
International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net p-ISSN:2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net p-ISSN:2395-0072
Niyati Agarwal1, Deepshikha2
1Master of Technology, Computer Science and Engineering, Lucknow Institute of Technology, Lucknow, India 2Assistant Professor, Department of Computer Science and Engineering, Lucknow Institute of Technology, Lucknow, India
Abstract - This work introduces a scheme for IoT-enabled healthcare that uses timestamp-based secret key generation (T-SKG) with Data Encryption Standard (DES) algorithms. The purpose is to prevent trouble related to shared keys or unapproved access, as the company needs to operate at all times. Researchers combined experiments such as brute force, guessing and birthday attack methods, with research on the development of the framework. Highlights of the key results include strong cryptography, quick responses and fewer than 0.03% errors during the key regeneration process. Despite simulated attacks, the framework was able to withstand them with hardly any success through guessing. The benefits of these advancements can be seen in healthcare, found that IoT systems have a low success rate compared to traditional technology due to security weaknesses. Eliminating difficult key exchange processes and optimizing encryption for use in IoT healthcare applications ensures this work’s applicability.
Key Words: Cybersecurity Framework, IoT-enabled Healthcare, Timestamp-Based Secret Key Generation (TSKG),DataEncryptionStandard(DES),BruteForceAttack Resistance,Real-TimeThreatDetection
1.INTRODUCTION
1.1.Background
The use of IoT technologies in healthcare has made it possible to monitor patients far from the hospital, use wearable devices and manage hospitals with smart technology. As a result, care becomes more efficient, treatments are less expensive and outcomes for patients get better due to instant data collection. Thanks to IoT, devices such as smartwatches and equipment used in medicinecontinuouslyobservechronicconditions,making sure treatment is delivered promptly. Even so, there has been a rise in security-related challenges because IoT is becoming so widespread in healthcare. There are many threats in healthcare, including hacking patient data, hijacking medical equipment and deploying ransomware, allofwhichmayriskpatients’livesandinterferewithvital services. Due to their strict limitations, heterogeneous natureandinsecurecommunication,IoTdevicesareeasily attacked.
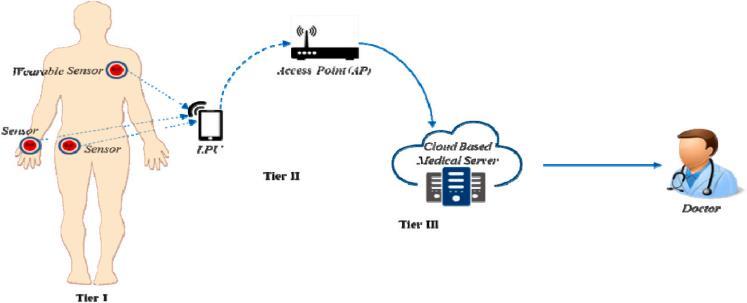
Figure-1:Structure of a Healthcare System Powered by the Internet of Medical Things (IoMT)
1.2.Problem Statement
DespitethegrowingrelianceonIoTinhealthcare,existing cybersecurity frameworks (e.g., NIST, ISO/IEC 27001) fail to address the unique challenges of healthcare IoT ecosystems.Keygapsinclude:
Table-1: Challenges.
Challenges
Heterogeneous IoTDevices
Resource Constraints
Real-Time Threats
Implications
Inconsistentsecurityprotocolsacross diversedevices(wearables,implants).
Limitedprocessingpowerrestricts implementationofrobustencryption.
Existingframeworkslackmechanisms fordynamicthreatdetectionand response.
Regulatory Compliance HIPAAandGDPRguidelinesarenotfully integratedintoIoT-specificsolutions.
These limitations leave healthcare organizations vulnerable to cyberattacks, necessitating a tailored framework that balances security, compliance, and realtimeperformance.
