
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
K. Sampath Kumar1, Shambhavi Sharma2, Pramod Kumar Jha3
1SRF, IT, CAS, DRDO, Hyderabad, India
2Scientist –‘B’, IT, CAS, DRDO, Hyderabad, India
3Scientist –‘G’, IT, CAS, DRDO, Hyderabad, India
Abstract - The widespread adoption of web-based applications, coupled with the increasingly fragmented nature of user digital footprints across multiple browsers, necessitates a robust and centralized solution for comprehensive browser activity monitoring and analysis. This paper introduces a novel system designed for securing the digital gateway capable of ingesting, processing, and analysing browser data from diverse sources like Chrome, Firefox etc... This system integrates real-time threat intelligence feeds for malicious domains and phishing URLs, categorizes web visits, and provides comprehensive analytics dashboards covering security posture, activity patterns, and cross-browser comparisons. Crucially, it incorporates a sophisticated User and Entity Behavior Analytics (UEBA) module that establishes individual user baselines and proactively flags anomalous behaviors, such as out-ofhours activity or visits during non-working periods. Through its holistic approach to browser data analysis and proactive threat detection, this behavioral analytics system empowers organizations and individuals with enhanced visibility into online activity and improved capabilities for identifying and mitigating security risks.
Key Words: Browser forensics, User and Entity Behaviour Analytics (UEBA), Threat intelligence, Web security, Data analytics, Anomaly detection...
The digital world today revolves heavily around the internet, with web browsers acting as the main gateway for work, communication,andentertainment.Thismakesbrowserdataaninvaluableresource,offeringinsightsintouserproductivity whilesimultaneouslyexposingvulnerabilitiestovariousCyberthreatssuchasphishingattacks,malware,anddataleaks.Since usersoftenswitchbetweenmultiplebrowsersanddevices,managingandsecuringthisscattereddigitalfootprintbecomesa complextaskforindividualsandorganizationalsecurityteamsalike.
