A SURVEY OF COMPUTER NETWORKING THEORY AND PRACTICE
Rajesh Kumar System Analyst, Department of E-Governance. University Grants Commission New Delhi-110001 ***
ABSTRACT: In a computer network system, the many computers are connected to one another in order to facilitate the exchangeofdigitalinformation.Acomputernetworkis,initsmostbasicform,acollectionofdevicesthatareconnectedtoone anothervialinks.Distributedprocessing,inwhichataskissplitupandcarriedoutsimultaneouslyamongmultiplecomputers, isutilisedbycomputernetworks.Anassaultonanetwork'sresourcesisconsistentlyoneofthemostdifficultobstaclesitmust overcome.Theidea ofcomputernetworksisexaminedindepthinthisresearchstudy.Acomputernetworkconsistsofa collectionofdevicesthatareconnectedtooneanothervialinks.Hostsinpersonalcomputers,phones,andservers,inaddition tonetworkingdevices,canallbeconsiderednodesinanetwork.AccesstotheWorldWideWebforapplications,shareduseof applicationandstorageservers,printers,andfaxmachines,anduseofemailandinstantmessagingprogrammesareallmade possible through the use of computer networks. Sharing of information across many computer networks allows for the completionofavastarrayofjobs.Thereareopensystemsandclosedsystems,thetwoprimarycategoriesofsystems.Anopen systemcanbequicklyconnectedtothenetworkandisimmediatelyreadyforcommunicationwhenitdoesso.Ontheother hand,aclosedsystemcannotbesimplyjoinedtoanothernetworkduetotherequirementofadequateauthentication
KEYWORDS: Computernetworks,Protocols,Typesofnetworks,Topology,Nodes,Datatransfer.
1. INTRODUCTION
Anetworkofcomputers,servers,printers,routers,andswitchesthatareallconnectedtooneanotherandabletoexchange informationwithoneanotheriscalledacomputernetwork.Acomputernetwork'sprincipalfunctionistoenableusersin different locations to share data and resources with one another. Depending on their scale, location, topology, and communicationprotocols,computernetworksfallintoanumberofdistinctcategories.LocalAreaNetworks(LANs),WideArea Networks (WANs), Metropolitan Area Networks (MANs), Storage Area Networks (SANs), and Wireless Networks are all examplesofpopulartypesofnetworks.Localareanetworks(LANs)arenetworksthatconnectdevicesinsideasinglebuilding orcampus.Sincethesenetworksaremorelocalizedandcontainfewernodes,theyaremoreefficientanddependablethanwide areanetworks.Fileandprintersharing,aswellasemailandotherformsofonlinecommunication,relyheavilyonthem.Onthe other hand, wide-area networks (WANs) link offices located in various cities or even in other countries. These networks connectdevicesacrossawidergeographicregionthanLANsdoandmakeuseofavarietyoftechnologies,includingleased lines, satellite connections, and virtual private networks. Wide area networks (WANs) are widely employed for teleconferencing,videoconferencing,andcloudcomputing.MANsarequitesimilartoLANs,excepttheyconnectnumerous LANsacrossagreaterarea,suchasacityormetropolitanregion.Databackup,datareplication,anddisasterrecoveryarejust some of the storage-related tasks that SANs are designed to handle. Wireless networks eliminate the requirement for wiredconnections between nodes by employing radio waves. The simplicity and adaptability of these networks are contributingtotheirrisingpopularity.Wi-Fi,shortfor"wirelessfidelity,"referstoaspecificformofwirelessnetworkthatis widelydeployedinmanydifferentsettings.Datatransmissionandexchangeincomputernetworksismadepossible bya combinationofphysicalconnectionofdevicesandnumerouscommunicationprotocolsandtechnologies.Amongthemare Ethernet,Wi-Fi,TCP/IP,DNS,FTP,HTTP,andaplethoraofothers.Theeffectiveness,safety,anddependabilityofacomputer network dependonitsdesign,configuration,andadministration.Whenplanningandmanaginga network,securitymust alwaysbeatoppriority.Itentailstakingprecautionstopreventhackers,thieves,viruses,andothersecurityrisksfromgaining accesstothenetwork.Firewalls,anti-malwareprogrammes,IDS/IPS,andencryptionareonlyafewofthestandardsecurity methodsusedtoday.Inconclusion,acomputernetworkisasophisticatedsystemthatenablesdevicestointeractwithone anotherandsharedataandotherresources.Differentsizes,topologies,andtechnologycharacterisethemanydistinctvarieties of networks. Network performance, security, and dependability all improve with well-thought-out planning, setup, and maintenance.
