
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
Anish Mathew Architect, DMI (Digital Management Inc.), Headquarter: McLean, Virginia, USA
Abstract - Thewidespreadadoptionofmobiletechnologies, such as smartphones, tablets, wearables, and Internet of Things (IoT) devices across organizations, has transformed both operational and security landscapes into their core nature. The rise of remote working, adoption of bring-yourown-device (BYOD) policies, and mobile-first strategies have introduced new attack vectors, thus necessitating advanced, responsive,andscalablesecuritysolutions.Whileconventional Mobile Device Management (MDM) solutions have been effective, they often lack contextual intelligence and the capability to adapt to the continuously changing corporate environment.MobileDeviceManagement(MDM)isasoftware solution or platform that allows organizations to manage, secure, enforce corporate policies, meet regulatory requirements,andgovernmobiledevicesusedbyemployeesin a corporate or workplace environment. While it offers basic policyenforcementandprovisioning,itfaceslimitationsfrom evolving threats in the form of phishing, ransomware, zeroday exploits, and insecure applications. The introduction of Artificial Intelligence (AI) has emerged as a strong catalyst, elevating MDM solutions to intelligent, self-learning, and proactive mobile security systems.
This manuscript provides a comprehensive examination of artificial intelligence-driven methodologies pertinent to mobile security within enterprises, encompassing predictive threat analytics, behavioral modeling, anomaly detection, real-time automated responses, and autonomous policy enforcement. Furthermore, it explores the underlying architecture, practical applications, challenges, and prospective avenues for organizations seeking to implement AI-based Mobile Device Management as an essential component of their digital transformation strategy.
Key Words: Mobile Device Management (MDM), Artificial Intelligence (AI), Enterprise Mobile Security, Threats (or Evolving Threats), Anomaly Detection, Security Solutions, Digital Transformation, Mobile Devices, Policy Enforcement
Mobile phones have become central to today's digital workplaces, allowing employees to access, process, and transmit confidential organizational information from almostanyremotelocation([2]).Theaccelerateduptakeof mobile-firstapproachesandBYODpolicieshasexpandedthe enterprise threat landscape, subjecting organizations to a myriadofsecuritythreatslikedataleakage,devicehijacking,
phishing,insecuremobileappuse,andsophisticatedmobile malware ([3],[4],[5]). These issues are compounded in hybridandremoteworkspaces,wherecentralizedsecurity controlstendtobelimitedinscopeandresponsiveness.
Mobile Device Management (MDM) systems traditionally havebeenacorebuildingblockformobiledevicesecurityin the enterprise, offering capabilities such as remote wipe, policyenforcement,andcompliancemonitoringofdevices ([6],[7],[8]).However,asthreatsbecomemoresophisticated and enterprise mobile environments grow in size and complexity, traditional MDM solutions increasingly are found lacking ([9],[10]). The use of static policies, manual control, and reactive responses limits their ability to successfully counter dynamic and contextually aware threats.
To overcome this imbalance, the integration of Artificial Intelligence (AI) into Mobile Device Management (MDM) solutions is being undertaken to enable predictive and adaptive mobile security. AI-powered MDM systems leverage risk analysis, machine learning algorithms, and behaviouralanalyticstodetectanomalies,analysecontextual risks,andtriggerautomatedremediationmeasuresinreal time([12]).ThisinnovationtransformsconventionalMDM intoanadvanced,self-adaptive,andanticipatorysystemthat notonlyelevatestheefficacyofcybersecuritybutalsouser experienceandoperationalproductivity.
The ecosystem of enterprise mobility has experienced hypergrowth over the past several years, driven by bringyour-own-device(BYOD)practices,cloud-nativeworkflows, andthespreadofremoteworkingenvironments.Although mobile devices provide unmatched flexibility and productivityimprovements,theyalsocreateanexpandinglist ofsecuritythreatsthattheenterpriseisnotwellpositioned tocounter([3],[4],[5]).
One specific subset of threats arises from phishing and smishing (SMS phishing) attacks, which take advantage of humanmistakesbyusingtrickerymessagestoeithersteal credentials or convey malware. Such social engineering attackscontinuetobeoneofthemostsuccessfulinitialaccess vectorsinenterprisecompromises,particularlywhenpaired with credential reuse and untrusted mobile apps ([14]). Ransomware and mobile-specific malware now highly

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
advancedandpolymorphic representasignificantthreatto organizationaldataintegrity,frequentlyattackingendpoint vulnerabilities and taking advantage of weak or tardy patchingcycles([13]).
Mobile devices are also commonly subject to man-in-themiddle(MITM)attacks,especiallyoverunsecuredpublicWiFinetworks,enablingadversariestointerceptormodifydata intransit.Zero-dayvulnerabilities,whichmaybeexploited priortovendorspushingpatches,anddataleakagethreats fromunvettedthird-partyapps oftencircumventingmobile application management policies altogether further complicatetheenvironment.Physicalthreatssuchasdevice theft and unauthorized access contribute to the attack surface, with adversaries attempting to exfiltrate sensitive corporateinformationstoredlocallyorcachedbyenterprise applications([2]).
