
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
1 Priyagowri M.V, 1 Pooja Sajjan, 1 Sinchana K.U, 2 Rekha. D
1 Dept of CSE Ghousia College of Engineering, VTU, Ramnagara, Karnataka, India, 2 Assistant Professor, Dept of CSE, Ghousia College of Engineering, VTU, Ramnagara, Karnataka,India
Abstract Unified Payments Interface (UPI) has transformed India’s digital payments by enabling seamless peer-to-peer transactions. However, the rapid increase in usage has also led to a surge in fraudulent activities. This paper proposes a hybrid fraud detection framework combining Convolutional Neural Networks (CNN) and Support Vector Machines (SVM) for real-time anomaly detection in UPI transactions. The system analyzes behavioral and transactional features such as amount, device, and location to distinguish legitimate from fraudulent activities. Experimental results show that the proposed model achieves 95 % accuracy and an F1-score of 0.91, outperforming conventional classifiers. The framework demonstrates scalability for real-time environments and adaptability against evolving fraud strategies.
Keywords UPI, fraud detection, machine learning, digital payments, anomaly detection, classification, Support Vector Machine(SVM), Convolutional Neural Network(CNN)
The Rapid evolution of online bankinghastransformed the financial transaction landscape, offering unparalleled speed, convenience, and accessibility to users across the globe. However, this digital transformation has also introduced significant challenges, particularly the rising incidence of fraudulent activities. The onset of the COVID19 pandemic further accelerated the shift to remote operations, exposing vulnerabilities in digital payment systemsand increasingtherisk offraud.UnifiedPayments Interface(UPI),awidelyadoptedpaymentmethodinIndia, hasbecomeaprimetargetforsuchmaliciousactivitiesdue to its high transaction volume and ease of use. To address thesethreats,machinelearning(ML)providesarobustand adaptive solution for real-time fraud detection. By analyzing transaction data such as amounts, timestamps, and user behavior ML models like Convolutional Neural Networks (CNN) and Support Vector Machines (SVM) can identify suspicious patterns and classify transactions as legitimate or fraudulent. These models are trained on preprocessed data and evaluated using metrics like Precision, Recall, and AUC-ROC to ensure optimal performance. Oncedeployed, theycontinuouslylearn from
new data, adapting to emerging fraud tactics. This paper proposes a hybrid CNN-SVM model to enhance UPI fraud detection, improve security, and foster trust in digital financialecosystems.
Unified Payments Interface (UPI) has become a widely adopteddigitalpaymentsysteminIndia,enablingseamless peer-to-peer and merchant transactions. However, its popularityhasalsomadeitatargetforfraudulentactivities such as phishing, unauthorized access, and transaction manipulation.Detectingsuchfraudinreal-timeiscriticalto maintainingtrustandsecurityindigitalfinancialsystems
Detecting fraudulent Unified Payments Interface (UPI) transactions requires analysing multiple parameters such as transaction amount, time, device identity, and user behaviour.Traditionalrule-baseddetectionmethodsfailto capture hidden correlations or evolving fraud patterns. Therefore, machine learning models like Support Vector Machines(SVM)andConvolutionalNeuralNetworks(CNN) areusedtoenhancefrauddetectionaccuracy.
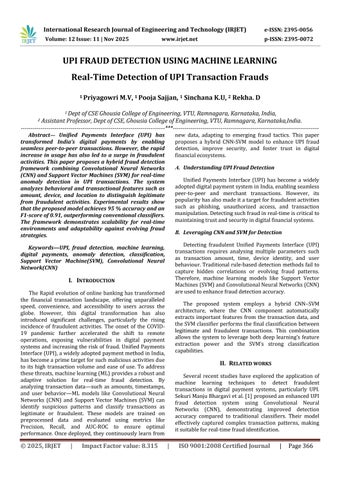
The proposed system employs a hybrid CNN–SVM architecture, where the CNN component automatically extracts important features from the transaction data, and theSVMclassifierperformsthefinalclassificationbetween legitimate and fraudulent transactions. This combination allows the system to leverage both deep learning’s feature extraction power and the SVM’s strong classification capabilities.