2. COMPONENTS OF A COMPUTER NETWORK
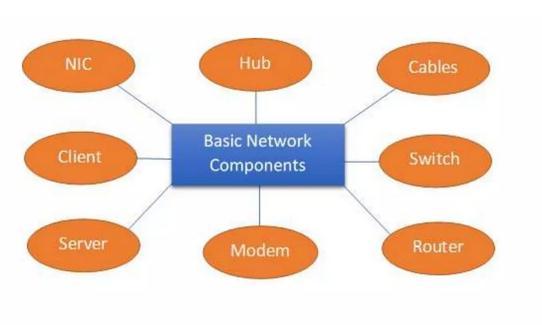
2.1 NIC (National interface card)
Anetworkinterfacecontroller,oftenknownasaNIC,isapieceofhardwarethatactsasaconduitforinformationtogo between a computer and another piece of hardware. The hardware addressesare kept in the NIC,and the data-link layer protocolusestheseaddressestoidentifythesystemthatisconnectedtothenetwork[3].TheNICisresponsibleforstoringthe hardwareaddresses.Thismakesitpossibleforthedatatobetransmittedtothecorrectdestination.ThewirelessNICandthe wiredNICarethetwovarietiesofnetworkinterfacecard(NIC)thatareavailable.
Allcontemporarylaptopsmakeuseofwirelessnetworkinterfacecards(NIC),andaconnectionisestablishedby meansofanantennathatmakesuseofradiowavetechnology
CablesarewhatfacilitatetheflowofdatathroughthemediumusingtheWiredNIC.
2.2 Hub
Incomputernetworking,ahubisadeviceusedtoconnectnumerouscomputerstoaLAN.Onceithasreceivedadatapacket fromonedevice,itwillsenditontoeveryotherdevicethatislinkedtoit.Thismeansthatdatatransmissionfromtwodevices connectedtothehubatthesametimecancausecollisionsanddegradenetworkperformance.Hubswerewidelyusedinthefirst stages of the networking revolution since they were low-cost and simple to set up. However, because to technological advancementsthathavemadeswitchesmorereasonablypricedandefficient,theyhavebecomelessfrequentinrecentyears.A switchisasmarterdevicethatonlysendsdatatotheintendedrecipient,whichgreatlyimprovesnetworkspeedbydecreasing congestion.However,hubsstillhaveaplace,especiallyinlow-trafficenvironmentswherepriceisafactor.Theabilitytoeasily monitornetworktrafficandidentifyissuesmakesthemvaluablefortroubleshootingaswell.
Incomputernetworking,arouterisadeviceusedtolinkandroutedataacrossseveralnodesonseparatenetworks.Likea trafficcop,itdirectstheflowofinformationbetweennetworksliketheInternetandacompany'sinternalLAN.

Inordertodeterminetheoptimalroutingforeachincomingdatapacket,routerslookatitsdestinationIPaddress.Routing tables, which hold data about the networks linked to the router and the paths to reach them, are used to make these determinations.Networkaddresstranslation(NAT)isafeatureofroutersthatenablesnumerousLANdevicestoshareasingle externalIPaddress.
Routersnotonlyforwarddatabetweennetworks,butcanofferadditionalsecurityfunctionslikefirewalls.Theycanprevent hackersfromgainingaccesstoasystemandprotectanetworkfrommalicioussoftware.
Routers can be purchased as physical devices, as network switches that also do routing, or as computer or server-based software.Theyplayacrucialroleintoday'scomputernetworksbyfacilitatingcommunicationbetweendevicesandnetworks andgrantingusersaccesstotheinternetandotherexternalnetworks.
2.4 Modem
A modem isa gadgetthatallows a computer orother device toconnect to theinternet via a telephoneline. Thename "modem"isanabbreviationfor"modulator-demodulator,"whichiswhatitdoes.
A modem is a device that takes digital information from a computer and changes it into an analogue signal suitable for transmission over a telephone or cable connection. Using the preexisting telecommunications infrastructure, this enables computersandotherdevicestoconnectwitheachotherovergreatdistances.