Toalleviatethesedifficulties,companieshavetraditionally usedMobileDeviceManagement(MDM)platformstoassert centralizedcontrolovercorporateendpoints.Conventional MDM products provide a range of functionalities, such as device enrollment, remote lock and wipe, OS update management, app policy enforcement, and compliance reportingforregulatoryorinternalgovernancerequirements ([6],[7],[8]).ThesetoolsenableITadministratorstomonitor device posture and guarantee consistent configuration of heterogeneousdevicefleets.
Yet,theshortcomingsofconventionalMDMsolutionshave become more pronounced in dynamic, heterogeneous enterpriseenvironments.Tobeginwith,theyusuallywork with fixed policies that are devoid of the contextual awarenessnecessarytokeepupwithchanginguserbehavior, likeregularchangesinworklocations,devices,andnetworks ([9],[10]).Suchinflexibilitycompromisestheirefficiencyin remote work, mobile-first cultures where user behavior is difficulttoanticipate.
Second,legacyMDMsolutionsneedtobemanagedmanually, imposing substantial demands on IT staff who need to constantly monitor telemetry, examine threats, and tune policiesbyhand oftenafterabreachhastakenplace.This speaks toa larger problem: a reactive security stance that slowsdownthreatresponseandfailstoprovidethereal-time agilityrequiredtokeepupwithtoday’scyberattacks.
In addition, legacy MDM does not have substantial user behavioral insight and device context. Devoid of mature behavioralanalyticsormachinelearningalgorithms,these platformsarenotabletodifferentiatebetweenlegitimateyet anomalousactivityandgenuinethreats.Thisnotonlyhinders threat detection but also false positives and operational inefficiencies([3],[4]).Lastly,asbusinessesexpandmobile operations, MDM platforms tend to experience scalability bottlenecks failingtoensureperformanceandconsistency acrossthousandsofdistributedendpoints([16],[17],[18]).
While traditional Mobile Device Management (MDM) solutionsoffervital functionalitytoenablemobilesecurity and enforce policies, they fall short in terms of their capabilitytoforeseeandcounterthesophisticatedthreatsof today.Thisshortcominghaspavedthewayforintegrating artificial intelligence (AI) and machine learning (ML) into mobile security frameworks, ushering in a new era of adaptive, intelligent, and contextual enterprise mobility management.
The incorporation of Artificial Intelligence (AI) and MachineLearning(ML)withinMobileDeviceManagement (MDM) systems represents a seminal advancement in enterprise mobile security. With increasing complexity in mobile environments and dynamically evolving threats, conventionalrule-basedsecuritymodelslacktheabilityto provide timely and adaptive defines. AI-powered MDM solutions, on the contrary, present a paradigm shift transitioning from reactive enforcement to predictive, behaviour-centricthreatmitigation([9],[10],[12]).
One of the core innovations in this field is detecting anomaliesviauserbehaviouranalysis.Artificialintelligence modelscontinuouslylearnfromnormaluserbehaviourby examining multiple inputs, including application usage patterns, network activity, screen interactions (including swipe patterns and typing speeds), and contextual data about devices ([13]). When the system recognizes a deviationfromtheselearnedbehaviours,suchasabnormal applicationaccessatunusualtimesorunexpectednetwork routing, it classifies the incident as a potential security threat. Such context-aware anomaly detection algorithms enablethreatstobeidentifiedmorequicklycomparedwith conventionalstaticpolicychecksandsignificantlyreduces thefrequencyoffalespositives([5]).
Complementing this ability is the use of predictive risk scoring, whereby artificial intelligence platforms amalgamateinputsfromhistoricalbehaviourprofiles,device health metrics, and real-time threat intelligence feeds to assign a dynamic risk score to all devices or sessions ([6],[7],[8]).Thescoresenableaccurateandadaptiveaccess control decisions. For instance, a device that has been assignedahigh-riskscoremaybetemporarilyblockedfrom connectingtocorporateVPNsorsensitivedatastores,while a low-risk device is allowed to continue uninterrupted operations. This risk-centric model of access control fits squarely within the Zero Trust methodology that is being widelyadoptedacrossenterpriseinformationtechnology.
Besides,behaviouralbiometricsprovidesanon-intrusive, continuousauthenticationlayerbyscrutinizingphysiological andbehaviouralcharacteristicsspecifictoindividuals.These comprise keystroke dynamics, gesture navigation, touch pressure,and evendevicehandling behaviour([19]).This

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
informationenablesthesystemtodifferentiatebetweenthe authenticuserandanimposter,evenifthevalidcredentials have been submitted. This method has been found to be extremely useful for account takeover prevention and detecting insider threats in real-time ([13]).
Another essential role of AI-driven MDM is automated remediation.Afterariskoranomalyhasbeendetected,the system can launch mitigation measures automatically isolatingthedevicefromthenetwork,revokingcredentials or VPN access, initiating OS-level rollback, or enforcing temporary lockout ([16],[17],[18]). These measures are taken with near-zero latency, significantly minimizing the timeframewithinwhichanattackercantakeadvantageofa breacheddevice.
