
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
Dr. Nikita Bahaley1
1Assistant Professor, Dept. of Information Technology, Pillai College of Arts, Commerce & Science (Autonomous), New Mumbai, Maharashtra, India
Abstract - The increasing number of cyber-attacks on network systems has become a significant challenge for network security under real-time network scenarios. Deep learning models have proven to be effective in identifying network attacks. However, these models require a large amountofdatafortraining,andtheirimplementationcan be computationally expensive when deployed on large-scale networks. To overcome these issues, this paper proposes a blockchain-based deep learning model that utilizes the advantages of blockchain to enhance the efficiency and security of network attack identification and mitigation. The proposedmodeluses a novelProof-of-Wireless-Trust (PoWT) consensusalgorithmtovalidateandsecurethetrainingdata, and a customized Binary Cascaded Deep Learning Model (BCDLM) for training the model w.r.t. multiple attack signatures. The blockchain-based model is designed to detect and mitigate dynamic network attacks in real-time, thereby enhancing the security of network systems. The proposed model is evaluated using different network datasets.
Key Words: Network, Attacks, Dynamic, Bioinspired, Machine, BFO
Stabilityisanessentialcomponentinthedesignandanalysis of networking & control systems. In networked control systems (NCS), the restricted on-board energy resources provided to the system demand the implementation of solutions that decrease processing, such as status monitoringandcontrolinputupdate[1].Duetotheadvent ofcyberattacks,theresistanceofNCSs(networkedcontrol systems) to different forms of assault has attracted substantialattentionandiscurrentlyoneofthemostserious concernsinNCSsviaAdaptiveDynamicProgramming-based Optimalevent-triggeredNN(ADPONN)controller[2].Fora longtime,stabilityanalysisandcontroldesignhavereliedon continuous-time state measurements and control approaches [3]. Researchers were required to utilize sampled-datatechniques[4]inNCSsowingofphysicallimits suchasenergyandnetworkcapacity,whichneededfrequent stateassessmentandcontroladjustments.Inrecentyears, the use of event-triggered (ET) techniques to further decreaseprocessinghasgainedattention.IntheETsystems, data updates and transfers are only sent out if specific criteria are met. The detection of events in various ET
systems [5] involves continuous-time state measurement and monitoring of the triggering condition, both of which utilizealargeamountofenergy.TheemergenceofsampleddataETsystemshaseasedthisneed.Intheseprocedures, merely periodic samples of the system are employed to evaluate the condition and monitor the ET state [6, 7]. Recentworkhasproposedadynamiceventtriggering(DET) techniquethatintegratesanextradynamicvariableintheET condition. As illustrated in [1], the deployment of DETs resulted in fewer transmissions than so-called static ET approaches.Nonetheless,itisassumedin[8,9,10,11,12, 13]thatmeasurementsandeventswouldbemonitoredin real time via Event-Triggered Dynamic Watermarking operations.
