





Data centres are now recognised as part of the UK’s Critical National Infrastructure (CNI), elevating expectations around resilience, compliance, and physical protection. Growth in AI, edge computing, and cloud services are intensifying demands on sites located ever closer to communities, while regulators and technical authorities are raising the bar on cyber-physical risk management. Crucially, data centres will now be able to opt into the Nationally Significant Infrastructure Projects (NSIP) regime, meaning that planning decisions will be made instead by the Secretary of State, allowing for a streamlined application process for data centres.
This whitepaper sets out the updated threat landscape, relevant standards, and practical design, operation, and maintenance guidance for perimeter-focused security
that is robust, aesthetic, and sustainable. It reflects current UK and global market dynamics, regulatory changes such as NIS2, and the latest innovations in intelligent monitoring, access control, and hostile vehicle mitigation.
Demand for data centre capacity continues to rise. Because data centres are not assigned a specific industrial category in the UK, assessing their direct contribution to the economy is challenging. According to techUK, UK data centres are estimated to generate around £4.7 billion in gross value added each year, a figure derived from averaged findings across several international studies.
In 2024, UK data centres were designated as Critical National Infrastructure, bringing prioritised support, coordinated incident response, and heightened expectations for resilience. Subsequent government papers and industry analysis highlight planning constraints, grid capacity, and the need for proactive site identification, especially for AI and edge facilities that favour urban or near-urban locations.
The National Cyber Security Centre reported a 16% rise in hostile cyber activity in 2024, reinforcing the need for holistic protection across physical, personnel and cyber domains. Operators of nondesignated sites should also raise their security posture, since targeting may be indiscriminate.
Uptime Institute’s 2025 analysis shows outages are becoming less frequent, but costly incidents persist. Over 54% of respondents reported their last significant outage cost more than £79,000, with 20% exceeding £790 million, underlining the business case for disciplined physical security and operations.
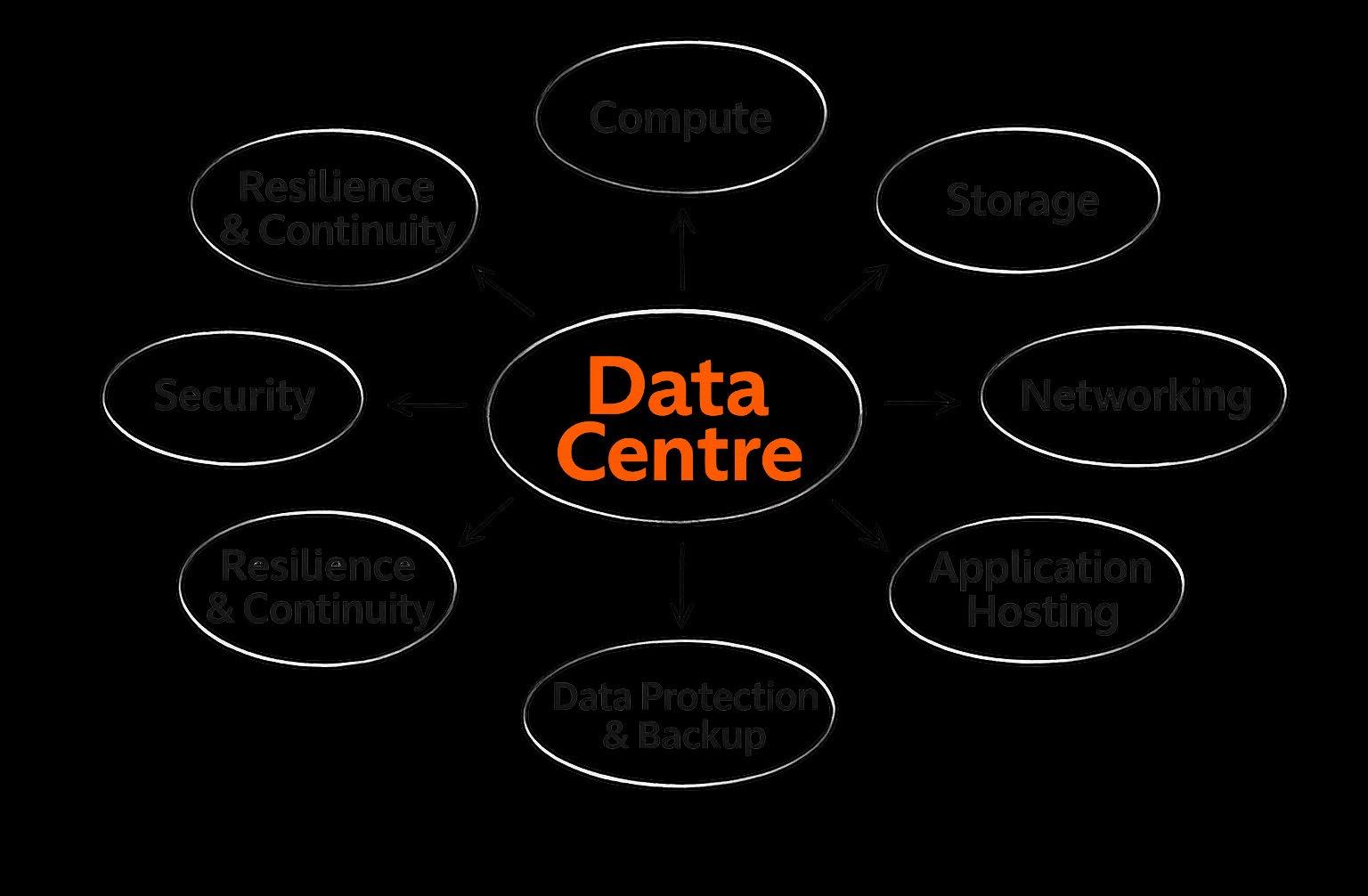
Data centres can be grouped in several ways depending on who owns them, how large they are, and what purpose they serve:
• Micro data centres: Compact, self-contained, preintegrated units that bundle IT equipment, power, cooling, and security into a single rack or cabinet, acting as scaled-down versions of traditional data centres for edge computing, remote sites, and space-constrained environments, offering rapid deployment, scalability, and localised processing.