Underlying these functions is the core mechanism of machine learning that continually optimizes system performance based on experiential learning. Machine learningmodelscontinuouslyadapttonewuserbehaviours, changing threat environments, and organizational policy changes.Theycanrecommendbetterpolicyconfigurations, identify gaps in security deployment, and automate compliance procedures such as patch management and encryptionenforcementonlargenetworksofdevices.
Inconclusion,AI-drivenMDMsolutionsembodyamove towardautonomous,adaptive,andresilientmobilesecurity systems. Through learning from users' behaviour, dynamicallyevaluatingrisk,andimplementingautomated response, they dramatically improve an organization's capacity to safeguard sensitive information in everdistributedandmobile-firstworkingecosystems.
Table -1: KeyFeatures
Feature Description
Autonomous Device Configuration
Real-Time Threat Mitigation
Behavioral Biometrics
Self-Healing Devices
AIalgorithmsautomaticallyconfiguredevice settings suchasencryption,VPNprofiles,and accesslevels basedonuserrole,historical behavior,anddeviceprofile([9],[10]).
AI-poweredsystemsintegratethreat intelligencefeedsandbehavioralanalyticsto proactivelydetectandblocksuspicious activitiesinrealtime([12]).
AIcontinuouslymonitorshowusersinteract withdevices,e.g.,typingrhythm,gesture dynamics,apptransitions todetect unauthorizedaccessoranomalies([13],[19]).
Thesystemidentifiesmalfunctions, misconfigurations,orsuspiciousstatesand autonomouslyresolvesissueswithoutmanual ITintervention([16],[17],[18],[5]).
Policy Optimization Machinelearningmodelsassessusagetrends andriskfactorstocontinuouslyrefineand personalizesecuritypoliciesforindividualsor departments([6],[7],[8],[9],[10]).
Context- AIdynamicallyadjustsaccessrightsbasedon
AwareAccess Controls contextualdatasuchasgeolocation,timeof access,devicehealth,andnetwork trustworthiness([12]).
Transitioning from Traditionalto AI-Enhanced MDM Deployment in an Automotive Enterprise
Inamid-sizedautocompanywithroughly400to500mobile endpoints,consistingofaheterogeneousgroupofiOSand Android smartphones as well as tablets a traditional Mobile Device Management (MDM) solution was initially deployed to establish baseline governance on its mobile landscape.Theconventionalsolutionprovidedrudimentary features such as device enrollment, policy compliance scanning, operating system updates, application lifecycle management,andsecurityenforcement.
Evenasitofferedimportantadministrativemanagement,the system'soperationsmodelwasyetverymanualandreactive inapproach.ITadministratorshadtomanuallylogintothe MDM console in order to initiate activities such as patch delivery,softwareupgrades,andremediationprocesses(e.g., locating,locking,orerasingstolenorcompromiseddevices). All these laborious procedures inevitably produced high operationallatencyandinefficiencies.Forinstance,critical OSpatchinstallationsweretypicallydelayed,withdevices temporarily exposed to known vulnerabilities. Further, compliance scanning necessitated proactive IT personnel follow-uptoidentifyandcorrectnon-compliantmachines, usuallyonanad-hocbasis.
Securityresponse-speaking,itcouldtakeseveralhoursafter the fact to enact device lockdown or data wipe remotely becausehumaninterventionwasrequired.Aseffectiveasit wasforlightweightmonitoring,themodelwasn'tdesigned with the range, flexibility, and intelligence necessary to effectivelycounternewmobilethreatsonthefly.Lackingin thecalculationwereautomatedthreatdiscovery,behavioral anomaly detection, and dynamic policy adjustment capabilitiesnowviewedasderigueurduetothenatureof mobile-firstbusinessoperations.
To counter such limitations, the company evaluated and deployed an AI-powered MDM solution designed to consolidatepredictiveanalytics,autonomousremediation, andcontinuousriskmonitoring.Thenewsystemsupported predictivepatchmanagement,whereinvulnerabilitieswere identifiedandpatchedproactivelydependingonbehavioral patternsandthreatintelligence.Thecapabilityofreal-time threatdetectionallowedtheplatformtoinitiateautomatic actions such as device quarantine, access revocation, or credential invalidation without needing administrator approval.
Moreover,AI-enforcedcompliancehelpedtogreatlyreduce administrativeburdensofmonitoringcompliancemanually,

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
enabling dynamic policy enforcement according to contextual factors like device location, usage, and risk profiles.
For the IT organization, it meant removal of duplicative console-levelworkandredirectionofresourcestohigherorder planning and innovation. Organizationally, the AIenhanceddeploymentofferedmeasurableimprovementsin securityposture,incidentmanagementresponsetime,and
scalability positioning the enterprise to handle future growthinitsmobilebusinessmoreefficiently. This case underscores the actual benefits of adopting AIbasedMDMsystemsincommercialenvironmentsseekingto balance mobility with resilience, agility, and proactive securitymanagement.