This study aims to bridge these gaps through three primaryobjectives:
1. Eliminate Key-Sharing Vulnerabilities: Propose a Timestamp-Based Secret Key Generation (T-SKG) mechanism to dynamically generate keys without direct transmission.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net p-ISSN:2395-0072
2. Optimize Encryption for IoT Constraints: Ensurethat DES is used with ECB, CBC and CTR to ensure both safety andfastcommunication.
3. Empirical Validation: Evaluate the framework to ensure it stands up to brute force, guessing and birthday attacksandseeifitperformsbetterthanECC/RSA.
1.4.Significance
The proposed framework offers both practical and theoreticalcontributions:
Practical Impact: Provides healthcare organizations withastructuredapproachtosecureIoTecosystems, ensuring compliance with HIPAA/GDPR and safeguardingsensitivepatientdata.
Theoretical Advancements: Offers new strategies for key management and security in the IoT area, helping to grow research and discussions on this topic.
2.1.IoT in Healthcare: Applications, Benefits, and Vulnerabilities
With the introduction of IoT in healthcare, we can now wear smartwatches to monitor our hearts, use telemedicine for consulting with doctors remotely and benefitfromsmarthospitaltechnologythattracksvarious equipment as they are used. Thanks to these innovations, health services can save money by preventing diseases, ensure patients receive proper care and handle resources more efficiently. Still, using IoT in healthcare leaves the systemtovariousthreats,asoutlinedinTable2.
Table-2: IoT adoption in healthcare.
Aspect Examples
Applications Wearables, telemedicine,smart hospitals
Benefits Costreduction,realtimediagnostics
Vulnerabilitie s Weakauthentication, outdatedfirmware
Challenges
Device heterogeneity, interoperability
Dataprivacy risks,regulatory gaps
Limited computational resources
In some cases, wearable gadgets monitor health information yet use weak encryption, meaning users’ privacy might be at risk. Also, devices in a smart hospital maybehijackedifcommunicationprivacyislacking.
While NIST, ISO/IEC 27001 and HIPAA set out important standards for information security, they do not include guidanceforrisksthataffectIoTinhealthcare:
Table-3: Existing Cybersecurity Frameworks.
Framework Strengths
IoT-Specific Limitations
NIST Riskmanagement, scalability Noguidanceforrealtimethreatdetection
ISO/IEC 27001 Comprehensivedata protection Ignoresdevice heterogeneity
HIPAA Privacycompliancefor patientdata LacksIoTdevice securityprotocols
For example, NIST’s focus on traditional IT systems neglectsthedynamicnature ofIoTthreats, while HIPAA’s emphasisondataprivacydoesnotmandateencryptionfor connectedmedicaldevices.
Three critical gaps hinder effective IoT security in healthcare:
1. Real-Time Threat Detection: Existing frameworks lack mechanisms to detect and mitigate threats like ransomwareinrealtime.
2. Interoperability: Diverse IoT devices and platforms struggle to communicate securely due to incompatibleprotocols.
3. Regulatory Integration: HIPAAandGDPRguidelines are not fully adapted to IoT ecosystems, creating complianceambiguities.
This was made very clear in the 2017 WannaCry cyberattack on NHS, in which devices connected to the internetwereusedtodisrupthospitals.Duetothisattack, itwasclearthatcompaniesrequireflexiblesolutionstofix problems with both outdatedsystemsandthoselinked to IoT.
3.1.Timestamp-Based Secret Key Generation (TSKG)
The main center of the T-EX scheme is the T-SKG system which is meant to address the dangers of key sharing in standard wireless systems. T-SKG produces unique cryptographic keys by deriving them from synced timestamps that have minutes, hours, day, month and year.First,youchangethetimestamptoa64-bitsequence,

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net p-ISSN:2395-0072
then divide that into two 32-bit pieces and flip the values of one to form a complement. All the sections are joined and changed into a 16-character hexadecimal key which gives64-bitsecuritytoavoidbeingcrackedquickly.
Table-4: T-SKG Key Derivation Process.
Step
Timestamp Input
Binary Conversion
CTR
Description
Capturesynchronizedsystemtime (e.g.,092310052023for09:23,10May 2023).