Themodemyouneedwillvarybasedonthenetworkyou'reconnectingto.Connectingtothewebviaaregularphoneline requiresadial-upmodem,whereasconnectingviaacableTVnetworkcallsforacablemodem.DSLmodems,whichemploy digitalsubscriberlines(DSL)todeliverbroadbandInternetaccessoverregularphonelines,areanotheroption.
ISPsaretheoneswhosupplymodems,whichcanbestandalonedevicesorcomponentsoflargernetworkingdevices.Some modemsadditionallyprovideextrafunctionality,suchWi-Fioraphoneline.
Whenitcomestoconnectingcomputersandotherdevicestotheinternetandfacilitatinglong-distancecommunication,modems playacrucialrole.
2.5 Switches
AswitchisacomputernetworkingdevicethatconnectsnumerousdevicesonaLANandcontrolstheflowofdatabetweenthem. Switchesaresmarterthanhubsandcanjustsenddatatothedevicethatneedsit,ratherthanbroadcastingallincomingpackets toallconnecteddevices.
Todeterminewhichportshouldreceiveanincomingdatapacket,switchescheckitsdestinationMACaddress.Hubs,whichcan leadtocollisionsandslowdownnetworktraffic,areavoided,whichbothreducescongestionandincreasesperformance.
Separateunits,networkcardsthatdoubleasswitches,andscalable,modularswitchesarejustafewofthevarioustypesof switches available. The ability to adjust settings like virtual local area networks (VLANs) and Quality of Service (QoS) prioritisationisonewaytoclassifywhetherornottheyaremanaged.

Inorderforcomputerstotalktooneanotherviaalocalareanetwork(LAN)andfordata-intensiveactivitieslikevideostreaming and online gaming to go smoothly, switches are an essential part of today's networks. Access to the network can also be restrictedusingsecuritymeasureslikeMACaddressfiltering.
2.6 Cables
Today'scommunicationandinfrastructurenetworkssimplycannotfunctionwithoutcables.Theyenablethetransmissionof information,energy,andsignalsbetweenvariousentities.Copper,aluminium,andfibreopticstrandsarejustafewexamplesof thematerialsusedtoconstructcables.
Powercables,datacables,coaxialcables,andEthernetcablesarejustafewexamples.Datacablesareusedtotransportdigital data overshorterdistances,whereaspowercablesareusedtotransmitelectricalpower.Coaxial cablesareusedforhighfrequencybroadcastslikecableTV,theinternet,andothersimilarapplications,whereasEthernetcablesareusedforlocalarea network(LAN)connections.
Fibreopticcablesareamodernformofcablethatutilisestransparentstrandsofglassorplastictorapidlycarrydataacross great distances. Since these cables can transfer a lot of data swiftly and efficiently, they are gaining popularity in the telecommunicationsandinternetinfrastructureindustries.
Cablesareessentialtotheoperationofnearlyeveryaspectofourmoderntechnologicalandphysicalinfrastructure.Theymake possiblethevastmajorityofmodernconveniencesweuseonadailybasis.Mainlytherearethreetypesofcables:
a. Coaxial cable
Inelectricalwiring,acoaxialcable(orcoaxcable)hasthreeparts:aninnerconductor,anoutsideconductor,andaninsulating layer.Thesignalissentdownthecopperinnerconductor,whiletheoutsideconductoractsasashieldtoblockoutunwanted signals.Radiofrequencysignals,includingthoseusedforcableTV,internetconnections,andothercommunicationsapplications,
aretypicallytransmittedoveracoaxialcable.Duetotheirsuperiorbandwidth,minimalsignalloss,andnoisetolerance,these cablesarefrequentlyusedinplaceofothers.
b. Twisted pair cable
Twistedpaircableisatypeofinsulatedcopperwiringcommonlyusedintelecommunications.SinceEMIandcrosstalktendto worsenthequalityofdatatransmissionsatgreaterdistances,thetwisteddesignhelpstomitigatetheseissues.
Telephones,Ethernetnetworks,andInternetconnectionsarejustafewexamplesofthewidespreaduseoftwistedpaircables forspeechanddatatransmission.Cat5,Cat6,andCat7areonlyfewofthecategoriesavailable;eachhasitsownuniquesetof requirementsintermsofbandwidth,maximumtransmissiondistance,andotherfeatures.