The value of DET techniques is considerably boosted by integrating a mechanism for measuring and monitoring gathered data. A sampled-data DET framework for linear systemstabilizationhasbeenproposedin[14,15].Riccatibasedapproaches[14,15]complicatethecontrollerdesign, andthecontrolgainsmustbedeterminedbeforehand.Inthe contextofETcontrol,therearefrequentlytwotechniques for developing unknown control and ET parameters: I emulation and (ii) co-design. In the emulation-based techniques, the control gain is first determined without takingtheETschemeintomind.Inthesecondstage,theET parametersareproduceddependingonthesuppliedcontrol gain values. In co-design methodologies like Model PredictiveControl(MPC)[16,17,18,19,20],thecontrolgain andETparametersaregeneratedconcurrentlyusingasingle framework.TheETparameterfeasiblezonesareconstrained by the initial selection of the control gains, which is a weakness of the emulation-based design via Neural Network-based Function Approximation Technique (NN FAT)[21,22,23,24,25].TheETapproachisconsequently lesseffectiveinloweringthevolumeoftransmissions.The application of the co-design technique for sampled-data dynamic event-triggered control deserves additional exploration. The functioning of NCSs may be dramatically reduced by assaults utilizing a number of malicious modification methods. If the adversary's impact is not adequatelyaccountedforin thestabilityanalysis,theNCS maybecomeunstableinresponsetoassaults.DDoSassaults are one of the most popular forms of cyberattacks (DoS) (DoS). In DoS, the opponent typically blocks transmission channels.Despitethefactthatsensor/controlpacketlosses

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
havebeenstudiedforNCSsinthepast[26,27],addressing the DoS phenomenon induced by adversaries needs a separateformulationoftheproblem[28].Contrarytotrue packetdropout,whichcanconceivablybeseenasarandom process,pickingastochasticbehaviorforDoSassaultsfails toeffectivelydepictthemalevolentandintelligentcharacter of an opponent, as noted in [29, 30]. Resilience results againstDoShavebeenpublishedin[31,32,33]forvaried applications.AssumingtheDoShasaperiodicpattern,[34, 35, 36] investigate the resistance of various NCSs to DoS Notably,takingperiodicorstochasticpatternsintoaccount for DoS may not sufficiently portray the unknown and hostilenatureof the opponent. In [37, 38,39, 40], a fuller model for DoS is addressed, in which the DoS incidence patternispresumptivelyunexpected.Onlytheopponent's energylimitsmaybeexploitedtodescribetheseDoSmodels. For instance, when analyzing DoS, [2] only examines the aggregatelengthandfrequencyoftheassaults.Basedonthe lengthandfrequencyofDoS,[2]determinesthelevelofjoint resistance to DoS. The references [2, 4, 10, 24] employ an emulation-basedmethodtoattainthehighestdegreeofDoS resistance. One of this method's drawbacks is that it producesaconservativelimitforthealloweddegreeofDoS. Causedbytheutilizationofnormsandextremeeigenvalues in the linked matrices to construct the enhanced DoS boundaries. An alternate strategy is to embed the desired amountofresiliencewithintheco-designframework,which forbidstheusageofsuchnormsandeigenvalues.Inresponse totheaforementionedinadequacies,thefollowingportionof