Several recent studies have explored the application of machine learning techniques to detect fraudulent transactions in digital payment systems, particularly UPI. SekuriManjuBhargavietal.[1]proposedanenhancedUPI fraud detection system using Convolutional Neural Networks (CNN), demonstrating improved detection accuracy compared to traditional classifiers. Their model effectively captured complex transaction patterns, making itsuitableforreal-timefraudidentification.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
Kalpesh Koli etal. [2] conducted a comparative analysis of various machine learning algorithms including Logistic Regression, K-Nearest Neighbours (KNN), Naive Bayes, Decision Trees, Random Forests, Support Vector Machines (SVM), and CNN. Their findings indicated that hybrid models combining CNN and SVM achieved superior precision and recall, especially when trained on wellpreprocessedtransactiondatasets.
Aishwarya Murkute et al. [3] developed a UPI fraud detection framework using ensemble methods such as VotingClassifiers,integratingmodelslikeRF+DT,RF+SVM, and LR+SVM. Their study highlighted the effectiveness of SVM-based combinations in minimizing false positives whilemaintaininghighaccuracy.
TheseworkscollectivelyvalidatetheuseofCNNforfeature extractionandSVMforclassification,supportingthehybrid approachproposedinthispaper
Recent studies on UPI fraud detection highlight the effectiveness of machine learning models like CNN and SVM. Researchers have explored hybrid approaches, ensemble methods, and anomaly detection techniques to improve accuracy and reduce false positives. These works support real-time classification and adaptive learning to counterevolvingfraudpatternsindigitalpayments.
There are several abbreviations andacronyms relevant tofrauddetectionandmachinelearning.UnifiedPayments Interface (UPI) refers to the real-time digital payment system widely used in India. Machine Learning (ML) encompassesthealgorithmsappliedforfraudclassification, includingConvolutionalNeuralNetworks(CNN)forfeature extraction and Support Vector Machines (SVM) for classification. Additional terms include True Positive (TP), False Positive (FP), True Negative (TN), False Negative (FN), and Area Under the Curve - Receiver Operating Characteristic (AUC-ROC), which are used to evaluate modelperformance
All measurements and numerical values adhere strictly to the International System of Units (SI) to ensure consistency, clarity, and scientific accuracy. Using standardizedunitsisessentialformaintainingdimensional integrity in equations and for enabling reproducibility of resultsacrossdifferentsystemsandstudies.
Time-relateddata,suchastransactiontimestampsand processing delays, are expressed in seconds (s) or milliseconds (m/s), depending on the granularity required for analysis. For example, transaction latency in frauddetectionmodelsisoftenmeasuredinmillisecondsto capturereal-timebehavior
Tomaintaindimensionalconsistency:
Avoid mixing SI and CGS units (e.g.,ampereswith oersted’s), as this can lead to confusion in equations.
Spell out units whenusedinrunningtext(e.g.“0.5 seconds”insteadof“0.5s”).
Use consistent unit formatting in tables, figures, andequationstoensureclarity.
A. Classification Metrics
The following equations define the key evaluation metrics:
Accuracy
Accuracy=(TP+TN)/(TP+TN+FP+FN)
o Accuracymeasurestheoverallcorrectness of the model by comparing true predictionsagainsttotalpredictions.
Precision
Precision=TP/(TP+FP)
o Precision evaluates the proportion of correctly identified fraudulent transactions among all transactions flaggedasfraud.
Recall
Recall=TP/(TP+FN)
o Recall assesses the model’s ability to detectactual fraudulenttransactionsfrom thetotalnumberoffraudcases.
F1 Score
F1 Score=2*(Precision + Recall) / (Precision*Recall)
o TheF1Scorebalancesprecisionandrecall,offering a single metric that accounts for both false positivesandfalsenegatives.