Twistedpaircablesarewidelyusedinthecommunicationindustrybecausetheyareinexpensiveandsimpletosetup.They deliverconsistentperformanceandareapplicableinavarietyofsettings,fromhomeofficestoenterprise-widerollouts.
c. Fibre optic cable
Thinstrandsofglassorplasticareusedinfibreopticcablestoswiftlycarrydataovergreatdistances.Multipleopticalfibresare enclosedinaprotectivejacketandformthecable.Eachfibreisaroundthethicknessofahumanhairandcantransmitdataover severalchannels.
Compared to copper cables, fibre optic cables have many advantages, including greater bandwidth, greater transmission distances,andresistancetoelectromagneticinterference(EMI).Theyfindwidespreaduseinhigh-speeddatatransmission settingsincludingtelecommunicationsnetworksandinternetbackbones.
Intermsofspeedandreliability,fibreoptictechnologyhascompletelychangedthewayweshareandaccessinformation. Despitethefactthatfibreopticcableinstallationismoreexpensivethancopperorcoaxialcableinstallationintheshortterm,the long-termbenefitsandsavingsmorethanmakeupfortheoriginaloutlay.
3. THE USE OF A COMPUTER NETWORK IN APPLICATIONS
3.1 Resource share
Allowforthesharingoffiles,data,andvariousothertypesofinformationina networkcontext,andgrantauthorisedusers accesstothefiles,data,andinformationthatiskeptonothercomputersthatarepartofthenetwork.

3.2 Interpersonal communications
E-mail,instantmessaging,chatrooms,thetelephone,videotelephoneconversations,andvideoconferencingarejustfewofthe waysthatindividualsareabletocontactwithoneanotherinanefficientanduncomplicatedmannerthankstotheuseofa network.
3.3 Server-Client model
Theserver-clientconceptiscommonlyusedinthefieldofcomputernetworking.Aserverisacentralcomputerthatisusedto store information and is maintained by the system administrator in this way. The server is accessed by other computers. Computersactingasclientsestablishconnectionswiththeserver.Clientsarethecomputersthatareemployedinordertogain accesstothedatathatisstoredontheserverviatheuseofaremoteconnection.
3.4 E-commerce
In businesses, a computer network is another component that is of the utmost importance. You should carry out your commercialoperationsonline.WebsiteslikeAmazon.com,whichdoalloftheirbusinessontheinternetandserveasamodelfor e-commerce,arethegreatestexamplesofwhate-commercemaylooklike.
3.5 Communication medium
Theoverallnumberofusersisstillunknown.Computernetworksdemonstratethequalitiesofacommunicationmediuminthat theyhavethesefeatures.Forexample,acorporationisconsideredtohaveanemailsystemifithasmorethanonecomputerand itsemployeesuseemailastheirprimarymethodofday-to-daycommunication.
4. THE BENEFITS OF WORKING WITH A COMPUTER NETWORK
Using a computer network has many useful applications. Some of the main benefits are as follows:
A. Sharing resources: Connecting many computers together in a network allows them to share peripherals like scanners,printers,andharddrives.Employees'accesstoresourcesisfacilitatedandexpeditedasaresult.
B. Improved communication: Networksfacilitateworkerinteractionbyuseofelectronicmail,IM,andothermeansof groupcommunication.Asaresult,productivityincreasesandcollaborativeeffortsbecomelessofahassle.
C. Increased security: Firewalls, passwords, and other network security measures can keep prying eyes out of computersandoffofprivateinformation.
D. Remote access: Withanetworkinplace,employeesareabletoconnectwithoneanotherandshareinformationfrom any location in the world. Businesses that employ freelancers or individuals who frequently travel to different locationsmaybenefitgreatlyfromthis.

E. Cost savings: Bysharingresourcesandusingcentralservers,companiescansavemoneyonhardwareandsoftware expenses.Additionally,networkscanhelpreducedowntimeandincreaseefficiency,whichcanleadtocostsavings overtime.