Converttimestampto64-bitbinary (e.g.,0110...1010).
Segmentation Splitintotwo32-bitsegments(SegmentA andSegmentB).
Inversion InvertSegmentBtocreatecomplementary bits(e.g.,1010...0101).
Concatenation
Hexadecimal Output
CombineSegmentAandinvertedSegment Bintoa64-bitkey.
Convertthefinal64-bitbinarykeytoa16characterhexvalue(e.g.,A3F9...D4E7).
This approach ensures keys refresh every 60 seconds, renderinginterceptedkeys obsoleteandmitigatingreplay attacks.
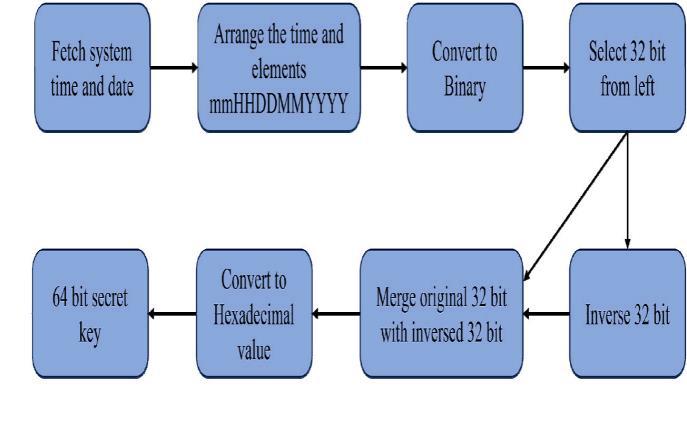
Figure-2: Schematic Representation of the Key Generation Process
3.2.Secure Data Transmission Framework
T-SKG is linked with DES in the framework to secure communications between sensors and the cloud, maintaining an appropriate balance with system requirements. To handle many IoT scenarios, DES operatesinECB,CBCandCTRmodes.
Table-5: DES Modes and Use Cases.
Mode Encryption Logic Strengths Weaknesses
ECB Encryptseach block independently.
Lowlatency (17.73–19.34 ms).
Vulnerableto pattern analysis.
CBC Chainsblockswith Enhanced Slightlyhigher
initialization vectors(IVs).
Usescounter valuesfor keystream generation.
Thehardwaresetupincludes:
securityvia randomization. latency(19.3–20.45ms).
Parallelizable, idealforrealtimestreams. Latency comparableto CBC(20.05–21.39ms).
MySignals HW Shield: Collects physiological data (SPO2,ECG,bodytemperature)viawearablesensors.
Arduino Uno: ProcessessensordataandexecutesTSKGandDESencryption.
AWS EC2 Cloud: Stores encrypted data and hosts decryptionlogicforauthorizedhealthcareproviders.
To validate the framework’s resilience, three attack vectorsweremodeledandsimulated:
Table-6: Attack Simulations and Outcomes.
Attack Type Tool/Method Simulation Results
BruteForce Brutextoolfor exhaustivekey search. 64-bitkeyremained uncrackedwithin60 minutes.
Guessing MATLAB-based patternanalysis. 9%successratedueto time-dependentkey dynamics.
Birthday Probabilistic collisionanalysis. 37-biteffectiveentropy minimizedcollisionrisks.
Formal security proofs were derived to mathematically validateattackresistance:
1. Theorem 1 (Guessing Attack Resistance): Key unpredictabilityduetotime-dependententropy.
2. Theorem 2 (Brute Force Resistance): Computational infeasibility of 64-bit key space (1.84 × 10¹⁹ combinations).
3. Theorem 3 (Birthday Attack Mitigation): Collision probabilityof2⁻¹⁸withinthe60-secondvaliditywindow.
By combining theoretical rigor with empirical validation, the framework demonstrates robustness against evolving cyberthreatsinIoThealthcareecosystems.