this book provides constructing a bio-inspired machine learning model for anticipating dynamic network assaults using traffic pattern analysis. The effectiveness of the recommendedmodelwasassessedandcontrastedinSection 3 of this book. Under varied real-time settings, measures including attack detection accuracy, recall and precision levels, and attack detection latency were developed. This article continues by expressing a few fundamental observations on the presented model and recommending methodstoenhanceitforuseinreal-worldscenarios.
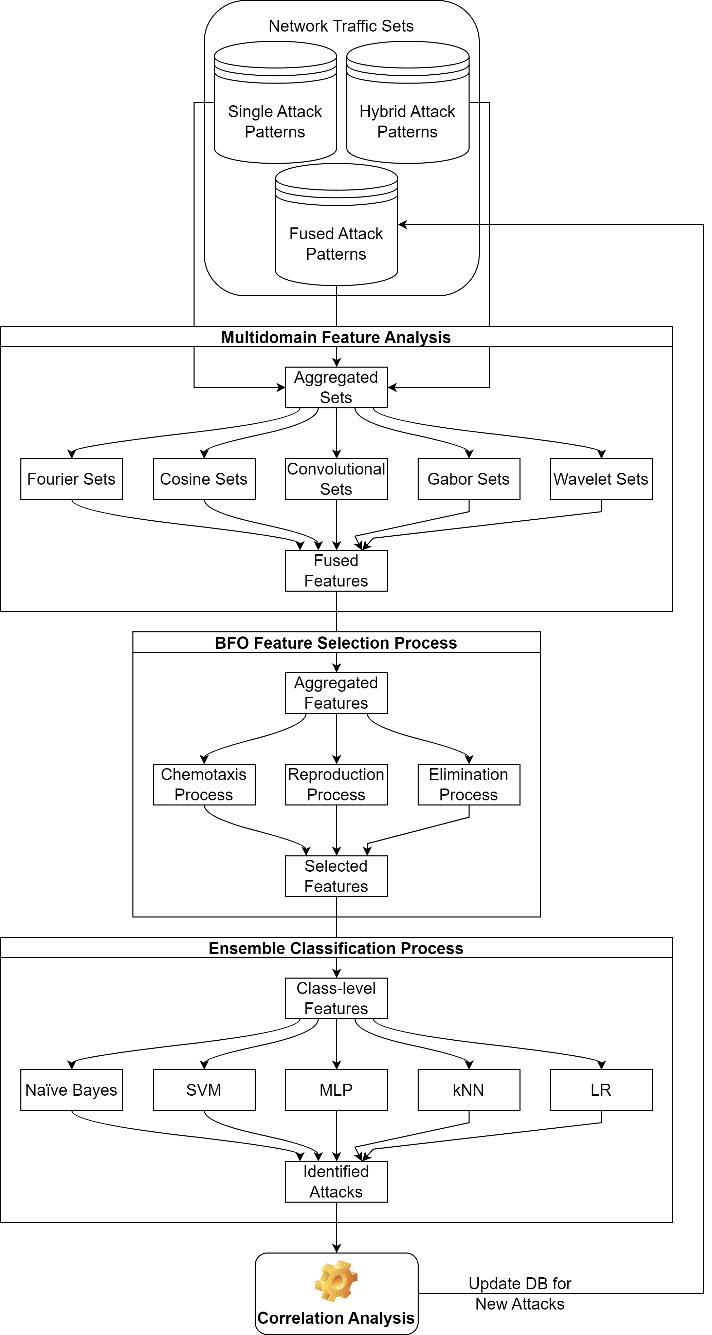
Asperthebriefreviewofattackanalysismodelsitcanbe observedthatsecurityexpertshaveproposedawidevariety of pattern analysis models, but most of them are either highly complex, or cannot be scaled for larger network densities. In addition, the efficiency of such models diminishes in proportion to the number of attack combinations, limiting their applicability to real-time use cases. This section discusses the design of a bio-inspired machine learning model for estimating dynamic network attacks by analyzing traffic patterns in order to address theseissues.Figure1depictsthemodel'sflow,whereitcan beseenthattheproposedmodelinitiallycollectslarge-scale attack-specificinformationsetsandthenusesthesesetsto
extract multidomain features. These capabilities perform frequencyanalysis,energyanalysis,window-basedanalysis, andspatio-temporalanalysis,whichaidsinidentifyingtraffic patternsforspecificattacktypes.Thesetrafficpatternsare processedbyaBacterialForagingOptimizer(BFO),which aidsintheidentificationofattack-specificfeaturesetswith high density. The identified features are classified using a combination of ensembles of weak classifiers whose performance is enhanced through boosting operations. These classifiers consist of Nave Bayes (NB), Multilayer Perceptron (MLP), k Nearest Neighbours (kNN), Support VectorMachine(SVM),andLogicalRegression(LR),allowing themodeltoidentifydynamicnetworkattacks.
Themodelusesamultidomainfeatureanalysisprocessto estimatefrequencypatterns,entropypatterns,convolutional patterns, spatial and wavelet patterns from traffic data

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
samples.Thisassistsinidentificationofaugmentedtraffic patterns for different attack types. This is done via the followingprocess,
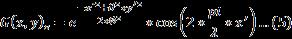
FourierTransformisusedtoidentifyfrequencyfeatures viaequation1,
Where, is the set of values present in the traffic data samples, while are total number of values which are availablefortrafficanalysis.
Discrete Cosine Transform (DCT) is used to estimate entropylevelsoftrafficpatternsviaequation2,
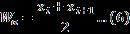
Window-based convolutional sets are estimated via equation3,
Where, are dimensions of window & strides, while isanactivationenginethatusesLeakyRectilinear Unitforretainingpositivefeaturesetsviaequation4,
Where, representsaretainingconstant,whichassistsin scalingpositivefeaturesets.
Similar to these, Gabor features are estimated via equation5, Where, isthesamplenumberanditssamplevalue,while represents different scaling angles, and wavelengthsforGaboroperations.