Currentsolutionstendtofallshortwhenitcomestoprovidingacomprehensiveview.Toolsdesignedforspecificbrowserslack theabilitytooffercross-platformvisibility,andgeneralsecurityinformationandeventmanagement(SIEM)systemsoften struggletohandlethedetailedandvariedformatsofrawbrowserdata.Foreffectivesecurity,itisessentialtoconnectuser activitieswithknownthreatindicators,understandtypicalbrowsinghabits,andquicklydetectunusualbehaviorsthatdeviate fromthesepatterns.
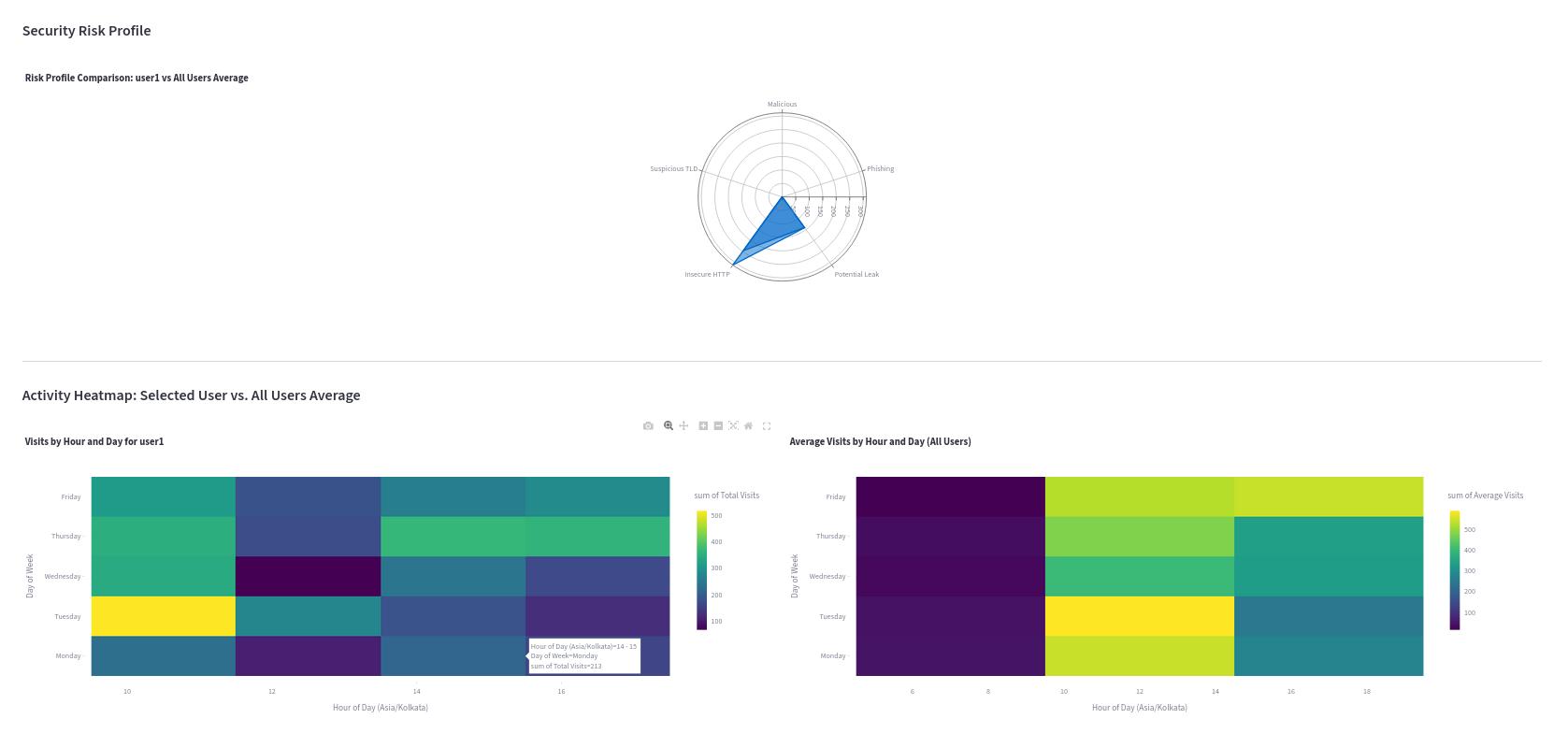
Inresponsetothesechallenges,weintroduceanovel,all-encompassinganalyticsanduserbehaviormonitoringsystemthat worksacrossmultiplebrowsers.ThissystemcentralizesdatacollectionfrompopularbrowserslikeChrome,Firefoxetc.., integratingexternalthreatintelligencesourcessuchasURLhausandOpenPhishtoidentifymaliciousandphishingURLsboth retrospectivelyandinreal-time.Italsocategorizesvisitedwebsitesintomeaningfulgroupstoenhanceanalyticalinsights.The systemfeaturesinteractivedashboardsthatnotonlyspotlightsecurityriskssuchasvisitstoharmfulsites,insecureHTTP connections,andpotentialtokenleaksbutalsoprovidedetailedviewsofuseractivity,includingpeakbrowsingtimes,visit frequencies,comparisonsamongusers,andbrowserusagetrends.
Oneofthissystem’skeystrengthsliesinitsUserandEntityBehaviorAnalytics(UEBA),whichbuildsdynamicprofilestodetect andflagabnormalbrowsingbehaviorsthatstrayfromestablishedbaselines.Thiscapabilitysignificantlyimprovestheabilityto identifythreatsproactively.Overall,thismulti-browserbehavioralanalyticsapproachoffersauniqueintegrationofdiverse browserdata,threatintelligence,andsophisticatedbehavioralanalytics,deliveringdeepvisibilityandactionableinsightsto enhancesecurity.
Researchinbrowserforensicsandwebactivitymonitoringhasseenconsiderableprogress,withvarioustoolsdevelopedto addressdifferentaspectsofthesefields.Thesetoolsgenerallyfallintoseveralcategories.First,therearebrowser-specific

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
forensictoolssuchasBrowserHistoryExaminerandForensicBrowser,alongwithcustomparsingscripts.Thesetoolsare effectiveatextractingandanalyzingdetaileddatafromindividualbrowsersbutfallshortwhenitcomestoaggregatingand correlatinginformationacrossmultiplebrowsersorusers,limitingtheirabilitytoprovideacomprehensiveoverview.