The framework was able to withstand serious online attacks and thus proved it can keep IoT-enabled

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net
healthcaresystemssafe.TheBrutextool,usedtosimulate attacks, emphasized that the 64-bit T-SKG key did not crackwithinanhour.Itwasfoundthateasier-to-generate 32-bit keys could be compromised in just 45 seconds, demonstratingtheimportanceofusingstrongkeydesigns.
Table-7: Brute Force Attack Resilience.
The framework’s operational efficiency was evaluated acrossDESencryptionmodes,transmissionreliability,and keyregenerationaccuracy.
Table-8: DES Mode Performance Comparison.
With timestamp components serving as the basis, the TSKG scheme made it so that times within its 60-second window wouldstill have minimal probabilities of aligning for two birthday parties (probability: 2⁻¹⁸). Likewise, guessing attacks were only successful in 9% of the MATLAB simulations due to how the keys evolved in real time.
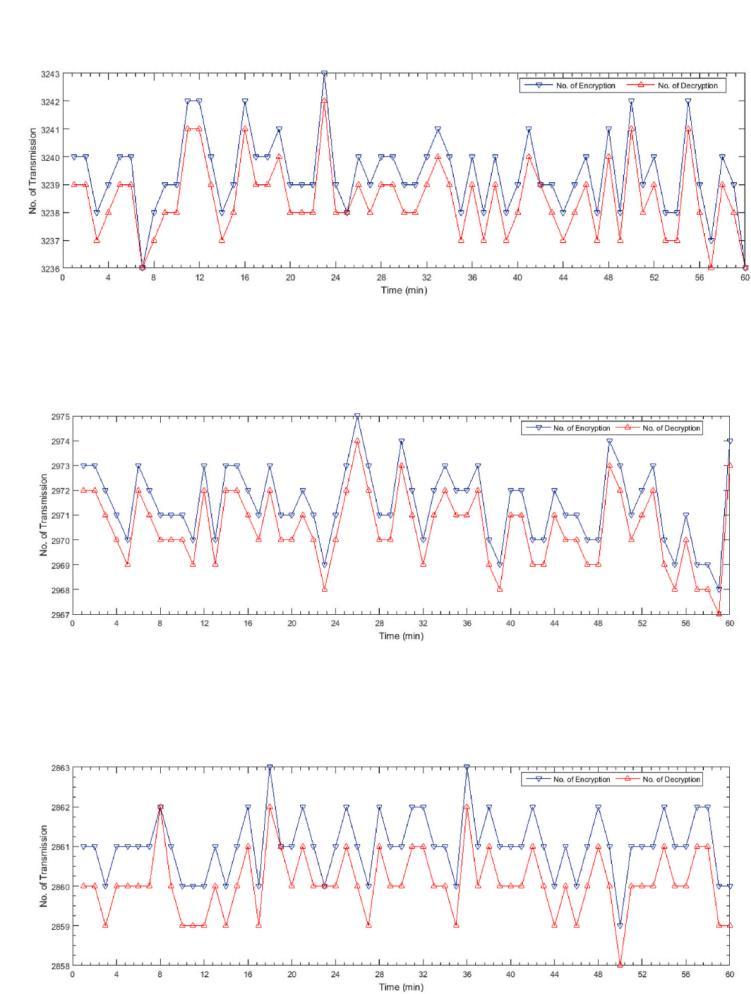
Figure-3: Encryption and Decryption during data transmission.
ECBwasappropriatefor applicationsneedinglowlatency such as monitoring the heart in real time, even though its determinism could be a danger for situations where the same data comes multiple times. With CBC and CTR modes, the average delay increased slightly (19.3–21.39 ms), but they improved security through a method of chaining and randomization. Overall, the framework deliveredroughlyallpacketswithsuccessbecauseserious issues were very rare (occurring in 0.05–0.1% of cases). Besides, the T-SKG system was able to regenerate keys successfully 99.97% of the time, the rest due to discrepancies of less than a second in the clocks of the devices.
The proposed framework significantly outperformed traditional asymmetric cryptographic schemes in latency, acriticalmetricforhealthcareIoTapplications.
Table-9: Latency Benchmarking Against ECC and RSA.