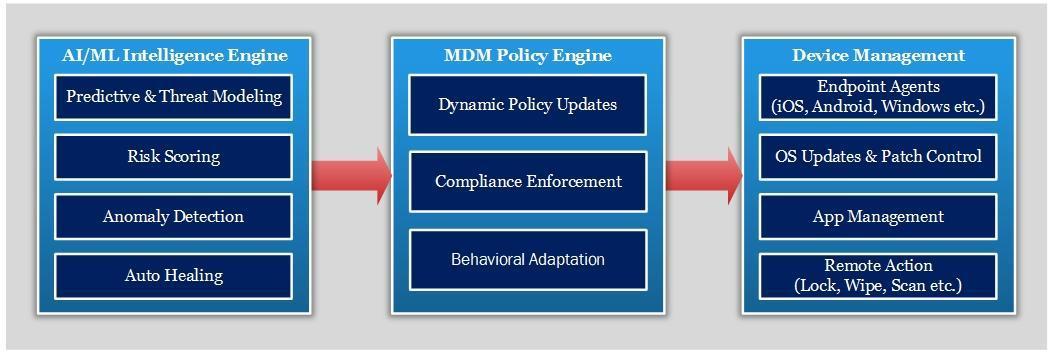
The architecture of an AI-powered Mobile Device Management (MDM) threat protection module is typically structuredintothreefunctionallayers.Eachlayerperformsa series of unique responsibilities, facilitating modularity, scalability, and real-time responsiveness for enterprise mobilesecurityprocesses.
Thefoundationlayerisresponsibleforgatheringtelemetry datafrommanagedmobileendpoints.Theseinclude but arenotnecessarilylimitedto userauthenticationattempts, application usage statistics, app installation logs, network trafficflows,sensorreadings,andgeolocationinformation. Thesedatastreamsarerequiredsothatbehavioralbaselines can be constructed as well as contextual risk assessment enabled ([13]). Telemetry data is collected in real time or near-real time using secure, encrypted communication channels, usually leveraging protocols such as TLS in conjunctionwithtoken-basedauthenticationschemessuch asJWT.
Located in the middle of the system, this level employs advancedmachinelearning(ML)andartificialintelligence (AI)algorithmsforthreatidentificationandriskprediction.
Commonapproachesaretime-seriesforecastingforthreat prediction([19]),supervisedclassification(suchasRandom Forests,XGBoost),andanomalydetection(suchasthrough IsolationForestorOne-ClassSVM).Themodelscontinuously process andconsumetelemetry data to generate dynamic threatscores,detectanomaliesfromtypicalbehavior,and predictprobablecompromiseevents.TheAIenginecanalso ingest threat intelligence feeds from the outside world to constructsituationalawarenessandadapttonewthreats.
Drawinginspirationfromlessonsgeneratedbytheanalytics layer,thepolicyenforcementmoduleappliesautomatedor semi-automated security measures. These include device quarantine, revocation of access tokens, app blocking, remote wipe of data, or sending for manual analysis to a Security Operations Center (SOC). Enforcement is done throughpre-definedpolicyenginesthatcommunicatewith the underlying MDM foundation through APIs and administrative SDKs ([12]). The detection-to-enforcement latencyisminimizedinordertooffertimelycontainmentof threats.
Several enterprise-grade MDM platforms support this architecturepatternthroughrobustAPIintegrationandAI extensibility.
Someoftheprominentplatformsinclude:

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
MicrosoftIntune–OffersGraphAPIandintegration withMicrosoftDefenderforEndpointandSentinel.
VMwareWorkspaceONE–OfferspolicyAPIsand UEMintegrationwithVMwareCarbonBlack.
IBMMaaS360–ComeswithWatsonAIforcontextual threatintelligence.
IvantiNeurons(previouslyMobileIron)–Offersrealtimepolicyorchestrationandanomalydetection capabilities.
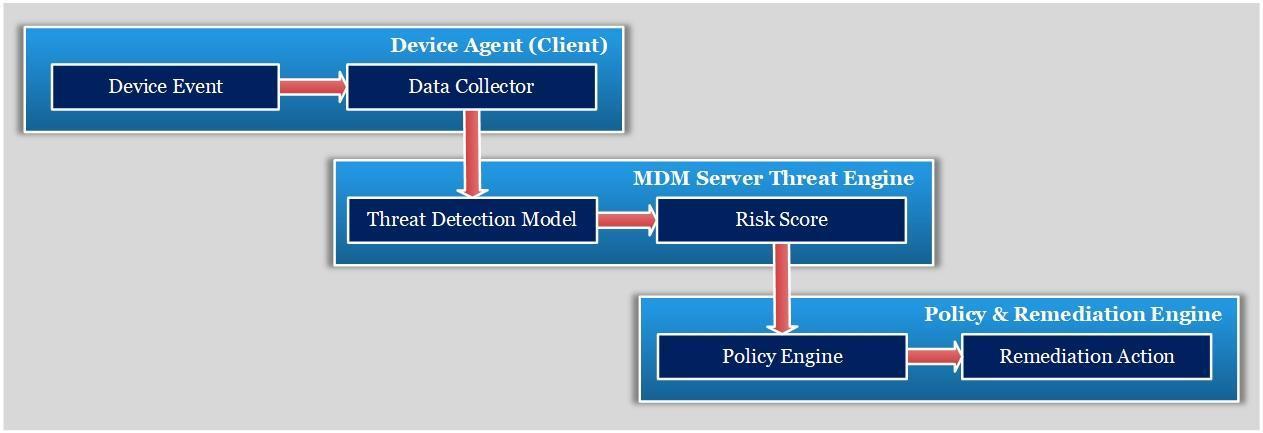
TheproposedAI-drivenMobileDeviceManagement(MDM) systemiscomposedofthreeprimarysystemcomponents: (1)theDeviceAgent,(2)theMDMServerThreatEngine,and (3)thePolicyandRemediationEngine.Thecombinationof thesethreecomponentsprovidescontinuousdatacollection, real-time threat analysis, and automatic security enforcementacrossenterprisemobileenvironments.
