AI development tools that make advanced AI more accessible to public and private sectors alike.
We are also committed to advancing responsible AI adoption by working with regulators and policymakers to shape governance models that ensure transparency, accountability, and ethical use. At the same time, we are exploring opportunities to export the UAE’s sovereign AI blueprint to other regions, sharing the success of a model that balances global innovation with national sovereignty.
Ultimately, our goal is to help position the UAE and the wider Middle East as a trusted hub for AI-driven progress, where technology not only fuels economic growth but also enhances societal well-being and resilience.
"Our Sovereign Public Cloud meets the highest standards of assurance, with all workloads, models, and data processed within the UAE under national jurisdiction. It is governed by Insight, Core42’s compliance and controls platform, which provides complete visibility and policy enforcement across every environment."
The cybersecurity landscape is undergoing its most profound transformation in decades. Perimeters have disappeared, hybrid work is now quite entrenched, and cloud-first architectures have become the default foundation of digital business. Attackers, meanwhile, are no longer relying solely on brute-force tactics or broad malware campaigns. They are now leveraging automation, behavioural mimicry, and increasingly, artificial intelligence to accelerate every stage of the attack chain. In such an environment, the traditional network security model has collapsed under its own limitations.
This shift has pushed Zero Trust from an aspirational design philosophy to a frontline operational imperative. Modern enterprises, regardless of industry, size, or geography, now rely on Zero Trust as their foundational defence model.
While Zero Trust remains the only defendable architecture in today’s environment, its success depends heavily on organizational culture, identity governance, and continuous enforcement. More importantly, artificial intelligence is set to redefine both attack and defence paradigms, requiring enterprises to evolve beyond static Zero Trust models into adaptive, intelligent security ecosystems.
Zero Trust’s relevance in 2025 is rooted in a simple truth that attackers no longer need to break in; they simply log in. Identity-driven attacks have overtaken perimeter-based intrusions, and the assumption that everything inside an enterprise network is safe has become dangerously obsolete.
Faisal Khan, Associate Director, Information Security & Compliance IT Security and Compliance, DWTC says "Zero Trust has become essential, simply because the old assumptions of a secure internal network no longer hold valid. Workloads, data, and users now sit everywhere, so trust can’t be inherited rather it has to be earned with every request."
He highlights that Zero Trust is not a product category or a technology purchase but a behavioural transformation.
"In our environment, we treat Zero Trust less as a product and more as a culture shift. Every system, user, and device must continuously validate its identity and intent. This approach has helped us reduce lateral movement, tighten access pathways, and
Faisal Khan
Associate Director, Information Security & Compliance IT Security and Compliance, DWTC

give leadership a clearer view of real risk instead of perceived safety."
This perspective resonates across the industry. Organizations adopting Zero Trust quickly learn that it requires dismantling long-standing assumptions about internal trust.
Karthik Hemachandran, Information Security Manager, Albatha emphasizes the same point when he says, "Zero Trust is essential because the traditional perimeter no longer exists and attackers don’t need to force their way in anymore; they simply log in using compromised credentials, exposed APIs, misconfigurations, or weaknesses in third-party access. Identity-driven attacks dominate the threat landscape, and relying on implicit trust inside a network has become a systemic risk."
He goes further to position Zero Trust not as an enhancement, but as the only sustainable operating model.
"In my view, Zero Trust is not just a framework. It is the only defensible operating model for the digital era. We trust Zero Trust; everything else is challenged and certified."
Jacob Mathew, Technology and Cybersecurity Leader adds a wider operational angle, noting that Zero Trust’s rise stems from the fragmentation of digital environments.
He says, "Zero Trust is moving security away from traditional network perimeters and placing identities at the centre. The focus is now on least-privilege access for both human and machine accounts, supported by just-in-time access for sensitive or privileged tasks."
Collectively, these insights portray a cybersecurity world where
trust is no longer a default state and it must be continuously earned, verified, and monitored.
Micro-segmentation appears at the center of every strong Zero Trust architecture. The reason is simple: once attackers breach an initial point, whether through phishing, credential theft, or supply chain compromise, their ability to move laterally determines the scale of the damage.
Faisal underscores how micro-segmentation is key to internal security posture.
"Micro-segmentation being an essential part of the Zero trust framework gives us the ability to contain threats before they spread. Instead of relying on large network zones, we break environments down into smaller, isolated segments with strict access policies."
Elaborating on the “small room vs large building” analogy that has become central to segmentation discussions, he says, "This means even if an attacker compromises a single asset, they’re essentially trapped in a small room rather than gaining access to the entire building. For us, micro-segmentation has been crucial in protecting high-value systems and legacy workloads that cannot be modernized easily."
Karthik shares his assessment, "Micro-segmentation is one of the most decisive enforcement layers in a Zero Trust strategy. You simply cannot claim Zero Trust while operating a flat network; that is security theatre, not security architecture."
He highlights the critical risk area; the east–west traffic.
"East–west traffic is where attackers thrive, and micro-segmentation is the only realistic way to control that internal movement with precision."
By isolating workloads, segmenting application pathways, and restricting internal trust boundaries, micro-segmentation becomes the practical enforcer of Zero Trust, not just a conceptual layer, but a lived operational barrier.
Protecting data throughout its lifecycle is a defining requirement of Zero Trust. The experts converge on a shared belief that datain-use security is now the most critical and most exploited gap.
Jacob outlines a structured approach driven by classification and policy enforcement.
He says, "The first step is to ensure that all data is classified, staff trained and data has security controls in place based on the data classification."
He then goes to elaborate on the specific protections across data states.
Jacob Mathew Technology and Cybersecurity Leader

"For data at rest, I rely on strong encryption and strict access controls. For data in motion, I use secure protocols, micro-segmentation, and identity-driven policies. For data in use, I focus on endpoint hardening, real-time monitoring, and adaptive controls that verify behaviour before allowing access."
This comprehensive approach reflects how data security must now be tied directly to identity and behavioural controls.
Karthik points out that the blind spots need to be taken care of when securing data.
"Protecting data requires more than encryption and good intentions. If you only secure data at rest and in motion, attackers will simply take it while it’s in use. That is the blind spot most compromises exploit."
He also highlights one of the most overlooked risks in modern IT environments, which is backups.
He says, "Backups are often the forgotten exposure. Too many administrators leave backups unencrypted because it’s 'faster' to decrypt and restore. Faster for attackers too. Zero Trust treats backups with the same rigor as live systems."
The message is clear that is data protection in a Zero Trust world must be continuous, contextual, and state-agnostic. Anything less leaves exploitable gaps.
The modern enterprise operates across an ecosystem of clouds, devices, and remote endpoints. In this environment, Zero Trust is not just useful but a requirement.
Jacob highlights the identity-centric architecture that makes this possible.
"The focus is now on least-privilege access for both human and machine accounts. This approach closes the gaps between cloud platforms, remote endpoints, and SaaS environments, giving leaders a consistent, scalable, and more adaptable security posture across the entire digital estate."