Next,webanalyticsplatformslikeGoogleAnalyticsfocusprimarilyonwebsiteperformanceanduserengagementfromthe perspectiveofwebsiteowners.However,theydonotanalyzedatastoredlocallyonbrowsersnorintegratethreatintelligence relevanttosecuritymonitoring.EndpointDetectionandResponse(EDR)andSecurityInformationandEventManagement (SIEM)solutionsoffersomemonitoringofbrowser-relatedactivitiesbuttendtoconcentrateonbroaderendpointbehavior's suchasexecutablefilesornetworktraffic,ratherthandeepanalysisofhistoricalbrowsersessions.Moreover,SIEMsystems usuallyrequiresignificantcustomizationtoparsedetailedbrowserdataandoftenlackspecializedUserandEntityBehavior Analytics(UEBA)featurestailoredtobrowsingbehavior.
NetworkIntrusionDetectionSystems(NIDS)areanothercategory,capableofidentifyingmalicioustrafficpatternsatthe networklevel.Despitetheirstrengths,NIDSdonotprovidedetailedinsightsintoindividualbrowserhistories,unflaggedHTTP sites,oruser-specificbehaviorpatterns.TraditionalUEBAsolutionsareeffectiveatdetectinginsiderthreatsandcompromised accountsbyanalyzingarangeoflogsincludingloginattempts,fileaccesses,andapplicationusage.Yet,manyofthesesystems donotintegratedeep,historicalmulti-browserdataasacorecomponentforprofilingoranomalydetection.
Ourproposedsystemsetsitselfapartbyofferingaunifiedplatformthataddressesthecomplexitiesofingestingdatafrom multiplebrowsersandcombinesitwithreal-time,integratedthreatintelligence.ItsUEBAengineisspecificallydesignedto analysegranular,user-focusedbrowsingbehaviour.Thisapproachenablesustodetectsubtleanomaliesthatmightbemissed whendataisfragmentedacrossdifferenttoolsorsources,providingamuchmorecomprehensiveandactionablesecurity perspective.
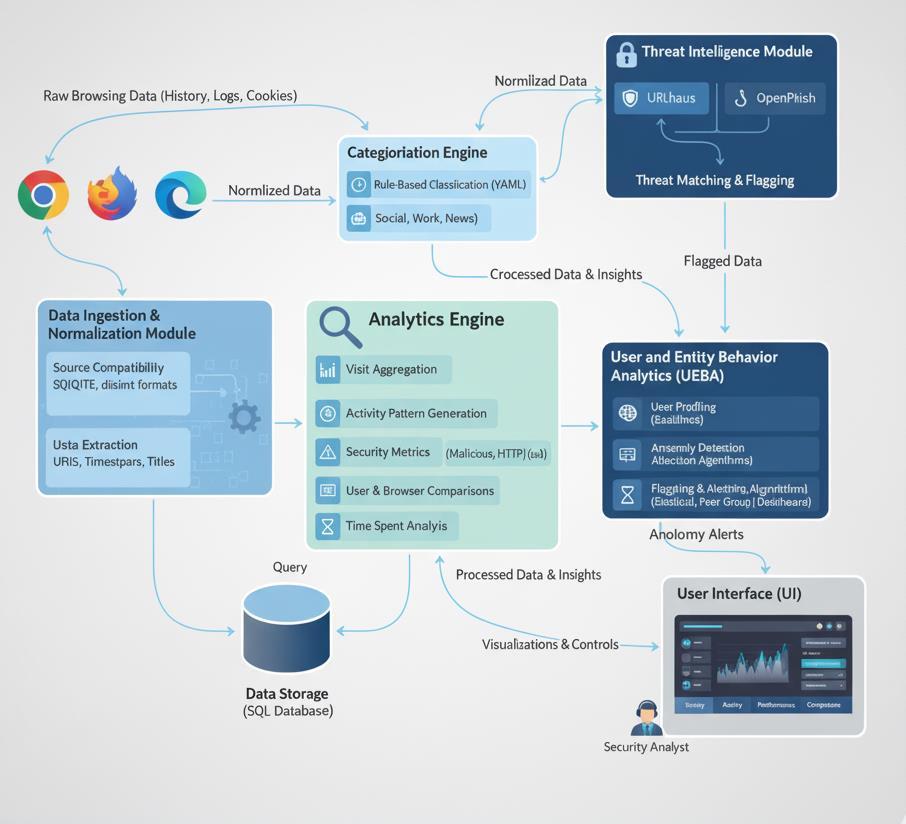
Ourproposedsystemiscomposedofseveralinterconnectedmodules,designedforscalabilityandmodularity.Thehigh-level architectureisdepictedbelow.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
Thismoduleisresponsibleforcollectingandprocessingrawbrowsingdatafromvarioususerbrowsers.