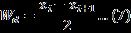
Thesefeaturesarefurtheraugmentedviaextractionof approximate( )anddetail( )Waveletfeaturesvia equations6&7asfollows,
A combination of these features is capable enough to represent input traffic patterns into multidomain feature sets.Butthesefeaturesetshaveinherentredundanciesdue tosimilaritiesbetweeninter-classfeatures.Toreducethese redundancies and retain highly variant feature sets a BacterialForagingOptimizer(BFO)isused,whichworksas perthefollowingprocess,
Tosetuptheoptimizer,asetofconstantsareinitialized asfollows,
o Total count of Bacteria that will take part in the optimizationprocess( )
o Total iterations for which these bacteria will be reconfigured( )
o Bacteriumlearningrate( )
To generate initial Bacterium, a set of Chemotaxis operations are used, which work as per the following process,
o Stochasticallygenerateasetoffeaturesviaequation8,
Where, arethecountoffeatureswhichareaggregatedby themultidomainfeatureextractionengine,while is astochasticMarkoviannumbergenerationprocess.
o Oncethesefeaturesareestimated,thenaBacterium fitnessiscalculatedviaequation9,
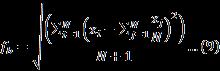
Once a set of Bacterium are generated, and then thresholdfitnessisestimatedviaequation10,
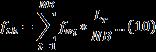
Reproductionoperationsfromcurrentiterationtonext iterationareperformedforBacteriumwith
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072 © 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page439

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
Elimination operations from current iteration to next iterationareperformedforBacteriumwith
Basedontheseoperations,Bacteriumareregenerated formultipleiterations.
Oncealliterationsarecompleted,thenasetoffinalfeature vectorsareaggregatedviaequation11,
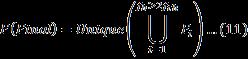
Thissetrepresentsfeatureswithhighervariance,thuscan assistinimprovingclassificationperformancefordifferent attack types. This performance is further tuned via integrationofmultipleweakclassifiers,andboostingtheir performance via accuracy-based fusion operations. To performthistask,NaïveBayes(NB),kNearestNeighbours (kNN), Logistic Regression (LR), Support Vector Machine (SVM),andMultilayerPerceptron(MLP)werefused,which assistedinefficientclassificationfordifferentattacktypes. Parametersetsforeachoftheseclassifierswereselectedas pertable1,
Weak Classifier used for fusion operations
Parameters initialized for these classifiers
NaïveBayes(NB) Priors (P) is a probability metric, whichisevaluatedasperequation12,
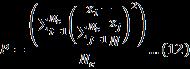
Smoothing Value ( ), is equated to
k Nearest Neighbours(kNN) k = 1, for singular feature classificationoperations
Multilayer Perceptron
Alpha, which is a regularization constant,itequatedto
Max Iterations are same as of theLRprocess
Maximum Function Calls are also same as , which makes the process highly efficient even under multipleattacks
Table-1
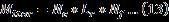
All these classifiers are fused together to estimate final attackclassviaequation14,
Where, representsoutputclassandaccuracy of classifier , while is the output attack class. This informationisusedtoestimatefinalattackprobabilityvia equation15,
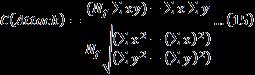
Where, representsdatabasefeaturesfordifferentattack classes,while representsfeaturesofnewtrafficsamples. Foranyattacktypeif ,thenthesample isclassifiedintothatattacktype,anditsmetadataisupdated in the database, which assists in iterative feedback operations. Due to which the model is able to iteratively learnfromnewsamples,andprovideefficientclassification resultsevenunderreal-timeattacks.Efficiencyofthismodel isestimatedintermsofaccuracy,precision,recall,anddelay metricsinthenextsectionofthistext.