Karthik emphasizes the dependence of cloud architectures on Zero Trust:
"Zero Trust is the only security model that actually makes the modern workplace possible. Multicloud, SaaS adoption, and remote work have erased any notion of a fixed perimeter, and without Zero Trust the entire structure would collapse under its own complexity."
This highlights a critical reality that cloud security cannot rely on perimeter assumptions or flat network models.
Karthik make a blunt assessment of legacy approaches when he says, "Cloud environments depend on identity-driven access and continuous verification; trying to operate them with legacy trust assumptions is simply unthinkable."
From SaaS to hybrid cloud, Zero Trust has become the connective tissue that maintains consistent policy enforcement and reduces the attack surface across heterogeneous platforms.
Zero Trust adoption is not without obstacles. All three experts identify the same core challenges. The typical hurdles are visibility gaps, unmanaged devices, and legacy infrastructure.
For Faisal, visibility is the biggest challenge. He says, "The biggest hurdle is visibility. You can’t enforce trust where you don’t have insight. Distributed teams, contractors, and unmanaged devices introduce gaps in control and monitoring."
He explains, "We counter this with stronger endpoint checks, conditional access, and shifting sensitive workloads into controlled virtual environments."
Karthik agrees, pointing out the operational difficulties rather than technical ones. In his opinion, "The hardest part of extending Zero Trust isn’t the technology; it’s the reality of how people work today."
He says that unmanaged devices are the largest blind spots.
"Unmanaged devices remain the biggest blind spot. They are endpoints without posture, control, or accountability. When contractors and third parties arrive with their own machines and their own security standards, it creates an unpredictable attack surface that no policy alone can clean up. You cannot enforce contextual access if the context itself is unreliable.”
He further highlights legacy systems as a major barrier.
"Legacy systems make this worse. Many of them can’t handle modern authentication or conditional access and force organizations to maintain insecure exceptions. BYOD, inconsistent JML processes, and user resistance to stricter controls all add friction to an already complex ecosystem."
These challenges reveal that while Zero Trust principles are sound, the practical realities of distributed work and legacy technology often slow or complicate implementation.
According to Jacob, these are challenges to Zero Trust implementations from an organizational culture point of view. He says, “I often find the technology part of Zero Trust far easier than the cultural shift that comes with it. The biggest challenges are getting teams to move away from legacy thinking, breaking long-standing trust assumptions, and building a mindset where identity, verification, and continuous monitoring become part of everyday work. It also requires strong sponsorship from leadership, clear communication, and steady change management to ensure people understand why these changes matter and how they support a safer, more agile business."
All three experts unanimously agree that Zero Trust alone will not be enough to defend against next-generation AI-powered threats. Faisal summarises the evolving threat landscape when he says, "Zero Trust gives us a strong foundation, but AI-driven attacks change the game. Attackers can now move faster, mimic user behaviour, and bypass traditional indicators."
Jacob says that we have to move towards an adaptive model while Zero Trust is foundational.
“Zero Trust is a great starting point, but frankly in my opinion, it can't hold up alone against the new wave of AI-powered attacks. The bad guys are now using AI to automatically spy on us (reconnaissance), build perfectly customized weapons (exploits), and even change their tactics instantly as they attack. This means our defences can't be static anymore. We have to be just as dynamic. We need to add extra muscle, like continuous behavioural analytics, autonomous threat response, and real-time identity risk scoring that can adjust access decisions instantly. The future of cybersecurity isn't sticking to fixed "Zero Trust" rules; it's moving toward an adaptive model where AI works for us, helping us predict, block, and contain threats."
Karthik says that Zero Trust alone won’t be enough to tackle AI driven threats.

"Zero Trust remains essential, but it is no longer sufficient on its own… AI-driven attacks have changed the pace and scale of threats, and organizations that stop at Zero Trust will find themselves outmatched."
He says, "The future of cybersecurity is Zero Trust supported by intelligent, adaptive, AI-driven defence that reacts faster than human teams ever could."
The consensus that emerges from the expert perspectives is that Zero Trust is necessary, but AI-augmented defence is inevitable.
Zero Trust has moved beyond buzzword status to become the structural backbone of enterprise security. It reshapes identity governance, network design, data protection, and cloud architectures. Yet, as AI-driven threats accelerate, Zero Trust can no longer stand alone. The next generation of cyber defence will be built on Zero Trust principles but enhanced through dynamic analytics, behavioural intelligence, and autonomous response.
Organizations that adapt will gain resilience. Those that treat Zero Trust as a one-time project rather than a dynamic security operating model will fall behind. The future belongs to enterprises that combine Zero Trust with continuous learning, adaptive intelligence, and a culture of verification, because in the modern threat landscape, trust is no longer a default. It is earned, enforced, and continuously validated.
In this interview, Neil Roseman, CEO of Invicti, explains how proof-based results, ASPM, and AI-enhanced DAST are helping organizations secure modern applications at scale, without slowing innovation.
What do you see as the most significant threats enterprises face today when it comes to application security, and what best practices should they prioritize to reduce these risks?
AI is accelerating everything, including risk. Enterprises are building and deploying software faster than ever, often with AI-generated code that no one fully reviews or understands. The math is simple: more code means more vulnerabilities, and that’s before factoring in the sometimes questionable quality of AI-supplied code. The best defense is automation that’s deeply embedded in the DevSecOps workflow. You need security scans that run at the same speed as your releases and are automated, continuous, and accurate enough to trust without second-guessing.
How has Application Security Posture Management (ASPM) evolved, and why has it become such an essential component of modern security programs?
As an industry, we’ve gone from chasing vulnerabilities with point tools to drowning in data from dozens of scanners. Everyone demanded automation, and they got it, but automation without prioritization only amplified the noise. That drove the need for ASPM to tie everything together so teams can focus on what actually matters: risk that’s real and exploitable. Today, ASPM isn’t a convenience feature – it’s foundational for any mature AppSec program.
Invicti has been actively embedding AI capabilities into its DAST solutions. How is AI enhancing accuracy, coverage, and remediation speed across your testing processes?
AI is transforming how we test applications. We’re using it to solve the hardest automation challenges, especially “fuzzy” problems like login, authentication, and complex workflows that used to require manual setup. This lets us crawl and test deeper, deliver more accurate results, and drive better correlation and prioritization. What matters is that we’re using AI not as a gimmick but as a force multiplier for our already industry-leading capabilities like proof-based scanning. Unlike some competitors, we’re not pretending it’s a magic box.

Neil Roseman CEO,
Invicti
How important is it to embed security throughout the developer workflow, and what steps can organizations take to ensure developers become active stakeholders in application security?