Source Compatibility: SupportsmajorbrowsersincludingGoogleChrome,MozillaFirefoxandpotentiallyothers.It handlestheirdistinctdatabaseformats.
Data Extraction: Extracts critical information such as visited URLs, timestamps, visit durations, tab titles, and potentiallydownloadhistory,searchqueries,andcookiesdependingonconfigurationandprivacyconsiderations.
Normalization: Converts disparate browser data into a standardized schema for consistent processing by downstreammodules.Thisincludesuniformtimestampformats,URLparsing,anduseridentification.
3.2. Threat Intelligence Module
Toproactivelyidentifyknownthreats,thesystemintegratesandmaintainsup-to-datethreatintelligencefeeds.
Feed Integration: AutomaticallyloadsandupdateslistsofknownmaliciousdomainsfromsourceslikeURLhausand phishingURLsfromOpenPhish.Thesefeedsareregularlyrefreshedtoensureaccuracyagainstevolvingthreats.
Threat Matching: Duringdataprocessing,eachvisitedURLischeckedagainsttheseloadedmaliciousandphishing lists.Apositivematchimmediatelyflagsthevisitasasecurityincident.
3.3.
Understandingthecontextofwebvisitsiscrucialforbehavioralanalysis.
Rule-Based Classification: UtilizesaconfigurableYAML-basedrulefiletoclassifyURLsintopredefinedcategories.Eachrule canemployregularexpressionsorkeywordmatchingagainstURLpatternsordomainnames.
Dynamic Application: Categorizationoccursafternormalizationandbeforedetailedanalytics,enrichingthedataset withcontextualmetadata.
3.4. Analytics Engine
Thismoduleperformsthecoredataprocessingtoderiveactionableinsights.
Visit Aggregation: Calculatestotalvisits,uniquedomainsvisited,andaveragevisitdurationperuser,perday,andper browser.
Activity Pattern Generation:Identifiesbusiestdaysoftheweekandbusiesthoursofthedayonaverageacrossall usersorindividually.Calculatesaveragenumberofvisitsperday.
Security Metrics: Quantifiesthenumberofvisitstomalicioussites,phishingsites,andinsecureHTTP-onlysites.Italso identifiesURLsthatmayrepresentpotentialtokenleaks.
User and Browser Comparisons: Facilitatesdirectcomparisonsofbrowsingpatterns,securityrisks,andcategory usagebetweendifferentusersandacrossdifferentbrowsers.
Time Spent Analysis:Calculatescumulativetimespentonsiteswithinspecificcategories,brokendownbyuseror acrossallusers.
3.5. User and Entity Behavior Analytics (UEBA) Module
Thisistheintelligencecoreofour,designedtodetectanomaliesindicatingpotentialinsiderthreats,compromised accounts,orpolicyviolations.
User Profiling: Foreachindividualuser,thesystemestablishesabaselineof"normal"behavior.Thisprofileincludes typicalworkinghours,commoncategoriesvisited,averagedailyvisitcounts,andusualactivitypatternsonspecificdays.
Anomaly Detection Algorithms:
o Rule-BasedAnomalies:Flagspredefinedsuspiciousactivities(anybrowseractivityonholidaysoroutsideof establishedworkinghourslike9AM-6PM).
o Statistical Deviation: Usesstatisticalmethods(e.g.,standarddeviation)toidentifysignificantdeviations fromauser'sestablishedbaselineformetricslikevisitcount,duration,orunusualcategoryaccess.
o Peer Group Analysis: Comparisonofauser'sactivityagainstapeergroupwithsimilarrolesordepartments toidentifyoutliers.
Flagging and Alerting: Whenananomalyisdetected,itraisesa flag,providingdetailsabouttheuser,thespecific activity,andthereasonfortheflag,empoweringsecurityanalyststoinvestigatefurther.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
Arobustdatabasestoresthenormalizedbrowserdata,threatintelligencefeeds,categorizedvisitdata,andgeneratedanalytical insights.Thisensuresefficientqueryingandhistoricalanalysis.