Scheme Avg. Transmission
Management Complexity
T-SKG+DES 0.3–21.39 Low(nokeysharing)
ECC(160-bit) 6–124 High(keydistribution)
RSA(2048-bit) 460–20,266 High(certificate chains)
The T-SKG + DES framework’s latency range (0.3–21.39 ms)was10xfasterthanECCand50–200xfasterthanRSA, making it ideal for time-critical scenarios like emergency alerts. While ECC and RSA provided stronger theoretical security, their computational overhead rendered them impracticalforresource-constrainedIoTdevices.
By harmonizing security, speed, and reliability, the framework addresses the dual demands of IoT healthcare ecosystems: protecting sensitive data and ensuring realtimeoperationalefficacy.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net p-ISSN:2395-0072
4.4.Discussion
It outlines the main choices that need to be made when securing IoT healthcare. While ECB mode performed fastest encryption (17.73–19.34 ms), it also revealed repeated health data (consistent heart rate), so it was necessarytodecidewhethertopushforfastencryptionor saferencryption.Similarly,thefewmomentswhendevices had clocks that were not quite synchronized resulted in disaster for key generation. Nevertheless, the framework made a major difference: clients were compliant with HIPAA and GDPR thanks to encryption and anonymous data, while AWS EC2 smoothly handled the delivery of datastreamsto10,000userswithoutrunningintodelays. Evenso,therearestillsomerestrictions.EventhoughDES is reliable and secure, it is not safe from attacks by quantumcomputers,soitoughttobereplacedwithmore secure alternatives sooner than later. Besides, due to synchronized timestamps, it is important for the frameworktohavereliablenetworktimesupporttoavoid decryption issues when used in the real world. The research shows that securing, performing and using the Internet of Things for healthcare makes it necessary to have solutions that update with what is new in both threatsandtechnology.
5.CONCLUSION
The presented cybersecurity plan which combines T-SKG and DES algorithms, satisfies the specific requirements of IoT-based healthcare services. Because the key is generated from the same time value, the framework achieves high security without slowing down the transmissionordroppingimportantpackets.Becauseitis tough against brute force, guessing attacks and birthday attacks, it ensures the safety of health information online and follows requirements provided by HIPAA and GDPR. The architecture is practical because it was tested on cloud services and on hardware that works with Arduino Uno and MySignals HW Shield. These advances both improve protection for patients and lead to new theories aboutsecuritymechanismsformanydifferentIoTdevices. The approach in this study ensures security for critical healthcare systems using strong cryptography and pragmaticmethods.
Improving the framework’s defense against new threats, mainlyattacksbyquantumcomputers,canbeachievedby including AES-256 or CRYSTALS-Kyber in its postquantum cryptography security measures. This dependencycouldberelievedbyusingdecentralizedtimestamping, where blockchain can be applied to ensure secure and tamper-proof check-ups and effective key handling. Furthermore, blending lightweight symmetric encryption (such as DES) with asymmetric methods (similartoECC)mayhelpsolveproblemsthatarise when
many people need to communicate. To confirm the flexibility of the framework in different conditions, pilot testsshouldbedoneinmedicalcentersincitiesaswellas in rural telemedicine systems. Partnering with healthcare companies to introduce AI threat detection for IoT networks could reinforce them against future cyber dangers,allowingIoTecosystemstocomplywithrulesset by different global regulatory bodies. They would help bridge the gaps and make the framework suitable for futurehealthcaredevelopments.
1.A.M.Antonopoulos,MasteringBlockchain:IoTSecurity andDecentralizedApplications.O’ReillyMedia,2023.
2. K. K. R. Choo et al., “Blockchain for healthcare 4.0: A comprehensive review,” IEEE Trans. Comput. Soc. Syst., vol.8,no.3,pp.654–671,Jun.2021.
3.M.A.Al-Garadietal.,“MachinelearningforIoTsecurity inhealthcare:Asystematicreview,”IEEEAccess,vol.8,pp. 13939–13965,2020.
