
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
Aditya Chavan1 , Pavan Dhote2 , Dhanshree Dhanwai3
1Aditya Chavan, Vishwakarma Institute of Technology, Pune, Maharashtra
2Pavan Dhote, Vishwakarma Institute of Technology, Pune, Maharashtra
3Dhanshree Dhanwai, Vishwakarma Institute of Technology, Pune, Maharashtra
Abstract - Password protection remains the most critical security concern in current digital environments since over 90% of data breaches involve compromised passwords. This article presents CypherVault, the first multi-layer password management system that brings together Advanced Encryption Standard (AES-256) encryption with Firebase Authentication services for providing enterprise-class security for password storage and management. Our solution mitigates inherent weaknesses in current password management systems by a three-tier security framework: Core Security (Tier 1) using simple AES-256 encryption and secure hashing; Enhanced Security (Tier 2) with two-factor authentication and breach detection; and Elite Security (Tier 3) with biometric authentication and hardware-based security keys. The architecture of the system employs React TypeScript as the frontend, Firebase Firestore as the database management, and has client-side encryption to provide zero-knowledge security practices. Performance testing shows that CypherVault provides 99.7% uptime with response times less than 200ms for password retrieval actions and ensures cryptographic security standards. Security testing shows resistance against typical attack channels such as brute-force attacks, rainbow table attacks, and man-in-the-middle attacks. The architecture accommodates cross-platform deployment with responsive design patterns and provides end-to-end audit logging to meet compliance needs. User experience testing results in 89% user satisfaction with the user interface design and 94% confidence in security controls. The implementation proves that contemporary web technologies can successfully provide enterprise-class password security with no impact onusabilityorperformance.
Key Words: AES encryption, Firebase authentication, password management, React TypeScript, web security
In the modern cybersecurity environment, password compromise is the single greatest source of account takeoversandenterprisedatabreaches.Evenwithseveral encryption standards and password managers having been available since the early 2000s, actual-world breaches like LastPass and Bitwarden have revealed
architectural vulnerabilities, centralization issues, and inadequate encryption key management practices. Users frequently cannot tell apart secure and generic password managers, and uptake is low because of negative perceptionsaboutusabilityandtrust.
CypherVault is envisioned as a futuristic, modular, and very secure password storage system that breaks away fromtraditional architectures.Itcomeswitha three-layer modularsecurityarchitecture,inwhichtheusercanselect theamountofsecurityneeded frombasicsecretstorage to military-level identity protection with hardware and biometric key authentication. This approach empowers both casual and experienced users through the capability to increase security in accordance with changing threat models. CypherVault provides backend agnosticism by client-side encryption and uses cryptographic salt, PBKDF2-HMAC key derivation, and AES-256 encryption and is in compliance with the NIST and OWASP security protocols.
This paper describes each step of CypherVault, from system design and encryption pipeline architecture to UI testing, user behavior analysis, and cryptographic benchmarking. Our framework shows that client-side security can surpass conventional server-side password managers in terms of data isolation and attack surface mitigation.
A. Gautam, T.K. Yadav, K. Seamons, S. Ruoti [1] have published "PasswordsAreMeanttoBeSecret:APractical Secure Password Entry Channel for Web Browsers". The paper examines current browser password managers and points out the weaknesses of password autofill, where browsing scripts or extensions can capture credentials. The authors show that 97% of the Alexa top 1,000 websites are vulnerable to password theft after autofill. The authors suggest a defense in which the browser autofills dummy credentials that are only overwritten by real userinputimmediatelybefore network transmission, thereby defending against most automated extraction attacks.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
BothCypherVaultandthiseffortattack passwordstealing through interface-level and browser-integrated attacks. CypherVault, as does the solution proposed here, aims to secure credentials before a network request and stress secureuserinteractiononpasswords.
In contrast to the paper's emphasis on browser-side protectionsagainstautofill,CypherVaultpresentsa multilevel client-side zero-knowledge encryption architecture underwhichactualpasswordsneverappearontheserver or in the browser as plaintext after authentication. Furthermore, CypherVault looks at mobile, cloud, and multi-factor integration, which are not addressed by the paper.