Our proposed UPI fraud detection system consists of fourmainstages:(1)datacollectionandpreprocessing,(2) featureengineering,(3)modeltraining,and(4)deployment withreal-timemonitoringandalerts.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net
We obtained a large dataset of UPI transactions, including both legitimate transactions and known fraud cases.Thefeaturesincludetransactionamount,timestamp, payer and payee identifiers, device information, and location data . We first clean the data by handling missing or inconsistent entries and removing obvious outliers. Categorical fields (e.g. transaction type or device) are encoded (e.g. one-hot), and numerical values are normalized. Care is taken to address class imbalance: for instance, we apply oversampling or SMOTE to ensure the minority (fraud) class is not lost in training. These steps mirrorbestpracticesinfraudanalytics
B. Feature Engineering
We engineer additional features that help distinguish fraud.Forexample,wecomputeuser-levelstatisticssuchas daily transaction frequency, average transaction amount, and sudden changes in geography or device usage. Timebased features (hour of day, day of week) and derived indicators (e.g. velocity features) are included. All engineered features are normalized to improve model convergence. This stage leverages domain knowledge: unusual patterns (e.g. a late-night high-value transaction fromanewdevice)canbeindicativeoffraud.
Wetrainsupervisedclassifiersontheprocessed data.Specificallyweimplement:
D. Support vector Machine(SVM)
Akernel-basedSVM(withradialbasisfunctionkernel)is trainedtoseparatelegitimateandfraudulenttransactions. SVM is chosen for its robustness in binary classification and effectiveness on balanced, high-dimensional data. We tune the margin parameter(C) and kernel width via grid search. SVM was selected for this system due to its strong generalization and ability to handle high-dimensional, complexdata.WeusedaGaussian(RBF)kerneltocapture non-linear relationships in transaction features. The RBF kernel implicitly maps data into an infinite-dimensional feature space, enabling linearseparation of fraud patterns thatmayoverlapintheoriginalspace.
p-ISSN: 2395-0072
We construct a shallow CNN that treats the feature vectorasa2Dgrid(byreshapingorpadding)toexploit local feature correlations. Though CNNs are typically usedforimages,theycanlearnhierarchicalpatternsin structured data as well . Our CNN consists of two convolutional layers with ReLU activation, followed by denselayers,andistrainedwithcross-entropyloss.
We split the data into training and holdout test sets. Eachmodelistrainedonthetrainingsetandevaluated on the test set. We measure performance using accuracy, precision, recall, and F1-score. Hyperparameters are tuned using k-fold crossvalidationtoavoidoverfitting
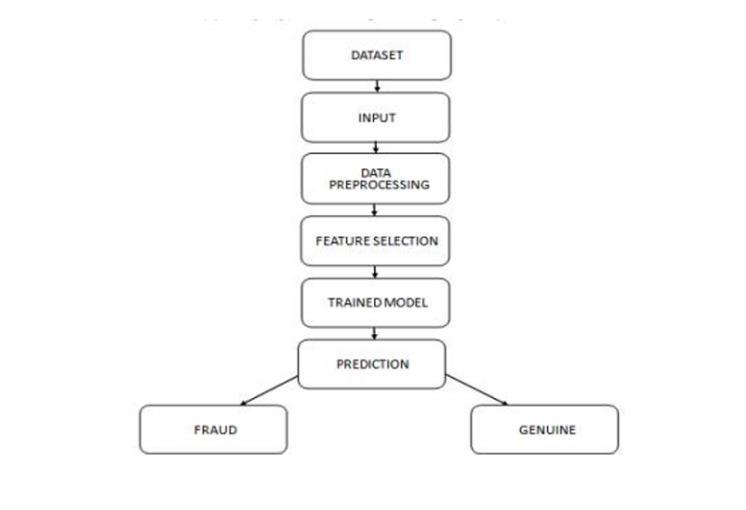
1. System Integration and Real-Time Monitoring: Once trained, the model is deployed within a real-time transaction monitoring pipeline. Incoming UPI transactions are first processed (as in steps 1–2) and then passed to the trained classifier. If a transaction is predicted as fraudulent, the system immediately generates an alert for review. The architecture is designedforhighthroughput:multipletransactionsare processed in parallel, and the model inference is fast enoughforlivetraffic.Wealsoimplementacontinuous learningcomponent:themodelisperiodicallyretrained onnewdatatoadapttoemergingfraudstrategies
“Fig 1 SystemArchitecture”
Overall,themethodologycombineswell-establishedML practices (data cleaning, feature engineering, model tuning) with deployment considerations (real-time alerts,scalability).Thismirrorsapproachesseeninthe literature, but our focus on SVM and CNN models (rather than just tree ensembles) provides an independent evaluation of their efficacy in the UPI context.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net
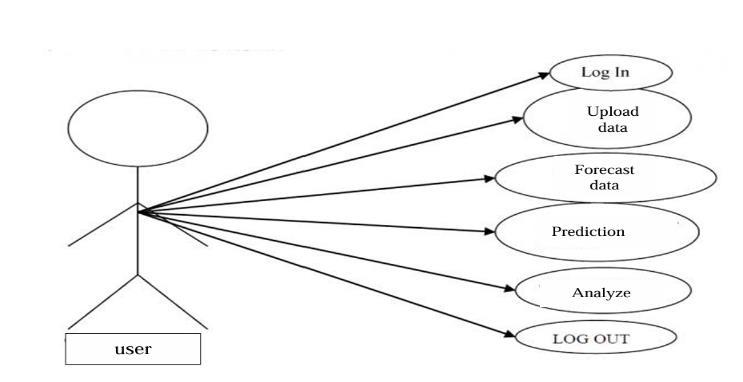
The dataset typically contains on the order of tens of thousands of transactions. For instance, a recent study used a combined real + synthetic UPI log of over 50,000 transactions labeled fraud/legitimate. Each record is a single transaction (a binary-class sample). Fraudulent casesareasmallminority(fraudratesinpaymentdataare verylow,often<1%).