5. DISADVANTAGES OF COMPUTER NETWORK
While computer networks have many advantages, there are also some disadvantages to be aware of, including:
a) ThreatstonetworksecurityComputernetworkspresentnewentrypointsforhackersandothercrooks.Inadequate networksecuritymightresultinthedisclosureoralterationofsensitivedata.
b) Computer networks can be difficult to implement and manage, eating up a lot of time and money. This might be difficultforstartupswithlittleresourcesandknowledge.
c) Intheeventofanetworkoutageorothertechnicaldifficulties,businessesthatrelylargelyoncomputersmayendure disruptionsinservice.Productivityandincomemaysufferasaresultofthis.
d) Settingupandmaintainingacomputernetworkcanbecostly,despitethefactthattheyhelpbusinessessavemoneyby standardising procedures and increasing productivity. All the resources (computers, programmes, and people) requiredtokeepthenetworkrunningsmoothlygounderthiscategory.
e) Connectivityissues,incompatibilities,andhardwarefailuresarejustafewexamplesofthetechnicalproblemsthatcan ariseincomputernetworks.Fixingtheseproblems,especiallyifyouneedtobringinoutsidetechnicalexpertise,may beexpensiveandtime-consuming.
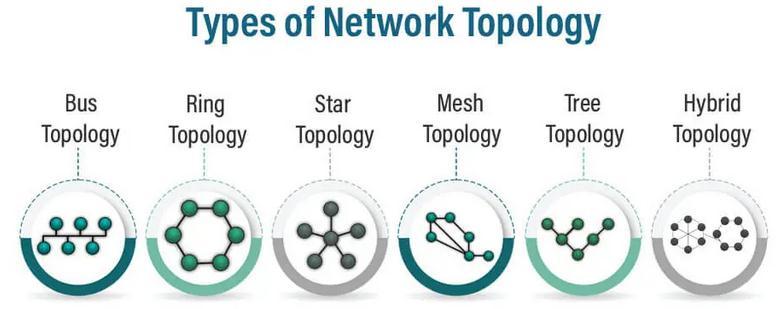
6. TOPOLOGY IN COMPUTER NETWORK
Theterm"topology"maybebrokendownintoitsmostelementarycomponents,whicharetheorganizationofanetworkand themethodinwhichthevariouscomponentsofthenetworkareconnectedtooneanother.Boththelogicalandthephysicalmay bethoughtofastopologiesintheirownright.Neitheroneismoreimportantthantheother.Thebasicgoalofphysicaltopology istoofferageometricrepresentationofallofanetwork'snodes,andoneofthepurposesofphysicaltopologyistotrytoprovide thisrepresentation.
6.1 Bus Topology
a) The bus topology that is utilized often is also referred to by the phrase "backbone cable." A bus topology is characterizedbytheuseofasinglecabletolinkeachnodetotheothernodesinthenetwork.
b) Therearetwowaysthateachnodecanconnecttothebackbonecable:eitherdirectlyorindirectlythroughadrop cable.
c) Wheneveranodeorsystemwishestosendamessagetoanothernodeorsystemusinganetwork,itwillfirstupload the message to the network. The message is transmitted to each and every node in the network, regardless of whetherornotthatnodehasanaddressassociatedwithit.

d) Thebustopologyisthemostfrequentstructureusedfornetworktopologiesthatadheretothe802.3(Ethernet)and 802.4standards.
e) Theconfigurationofabustopologyisnoticeablysimplerincomparisontothedesignofothertopologies.
f) The"singlelane"thatallowsforthetransmissionofmessagestoallofthenodesiswhatismeantwhentheword "backbone"isused.
6.2 Ring Topology
a) Theonlydifferencebetweenthistopologyandthebustopologyisthatthenodesareconnectedwithoneanother usingapoint-to-pointconnection.
b) Duetothefactthatitisunidirectional,datatransfermayonlyoccurinonewayatatime.
c) Thereisnoonepointatwhichtheconnectionsbetweenthevariousnodesinthisstructurecometoastop,asallofthe nodesareconnectedtooneanother.
d) Thisstructureisreferredtoashavingringtopologyduetothering-likestructurethatitpossesses.
e) Whenaringtopologyisutilized,theflowofdataoccursinaclockwisemanner.