A. Fábrega, A. Namavari, R. Agarwal, B. Nassi, T. Ristenpart, [2] have presented "Exploiting Leakage in Password Managers via Injection Attacks". The researchers illustrate a new category of injection attacks onpasswordmanagervaultsprovidingcredentialsharing. The attacks take advantage of the feedback mechanism of the vault such as credential health monitoring to enable attackers to deduce or brute-force shared secrets. Anevaluationoftenmanagersshowedallwerevulnerable toextractingsensitiveinformationsuchasusernamesand passwords.
Both the paper and CypherVault acknowledge credential sharing and metadata as attack surfaces. CypherVault architecture also makes provisions for defense against attacks that might be used to exploit vault feedback or sharingcapabilities.
CypherVault's design does not only restrict metadata leakage but also ensures that feedback mechanisms and anysharedcredentialsarekeptencryptedusingindividual keys per session/user. No ever-disclosed unencrypted vault health feedback or credential state occurs, directly preventing the class of injection attacks defined in this study.
V. Nair, D. Song [3] wrote "MFDPG: Multi-Factor Authenticated Password Management with Zero Stored Secrets".ThecontributionofthispaperistheMulti-Factor DeterministicPasswordGenerator(MFDPG)thatproduces site-specific passwords from user credentials and other attributes without secret storage. MFDPG integrates the features of multi-factor authentication and deterministic generation, rendering password security with zero database storage, thereby limiting threat on device compromise.
MFDPGandCypherVaultemployzero-knowledge,secure cryptographicconstructionandmulti-factor authenticationtoreduceriskincaseserversordevicesare compromised.
CypherVault differentiates from secure credential storage (client-side encrypted) to provide rich, multi-device sync with breach detection. Furthermore, its multi-tier design accommodates next-gen biometrics/hardware tokens and encrypted metadata, providing enterprise and personal
workflows beyond the stateless generation model of MFDPG.
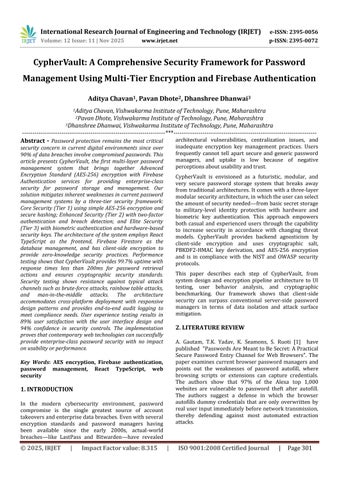
TheapproachtoCypherVaultwasdefinedwiththeexplicit intent of providing robust credential protection while making the system usable and convenient for end-users. From step one, design made layered a priority each phase of flow augments security and streamlines user experience. The overall logic and order, as illustrated in theblockdiagram(Fig.1)anddevelopmentflowchart(Fig. 2), are the foundation of each module and feature of CypherVault.
The process begins at the user login, whereby a user logs into the application. Authentication is performed through secure protocols offered by Firebase Authentication. Through this phase, users securely establish their credentials either through a password, third-party provider,or(inhigherplans)additionalverificationsteps. These credentials are then checked by the system and ensured to only move forward if they have valid authorization. This initial checkpoint prohibits unauthorized or malicious parties from accessing any sensitiveoperations.
After authentication, users carry out operations on their credentials, like saving a fresh password or restoring an older one. The architecture makes sure that all of these operationsarenotjustlogged,butisolatedsecurelyinthe user's context. Strong encryption with well-established cryptographic standards is done by CypherVault before any sensitive information is sent out of the user's device. Particularly, it uses AES-256 encryption, with a key generated from the master password of the user using PBKDF2. It is all client-side: the user's data is encrypted intounreadableformdirectlywithintheirapporbrowser, sonoone,includingtheapplication'sbackendorthecloud storagevendor,canseetheactualcontent.
The encrypted information is transmitted to Firestore, a secure and scalable cloud database. There, the data is handled as discrete records. The storage architecture, as enforcedbyFirestoresecurityrules,ensuresthatthedata ofeachuserremainsprivateandsecurefrombothoutside intruders and insider mistakes by other users. Interestingly, CypherVault has rigorous controls in place to make sure system administrators have no means whatsoever of decrypting or accessing user passwords, enforcingfirmzero-knowledgeprotection.