3.7. User Interface (UI)
TheUIprovidesanintuitive,tab-baseddashboardforvisualizingallgeneratedanalyticsandUEBAalerts.
Tabs: Dedicated sections for "Security," "Activity Patterns," "Categorization," "Browser Comparison," and "UEBA Alerts."
Visualizations:Employsavarietyofchartsandgraphstomakecomplexdataeasilydigestible.
The multi-browser behavioral analytics system is primarily implemented using Python due to its rich ecosystem of data processingandvisualizationlibraries.
[1] Data Parsing: CustomparsersforSQLitedatabases(usingsqlite3)areemployedtoextractdataefficientlyfromvarious browserstorageformats.
[2] Threat Intelligence Management:BasicfileI/Oforloading(usingos,shutil,pathlib)andpotentiallyrequests.
[3] Database Interaction: sqlite3forPythonmanagesdatastorageandretrieval.
[4] Analytics and UEBA: pandasfordatamanipulation,numpyfornumericaloperations,andpotentiallyScipy/Scikit-learn areinstrumentalinperformingcalculationsandanomalydetection.
[5] User Interface: Theweb-basedUIisbuiltusingStreamlittoensureinteractivityandrichvisualizations.plotly.expressis usedforgeneratingthevariousgraphs.
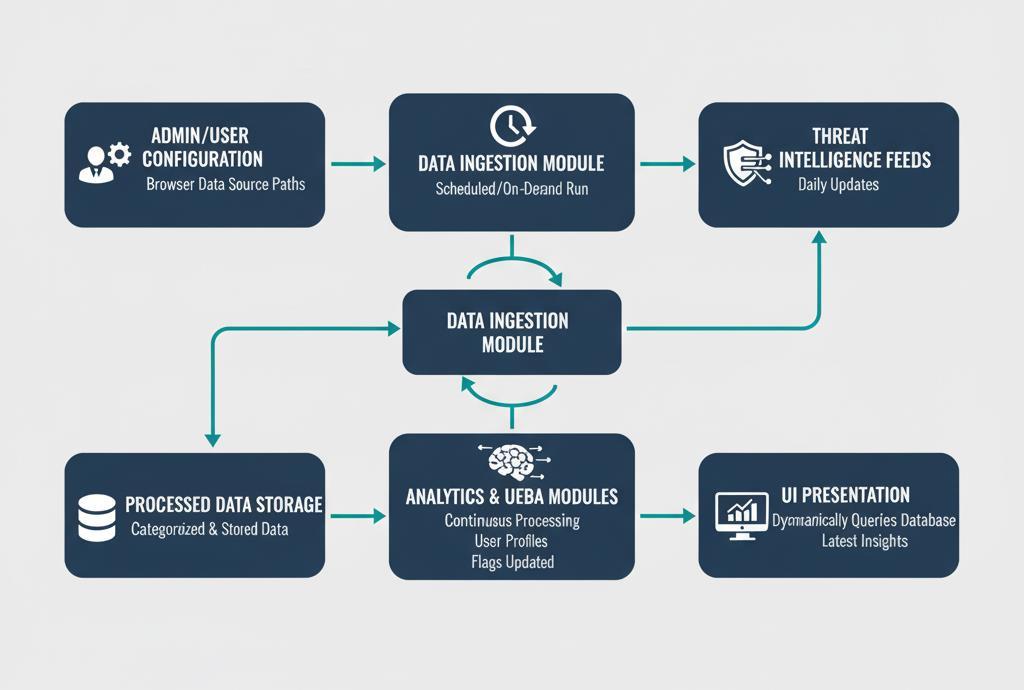
Atypicalworkflowinvolves:
1. Admin/userconfiguresbrowserdatasourcepaths.
1. DataIngestionmodulerunsatscheduledintervalsoron-demand.
2. Threatintelligencefeedsareupdateddaily.
3. Processeddataiscategorizedandstored.
4. AnalyticsandUEBAmodulescontinuouslyprocessnewdataandupdateuserprofiles/flags.
5. TheUIdynamicallyqueriesthedatabasetopresentthelatestinsights.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
5.1. Threat Detection Performance
The system successfully identified Potential Credential Leaks and Unencrypted (HTTP) Connections attempts within the dataset.