You can’t bolt on security anymore, it has to live where developers live. The fastest way to make developers care about security is to make it frictionless. Tools should run in the repo and CI/ CD pipeline, not in a separate universe. But the traditional shiftleft message has worn thin as static tools flood developers with noise and false positives. That’s why we’re focused on DAST that’s integrated, zero-noise, and proof-based. When you can automatically send a verified ticket that says, “Here’s an exploitable critical issue and here’s how to fix it,” that’s when developers can truly adopt a security mindset.
API-related vulnerabilities have become a major attack vector. How does Invicti approach API security, and what are the biggest challenges organizations face in this area?
Modern applications are really about the backend APIs being called. The biggest challenge now is finding, cataloging, and testing all those APIs, including the shadow and zombie ones nobody knows about. We’ve been steadily expanding Invicti’s API security capabilities, and we now offer something unique in the industry. Invicti combines multi-layered discovery with industry-leading API scanning on one unified platform. Whether through zero-click, sensorless, or agent-based discovery, we help customers find every endpoint and then prove which ones are truly vulnerable.
Invicti has been broadening its product suite in recent years. Can you highlight some of the latest additions or enhancements that expand your value proposition beyond traditional DAST?
Invicti started as the best DAST in the world (and it still is), but today we’re much more than that. We’ve evolved into a full application security platform that covers the entire attack surface, so not just web frontends but also APIs, both in scanning and discovery. We’re adding AI-powered scanning features that move toward automated pentesting. And our acquisition of Kondukto has brought advanced ASPM that connects all this data into one unified risk view. We’re not only delivering accurate, proof-based results but also helping customers see the big picture and manage their overall security posture.
Visibility and prioritization are often challenges for security teams managing hundreds of web assets. How does Invicti help customers gain unified visibility and prioritize vulnerabilities that matter most?
Security teams don’t fail from a lack of data, they fail from too much of it. The problem comes from three areas: too many apps and APIs, too many tools, and too much noise from those tools. Invicti cuts through that chaos with verified results from proofbased scanning, unified within an ASPM platform that centraliz-
es and correlates everything. Our DAST acts as the fact-checker that keeps other tools honest. And our Predictive Risk Scoring highlights the riskiest assets even before scanning, helping teams focus their efforts where they matter most.
As AI-driven development and low-code platforms proliferate, how is Invicti preparing to secure the next generation of rapidly built and deployed web applications?
We’re entering the era of black-box development: code written by AI, deployed by anyone, and running everywhere. In that world, traditional code-based testing can’t keep up because no one knows where the code lives or how it really works. That’s why DAST is becoming more valuable than ever. DAST is tech-agnostic and really the only way to test security from the outside in at scale, without needing source code. No matter how that app is built, who or what wrote it, or how many new apps appear every week, we’re helping customers stay ahead in a world where software builds itself faster than humans can review it.
"Invicti combines multi-layered discovery with industry-leading API scanning on one unified platform. Whether through zero-click, sensorless, or agent-based discovery, we help customers find every endpoint and then prove which ones are truly vulnerable."
Jérôme Freani, Chief Product Officer at Aleria, shares insights on the company’s sovereign intelligence vision, new innovations like Aleria Sources and video analytics, and strategic partnerships with MBUZZ, NVIDIA, and DDN driving regional AI growth.
Discuss what solution Aleria focuses on?
Aleria provides a sovereign, scalable AI solution covering everything from cloud orchestration of infrastructure and services to our big data platform. It allows customers to connect to all different sources of data; ERP, CRM, databases, IoT, and more, and apply AI directly on top of it. AI can take different shapes through our operating system, using large language models, vision models, voice models, and many other applications implemented within companies in the UAE and worldwide.
Discuss your operations, focus and partnerships in the region?
We are based in Abu Dhabi and currently distributing our solutions across the Middle East and globally. Our partnerships with MBuzz, NVIDIA and DDN allow us to push our reach even further and scale our ecosystem internationally.
What were the highlights at your GITEX showcase?
GITEX is the largest event worldwide for tech startups, AI and emerging technologies. We were proud to participate this year with our partners NVIDIA, DDN and MBuzz, to represent solutions that are built in the UAE and look for global expansion.
Discuss your video AI solution?
Video AI is our solution for applying AI to any video stream. It covers all the analytics you can imagine, but goes beyond that with our own large language model embedded within it. This makes the Video AI platform capable of performing an almost unlimited number of use cases.
What is Aleria Sources all about?
Aleria Sources is our big data platform that connects to literally any source of information and processes it at high speed, on average 30 times faster than anyone else on the market. It enables customers to load, prepare and transform data as required and then feed it into AI models so the data can be exploited properly.
You emphasize “sovereign intelligence.” What does that mean for your customers?
Sovereign intelligence means that all AI capability and knowledge remain in the country where the platform is deployed. We give full control back to customers, whether running on sovereign infrastructure, where they fully control their data, or deploying the solution on-premise for maximum security and confidentiality.

Jérôme Freani Chief Product Officer, Aleria
Which customer segments is Aleria targeting in the region?
We cover different verticals, from SMBs, which we serve together with Etisalat, to government clients looking for turnkey solutions from infrastructure to end-user applications. We also work extensively with enterprises across different sectors.
What role do your ecosystem partners play in delivering these solutions?
We partner with MBuzz and DDN to deliver the best hardware and software solutions to our customers, ensuring that AI becomes embedded at their core and that they can use it every day with solutions that work today—not in the future.
At GITEX Global 2025, CXO DX spoke with Fady Richmany, Corporate VP & GM EMEA’ Emerging Markets -CEE, CIS, Middle East & META, Commvault about the company’s evolving approach to cyber resilience, its Metallic-powered Commvault Cloud platform, clean room recovery innovation, and the growing focus on securing AI workloads.
How does Commvault define cyber resilience, and what differentiates your platform’s approach from traditional backup solutions?
Back in the day, only a few companies could remain in the data protection game. Commvault has always been one of those pioneers, moving beyond traditional backup to what we now call cyber resilience.
The shift really began after an event we hosted in New York in October 2023, where we launched the Commvault Cloud Platform powered by Metallic. Metallic, our leading SaaS brand, became incredibly successful; our SaaS business grew from zero to 100 million dollars. So our Chief Marketing Officer decided to bring the two brands together under the Commvault Cloud umbrella.
We built the new platform on Metallic’s cloud-native, zero-trust architecture with AI capabilities fully integrated.
In simple terms, cyber resilience for us means helping customers detect, withstand, and recover from cyberattacks as quickly as possible. It’s about ensuring they are prepared and able to sustain operations with minimal disruption.
If a customer is breached, how fast can they come back to life? That’s the essence of fast cyber recovery, but it doesn’t happen out of thin air — it requires preparation.
We define cyber resilience around three key principles.
First, be ready, have immutable storage, air-gapped copies, and ensure no one can delete backups without authorization. Second, protect your Active Directory; It’s like the keys to the kingdom. Securing it is essential. And finally be ready to recover; continuously test your good copies and validate recovery workflows so you can restore quickly when things go wrong.