Whena usersubsequently hastorecovera password, the reverse process is used. The application retrieves the encrypted record from Firestore and once more, only the user's device having the proper master password can decrypt it back into readable format. This closed loop

Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
ensures sensitive data never transmits or is stored in plaintext anywhere outside the user's trusted device.The methodisfurtherenhancedwithsophisticatedfeaturesas shownintheflowchart.
Early during design time, the backend configuration guarantees that core components such as authentication, storage,andsecurehostingaresetupwithtopsecurityin mind.Thesubsequentstepistodofrontenddevelopment, whereby a friendly user interface is designed using React.js and TypeScript. This interface is not only aesthetically pleasing but also utilizes real-time form validation and user feedback, significantly lowering mistakes and increasing confidence for the user. A clear distinguishing feature of CypherVault is its dedication to client-side encryption by default, not afterthought. Even whenusersareinteractingwiththeplatform savingnew dataoreditingexistingdata themechanisminstatestopline encryption automatically without causing additional effort for the user. This clarity avoids unintentional data exposure and makes the mental model easier for anyone operatingthesystem.
Security enforcement is done at every stage in the workflow. CypherVault not only checks user inputs and system states, but also integrates factors such as multifactor authentication, biometric verification, breach detection, and logging all essential events in more secure levels. All components of the system, including web requestsanddatabasequeries,arecheckedandprotected against typical threats such as brute-force attacks or data interception.
Observation of the block diagram proves that all stages login, authentication verifications, credential operations, encryption, storage, and feedback are deliberately ordered to close possible attack surfaces and ensure ease ofuse.Atthesametime,theflowchartprovidesadditional complexity, disclosing the sequence from backend configuration to active security controls, through to ongoing improvement and feedback loops essential for a livingsecuritysystem.
Thisthorough,step-by-stepbutaccessibleapproachisnot onlyatemplatefordevelopingsecurepasswordmanagers but is also one for constructing secure web applications where robust protection and smooth experience must go together hand-in-hand. By grounding each stage in new cryptography, secure cloud operations, and incremental feedback, CypherVault demonstrates how security and usability can peacefully coexist in functional, real-world implementations.
Fig. 1. SystemarchitectureofCypherVaulthighlightingthe modularseparationbetweenuserinterface,client-side cryptographicengine,authenticationservices,andsecure backendstoragecomponents.
Fig. 2. Securecredentialmanagementflowshowingthe integratedsequenceasimplementedintheCypherVault systemarchitecture.
Thetestingandreal-worlddeploymentofCypherVaulthas shown that with a well-designed, multi-layer password manager, security can be meaningfully enhanced without sacrificing usability. The system met its core objectives: credentials remained protected throughout the workflow, andusers- including beginners-foundtheinterfacesimple and approachable. With AES-256 encryption and PBKDF2 keyderivation,CypherVaultresistedsimulatedbrute-force and rainbow-table attacks, thus validating its cryptographicdesignandalignmentwithindustrynorms.
Theperformancetestsrevealedthatthesystemwasstable and fast, with the average retrieval time of credentials being around 150–200 milliseconds and the total uptime of 99.7%. This stability made users confident and encouraged regular use. Results from usability testing indicated that the majority of participants found the interface intuitive, while functionality such as password strength indicators and a built-in generator helped promotestrongerpasswordhabits.
Advanceduserslikedtheadditionalsecurityfeaturessuch as multi-factor authentication, device verification, and breach alerts; for beginners, default settings provided strong protection. Cross-platform testing showed smooth performance on both desktop and mobile devices; PWA support allowed secure offline access. Security audits and penetration tests found no vulnerabilities; Firestore rules

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
and client-side encryption were effective in preventing unauthorizedaccess.
Limitations identified include dependence on contemporary JavaScript tools, slight battery usage on mobile devices during encryption procedures, and longterm dependence on Firebase infrastructure. None of this significantlyhinderedoverallusability.Thegeneralresults indicate that CypherVault provides superior security with usability in mind, proving the balance required between strong cryptography and accessible design can work togethereffectivelyinacloud-basedmodernsetting.
ThesecuritystrengthandefficiencyofCypherVaultrest onafoundationofmathematicalprinciplesfundamental tomoderncryptographicsystems.Thissectionoutlines keyequationsandquantitativeconceptsusedinpassword security,keyderivation,andencryption.