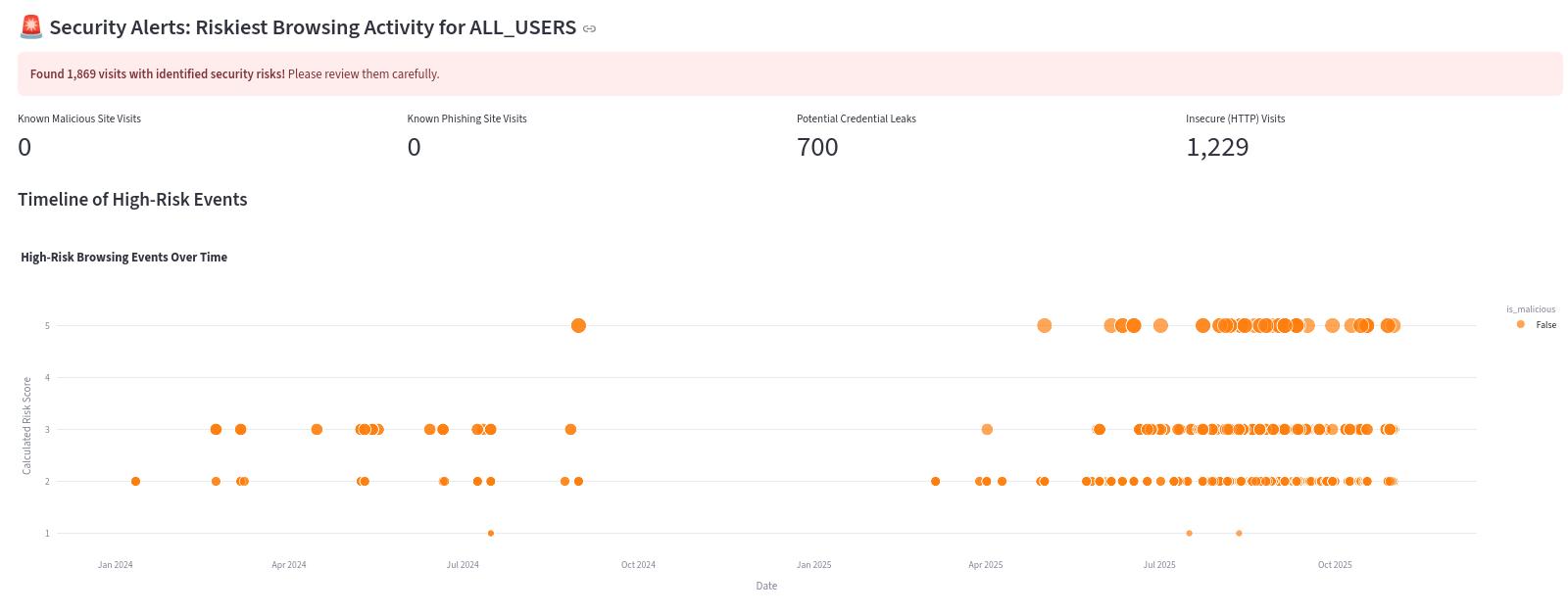
5.2. Activity Pattern Insights theanalyticsdashboardprovidedclearinsightsintoaggregatedandindividualuserbehavior.
Busiest Days/Hours:AnalysisrevealedthatFridaysbetween16PMand17PMwereconsistentlythebusiestbrowsing periodsacrossallusers,aligningwithtypicalworkschedules.
Average Visits: Usersaveraged128.1visitsperday,withnoticeablepeaksandtroughscorrespondingtoObserved patterns
Browser Comparison: Chromeaccountedfor42.5%and67.5%ofallvisitsandchromewasusedprimarilyforpersonal browsing,illustratingdistinctusagepatterns.