• Modular data centres: factory-built, pre-engineered, and portable IT infrastructure solutions that provide scalable power, cooling, and compute capacity. They are designed for rapid deployment, often in weeks rather than months, making them ideal for edge computing, remote locations, and scaling existing data centres.
• Enterprise data centres: These facilities are operated directly by the organisation that relies on them. They support internal operations and are built to meet the organisation’s specific operational and governance requirements.
• Co-location data centres: A specialist provider owns and manages the building and supporting infrastructure. This includes power supply, cooling systems, connectivity, and security. Customers lease floor space or racks within the facility and install their own servers and networking hardware.
• Co-hosting data centres: Here, the data centre operator not only supplies the building and environmental infrastructure but also owns the computing equipment. Customers purchase storage and processing capacity as a service rather than installing their own IT hardware.
• Hyperscale data centres: Built to deliver vast computing power, these sites are significantly larger than conventional facilities. A single hyperscale installation can cover hundreds of thousands of square metres and require power consumption exceeding 100 megawatts. Major cloud providers, including Amazon, Microsoft, and Google, are among the primary developers. These centres are also capable of supporting demanding AI workloads due to their scale and flexibility.
• AI data centres: Purpose-built to support large-scale artificial intelligence systems. They are engineered to accommodate specialised processors, high density server configurations, advanced cooling technologies, and substantial electrical demand associated with training AI models.
• Edge data centres: Smaller facilities positioned close to users or devices in order to reduce latency. As AI-driven applications grow, these localised centres are expected to play an increasingly important role in delivering responsive services and handling data near its point of origin.
Sites in dense areas must mitigate noise from HVAC, generators, and traffic while controlling light spill and maintaining a discreet visual profile. Timber acoustic barriers can reduce sound by up to 32 dB in laboratory conditions and integrate with certified high security designs, supporting both performance and aesthetics.
Modern data centres face an evolving spectrum of vehicle-borne threats, from deliberate ramming attacks to hostile reconnaissance using modified or heavier vehicles. As these facilities increasingly underpin national infrastructure, robust HVM is no longer optional; it’s a core component of physical resilience.