What about preventing reinfections after an attack, such as through clean room recovery?
Nothing can completely stop breaches, but managing resilience is where the focus should be. Cyber resilience goes beyond cybersecurity.
Corporate VP & GM EMEA’ Emerging Markets -CEE, CIS, Middle East & META, Commvault

Unfortunately, many organizations still invest heavily in firewalls, intrusion detection, and anomaly scanners and yet they get breached. The attack surface is too large, and threats can come from anywhere: internal users, external actors, or even a misplaced USB drive.
We run awareness programs like “Minutes to Meltdown”, a real simulation exercise for customers. It’s a tabletop scenario where CIOs, CISOs, and other leaders see how a breach unfolds in real time, from a simple email or user action, to understand how quickly things can escalate.
No amount of perimeter security can guarantee protection; you must be prepared for recovery.
We’ve seen real incidents where the ransom demands have been huge. Recovery can take time and costs, and in critical verticals like healthcare, it could be in millions. If organizations are ready and proactive, the impact would be minimal.
How ready is the regional market when it comes to cyber resilience and backup preparedness?
The UAE and wider GCC are pioneers. They are a beacon of innovation and technological advancement. The UAE Cyber Security Council has done an excellent job creating awareness, and we’re proud to partner with them on that mission.
We recently had the privilege of hosting their leadership at our booth during GITEX, and the collaboration is strong.
However, our studies show that trust is fragile; about 50% of consumers say they won’t do business again with a company that’s been breached. Even personally, I don’t store my credit card details online anymore. That’s how real the trust issue has become. People underestimate how breaches affect everyday lives. For example, in a breach in the healthcare segment, patients lost years of medical records. You can’t redo scans or blood tests; that’s data gone forever. That’s why cyber resilience is not optional; it’s essential.
Tell us more about Commvault’s clean room recovery and other new technologies.
Clean Room Recovery as a Service is our trademark innovation. We were the first in the industry to offer it. Once you have your “golden copy” of data from the vault, you can test and redeploy it safely.
Normally, rebuilding your application stack after an incident could take weeks. With Commvault Cloud Rewind, we can do it in an hour.
Commvault automates a cost-optimized data lifecycle that tiers copies to archival storage for less frequently accessed data. Combining Amazon S3 Glacier, Amazon S3 Batch Operations, and Commvault, you can achieve ultra-low-cost storage and optimal restore times, achieving up to 70% TCO reduction with faster scalability.
Recently, we acquired a company called Satori, which strengthens AI security, protecting large language models (LLMs) and their underlying data. This acquisition makes the Commvault Cloud Platform more secure than ever and bridges the gap between data protection and AI security.
How is Commvault preparing for the rise of AI workloads?
We’re already ahead of the curve. AI is central to our strategy. On November 12, at our upcoming event in New York, we’ll make a major announcement focused on AI and the security of AI. Watch that space; it’s going to be a big one.
What have been the key highlights for Commvault at GITEX Global this year?
GITEX is always an incredible platform. It brings us closer to customers and partners.
This year, we signed several major MOUs and technology partnerships, including with HPE to integrate Zerto into our offerings, CrowdStrike for integrated security, and Beyond Identity Management.
We’ve also announced our Hyperscale X architecture, a software-defined solution built on HyperFlex, and deepened collaboration with Core42’s Sovereign Cloud, where we are among the top ISVs providing resilience capabilities.
We’re deeply embedded in the region’s technology ecosystem, with a strong market share across most verticals including manufacturing, retail, defense, healthcare, education and more. Every day, we continue innovating to help customers strengthen their resilience and recover faster from the unexpected.
"In simple terms, cyber resilience for us means helping customers detect, withstand, and recover from cyberattacks as quickly as possible. It’s about ensuring they are prepared and able to sustain operations with minimal disruption."
Tejas Lagad, Director – Asia, Middle-East, Africa for Digital Services at IN Groupe, shares strategic insights on how identity-first security, PKI modernization, and quantum readiness are shaping enterprise and government priorities in the region.
In today’s hybrid and highly distributed IT landscape, how does Nexus help enterprises in the Middle East maintain digital trust across users, devices, and applications, while keeping the process simple and manageable?
In a region where digital transformation is accelerating across government, finance, and energy, Nexus empowers organizations to maintain digital trust through its Smart ID platform. The solution delivers identity-first security for users, devices, and applications, whether hosted on-premise, in national data centers, or in the cloud.
Nexus today supports leading telecom operators, smart cities, the energy sector, and financial institutions across the GCC, simplifying trust management through automated certificate lifecycle management and Identity-as-a-Service (IDaaS). It ensures compliance with Saudi Arabia’s NCA ECC and UAE’s NESA frameworks while readily integrating with Tasheer, Nafath, and GCC smart city ecosystems, advancing digital sovereignty and interoperability.
As IoT and OT environments continue to converge, what’s Nexus’ approach to securing identities and authentication for connected devices in sectors like manufacturing and critical infrastructure?
As IT and OT environments converge in oil & gas, utilities, and transportation, Nexus delivers device identity assurance from the factory floor. It's Factory CA issues digital birth certificates to devices at the manufacturing stage itself, ensuring secure identity from day one.
This approach is already being used by regional energy producers and industrial automation providers to secure their connected ecosystems. Nexus also enables secure firmware signing, code validation, and Matter-compliant attestation aligned with IEC 62443, the EU Cyber Resilience Act, and Saudi Vision 2030—helping strengthen national resilience across critical infrastructure.
How does the Nexus platform secure cloud and on-premise environments, particularly when compared to the PKI capabilities of Microsoft ADCS?
While Microsoft ADCS was designed for traditional IT, Nexus provides a sovereign, cloud-ready PKI built for hybrid architectures and regulated sectors. It supports open standards like ACME, EST, and REST, enabling full automation and integration with regional cloud platforms and government services.
Trusted by public-sector clouds and tier-one banks in the Middle East, Nexus PKI—Common Criteria EAL4+ certified—offers active-active high availability and cryptographically signed audit logs. It’s a strategic modernization of digital trust aligned with Zero Trust and national digital sovereignty priorities.
How do you help enterprises automate the full lifecycle management of workplace device identities, and why is this automation becoming so critical today?
With distributed workforces and mobile-first operations expanding, automation is now essential. Nexus’ Smart ID for Workplace Devices and GO MDM integrate with Microsoft Intune, ServiceNow, and regional ITSM tools to manage both domain and non-domain devices.

Tejas Lagad
Director – Asia, Middle-East, Africa for Digital Services, IN Groupe
Major GCC telecoms, insurers, and public entities already rely on Nexus automation to manage millions of certificates—avoiding expiry outages, closing security gaps, and ensuring continuous compliance with NCA ECC and NESA. This frees IT teams to focus on innovation instead of firefighting.
How are compliance requirements influencing enterprise PKI strategies, and how is Nexus aligning its solutions to this shift?