SVM Regularization constant ( ),
where aretotalnumberofattack classes
Tolerance of error ( ), is also equatedto
Logistic Regression
Tolerance of error ( ), is same as ofSVMprocess
Class Weights are same as priors of theNBprocess
MaximumIterationsisestimated via equation13,
The proposed attack identification model initially collects large-scale attack-specific information sets and then uses thesesetstoextractmultidomainfeatures.Thesecapabilities performfrequencyanalysis,energyanalysis,window-based analysis, and spatio-temporal analysis, which aids in identifying traffic patterns for specific attack types. The identified traffic patterns are processed by a Bacterial ForagingOptimizer(BFO),whichaidsintheidentificationof attack-specificfeaturesetswithhighdensity.Theselected featuresareclassifiedusingacombinationofensemblesof weak classifiers whose performance is enhanced through

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
boostingoperations.TheseclassifiersconsistofNaveBayes (NB), Multilayer Perceptron (MLP), k Nearest Neighbours (kNN), Support Vector Machine (SVM), and Logical Regression (LR), allowing the model to identify dynamic networkattacks.Performanceofthismodelisevaluatedin termsofaccuracy(A),precision(P),recall(R),anddelay(d) metrics,whichareestimatedviaequations16,17,18and19 asfollows,
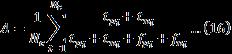
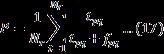
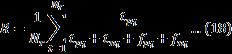
Where, represents true and false rates, while are the timestamps used for completion and start of the classification process. The model’s performance was evaluated for attack classes, whichweretakenfromthefollowingdatasets,
NetworkIntrusionDetection,thatcanbedownloaded from, https://www.kaggle.com/datasets/sampadab17/netwo rk-intrusion-detection
IntrusionDetectionEvaluationDataset,thatisavailable at,https://www.unb.ca/cic/datasets/ids-2017.html
IoT Intrusion Dataset, available at, https://sites.google.com/view/iot-network-intrusiondataset/home?pli=1
IoT Network Intrusions, that are available at https://ieee-dataport.org/open-access/iot-networkintrusion-dataset
SIMARGL, which are available at, https://www.kaggle.com/datasets/h2020simargl/sima rgl2021-network-intrusion-detection-dataset
All these sets were combined to identify DDoS, Masquerading, Sybil, Spoofing, Spying and Man-in-theMiddleattacks.Atotalof1millionsampleswerecollected with 7 different classes. The set was segregated into 70%
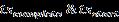
training, and 15% each of validation & testing operations. Based on this strategy, the accuracy of classification was evaluatedandcomparedwithADPONN[2],MPC[16],and NNFAT[24]intable2w.r.t.NumberofEvaluatedSamples (NES)asfollows,