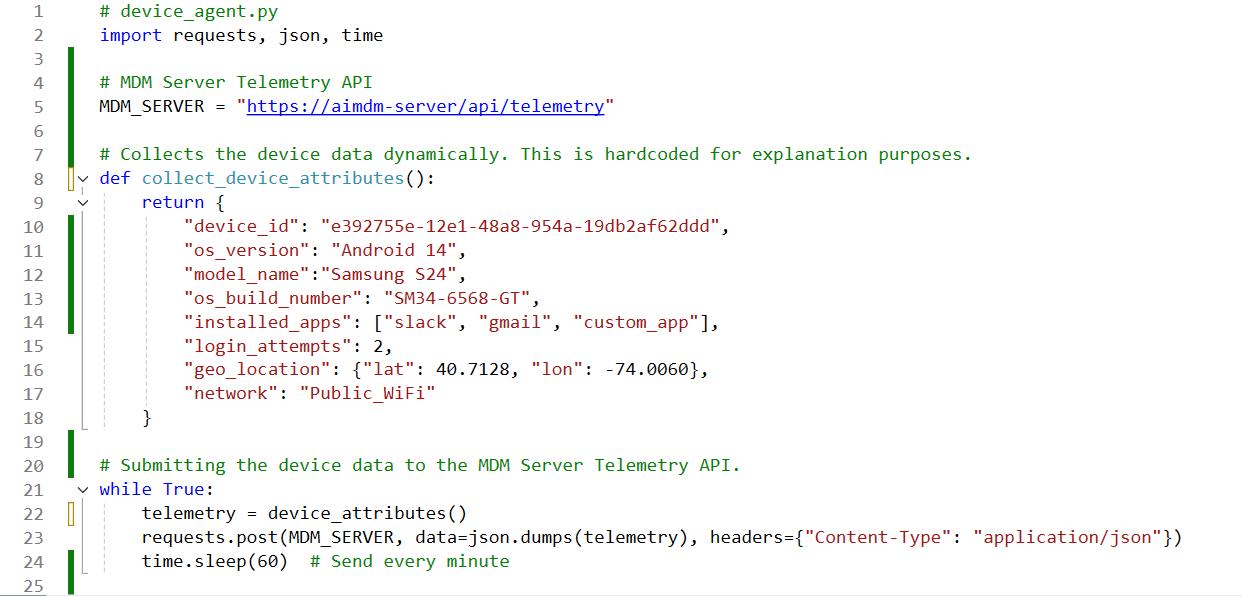
The Device Agent executes endpoint devices with mobile operatingsystemssuchasiOSandAndroid.Itistheprimary telemetry collector, constantly scanning and logging behavioral and contextual data. The agent can capture detailed points such as application usage patterns, geolocation,deviceposture,screeninteractionbehavior,and network state ([13]). Such data is provided to the MDM server through end-to-end encrypted communication channels, typically using TLS 1.3 in addition to authentication methods such as OAuth 2.0 or JWT for protectionagainstintegrityandconfidentialitybreaches.
The client-side agent is designed to be resource-friendly, leveragingbackgroundexecutionpoliciesandOS-nativeAPIs forreal-timedatacapturewithoutimpedingperformanceor deviceuserexperience.Itmayalsoleverageon-devicepreprocessing or edge inference in hybrid edge-cloud implementationstoreducelatencyforhigh-prioritythreat indicators.
Theseplatformsarearchitecturallywell-positionedforthe incorporation of AI-driven threat protection workflows, therebyenablingenterprisestotransitionfromrule-based security postures to dynamic, intelligence-based security frameworks.