Middle Eastern enterprises are aligning with national cybersecurity mandates such as NCA ECC, NESA, and Q-CERT, demanding cryptographic assurance and auditability.
Nexus, part of IN Groupe, supports this evolution with policy-based issuance, certified PKI, and tamper-evident audit trails. Its solutions underpin qualified e-signature, citizen ID, and e-government programs across multiple GCC countries, enabling compliance, interoperability, and long-term scalability.
How important is it for organizations to be ‘quantum-ready’ when it comes to PKI, and what steps is Nexus taking to enable this readiness?
Quantum readiness is no longer optional. Nexus is embedding post-quantum cryptography (PQC) standards such as CRYSTALS-Kyber and Dilithium, in line with NIST FIPS 203–205.
In collaboration with financial regulators and national digital identity authorities, Nexus is helping organizations define quantum-safe PKI strategies that secure their infrastructures well into the next decade—protecting everything from government data to financial transactions.
Nasri Nassereddine, Regional Vice President at Cumulocity, shares insights on AIoT adoption, challenges, and opportunities across the Middle East and Africa.
Discuss if and how AIoT is poised for a steep growth curve or adoption? What are the likely growth drivers globally and in the region?
AIoT is unquestionably on a steep growth trajectory. Globally the market is shift from proof-of-concepts to mainstream adoption, with AI and IoT increasingly increasingly viewed as an integrated engine of transformation rather than standalone technologies. Growth is being driven by the surge in connected devices, the maturity of AI models, and the rollout of high-speed networks such as 5G and LPWAN. At the same time, enterprises face mounting pressure to optimize resources, reduce costs, and achieve ambitious sustainability goals, making AIoT a natural enabler. In our region, the momentum is even sharper. National agendas like Saudi Vision 2030 and the UAE’s digital strategies prioritize smart cities, sustainable energy, and industry 4.0, creating fertile ground for AIoT to scale rapidly.
What are some specific challenges towards this journey?
This journey is not without challenges. Connectivity gaps remain in many regions, while enterprises contiue to grapple with data silos and legacy systems. Security and compliance are constant concerns, especially when data traverses edge, cloud, and onprem environments. Skills shortages are another challenge, as organizations often lack the expertise to combine AI with IoT to delivers measurable outcomes. Finally, moving from pilot to enterprise-wide deployments remains difficult, with scaling introducing adding complexity.
What are the solutions you bring to address AIoT deployments across industries? Which are the key industries for AIoT and for Cumulocity?
This is where Cumulocity stands apart. We offer an open, device-agnostic, low-code platform that simplifies the entire AIoT journey. Enterprises can onboard devices quickly, run real-time analytics at the edge or in the cloud, and integrate seamlessly with existing systems like ERP or SCADA. This flexibility supports a broad range of industries. In energy and utilities, we enable smart grids, predictive maintenance, and renewable integration. In manufacturing, we power digital twins, robotics, and quality control. In transportation and logistics, we deliver fleet management and asset tracking. In agriculture and smart cities, we support irrigation, waste, and environmental monitoring.
Discuss your regional operations and focus? Do you work directly with end customers or do you go with SIs?
In the Middle East and Africa, our focus is very clear, our strategy is partnership-led while staying close to strategic customers. For large-scale sectors such as utilities, energy, and mega-projects, we engage directly with end customers, always in collaboration with system integrators who bring scale and local presence. At the same time, we invest heavily in building ecosystems, through training programs, IoT hubs, and collaboration with universities and research institutes - to foster knowledge transfer and ensure sustainable growth.

How do your solutions address data security concerns across environments?
Security underpins everything we do. Our platform is built with multiple layers of security, including encryption, authentication, and strict role-based access controls. We comply with local data residency regulations, from GDPR in Europe to PDPL in Saudi Arabia, ensuring national requirements are met. By enabling analytics at the edge, we also minimize unnecessary data transfers, strengthening security while improving efficiency. Our multitenant, governance-driven architecture ensures that every deployment is isolated, controlled, and trusted.
What are the expected benefits across functions such as asset management, predictive maintenance etc? What other key enterprise functions can benefit significantly from AIoT? AIoT delivers measureable impact across enterprise functions. In asset management, it enables real-time visibility and lifecycle optimization. Predictive maintenance reduces downtime and extends asset longevity, while logistics and supply chains gain transparency and resilience. Beyond operatios, AIoT enhances sustainability, safety, and customer experience—helping enterprises operate more efficiently, launch new digital services, and meet environmental goals.
CRM today demands an AI-first approach that replaces traditional automation with intelligent, predictive, and proactive customer experiences writes William
O’Neill, Area VP & General Manager – GCC at ServiceNow
Traditional customer relationship management (CRM) systems are becoming increasingly obsolete, leaving brands at risk of falling behind the competitive curve.
Legacy platforms often create fragmented experiences and frustrated teams, by operating in silos. Intelligent CRM is now crucial to unify sales, marketing, service, and operations to deliver seamless customer journeys.
To fundamentally transform CRM, organisations must adopt a true AI-first mindset — shifting from digital automation to intelligent, predictive, and proactive engagement. This mindset should be three pronged: rooted in continuous learning, empowered by automation and futureproofed through predictive insight. Business success in the era of AI-driven transformation depends on it.
Your customer has changed, why hasn’t your technology?
We’re at an inflection point, with the United Arab Emirates (UAE) CRM market expected to grow to $402.14m by 2030. Regional businesses hope to modernise, meaning that CRM can no longer sit in the back office. Leaders need to rethink how they manage customer relationships as part of this, grasping AI as the catalyst for competitive advantage.
Omar Akar Regional VP, Middle East & Emerging Africa, Pure Storage
Sales teams want best-in-class tools that let them self-serve and find qualified leads so that they can quote high-value deals quickly without red tape. At the same time, revenue operations and finance are under pressure to streamline fulfillment, handle contract changes smoothly, and eliminate manual handoffs. Too

William O’Neill Area VP & General Manager – GCC, ServiceNow
often though, data silos between marketing and sales systems, challenges with order fulfillment and complex contract changes have stood in the way of this.
C-suite leaders across the UAE, and EMEA more broadly, are starting to recognise that simple digitalisation of processes won’t deliver the customer experiences that set them apart from the competition. Businesses, particularly in sectors like telecoms, finance, and manufacturing, are increasingly investing in agentic AI-enabled CRM to elevate customer experience and drive loyalty.
Generative and agentic AI are becoming established as major value drivers in customer relationship management, with measurable impact on key KPIs such as cost reduction, faster resolution times, lower customer effort, and improved satisfaction. For example, with agentic AI, ServiceNow is achieving 84% customer self-service and threefold improvement in case deflection, saving support teams 400,000 labour hours.