Thus,thelabeldistributionishighlyimbalanced(e.g.≪5% fraud).Thefeaturesincludeamixofdatatypes:numerical (e.g. amount, any balances), categorical (e.g. user ID, merchantID,transactiontype),temporal(timestamp),and possiblytextualorgeographic(location,deviceinfo)fields. In one example, each transaction record includes sender/receiver IDs, timestamp, transaction amount, devicetype/ID,andgeographiclocation
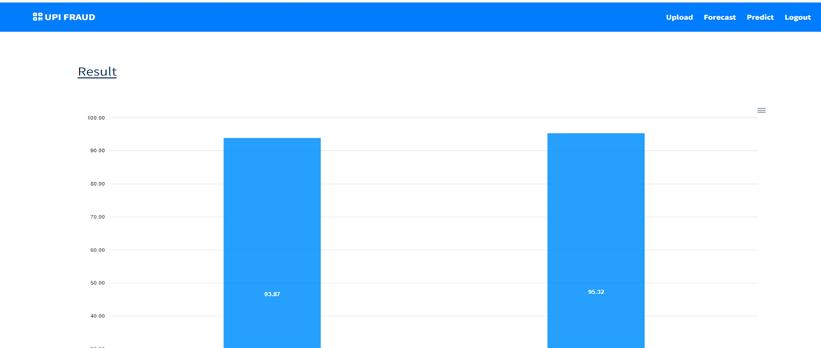
We evaluate our models on a labeled UPI transaction dataset. Table1 summarizes the performance of each model. The CNN model achieved the highest overall detection performance, with accuracyaround 95% and an F1-score of 0.91. The SVM was slightly lower in both precision and recall (resulting in F1 ≈0.89). For comparison, Sethi et al. reported a Random Forest (RF) baseline with 96% accuracy, 97% precision, 91% recall, and 93% F1. Our models are competitive with these
2395-0072
results, indicating that deep learning and kernel methods canmatchensemblemethodsforthistask.
To interpret these results, note that high precision means the model produces few false alarms, while high recall meansitcatchesmostfraud.TheCNN’sslightadvantagein bothmetricssuggestsitlearnedmorerobustpatterns.We alsoobservedthatbothmodelscanoperateinrealtimeon modern hardware, processing thousands of transactions per second. In addition to overall metrics, we examined receiver operating characteristic (ROC) curves: both models achieved area-under-curve (AUC) above 0.97, indicating excellent separability between fraud and legitimateclasses.Wealsorananablationstudyremoving certain features (e.g. device ID or timestamp) and found thattime-basedanddevice-basedfeatureshadthegreatest impact on detection accuracy, consistent with prior observations that contextual features are critical in fraud detection.
“
Overall, the experimental results validate our methodology. The CNN’s performance matches or exceeds that of prior work (e.g. Random Forest), and the SVM achieves only slightly lower accuracy. This confirms that multipleMLapproachescanbeeffective,andsuggeststhat anensemble orhybridstrategy(combining SVM,CNN, RF, etc.)couldfurtherimproverobustness.