Table-2:Attackdetectionaccuracyfordifferentusecases
© 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page441

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
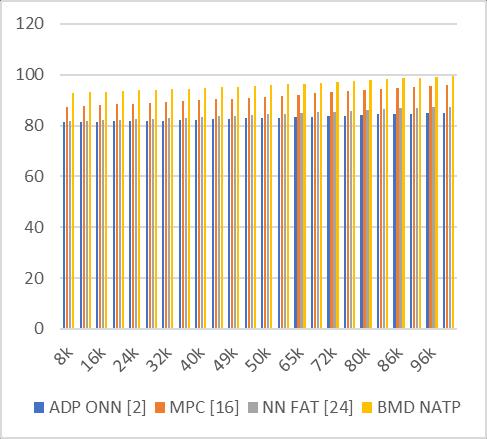
Chart-1:Attackdetectionaccuracyfordifferentusecases
Asperthisevaluationandchart1,itcanbeobservedthatthe proposed model is able to improve the classification accuracyby14.5%whencomparedwithADPONN[2],3.9% whencomparedwith[R2[,and10.4%whencomparedwith NNFAT[24],whichmakesitusefulforawidevarietyofrealtime network scenarios.Thisaccuracyisimproveddue to integrationofmultimodalfeaturesetsalongwithensemble classificationoperations.Similarly,theprecisionlevelscan beobservedfromtable2asfollows,
Table-3:Attackdetectionprecisionfordifferentusecases
Chart-2:Attackdetectionprecisionfordifferentusecases
Asperthisevaluationandchart2,itcanbeobservedthatthe proposed model is able to improve the classification precisionby9.5%whencomparedwithADPONN[2],1.9% whencomparedwith[R2[,and12.5%whencomparedwith NNFAT[24],whichmakesitusefulforawidevarietyofrealtimenetworkscenarios.Thisprecisionisimproveddueto integration of multimodal feature sets with Bacterial Foraging Optimization (BFO) and ensemble classification operations.Similarly,therecalllevelscanbeobservedfrom table4asfollows,

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
Asperthisevaluationandchart3,itcanbeobservedthatthe proposedmodelisabletoimprovetheclassificationrecallby 16.4% when compared with ADP ONN [2], 6.5% when comparedwith[R2[,and6.2%whencomparedwithNNFAT [24],whichmakesituseful fora widevarietyof real-time networkscenarios.Thisrecallisimprovedduetointegration of multimodal feature sets with Bacterial Foraging Optimization(BFO)andensembleclassificationoperations. Similarly,thedelaylevelscanbeobservedfromtable5as follows,
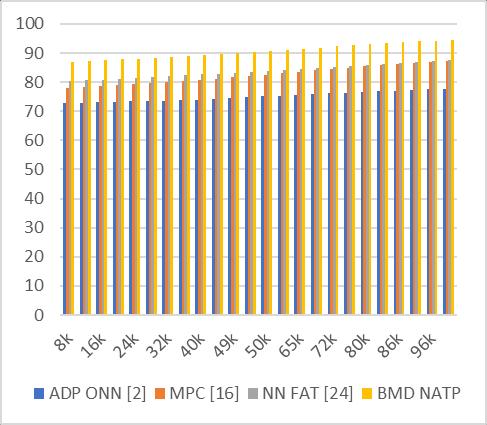
Table-4:Speedofattackdetectionfordifferentusecases

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
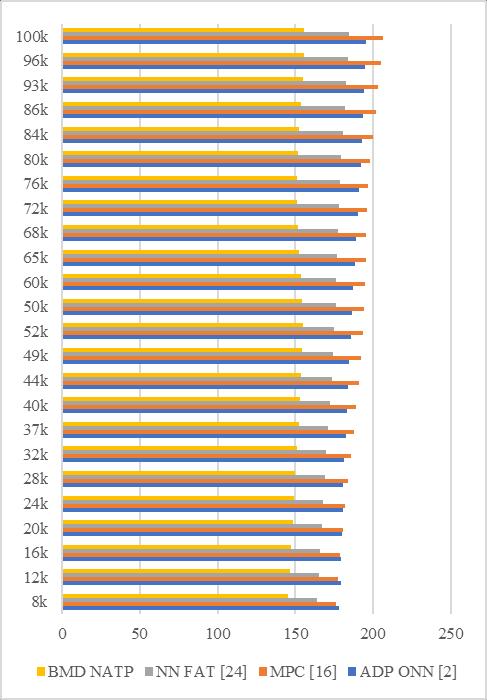
Chart 4:Speedofattackdetectionfordifferentusecases
Asperthisevaluationandchart4,itcanbeobservedthatthe proposedmodelisabletoimprovethespeedofclassification by10.5%whencomparedwithADPONN[2],18.3%when comparedwith[R2[,and6.5%whencomparedwithNNFAT [24],whichmakesitusefulforawidevarietyofhigh-speed network scenarios. This speed is improved due to integration of Bacterial Foraging Optimization (BFO) and ensemble classification operations. Due to these optimizations,theproposedmodeliscapableofimproving attackidentificationperformanceunderstaticanddynamic networkscenarios.