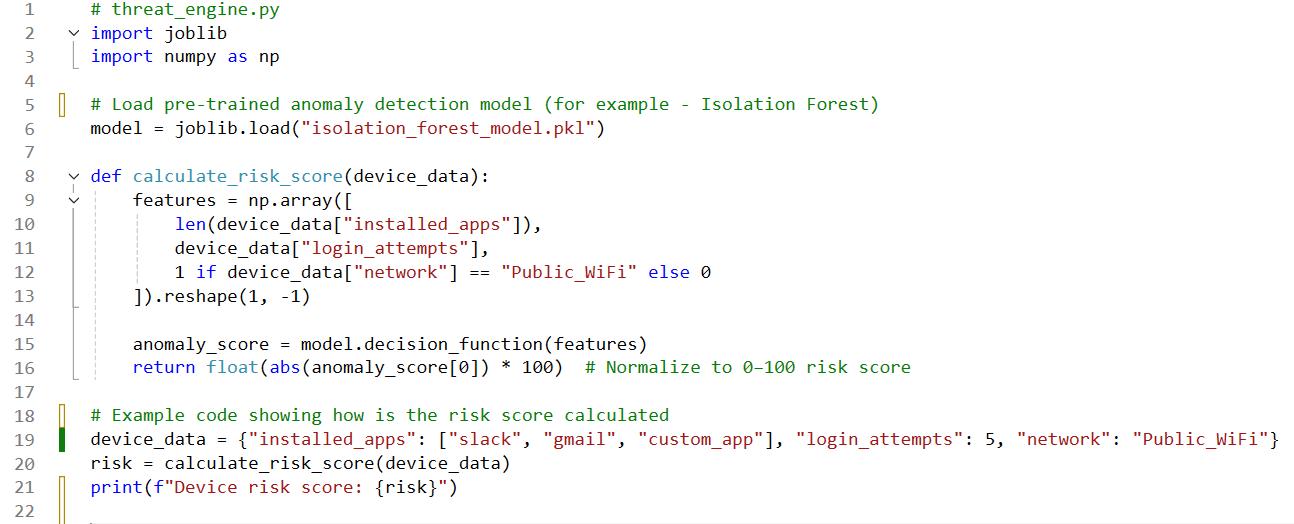
TheMDMThreatEngineisthecoreanalyticalsub-systemon the server side, responsible for examining the received telemetrydatafromdispersedendpoints.Itembedsmachine learning (ML) models trained with huge amounts of historicalthreatdatasets,enablingittorecognizeabnormal behavior, issue dynamic risk scores, and predict probable securitybreachesinrealtime([19],[12]).
Thethreatengineisarchitectedtoaccommodatebatchand streamprocessingarchitecturestoprovideresponsiveness and scalability. Anomaly detection models (e.g., Isolation Forest, LSTM networks) are applied to detect deviations from baseline user behavior, while risk score models consider a blend of environmental, behavioral, and contextual information. The output from this layer is forwardedtotheenforcementmoduleforremediableaction.
Policy and Remediation Engine is the enforcement component of architecture. Upon receiving high-risk indicatorsfromtheThreatEngine,itappliespre-configured oradaptivesecuritypolicies.Enforcementmeasuresinclude remotedevicelock,selectiveorfulldatawipe,revocationof access tokens, app quarantine, and conditional access limitations.
It is fully integrated with enterprise Identity and Access Management (IAM) solutions such as Azure Active Directory or Okta and Security Information and Event
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072 © 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
Management (SIEM) systems to provide an end-to-end responseworkflow.Integrationenablescross-matching of threat intelligence in real-time, centralized logging, and automationofincidentresponseprocesses([16],[17],[18]).
Data Collection
The three-level system architecture with its modularity enables mobile security enforcement to be proactive and dynamic in nature, utilizing AI in order to close the gap betweenthreatdiscoveryandresponseimplementationin distributedenterprises
ExamplecodewheretheclientagentsendstelemetrytotheMDMserverperiodically.
TheexamplecodedepictsusingAI/MLtogenerateadynamicriskscoreforeachdevice.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
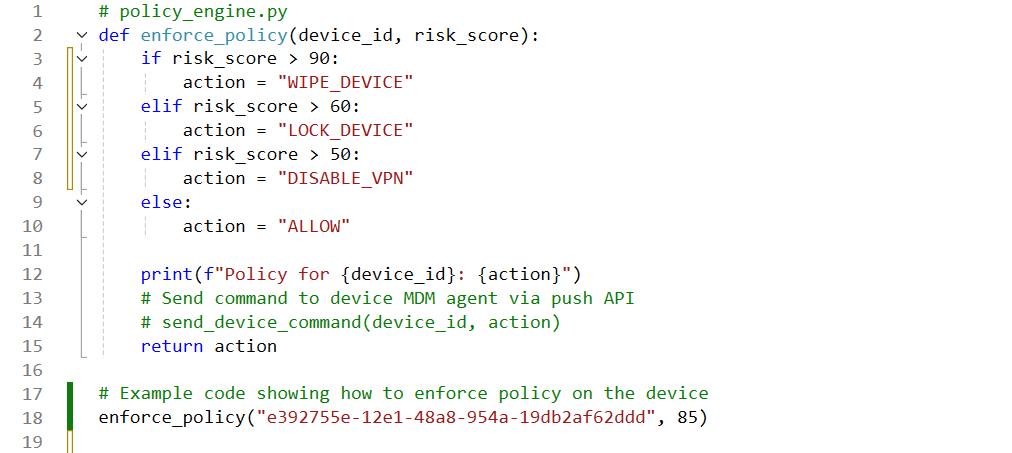
Policy Enforcement Engine
ExamplecodethatautomaticallyappliespoliciesbasedonAI-generatedriskscore.