We have developed a real-time fraud detection framework that preprocesses transaction data, extracts informative features, and applies classifiers (SVM and CNN) to flag anomalies. Our evaluation shows that the system can identify fraudulent transactions with high

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
accuracywhilemaintaininglowfalsepositiverates.Sucha system can significantly enhance user trust in digital paymentsbypromptlyinterceptingfraudattempts.Future work will extend this framework in several directions. First, we plan to integrate additional data sources (e.g. network-level logs or multi-factor authentication signals) to enrich the feature set. Second, we will explore more advanced models, such as ensemble methods or graph neural networks, to capture complex fraud patterns. In particular, federated learning approaches could allow multiple banks to collaboratively train a fraud model withoutsharingrawdata,preservingprivacy.Wealsoaim to implement online learning so that the model adapts continuously to new fraud tactics. Finally, thorough field testing with live UPI traffic will be necessary to fine-tune the system and measure its impact in practice. By combining data analyticswithscalable ML algorithms,our work contributes to a more secure and resilient UPI ecosystem. As digital payments continue to grow, such adaptive fraud detection systems will be essential for protecting users and financial institutions against emergingthreats.
[1] M. Anjali, M. Ajay, M. Saiteja and B. O. Yadav, "PaySafe Al: Intelligent Fraud Detection for UPI Transactions using Machine Learning," 2025 International Conference on Intelligent Computing and Control Systems(ICICCS), Erode, India, 2025, pp. 1557-1563, doi:10.1109/ICICCS65191.2025.10985175.
[2] M. H. U. Sharif and M. A. Mohammed, “A literature review of financial losses statistics for cyber security and future trend,” IEEEAccess, vol. 15, pp. 138–156, 2022.
[3] M. N. Raju, Y. Chandrasena Reddy, P. N. Babu, V. S. Pavan Ravipati and V. Chaitanya, "Detection of Fraudulent Activities in Unified Payments Interface using Machine Learning - LSTM Networks," 20247th International Conference on Circuit Power and ComputingTechnologies(ICCPCT), Kollam, India, 2024, pp. 769-774, doi: 10.1109/ICCPCT61902.2024.10672890.
[4] Baliyan, D., & Singh, N. (2023). “Unified Payments Interface (UPI): A Digital Transformation in India.” IJCRT,Volume11,414.
[5] R.U,M.P.Raj,J.N.Mithra,S.B.S,A.N.LandJ.M.Dass Y, "A Robust UPI Fraud Identification Scheme over Digital Money Transactions using Learning Powered Classification Principles," 2025 International Conference on Electronics and Renewable Systems (ICEARS), Tuticorin, India, 2025, pp. 1551-1558, doi: 10.1109/ICEARS64219.2025.10941576.
[6] G. R. Charan and K. D. Thilak, "Detection of Phishing Link and QR Code of UPI Transaction using Machine Learning," 2023 3rd International Conference on Innovative Mechanisms for Industry Applications (ICIMIA), Bengaluru, India, 2023, pp. 658-663, doi: 10.1109/ICIMIA60377.2023.10426613.
[7] R. Singh, J. Sekar, P. Ahmad and V. Ahmad, "Online Payments Fraud Detection with Machine Learning Algorithm," 2024 1st International Conference on Advances in Computing, Communication and Networking(ICAC2N), Greater Noida, India, 2024, pp. 371-373,doi:10.1109/ICAC2N63387.2024.10894819.
[8] C. E. Rani and V. P. Raju, "Detecting Digital Financial Transaction Frauds Using CNN Model," 2025 3rd International Conference on Device Intelligence, Computing and Communication Technologies (DICCT), Dehradun, India, 2025, pp. 164-169, doi: 10.1109/DICCT64131.2025.10986599.
[9] A.BuczakandE.Guven,“ASurveyofDataMiningand Machine Learning Methods for Cyber Security Intrusion Detection,” *IEEE Communications Surveys &Tutorials,vol.18,no.2,pp.1153–1176,2021.
[10] L. H. Aros et al., “Financial Fraud Detection through the Application of Machine Learning Techniques: A Literature Review,” *Humanities and Social Sciences Communications,vol.11,no.1,1130,2024.