At the heart of this evolution is a shift in thinking, reimagining CRM as a living, learning system of action. This AI mindset is rooted in three core principles:
1. Continuous learning: Rather than remaining static, modern CRM systems are designed to evolve with every interaction. They gather and analyse data over time, enabling the system to become smarter, more responsive, and better attuned to customer needs. This is real-time data that can drive fast decisions and eliminate guesswork.
2. Automation: By removing repetitive and manual tasks, automation allows teams to focus on more meaningful, high-value work. This not only improves efficiency but also enables deeper, more purposeful engagement with customers.
3. Predictive insight: AI gives businesses the ability to anticipate customer needs before they arise, using data-led signals to tailor experiences and services at scale. At a macro level, this enables automatic work order creation, intelligent scheduling and dispatch, proactive service, and AI-driven process mining. At a micro level, this level of personalisation strengthens satisfaction, loyalty, and long-term value with the customer.
Bringing this vision to life requires a CRM platform where AI, data, and workflows are deeply integrated. Agentic AI goes beyond basic automation. It can reason, decide, and act, either with human oversight or independently, delivering richer and more dynamic customer experiences.
With structured workflows in place, agentic AI systems can handle everything from simple queries to complex service requests,
fully automating the end-to-end process. Aside from its customer specific dividends, the adoption of AI is also helping to boost productivity and showcasing how an AI-first approach to CRM can unlock smarter, more efficient engagement at scale.
AI-powered CRM as the baseline for customer growth
Ultimately, this drive to boost customer experience isn’t about improving service, it’s about beating the competition. Bolted-on systems and reactive CRM strategies belong to the past.
Across the region, businesses that adopt a three-pronged AI mindset in their CRM strategy are reducing friction and positioning themselves for confident growth. The future of CRM is intelligent, adaptive, and human-centric. Organisations that act now will be the ones that lead. The future of CRM isn’t just about managing relationships — it’s about transforming them.
"To fundamentally transform CRM, organisations must adopt a true AI-first mindset — shifting from digital automation to intelligent, predictive, and proactive engagement. This mindset should be three pronged: rooted in continuous learning, empowered by automation and futureproofed through predictive insight."
Michael Byrnes, Sr. Director of Solutions Engineering META at BeyondTrust outlines a series of essential security principles that every enterprise should adopt before integrating AI agents into production environments.
Organizations in the United Arab Emirates (UAE) have recognized that agentic AI is no passing fad. One estimate puts its UAE market size at US$34.1 million in 2024 and projects an almost 44% year-on-year surge to reach US$49.1 million in 2025. A five-year CAGR of 48.3% is expected to lead to a US$352.2-million market in 2030. We find ourselves in a growing ecosystem of autonomy, so we should be very clear about everything agentic AI is and everything it is not.
Agentic AI is independent and persistent. It can act as a valet to employees or customers. It can be a compliance steward, a finance strategist, an engineer, or a diagnostician. However, agentic AI is not risk-free. The enterprises that take the plunge with AI agents must grant them far-reaching authority if they are to behave autonomously. That requires a level of trust that must come with caveats. To wind up an AI agent and let it go without due oversight is to invite catastrophe. We should never fall into the trap of assuming AI agents cannot make mistakes or be compromised by malicious parties. So, let’s consider a 10-point security plan for onboarding agentic AI so your organization can reap the benefits while side-stepping the risks.
1. Treat each agent as an identity
In the simplest case, a threat actor needs only to hijack the security credentials of an AI agent to wreak havoc on an environment. AI agents should be considered machine identities with all the uniqueness and traceability that implies. Each should be assigned a human owner to act as a first-instance contact if an incident occurs.
2. Apply the principle of least privilege
Just like humans, AI agents have a job to do. But each agent should be granted only enough access to systems to do that job. Generic or catch-all permissions leave too many doors ajar for attackers, so adopters of agentic AI must take care not to over-provision access for the expediency of the AI journey. Instead, use role-based access control (RBAC) or attribute-based access control (ABAC) and frequently review privileges to ensure unnecessary ones are removed.

Michael Byrnes Sr. Director of Solutions Engineering META, BeyondTrust
Agents, like humans, eventually complete their tasks and no longer need the systems access that was necessary to perform them. Persistent access is a common weak link in identity security. JIT access is an established best practice that calls for the revocation of credentials when tasks are complete. Secrets management solutions and privileged access management (PAM) platforms can help with orchestrating diligently logged, auditable JIT access.
The authentication of any person or autonomous digital process cannot be treated as a one-door event. Many damaging incidents can occur mid-session. Sessions should be monitored for any changes in agent behavior, and each escalation of privileges should be accompanied by additional authentication layers. Organizations should pay special attention to sensitive milestones like financial transfers or reconfigurations. Any unwarranted privilege escalations or exfiltration of sensitive data are worthy of red flags.
Agentic AI often uses other AI and data sources either through APIs or SaaS integrations. A best-practice audit of all third-party systems and resources is advisable. Any AI model or data pipeline that is used without validation of cryptographic signatures will constitute a risk. The reputation of the provider is also relevant. Organizations should embrace CVE monitoring and scan dependencies for vulnerabilities. Secrets management solutions can be used to store and administrate third-party API keys rather than embedding them in code or in unencrypted text files.
6. Establish network and identity boundaries
Agentic AI must be restricted in the resources to which it can connect. Access control lists and brokered communication through MPC servers will ensure that in the event of a compromise, an agent cannot be used for lateral movement. Enterprises should make use of sandbox development environments and separate control and data planes for production.
7. Maintain audit trails
Log everything for the day of accountability. If a cyber incident occurs, investigators must be able to see what each agent has been doing. This can only be done using encrypted, restricted, tamperproof logs.
8. Integrate agentic AI into ITDR
Unlike humans, AI agents can be part of the threat actor’s arsenal, acting on their behalf in real time. By streaming agent logs into identity threat detection and response (ITDR) systems (or SIEM, XDR, or SOAR platforms), UEBA (user and entity behavior analytics) can analyze telemetry as if it originated with a human, albeit using different baselines. For example, suspicious behavior for an AI agent might be behaving too much like a human.
9. Mandate human oversight
Human-in-the-loop is crucial for high-risk milestones. Agents should not, for example, be allowed to grant their own privileges. Be sure to identify the most sensitive workflows in your organi-
zation, such as financial or security, and make them subject to human assessment. Back this up with policies and escalation procedures and allow session shadowing so human agents can step in to prevent unfolding disasters.
10. Train users to be risk-aware
Humans are involved not only in the use of agentic AI but in its governance. That workforce must understand how to construct policy, how to escalate incidents, and how to safely design, implement and use AI. Make sure staff can identify AI risks. Run threat simulations and red-team exercises to show the consequences of errors.
Identity security has become the foundation of a mature threat posture in 2025. You will note that many of the urgings here are repurposed from those of humans and other machine identities. The difference between these identities and agentic AI is scale and speed, and those same differences apply to the harm that could be caused by compromised AI agents. AI agents can achieve more in a second than a human can in a year. And cyber compromise at the speed of light is something about which every organization should be concerned.