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
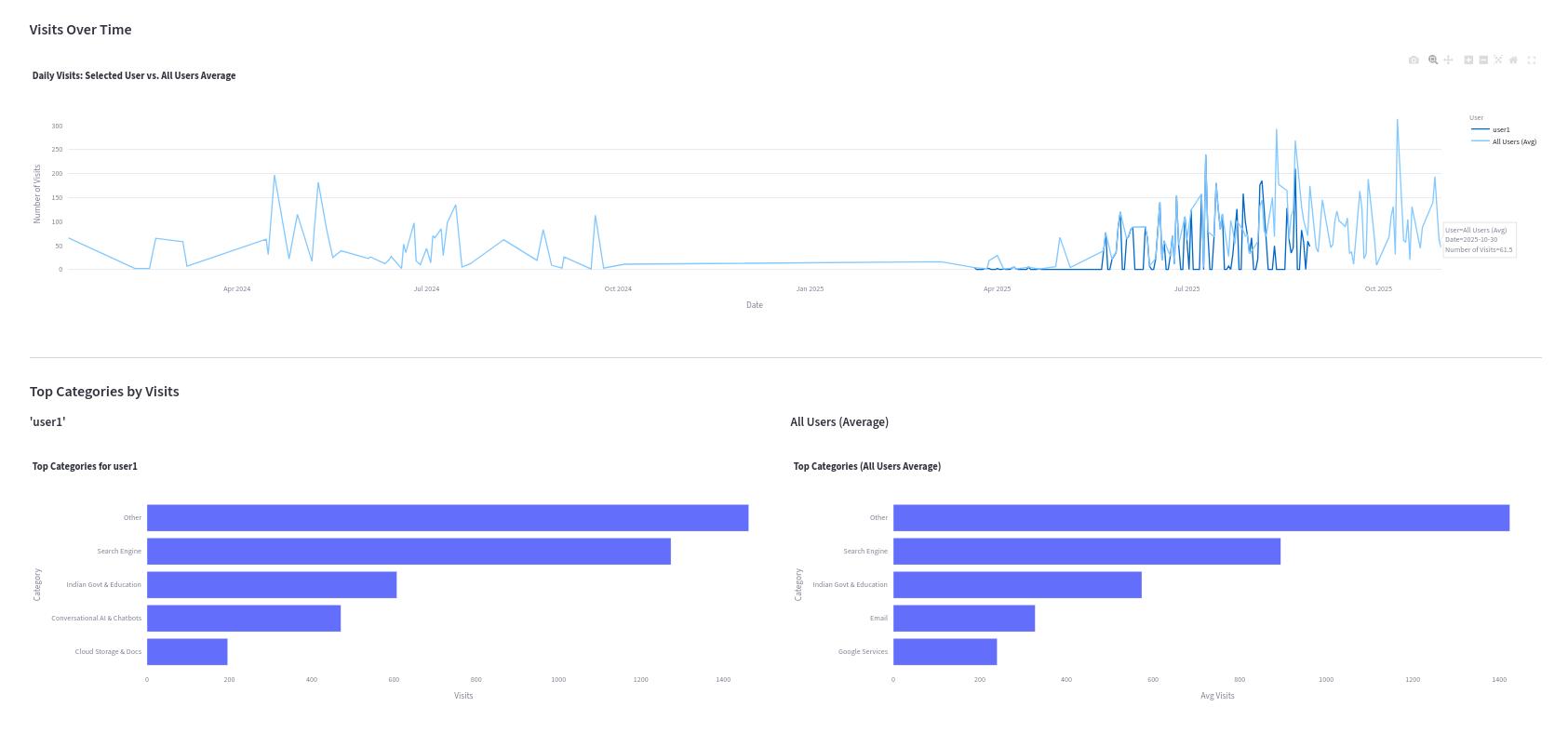
Theseresultsshowitscapabilitytotransformrawbrowserdataintoactionablesecurityintelligence,detectingbothknown threatsandsubtlebehavioralshifts.
Thismulti-browserbehavioralanalyticssystemdeliversacomprehensiveandunifiedviewofbrowseractivitythatgreatly strengthensanorganization’ssecuritycapabilitieswhileprovidingvaluableoperationalinsights.Bybringingtogetherdata fromvariousbrowsersandenrichingitwithreal-timethreatintelligence,thesystemaddressesasignificantshortcomingfound inmanyexistingsecuritytools.
OneofitsstandoutfeaturesisitsUserandEntityBehaviorAnalytics(UEBA)module,whichgoesbeyondtraditionalstatic,rulebaseddetectionmethods.Instead,itintelligentlybuildsprofilesofuserbehavior,enablingthedetectionofsubtleanomalies thatcouldsignalinsiderthreats,accountcompromises,orviolationsoforganizationalpolicies.Forexample,thesystem’sability toflagunusualactivitiesoccurringoutsideofregularworkinghoursorduringholidaysdemonstratesapracticalandeffective approachtoproactivemonitoring.