Effective access control is one of the most important pillars of physical security within any data centre environment. With rising expectations around security, compliance, and operational resilience, organisations are placing greater emphasis on systems that can verify, authenticate, and monitor every individual who enters
a critical facility. A robust strategy typically includes multi-factor authentication, zoned access, activity logging and monitoring, and integration with wider security infrastructure. For non-employees who enter the data centre, Visitor Access Control Process (VACPs) provide a structured approach. Key elements include pre-authorisation, identity validation on arrival, escort policies, temporary credentials and access restrictions, and departure logging and device checks.
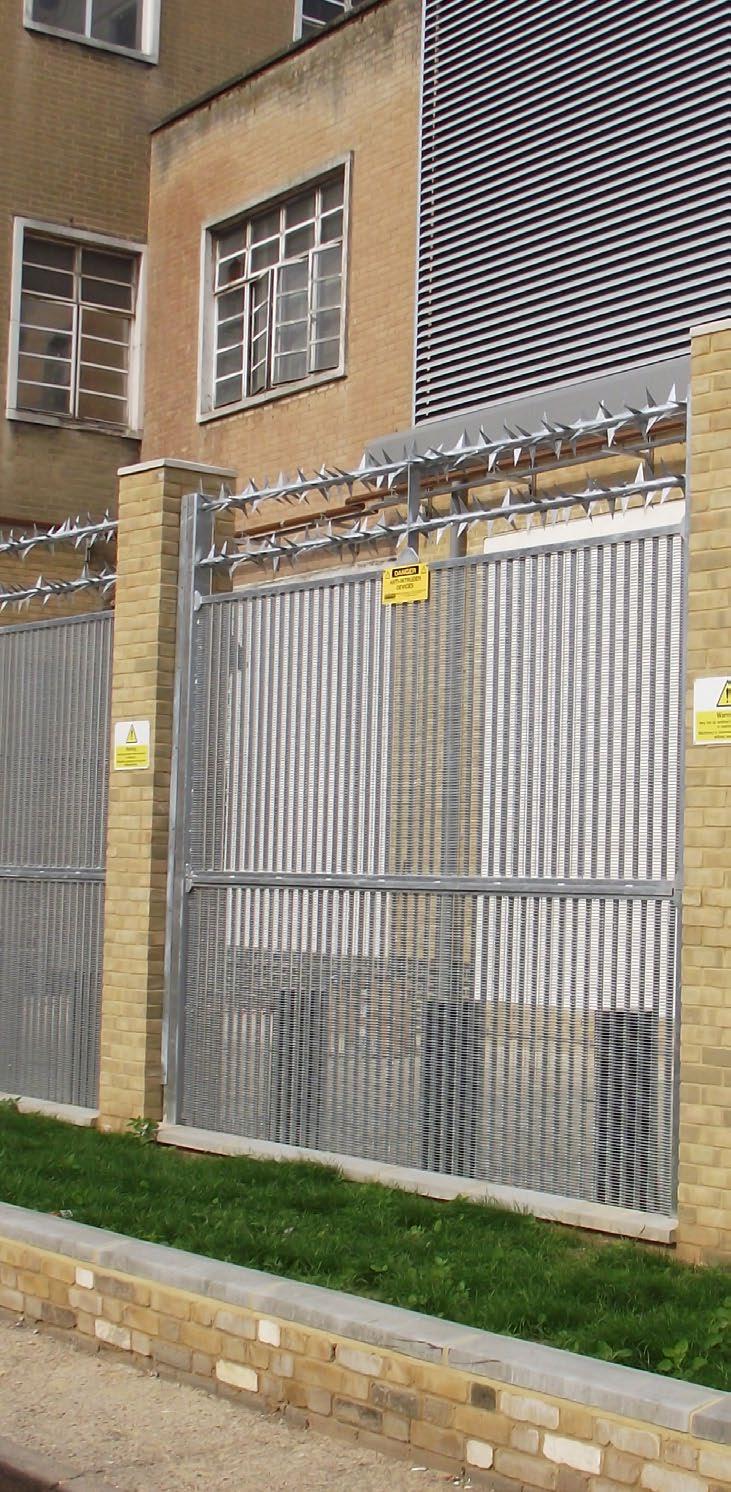
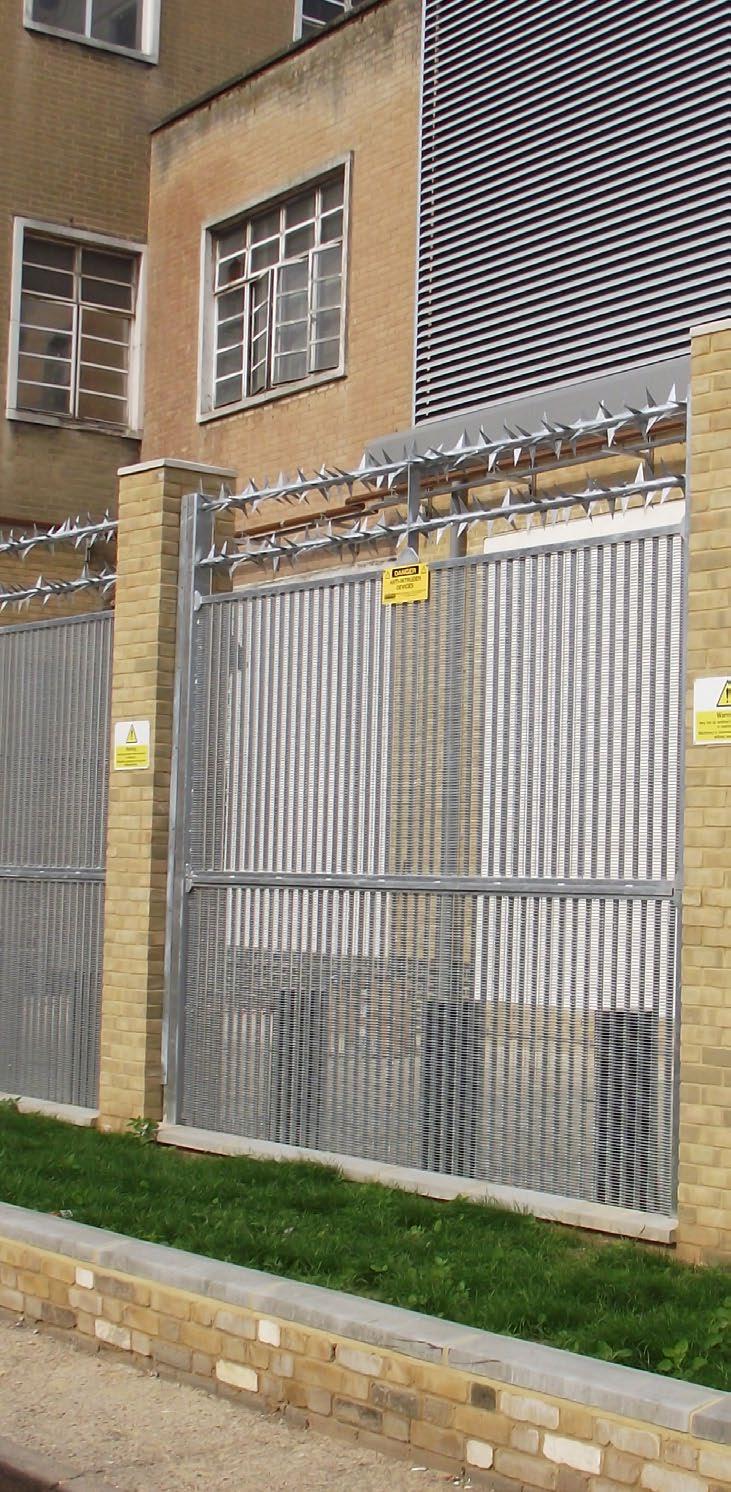
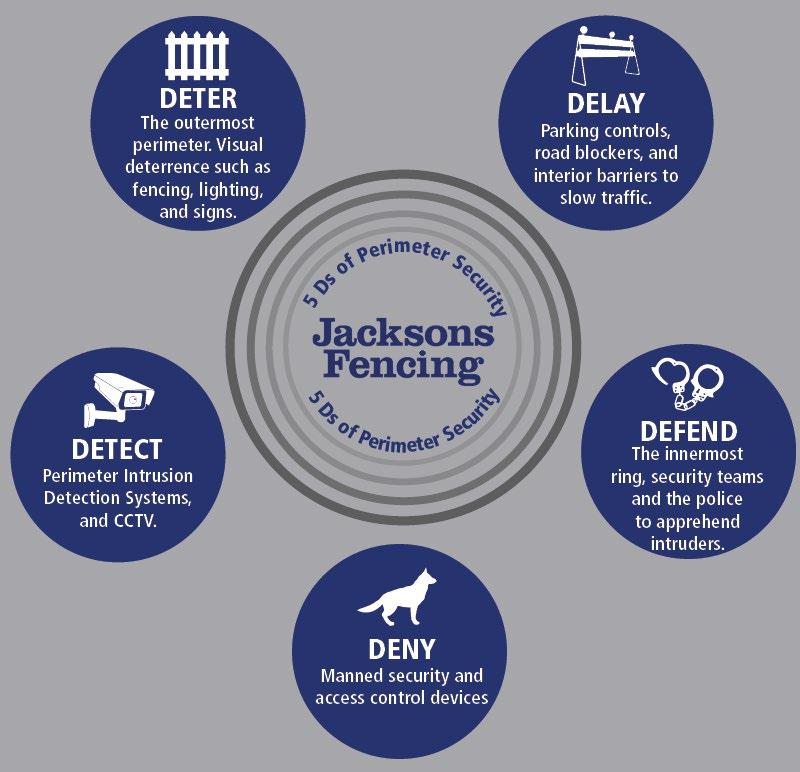
Perimeter security must anticipate covert entry, cutthrough attempts, and insider facilitation. Joint NCSC and NPSA guidance emphasises a unified strategy across physical, people, and cyber controls, spanning site geography, perimeters, data halls, and meet-me rooms.
Unified security operations and policy-led controls improve situational awareness and incident response. Leading practitioners advocate for convergence of IT, OT, and physical systems to reduce blast radius and accelerate recovery.