"To wind up an AI agent and let it go without due oversight is to invite catastrophe. We should never fall into the trap of assuming AI agents cannot make mistakes or be compro mised by malicious parties"
Onboarding artificial intelligence can secure the future of world’s critical electric systems through improvements in efficiency, innovation and decision-making. Power companies must adapt to thrive, says Gary Wong, Global Segment Leader of Power, Utilities, and Infrastructure at AVEVA

Gary Wong Global Segment Leader of Power, Utilities, and Infrastructure, AVEVA
The future of power and infrastructure hinges on algorithms, not concrete or cables. Companies that master data-driven decision-making will build the grids and networks of tomorrow—whether through new projects or by squeezing efficiencies from congested and aging systems.
But catering to the growing global population and the push for decarbonization requires new approaches in infrastructure. Not only do aging systems need to be upgraded, but utilities must become resilient and agile to withstand business uncertainties and freak weather events.
Power grids require $3.1 trillion in investments before 2030, according to research firm Rystad Energy. The lack of investment is
showing up in inefficiencies, reliability issues and missed opportunities in integrating renewables. In the US, for example, nearly 2,600GW of total generation and storage capacity—almost entirely zero-carbon—was awaiting connection even before Donald Trump’s inauguration. Across the pond, aging and outdated systems hinders National Grid Energy System Operator battery use in the UK, wasting renewables and increasing reliance on fossil fuels.
Relying on traditional models—manual controls, siloed approaches and static planning—is no longer sufficient. That’s where algorithms come in.
Power infrastructure is becoming smarter and greener, led by industrial artificial intelligence (AI) applications, and supported by the internet of things (IoT) and cloud computing.
Together, these technologies play a multi-faceted role in modern energy management, to take just one infrastructure example.
Using IoT data in the cloud, AI algorithms can predict energy demand with precision and optimize the integration of intermittent renewables such as wind and solar to adjust energy production, reduce waste and improve reliability. In contrast with traditional methods that rely on expansive assumptions and periodic schedules, these innovations deliver measurable improvements for cash-strapped utilities, with real-time feedback loops enabling human operators to optimize decisions and prevent issues before they arise.
On just one front, onboarding digital technologies today could save $1.8 trillion in global grid investment over the next two decades, according to the International Energy Agency.
Duke Energy knows how algorithms can save costs and improve
performance. Its single-window Monitoring and Diagnostic Center monitors diverse assets from renewable energy to coal and gas facilities across 60 plants in seven US states. Using low-cost sensors and AI algorithms, Duke tracks more than 500,000 data points and runs over 11,000 automated models across its fleet. Its operators now have real-time performance visibility and are alerted to problems before or as they occur. They have saved more than $250 million through predictive interventions so far, with one single early catch avoiding costs of $34 million.
Data-led technologies in the cloud likewise support cross-industry collaboration. Companies can jointly meet market needs by sharing operations information over a digital backbone. The USbased Western Energy Imbalance Market (WEIM) is a wholesale energy trading market that enables participating organizations to buy and sell energy. An advanced digital suite brings together its 22 members within a connected ecosystem, providing access to real-time information on market performance, business trends, and potential misalignments so that operators can minimalize financial settlement risks. Efficiency and decision-making have improved, and each WEIM member additionally benefits from flexibility and scalability, enabling competitiveness in an evolving market.
Elsewhere, innovative grid management is tackling the proliferation of new devices such as EVs, smart meters and solar panels are plugged in. UK Power Networks (UKPN) delivers electricity to 19 million homes in one of the world’s largest population centers. Recognizing the limits of reactive maintenance, it developed a data-intensive platform that processes four billion data points daily. AI-powered analytics predict failures before they happen, reducing outages and improving efficiency. With a centralized hub and streamlined operations, system operators can focus on network resilience, load balancing and strategic infrastructure decisions.
These are just some of the ways data and AI are proving their worth across key performance indicators such as grid reliability, cost reduction and energy efficiency in ways traditional methods can’t match.
But while AI will speed up grid modernization, it can’t do so without humans. Only when experienced professionals program, monitor and fine-tune digital systems in line with business and social goals, can they yield superior outcomes.
AI-generated insights can guide long-term planning and real-time algorithmic adjustments can address immediate challenges, but neither can replace human expertise.
That’s why the majority (75%) of power producers in key global markets will prioritize investments in AI for over the next 12 months, according to the AVEVA Industrial Intelligence Index
2024. Speaking about key target investments with the greatest potential to drive opportunity for their organization, nearly half (43%) of executives look to invest in digital platforms that enable their workforces to share data and collaborate with internal and external partners.
AI will be indispensable in driving utilities’ transition. But adopting AI isn’t a single-step upgrade. Whether in power or other sectors, companies must take a phased approach to go from outdated systems to intelligent, self-optimizing networks.
1. The first step is building a digital foundation after a comprehensive audit of existing infrastructure and data collection practices, value chain inefficiencies and operational challenges. By assessing where improvements are needed, companies can pinpoint target areas for AI-driven solutions.
2. Next, establish the necessary digital infrastructure for AI. Typically, this is a mix of cloud and edge computing to ensure applications run efficiently and effectively. The cloud delivers scalability, while real-time processing happens at the edge— critical to immediate decisions around predictive maintenance or load balancing.
3. Pilot programs with clear success metrics are crucial to test AI’s effectiveness and minimize risk. Well-defined pilots allow strategic recalibration and can secure buy-in.
4. Next come scaling and refining AI solutions across all aspects of operations, including
5. deploying customer-facing AI tools in line with business goals. Constant fine-tuning using live operational data is essential to get the most from AI tools.
6. As AI systems mature, the most essential step for long-term success is continuous innovation. This occurs by way of real-time performance monitoring, regular retraining of AI models with new data to improve accuracy and adaptability, periodic comparisons with KPIs and benchmarks, and adjusting goals based on performance insights.
The rise of digital-first utilities is only a matter of time. With the AI in energy market growing at a compound annual rate of 36% through to 2030, data-driven technologies will play a seminal role in building secure and decarbonized power and infrastructure systems to support humanity’s future. However, for AI-led digital transformation to be truly effective, it must be guided by clear policy frameworks, strategic partnerships with technology providers and investors and open dialogue with customers.
Algorithms can cement power’s future, but only if all stakeholders are on board. The question is no longer whether the sector will adopt AI; it’s whether it will do so fast enough to remain competitive.
Huawei eKitEngine AR180 series routers are high-performance enterprise-grade wireless routers designed for small and micro networks. They feature a robust, refined exterior with premium build quality.
The AR180 series supports Wi-Fi 7 technology, delivering dual-band concurrent speeds of up to 3600 Mbps. This enables smooth video streaming and gaming across multiple endpoints simultaneously, significantly improving user experience.