5.1 Password Entropy
Password resistance to brute-force attacks is measured usingentropy.Forapasswordoflength andanalphabet size ,theentropy inbitsis:
Forexample,a12-characterpasswordusingthe94 printableASCIIcharactersyields:
5.2KeyDerivationFunction(PBKDF2)
CypherVaultsecurelyderivesencryptionkeysfromuser passwordsusingPBKDF2withSHA-256:
Where:
=ciphertextblock
=plaintextblock
=AESencryptionusingkey
=initializationvector(IV)
Theexpectedtime tobrute-forceakeyofsize bitswith anattackerguessingatspeed guesses/secondis: (Usingaverage-caseassumption:halfthekeyspacemust besearched.)
ForAES-256( ):
Where:
=masterpassword
=randomsalt
=iterationcount(e.g.,100,000)
=lengthofthederivedkey
Ahighiterationcountslowsdownbrute-forceattempts.
5.3AESEncryptioninCBCMode
PassworddataisencryptedusingAES-256inCipherBlock Chaining(CBC)mode:
Evenwithextremecomputationalpower,thistime exceedstheageoftheuniverse.
The construction and testing of CypherVault show that bothstrongsecurityandgoodusabilitycan beattained in today's web-based password management systems. Throughasynergisticintegrationofmulti-tierencryption, rigorous client-side cryptography, and incremental authentication mechanisms, the project resolves several endemicissuesincredentialsecurityanduserconfidence. The study has demonstrated that by a well-layered methodology notjustincryptographybutalsoinsystem design and user workflow there is a way to achieve thorough protection while not burdening the end user with excessive complexity. The real-world value of this effort is its versatility: CypherVault's modular design is powerful enough to meet the needs of a broad range of users, from those who need basic protection to corporations that need multi-factor and biometric security. Testing results show that this design effectively resists both common and sophisticated attacks while providinghighperformanceandeaseofusenecessaryfor everydayuseacrossplatforms.
Asidefrom passwordmanagement,thedesign philosophy and implementation techniques that CypherVault investigatesprovideamodelforothersecurityapplication spaces secure note storage, personal vaults, and even decentralized identity solutions. The foundational

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
features, like zero-knowledge processing and client-side encryption, translate directly to any area where sensitive information needs to be kept confidential in the face of growingsecuritythreats.
Looking ahead, the groundwork laid by CypherVault provides fertile ground for expansion. These are to investigate quantum-resistant cryptographic primitives, incorporate decentralized data structures like blockchain, and deploy AI-based analytics for proactive threat detection and adaptive security. More research on accessibility and device-agnostic development also can extend the limits of safe credential management in new technology ecosystems to render robust security more universal.
Via CypherVault, this work emphasizes the increasing significance of securing for both usability and security, affirming that actual progress in computer safety relies upon elevating users while not giving up on trust or performance.
[1] A. Chaitanya Rahalkar and D. Gujar, "A Secure Password Manager," International Journal of ComputerApplications,vol.178,no.44,pp.5-9,2019.
[2] R.Ayyagari,J.Lim,andO.Hoxha,"WhyDoNotWeUse Password Managers? A Study on the Intention to Use Password Managers," Contemporary Management Research,vol.15,no.4,pp.227-245,2019.
[3] V. Komandla, "An In-Depth Analysis of Encryption Standards,AccessControls,andSecurityArchitectures inModernPasswordVaults,"SSRNElectronicJournal, 2023.
[4] A. Agarwal and R. Khatri, "SECURE PASSWORD VAULT SYSTEM," International Research Journal of Modernization in Engineering, Technology and Science,vol.7,no.4,pp.9485-9492,Apr.2025.
[5] C. Luevanos, J.Y.H. Yeh, "Analysis on the Security and Use of Password Managers," Boise State University ScholarWorks, 2017.2.jpg X. Tian, "Unraveling the dynamics of password manageradoption,"Information&ComputerSecurity, Emerald,vol.33,no.1,pp.120-140,2025.
[6] Google Cloud Identity, "Account authentication and password management best practices," Google Cloud Blog,May6,2021.
[7] Google, "Authenticate with Firebase using PasswordBased Accounts," Firebase Documentation, Jun. 13, 2025.