CreatingasuccessfulAI-basedMobileDeviceManagement (MDM)systemisamulti-aspectprocessthatmustbehigh performance, secure, interpretable, and scalable. The technicalconsiderationslistedbelowarethefoundationsfor developinganddeployingsucharchitecture.
Thetelemetryinformationcollectedfromendpointmachines needs to be secured, particularly because the information comprisessensitivebehavioralindicators,deviceidentifiers, and geolocation metadata. To ensure both confidentiality andintegrity,telemetrymustbetransmittedoverencrypted streams using Transport Layer Security (TLS), preferably version 1.3, in combination with next-generation authenticationmechanismssuchasJSONWebTokens(JWT). This collectively ensures secure mutual authentication, eliminatesman-in-the-middleattacks,andenablesstateless authorizationmechanismsthatplayakeyroleindistributed MDMarchitectures.
Theselectionofmachinelearning(ML)algorithmsdirectly influences the accuracy of detection, latency, and interpretability of the system. In the case of anomaly detectionunsupervisedtasks suchasidentifyingunusual userbehaviorordeviceactivity,IsolationForestsarefound to work effectively due to their efficiency and low false positiverates(Liuetal.,2008).Forsupervisedclassification, extreme Gradient Boosting (XG Boost) offers superior predictiveperformanceand scaling,makingitsuitablefor
risk scoring or malicious activity classification on large devicefleets([1]).
To conserve inference latency and network bandwidth, selected threat detection procedures can be deployed ondevice by using Edge AI techniques. This involves the deploymentoflight-weightMLmodelsorinferenceengines attheveryendpointonthemobile(e.g.,throughTensorFlow Lite or Core ML). Edge AI facilitates real-time anomaly detectionorcontinuousbehavioralauthenticationwithout theneedforround-tripcommunicationtotheserver.Such configurations are highly valuable in low-connectivity situationsorwhererapidresponseisnecessary([19]).
Atscale,MDMsystemsmustprocessandingesttelemetry from thousands of concurrently active devices. These demands decoupled, event-driven architecture through distributedmessagequeuingsuchasApache Kafka.Kafka delivers high-throughput fault-tolerant data ingestion pipelinesandhorizontalscalabilityoftheAIanalyticsengine ([6],[7],[8]). It’s publish-subscribe paradigm allows downstream analytics, persistence, and integration with threatdetectionmodulesandSIEMsystems.
Becauseofthehypersensitivityaroundautomateddecisionmaking and privacy of data, all AI-driven action device quarantine, revocation of access, or imposition of compliance mustbefullyauditable.Alldecisionsmustbe loggedalongwithrelevantmetadataliketimestamp,model version,inputfeatures,andresultingaction.Thisimmutable storageinfrastructurenotonlysupportsinternalauditsbut

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
complianceaswellwithindustrystandardssuchasGDPR, HIPAA,andNIST800-53([3],[4]).Suchtraceabilityiscritical
Example Technology Stack
ClientAgent:Kotlin(Android),Swift(iOS)
ServerFramework:PythonFastAPIorNode.js
AIModels:Scikit-learn,TensorFlow,orPyTorch
Database:PostgreSQLorMongoDBfortelemetry
MessageQueue:Kafkaforreal-timeeventstreaming
Policy Enforcement: REST APIs or MDM push notifications(APNs,FCM)
3.5 Benefits of AI-Powered MDM in Enterprise Security
Table -2: BenefitsofAIPoweredMDM
Benefits Description
ProactiveThreat Mitigation Detectandstopattacksbeforeimpact
AdaptiveSecurity Continuouslyadjustsprotectionbasedon real-timerisk
Operational Efficiency Reducesadminworkloadthrough automation
EnhancedUser Experience Personalized,non-intrusivepolicy enforcement
Comprehensive Visibility UnifieddashboardwithAI-insightsacross devicesandapps
CostSavings Optimizeddatausage,fewerdevice replacementsduetopredictive maintenance.
3.6 Implementation Challenges and Considerations
Table -3: ImplementationChallengeswithAIPoweredMDM
Challenge Description
DataPrivacy& Ethics Collectingbehavioralandbiometricdata raisesGDPR,HIPAAissues.
ModelBias MLmodelsmayinheritbiasesfromtraining data.
Explainability DecisionsmadebyAIneedtobe interpretableforaudits.
Integration Complexity RetrofittingAIintolegacyMDM frameworksmayrequiresubstantial reengineering.
Resource Requirements AIenginesdemandcomputeresources, makingcloud-nativearchitectures essential.
Model Transparency AIdecisionsmustbeexplainablefor auditingandcompliance
Compute Resource Requirements AIworkloadsmayrequirecloudoffloading oredgeAIprocessing
in maintaining trust in autonomous security systems and facilitatingforensicanalysisfollowinganoccurrence.