6.3 Star Topology
a) Astartopologyisasortofnetworkdesigninwhicheverydeviceonthenetworkislinkedtoacentralhuborswitch. This style of architecture is also known as a star configuration. The centralised hub serves as an intermediary, controllinganddirectingtheflowofdatabetweenallofthedevicesthatarelinkedtoit.
b) Everynodeonthenetworkhasadirectlinktothecentralhubwhenthenetworkissetupinastartopology,which enablesdevicestocommunicatewithoneanotherinatimelyandeffectivemanner.Becauseofthisarchitecture,evenif oneofthedevicesonthenetworkstopsworking,itwillnothaveaneffectontheotherdevicesonthenetworkbecause eachdevicehasitsownindependentconnectiontothehub.
c) Thesimplicityofinstallationandupkeepisoneofthemostsignificantadvantagesofferedbyastartopology.Inorderto addorremovedevices,oneneedjustconnectorunplugthemfromthecentralhub.Thiswillnotaffectthefunctionality of the remaining devices on the network. In addition, because each device has its own dedicated connection, the performanceofthenetworkcanbeoptimizedandmaintainedwithfarlesseffort.
d) Thefactthatastartopologyisdependentonacentralhubis,unfortunately,oneofitsdrawbacks.Intheeventthatthe hubfails,thefunctionalityofthewholenetworkwillbedisrupteduntilthehubiseitherfixedorreplaced.Inaddition, thecostofthecentralhubmightbeamajorinvestment,particularlyfornetworksthatareonabiggerscale.
e) Becauseofitsstraightforwarddesignanduser-friendliness,thestartopologyisfrequentlyusedintheconstructionof smalltomedium-sizednetworks.Itensuresthatdevicesareabletocommunicatewithoneanotherinadependableand effectivemanner,butcaremustbetakentoensurethatthecentralhubisproperlymaintainedandsafeguardedtoavoid disruptionstothenetwork.
6.4 Mesh Topology
a) A computer network witha mesh topology isan architecturein which the nodes are interconnected in a gridlike fashion.Inthisconfiguration,allnodesarelinkedtooneanother,allowingfordifferentcommunicationchannels.This meansthatevenifonelinkfails,datamaystillbesentviaotherchannels,makingmeshtopologyahighlyredundantand fault-tolerantnetworkdesign.
b) Wirelessnetworksfrequentlyemployamesharchitecture,especiallyforlarge-scaleinstallationswhereredundancy andstabilityareparamount.Somewirednetworksutiliseitaswell,includingthoseforHPCandserverfarms.When comparedtoothernetworktopologies,thefundamentaldrawbackofameshtopologyisthecomplexityandcostit entailsduetotheenormousnumberofphysicalconnectionsitrequires.
6.5 Tree Topology
a) Whenitcomestocomputernetworkdesign,"treetopology,"alsoknownas"hierarchicaltopology,"referstoa configurationinwhichnodesareplacedinahierarchicalstructure.Ahuborswitchinthecentreofthistopology connectstootherhubsorswitches,formingatree-likestructureamongthenodes.Inconventionalnetwork architecture, nodes at the bottom of the hierarchy represent end users or devices, while nodes higher up representroutersandswitches.
b) Enterprisenetworksoftenemploytreetopologyduetoitsscalabilityandmanagementbenefits,makingita popularchoiceforlarge-scaleinstallations.Ithascertainbenefitsoverbustopology,forexample,sinceitgives redundancyindatatransferandmaybeexpandedwithoutrequiringmajorchangestotheunderlyingnetwork architecture.However,ifthehierarchygoestoodeep,itcancauseperformanceconcernsandincreasedlatency, makingitmoredifficulttomaintainthanalternativetopologies.Asinglepointoffailurecandisruptthewhole networkbecauseofitsdependenceonacentralhuborswitch.

6.6 Hybrid Topology
a) Theterm"hybridtopology" referstoa specific category ofcomputer network design inwhichtwoormore distincttopologiesarecombinedintoasinglesystem.Thestar-bustopology,acombinationofthestarandbus topologies,isthemostprevalenttypeofhybridtopology.
b) Inthisconfiguration,acentralhuborswitchislinkedtoseveralnodesinastartopology,andthenodesinthe startopologyarelinked to eachother ina bus topology.Assubsetsof devices maybeadded or withdrawn withoutimpactingthewholenetwork,andbackupconnectionscanbeusedintheeventofaconnectionfailure, thisdesignproducesanetworkarchitecturethatisbothscalableandfault-tolerant.
c) Inbigbusinessnetworks,wherevariousdepartmentsmayneeddistinctnetworkarchitecturestosuitspecific requirementsoraccommodateexistingequipment,hybridtopologiesarefrequentlyutilised.Abustopology mightbeusedtoconnectindividualstartopologyLANsindifferentofficebuildingsintoaWANthatconnectsall oftheofficesinthefirm.