In terms of port configuration, the AR180 and AR180 Plus come with one 2.5GE high-speed LAN/WAN interchangeable port, one fixed GE LAN port, and three GE LAN/WAN interchangeable ports. Including all the above ports, the AR180 Pro provides an additional 2.5GE high-speed LAN/WAN interchangeable port for enhanced scalability. In addition, all models provide a dedicated Turbo acceleration port that prioritizes traffic from connected devices, effectively reducing latency and ensuring stable performance for critical services.
The AR180 series also supports Smart Mesh networking technology for intelligent, high-speed interconnection between devices, eliminating coverage blind spots. Its built-in IPSec VPN capability secures branch communication, while Application control enables time- and IP-based application access control, helping enterprises build a more efficient workspace.
Highlights:
• Support for Wi-Fi 7 technology, which is 20% faster than Wi-Fi 6
• One 2.5GE high-speed WAN port that provides ultra-gigabit bandwidth
• Coming with multiple WAN ports that enable flexible traffic steering and enhanced network efficiency and stability in diverse scenarios
• Dedicated Turbo acceleration port that prioritizes traffic for smooth video streaming and gaming
• Smart Mesh networking with up to eight devices and 20 m auto-discovery range, enabling easy deployment and full coverage

• Support for application control to accurately control network access as required
• The AR180/AR180 Plus features lossless foldable antennas with a compact and sleek design, easily fitted into compact spaces such as weak-current boxes and TV cabinets
Logitech has announced the launch of Signature Slim Solar+ K980 and Signature Slim Solar+ K980 for Business, wireless keyboards powered by any light—sunlight or artificial light—with no charging interruptions and no setup stress. Built with Logitech’s proprietary Logi LightCharge technology and designed for modern life, the keyboard features a full-size layout, laptop-style typing, and smart customizations that simplify work and personal tasks.
Signature Slim Solar+ stays charged without interruptions and is built to run for up to four months in complete darkness, so people can stay focused on what truly matters to them.
The plastic parts in the graphite version of Signature Slim Solar+ feature 70% certified post-consumer recycled plastic and include a specially designed rechargeable battery built to last up to 10 years, eliminating the need for replacement.
Signature Slim Solar+ K980 for Business is designed with IT needs in mind, with an always-on charged battery, no cable clutter, and minimal maintenance. It features a Logi Bolt USB-C receiver for secure, reliable connectivity in high-density environments. Employees can customize up to 23 shortcut keys, including the AI Launch Key, enhancing productivity without adding IT complexity.
AOC, a global leader in display technology, has announced the launch of its groundbreaking Q27G4ZD gaming monitor. Designed exclusively for the most dedicated competitors, this 27inch QD-OLED display combines the pinnacle of display innovation with e-sports performance to deliver a visually stunning and ruthlessly responsive gaming experience.
The Q27G4ZD is built around a state-of-the-art QD-OLED panel, offering a blistering 240Hz refresh rate, an incredible 0.03ms response time, and true per-pixel lighting control certified for DisplayHDR True Black 400. This monitor is engineered to provide gamers with the ultimate competitive edge.
Highlights:
• QD-OLED Panel with DisplayHDR True Black 400: Experience perfect blacks, infinite contrast, and breathtaking color with 100% sRGB and 99% DCI-P3 coverage. Quantum Dot technology ensures remarkable luminance and color purity.
• Blur-Free E-Sports Performance: An ultra-fast 240Hz refresh rate and near-instantaneous 0.03ms response time eliminates motion blur and ghosting, ensuring every frame is rendered with crystal clarity.
• Adaptive-Sync Technology: Flawless smooth, tear-free gameplay at virtually any framerate, compatible with both AMD and NVIDIA systems.
• Fully Adjustable Stand: Find the perfect ergonomic position

with height, pivot, swivel, and tilt adjustments.
• 3-Sided Virtually Frameless Design: Offers an immersive viewing experience and a near-seamless look in multi-monitor setups.
• Advanced Game Enhancements: Features like Shadow Control brighten dark scenes to reveal enemies, Dial Point provides custom on-screen crosshairs, and Game Color allows for saturation adjustment to spot finer details.
• Comfort for Marathon Sessions: Flicker-Free technology and a Low Blue Mode minimize eye strain during extended gaming sessions.
• Versatile Connectivity: Includes 2 signal inputs HDMI 2.0 and DisplayPort 1.4 input to connect to PCs and modern gaming consoles, along with a 4-port USB 3.2 Gen1 hub.
Highlights:
• Powered by Logi LightCharge: At the core of Signature Slim Solar+ is the proprietary Logi LightCharge technology, a unique power system that combines a light-absorbing strip, a long-lasting battery built to last up to 10 years, and an energy-efficient design for reliable, cable-free use.
• Thoughtfully crafted design: The slim, low-profile form creates a clean, minimalist desk setup that reduces visual clutter and complements modern laptops, monitors, and peripherals, bringing a sense of order and style to any workspace.

• Comfortable, familiar typing experience: The keyboard features a laptop-style feel, Scissor-switch keys, and a full-size layout with a number pad.
• Multi-device, multi-OS compatibility: It works seamlessly across operating systems with a multi-OS layout and allows users to switch typing between up to three devices: your work computer, home laptop, tablet, or phone, using Easy-Switch keys.
Worldwide IT spending is expected to total $6.08 trillion in 2026, an increase of 9.8% from 2025, according to the latest forecast by Gartner
“The uncertainty pause that began in the second quarter of 2025 started to alleviate in the third quarter and a significant budget flush is anticipated before the end of the year,” said John-David Lovelock, Distinguished VP Analyst at Gartner. “Despite being in the trough of disillusionment in 2026, GenAI features are now ubiquitous across software already owned and operated by enterprises and these features cost more money, aligning with this flush. The cost of software is going up and both the cost of features and functionality is going up as well thanks to GenAI.
“However, not all segments will experience this flush uniformly,” said Lovelock. “Software and services spending growth in 2025 does not recover in the same way as devices and data center systems. For instance, vertical-specific software spending has been slightly more affected, as vertical-industry-level software buyers are more sensitive to the policy changes and business uncertainties (see Table 1).”
Solid mobile phones and PCs shipment data over the first half of 2025 reported by vendors support the devices market’s strong growth projection for 2025, with spending expected to reach $783 billion in 2025, an increase of over 8.4% from the previous year. Spending on devices in 2026 is expected to be strong, but a bit slower.
“This growth in 2025 is mainly driven by stronger-than-expected spending on mobile phones,” said Lovelock. “The availability of AI devices has also boosted overall spending by more than $30 billion. With the replacement cycle unchanged, the stronger performance in 2025 will result in a lower relative growth rate for 2026, as demand has been pulled forward.
“In other areas, such as data center systems, the race to build AI infrastructure has further increased demand and growth expectations for data center servers, especially AI-optimized server racks. However, server demand growth remains limited by supply constraints,” continued Lovelock.
Source: Gartner (October 2025)