Future Directions in AI-Based Enterprise
Themobilesecurityforenterprisescenekeepsevolving,and withtheadditionofartificialintelligence(AI)willalterits possibilities.Borrowingfromthestartingpointlearningsof AI-powered MDM-integrated app launches, certain spaces arethenextfrontierofthisarena:
Federated Learning for Improved Privacy and Distributed Intelligence: Federated learning will enable collaborative trainingofAImodelsonmanydistributededgedevices,i.e., smartphones and tablets, without the need to transfer sensitiveenterprisedatatoacentralserver.Thiswillgreatly enhancedataprivacyandreducetheriskofdatabreaches while still allowing for the development of robust and intelligentthreatdetectionmodels.
Edge AI for Real-time Mobile Threat Defense: Shifting AI processing to the edge of the network directly on the mobiledevicesthemselves willreducethreatdetectionand response latency by orders of magnitude. By processing threatintelligencelocally,newthreatscanbediscoveredand remediatedinrealtime,improvingoverallsecurityposture andsafeguardingcriticalbusinessoperations.
ExplainableAI(XAI)forTransparencyandTrust:Assecurity operations become more embedded with AI systems, the abilitytounderstandandexplaintheirdecisionsisessential. ExplainableAI(XAI)willprovidethetransparencyneeded, allowing security analysts to understand why a particular threat was detected or a policy was enforced. Interpretability will establish trust in AI-based security systemsandimproveauditingandcompliance.
IntegratingwithGenerativeAIforProactiveSecurity:With the advent of generative AI (GenAI), enterprise mobile securityhastheabilitytounleashmightynewpowers.GenAI canbeemployedforautomatedpolicygeneration,creating adaptiveanddynamicsecuritypoliciesaccordingtoshifting threat landscapes. It can also be applied to facilitate enhanced threat simulations, enabling organizations to anticipate and simulate their defenses against new attack vectors,andassistincreatingdetailedremediationplans.
AI-Driven Unified Endpoint Security (UES): The future of enterprise mobile security is the unification of various disparatesecuritysolutionsintoasingle,AI-drivenplatform. AI-poweredMobileDevice Management(MDM) platforms will integrate natively with Endpoint Detection and Response (EDR), Security Information and Event Management(SIEM),andIdentityandAccessManagement (IAM) platforms. This unification will introduce a consolidatedandintelligentsecuritysolutionthatoffersend-
© 2025, IRJET | Impact Factor value: 8.315 |

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 12 | Dec 2025 www.irjet.net p-ISSN: 2395-0072
to-endvisibility,automatedthreatresponse,andproactive threatprotectionforeveryenterpriseendpoint.
TheintegrationofAIintoMDMisalandmarkevolutionin mobile enterprise security. We're moving away from a reactive, rule-based defense to one that's predictive, adaptive, and largely autonomous. This synergy allows organizationstoproactivelydetersophisticatedthreatsand radicallyenhanceoperationalefficiency.Ultimately,thisis notjustanissueofmorecomprehensivecybersecurity;it's an issue of enhancing user experience and overall operational nimbleness. Rather clearly, AI-driven MDM is becomingacornerstoneofmodernenterpriseITstrategy.
References
[1] Chen,T.,&Guestrin,C.(2016).XGBoost:AScalable TreeBoostingSystem.InProceedingsofthe22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining (pp. 785–794).
[2] Shabtai et al., 2012. Trends in Android Malware Detection
[3] ENISA. (2022). Artificial Intelligence Threat Landscape. European Union Agency for Cybersecurity.
[4] ENISA. (2022). Threat Landscape for Mobile Devices.EuropeanUnionAgencyforCybersecurity.
[5] Serroretal.,2020.ChallengesandOpportunitiesin SecuringtheIndustrialInternetofThings
[6] Gartner.(2023).ArchitectingScalableEvent-Driven SecurityOperations.
[7] Gartner. (2023). Market Guide for Mobile Device Management.
[8] Gartner. “AI in Mobile Device Management: 2024 MarketGuide.”
[9] Google Cloud. (2024). AI-Powered Device ManagementWhitepaper.
[10] GoogleCloud.“AI-poweredMobileThreatDefense: EdgeandFederatedLearningModels.”Whitepaper, 2024.
[11] IBM Security. (2022). the Rise of AI in Endpoint Security.
[12] IBMSecurity.(2023).AI-DrivenEnterpriseMobility withMaaS360.
[13] Khan, M., Arshad, S. Z., & Tahir, A. (2021). Behavioral Biometrics for Mobile Device Authentication: A Review. Computers & Security, 106,102291.
[14] Kumar,S.,Dwivedi,A.,&Vyas,A.(2023).Smishing Attacks and Mitigation Strategies in BYOD Environments.JournalofMobileSecurityResearch, 12(1),55–67.
[15] Liu,F.T.,Ting,K.M.,&Zhou,Z.-H.(2008).Isolation Forest. In Proceedings of the 2008 IEEE InternationalConferenceonDataMining(pp.413–422).
[16] Microsoft. (2024). Adaptive Access and Endpoint ProtectionwithIntuneandDefender.
[17] Microsoft. (2024). AI Integration in Endpoint Manager.
[18] Microsoft. “Adaptive Access and Endpoint ProtectionwithIntuneandDefender.”2024.
[19] Mondal, S., & Bours, P. (2017). A study on continuous authentication using a combination of keystrokeandmousebiometrics.Neurocomputing, 230,1