For years, NPSA approved fencing listed in the Catalogue of Security Equipment (CSE) was a core requirement for high assurance sites, including data centres. This long-standing framework changed significantly when NPSA confirmed that fencing and gates would be removed from the CSE from January 2026, along with the full withdrawal of its manual forced entry testing programme. Following this shift, NPSA now recommends that buyers specify perimeter products that have been independently certified to recognised forced entry standards such as LPS 1175. Importantly, Hostile Vehicle Mitigation (HVM) measures remain unaffected by this update and continue to be included within the CSE.
LPS 1175 provides rigorous forced-entry resistance classifications combining a tool category and delay time, enabling tailored specifications from A1 to H20.
It is widely used by specifiers for critical infrastructure perimeters and regularly updated to reflect evolving attack methods. Products tested to LPS 1175 help assure delay-to-entry performance. Manufacturers and specifiers increasingly reference Issue 8’s flexible combinations, with approved fencing commonly deployed at data centres and other high risk sites.
ISO 22343-1 and 22343-2 now define performance testing and application for vehicle security barriers. NPSA notes that certificates to PAS 68 and IWA 14-1 issued before March 2024 remain valid, but new tests should adopt ISO 22343.
Secured by Design remains a valuable framework for crime prevention and design quality across the built environment and is commonly referenced in high security site specifications.

As data becomes more critical to the modern economy, the potential impact of losing access increases. The government is therefore considering additional regulation to ensure data centres are resilient against issues such as cyberattacks.
While primarily a cybersecurity directive, NIS2 recognises that a digital system is only as secure as the physical environment housing it. The EU’s NIS2 Directive extends scope, strengthens accountability and requires an allhazards approach to risk management that explicitly
includes connected physical security systems, such as access control and surveillance. Operators must integrate these assets within cyber-resilient architectures and incident reporting processes.
UK data centres now benefit from prioritised government support and coordinated emergency access. While confidentiality applies to which facilities are designated, industry commentary advises all operators to enhance defences due to indiscriminate targeting.
Start with a rigorous risk assessment that considers attacker profiles, tools, time, standoff distances, local topography, utilities, and adjacent land uses. Select forced entry standards aligned with your threat model, response times, and detection capabilities.