However,thesystemdoesfacesomelimitations.Handlingsensitivebrowserdatarequiresstrictcompliancewithprivacy regulationssuchasGDPRandCCPA,meaningstronganonymizationmeasures,accesscontrols,andcleartransparencypolicies mustbeinplace.Whilethissolutionisdesignedforenterpriseenvironments,scalinguptoaccommodatemillionsofusersor

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
extremelylargevolumesofdatamaynecessitatemoredistributedprocessingframeworkslikeApacheSpark,whicharebeyond itscurrentarchitecture.Thesystem’seffectivenessalsodependsonthequalityandcoverageofexternalthreatintelligence feedsdealingwithzero-daythreatsremainsachallengethatcallsforfurtheradvancementinbehavioralanalytics.Additionally, supportingawidevarietyoflesscommonbrowserswouldrequireongoingdevelopmentandmaintenanceefforts.
Despitethesechallenges,thismulti-browseranalyticsapproachremainsapowerfulandflexibletoolfororganizationslooking togainin-depthvisibilityandleverageadvancedbehavioralanalyticsacrosstheirbrowsingenvironments,helpingthemstay aheadofevolvingCyberthreats.
Inthispaper,weintroducedamulti-browseranalyticsanduserbehaviormonitoringsystemdesignedforsecuringthedigital gatewayandaddressingthe complexchallengesofwebsecurityandactivityinsight. Byintegratingdiversebrowserdata sources,leveragingreal-timethreatintelligence,providingrichanalyticaldashboards,andimplementingasophisticatedUEBA module,itoffersasignificantadvancementinproactivesecurity.Itsabilitytoidentifymaliciousactivity,mapuserbehavior patterns,andflaganomalousdeviationsfromestablishedbaselinesempowerssecurityprofessionalswiththetoolsneededto safeguard their digital environments against evolving threats. This approach transforms fragmented browser data into a unified,intelligent,andactionablesourceofsecurityintelligence.
Thesystemcouldfocusonaddingreal-timemonitoringthroughstreamingdatapipelinestoenableimmediatedetectionand alertingofsuspiciousactivities.EnhancingtheUEBAmodulewithadvancedmachinelearningtechniques,suchasunsupervised anomalydetectionandsequenceprediction,couldimprovetheaccuracyofbehavioralprofiling.Integrationwithothersecurity toolslikeSIEMsandSOARplatformswouldhelpcreateamoreseamlessandautomatedsecurityecosystem.Expandingdata sourcestoincludenetworktraffic,DNSqueries,andendpointtelemetrycouldproviderichercontextforanalysis.Introducinga feedbackloopforsecurityanalyststoreviewflaggedanomaliesmayhelprefinedetectionmodelsovertime.Lastly,exploring proactive policy enforcement via browser extensions or endpoint agents could allow for automated responses to risky behavior.Thesedirectionsofferpromisingopportunitiestomakethismulti-browserbehavioralanalyticssystemmorerealtime,intelligent,andintegrated.
9. ACKNOWLEDGMENT:
WesincerelythankDrNSivasubramaniam,DS&DirectorCAS,forhisvaluableguidanceandunwaveringsupportinupholding cybersecuritycompliance.OurheartfeltgratitudegoestoShri.PraveenTandon,Scientist-’G’forhisconstantmotivation.We alsoappreciateourteammatesfortheirongoingsupportthroughouttheprocess.
10. REFERENCE:
[1]URLhaus.(n.d.).URLhaus:MalwareURLExchange.Retrievedfromhttps://urlhaus.abuse.ch/ [2]OpenPhish.(n.d.).OpenPhish-FreePhishingURLFeed.Retrievedfromhttps://openphish.com/ [3]Chandola,V.,Banerjee,A.,&Kumar,V.(2009).Anomalydetection:Asurvey.ACMComputingSurveys(CSUR),41(3),158.
[4]Harris,C.R.,Millman,K.J.,vanderWalt,S.J.,Gommers,R.,Virtanen,P.,Cournapeau,D.,...&Oliphant,T.E.(2020).Array programmingwithNumPy.Nature,585(7825),357-362.
[5]McKinney,W.(2010).DataStructuresforStatisticalComputinginPython.Proceedingsofthe9thPythoninScience Conference,51-56.