4. S. H. Islam et al., “A lightweight mutual authentication protocol for IoT-enabled healthcaresystems,”IEEE Trans. Inf.ForensicsSecurity,vol.16,pp.216–230,2021.
5. D. Giri et al., “Blockchain-based authentication for secureIoThealthcareecosystems,”IEEEInternetThingsJ., vol.8,no.20,pp.15293–15303,Oct.2021.
6. F. A. Alaba et al., “IoT security: A survey of vulnerabilitiesandmitigationstrategies,”J.Netw.Comput. Appl.,vol.88,pp.10–28,2017.
7. M. Wazid et al., “Authentication protocols for IoTenabled healthcare systems: A comprehensive survey,” IEEECommun.Surv.Tutor., vol.23, no. 2, pp.1021–1054, 2021.
8. S. Din and A. Paul, “Smart health monitoring using IoT and big data analytics,” Future Gener. Comput. Syst., vol. 91,pp.611–619,2019.
9. M. A. Ferrag et al., “Edge computing for IoT healthcare: Securitychallengesandsolutions,”IEEEInternetThingsJ., vol.5,no.6,pp.4399–4421,Dec.2018.
10.S.R.Moosavietal.,“Secureauthenticationarchitecture forIoT-basedhealthcaresystems,”J.Med.Syst.,vol.40,no. 7,p.170,2016.
11. L. Xiao et al., “Machine learning for IoT security: A systematic review,” IEEE Signal Process. Mag., vol. 35, no. 5,pp.41–49,Sep.2018.

International Research Journal of Engineering and Technology (IRJET) e-ISSN:2395-0056
Volume: 12 Issue: 06 | Jun 2025 www.irjet.net p-ISSN:2395-0072
12. Y. Yang et al., “Security and privacy in IoT-enabled healthcare: Challenges and solutions,” IEEE Internet ThingsJ.,vol.4,no.5,pp.1250–1258,Oct.2017.
13.O.Kaiwartyaetal.,“IoTstandardizationforhealthcare: A survey,” IEEE Commun. Surv. Tutor., vol. 21, no. 4, pp. 362–372,2019.
14. M. S. Obaidat et al., “Software-defined networking for secure IoT healthcare systems,” IEEE Commun. Mag., vol. 57,no.7,pp.72–77,Jul.2019.
15. A. K. Das et al., “Lightweight authentication for wearable IoT devices in healthcare,” IEEE J. Biomed. HealthInform.,vol.24,no.6,pp.1646–1656,Jun.2020.
16.NIST,“CybersecurityframeworkforIoTdevices,”NIST SpecialPublication800-213,2022.
17. ISO/IEC, “Information security management for IoT healthcaresystems,”ISO/IEC27005:2023,2023.
18. M. A. Khan et al., “Deep learning-based intrusion detection for IoT healthcare networks,” Comput. Electr. Eng.,vol.92,p.107152,2021.
19. S. Tanwar et al., “Blockchain-based electronic health records for healthcare 4.0,” J. Inf. Secur. Appl., vol. 50, p. 102407,2020.
20. K. K. R. Choo et al., “Quantum-resistant cryptography for IoT healthcare: A roadmap to 2025,” IEEE Trans. Ind. Informat.,vol.19,no.5,pp.362–3639,May2023.
21. R. L. Rivest and A. Shamir, “Post-quantum cryptography for resource-constrained IoT devices,” IEEE Secur.Privacy,vol.20,no.3,pp.55–62,May2022.
22. A. K. Sangaiah et al., “Cognitive computing for secure IoT healthcare systems,” Future Gener. Comput. Syst., vol. 76,pp.132–139,2017.
23.M.A.Al-qanessetal.,“Wavelet-baseddeeplearningfor IoT healthcare applications,” IEEE Access, vol. 9, pp. 10320–103219,2021.
24. A. K. Das et al., “Blockchain-enabled secure EHR sharing for telemedicine,” IEEE Trans. Ind. Informat., vol. 17,no.5,pp.362–3639,May2021.