Implement a layered design using the 5Ds, that deters, detects, delays, denies, and defends; enabling an appropriate response. Combine certified fencing, gates, and access control measures, considering anti-climb profiles, protected footings, tamper detection, and clear lines for surveillance or concealment where required. Where appropriate, integrate acoustic barriers that meet both noise and security needs.
Engineer pedestrian, visitor and vehicle entrances with rated products, controlled airlocks, and anti-tailgating.
For HVM, specify to ISO 22343 with foundations designed to test conditions, site soils and finishes, following NPSA advice on foundation realism beyond test arrangements.
Avoid advertising value. Use materials, profiles and landscaped buffers that blend into context, control light spill, and reduce sightlines to critical assets, while preserving surveillance effectiveness.
Timber and steel fencing systems with a 25 year guarantee can reduce embodied carbon while minimising maintenance burden. Where timber acoustic fencing is specified, products with forced entry standards such as LPS 1175 providing certified noise mitigation without compromising security.
The industry shift is toward intelligent automation that reduces false alarms, accelerates investigations, and augments operators. AI-assisted video analytics and intrusion detection are increasingly used to deliver outcome-focused security rather than monitoring alone.
Integrating access control, video, alarms and building systems into unified platforms improves response and resilience. Convergence between IT, OT, and physical security continues to tighten, enhancing situational awareness across multi-site estates.
Mobile credentials and biometrics are accelerating, with surveys indicating a rise in biometric use for physical access and strong preferences for unified, open platforms. This enables Zero Trust-aligned, contextaware access policies at the perimeter.
Autonomous drones and ground robots are moving from pilots to operations, providing consistent patrols, thermal and multi-sensor detection and rapid incident notification, especially in large or complex perimeters.

In the UK, powered gates are classed as machinery. Operators have responsibilities under the Supply of Machinery (Safety) Regulations and must ensure systems are safe, documented, and maintained. Regulation 18 of the Workplace (Health, Safety and Welfare) Regulations 1992 sets out safety aspects for doors and gates, and Regulation 5 requires a suitable schedule of maintenance.
Applicable standards include EN 13241 for powered doors and gates, EN 12453 for safety in use, and EN
12635 for installation and maintenance, with guidance on log books and inspection records.
Establish scheduled walk-throughs along the attack face and internal line. Check fixings, corrosion, ground shifts, foliage, and debris. Test automation, interlocks, emergency release and fail-safe modes. Record defects, prioritise remedial works, and maintain evidence for compliance.
1. Holistic risk assessment covering IT, OT, and physical layers, insider risk, and hostile reconnaissance.
2. Select certified products to LPS 1175 approvals aligned to threat and response times.
3. Specify HVM to ISO 22343 with realistic foundations and standoff distances.
4. Integrate acoustic barriers to mitigate noise and visual impact where community fit is required.
5. Adopt unified security platforms and AI-assisted monitoring for faster, more accurate response.
6. Modernise access control with mobile credentials, biometrics and contextual policies.
7. Plan for robotics and drone support on extended or unmanned perimeters.
8. Set maintenance schedules aligned to Regulation 5 and maintain log books per EN 12635.
9. Align with NIS2 obligations for connected physical systems across EU operations or supply chains.
10. Engage planners early on location, grid, fibre and environmental constraints for community-compatible designs.
The next generation of data centres will operate closer to communities, under tighter regulatory expectations and amid more complex threat dynamics. Future-proof physical security demands certified, layered perimeters that blend performance, aesthetics and sustainability, supported by intelligent operations and disciplined maintenance. Operators who integrate standards like LPS 1175 and ISO 22343, follow NPSA and NIS2 guidance, and modernise operations with unified platforms, AI and robotics will be better placed to deter, detect, delay and respond to threats without compromising community trust or business continuity.

For further information, advice or to arrange for a site visit or CPD, please contact us on 0800 41 43 43 or email highsecurity@jacksons-fencing.co.uk.
Stowting Common, Ashford, TN25 6BN
T: +44 (0) 1233 750 393 or 0800 41 43 43
E: security@jacksons-fencing.co.uk
W: www.jacksons-security.co.uk