7. CONCLUSION
Explaininthisarticletheanalyticalstudythatwasdoneonthemanyfundamentaltopologiessothatwemayhavearoughidea ofwhateachtopologycomprisesandhowtheydifferfromoneanother.Thefeaturesoftopologyareasfollows:reliability, scalability,flexibility,andefficiency.Ifitmixestwoormoredistincttopologies,thedesignmaybecomemoredifficult,andthe infrastructuremaybecomemoreexpensive.Thisisthesolepotentialnegativeoftheapproach.Thedevelopmentofcomputer networks will fundamentallyalter people's ways oflife,suchthatitwill neveragainbe thesame. Humanactivitieslikeas working,playing,andtalkingwillallmakeuseofnetworksinthefuture.Theproliferationofcomputernetworkshashadan effectontheprogressthathasbeenmadethroughouttheworld.Thenetworkswillgiverisetonewprotocolsandstandards, newapplicationswillbeconceivedup,andasaresultofthesechanges,ourliveswillcontinuetobetransformedandenhanced.A networkismadeupoftwoormorecomputersthatarelinkedtooneanotherbymeansofatelecommunicationssysteminorder tomakeiteasierforuserstoshareinformationandmakeuseofcommonresources.Ifbusinesseswereunabletoconnecttoa network,itwouldbeimpossibleforthemtoworktogetheronprojectsorshareresourceswithoneanother.Theabilityto forecastthecharacteristicsofcomplexnetworksrequiresfundamentalinformation,whichispartoftheprimitiveknowledge base.Itwouldappearthatelectroniccommunicationhasthepotentialtoevolveintoahighlyvaluabletoolfornetworking, particularlyifalargenumberofindividualswithsimilarinterestshadaccesstothetechnology.Specifically,thiswouldbethe caseiflargenumbersofpeoplewithsimilarinterestshadaccesstotheinternet.
REFERENCES
[1] A.Mangen,B.R.Walgermo,andK.Brønnick,“Readinglineartextsonpaperversuscomputerscreen:Effectsonreading comprehension,” Int. J. Educ. Res.,2013,doi:10.1016/j.ijer.2012.12.002.

[2] M.Jammal,T.Singh,A.Shami,R.Asal,andY.Li,“Softwaredefinednetworking:Stateoftheartandresearchchallenges,” Computer Networks 2014,doi:10.1016/j.comnet.2014.07.004.
[3] M.N.O.SadikuandC.M.Akujuobi,“Computernetworks,”in Computers, Software Engineering, andDigital Devices,2005.
[4] W.Liu,Z.Wang,X.Liu,N.Zeng,Y.Liu,andF.E.Alsaadi,“Asurveyofdeepneuralnetwork architecturesandtheir applications,” Neurocomputing,2017,doi:10.1016/j.neucom.2016.12.038.
[5] G. Edwards, “Methods Review paper Mixed-Method Approaches to Social Network Analysis,” ESRCNatl. Cent. Res. Methods,2010,doi:10.1108/17465640910978391.
[6] A.Hakiri,A.Gokhale,P.Berthou,D.C.Schmidt,andT.Gayraud,“Software-definednetworking:Challengesandresearch opportunitiesforfutureinternet,” Computer Networks.2014,doi:10.1016/j.comnet.2014.10.015.
[7] R. P. Richner, “Research Collection,” Brisk Bin. Robust Invariant Scalable Keypoints, 2011, doi: 10.3929/ethz-a010782581.
[8] C.Szegedy et al.,“Goingdeeperwithconvolutions,”in Proceedings of the IEEE Computer Society Conferenceon Computer Vision and Pattern Recognition,2015,doi:10.1109/CVPR.2015.7298594.
[9] A. Graves et al., “Hybrid computing using a neural network with dynamic external memory,” Nature,2016, doi: 10.1038/nature20101.
[10] N. M. M. K. Chowdhury and R. Boutaba, “A survey of network virtualization,” Comput. Networks, 2010, doi: 10.1016/j.comnet.2009.10.017.
[11] IEEE Computer Society, “IEEE Standard for Ethernet - Section Two,” IEEE Stand. Ethernet, 2012, doi: 10.1109/IEEESTD.2012.6419735.
BIOGRAPHIES
Rajesh Kumar SystemAnalyst
DepartmentofE-Governance UniversityGrantsCommissionNewDelhi-110001