The proposed attack identification model first gathers extensive information sets specific to attacks, using these sets to extract multidomain features. Frequency analysis, energy analysis, window-based analysis, and spatiotemporal analysis performed by these capabilities help identify traffic patterns for particular attack types. A BacterialForagingOptimizer(BFO)processestheidentified trafficpatternstohelpidentifyattack-specificfeaturesets withahighdensity.Combiningensemblesofweakclassifiers whoseperformanceisimprovedbyboostingoperations,the chosen features are classified. The model can recognize
dynamicnetworkattacksthankstotheseclassifiers,which include Nave Bayes (NB), Multilayer Perceptron (MLP), k NearestNeighbors(kNN),SupportVectorMachine(SVM), and Logical Regression (LR). When accuracy levels for various scenarios were estimated, it was found that the proposedmodelwasabletoincreaseclassificationaccuracy by 14.5% in comparison to ADP ONN [2], 3.9% in comparison to [R2], and 10.4% in comparison to NN FAT [24],makingitusefulforawiderangeofreal-timenetwork scenarios. The integration of multimodal feature sets and ensembleclassificationoperationsenhancesthisaccuracy. While it was found that the proposed model is able to increaseclassificationprecisionwhencomparedtoADPONN [2], [R2], and NN FAT [24] by 9.5%, 1.9%, and 12.5%, respectively.Thismakesitusefulforawiderangeofrealtime network scenarios. The integration of multimodal featuresetswithBacterialForagingOptimization(BFO)and ensemble classification operations has improved this precision.Itwasdiscoveredthattheproposedmodel,when assessedintermsofconsistencylevels,isabletoincrease theclassificationrecallby16.4%whencomparedwithADP ONN[2],6.5%whencomparedwith[R2],and6.2%when compared with NN FAT [24], making it useful for a wide range of real-time network scenarios. By combining multimodal feature sets with Bacterial Foraging Optimization(BFO)andensembleclassificationoperations, thisrecallisimproved.Itwasfoundthattheproposedmodel canimproveclassificationspeedby10.5%whencompared toADPONN[2],18.3%whencomparedto[R2],and6.5% when compared to NN FAT [24], making it useful for a varietyofhigh-speednetworkscenarios.Theintegrationof Bacterial Foraging Optimization (BFO) and ensemble classification operations has increased this speed. These improvementsenabletheproposedmodeltoenhanceattack identification performance in both static and dynamic network environments. Future testing of the proposed model's performance on more varied attack types will be necessary, and it can be expanded using transfer learning techniques for diverse attack types. Furthermore, by incorporating Q-Learning, Auto Encoder, and other incremental learning techniques, this performance can be enhanced. These techniques will help identify real-time attacksforvariousnetworkscenarios.
[1] "Security enhanced dynamic bandwidth allocation algorithmagainstdegradationattacksinnextgeneration passive optical networks," in Journal of Optical Communications and Networking, vol. 13, no. 12, pp. 301-311,December2021,doi:10.1364/JOCN.434739.
[2] H. Niu, C. Bhowmick and S. Jagannathan, "Attack DetectionandApproximationinNonlinearNetworked Control Systems Using Neural Networks," in IEEE TransactionsonNeuralNetworksandLearningSystems,

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
vol. 31, no. 1, pp. 235-245, Jan. 2020, doi: 10.1109/TNNLS.2019.2900430.
[3] C. Wu, X. Zhao, B. Wang, W. Xing, L. Liu and X. Wang, "Model-Based Dynamic Event-Triggered Control for Cyber-Physical Systems Subject to Dynamic QuantizationandDoSAttacks,"inIEEETransactionson NetworkScienceandEngineering,vol.9,no.4,pp.24062417, 1 July-Aug. 2022, doi: 10.1109/TNSE.2022.3163783.
[4] D. An, F. Zhang, Q. Yang and C. Zhang, "Data Integrity AttackinDynamicStateEstimationofSmartGrid:Attack ModelandCountermeasures,"inIEEETransactionson AutomationScienceandEngineering,vol.19,no.3,pp. 1631-1644, July 2022, doi: 10.1109/TASE.2022.3149764.
[5] L. Huang, J. Guo and B. Li, "Observer-Based Dynamic Event-Triggered Robust H∞ Control of Networked ControlSystemsUnderDoSAttacks,"inIEEEAccess,vol. 9, pp. 145626-145637, 2021, doi: 10.1109/ACCESS.2021.3121689.
[6] F.Han,Z.Wang,H.Dong,F.E.AlsaadiandK.H.Alharbi, "A Local Approach to Distributed $H_{\infty }$Consensus State Estimation Over Sensor Networks Under Hybrid Attacks: Dynamic Event-Triggered Scheme," in IEEE Transactions on Signal and InformationProcessingoverNetworks,vol.8,pp.556570,2022,doi:10.1109/TSIPN.2022.3182273.
[7] D.Ding,H.Liu,H.DongandH.Liu,"ResilientFilteringof Nonlinear Complex Dynamical Networks Under RandomlyOccurringFaultsandHybridCyber-Attacks," in IEEE Transactions on Network Science and Engineering, vol. 9, no. 4, pp. 2341-2352, 1 July-Aug. 2022,doi:10.1109/TNSE.2022.3163258.
[8] H.Yan,J.Wang,H.Zhang,H.ShenandX.Zhan,"EventBased Security Control for Stochastic Networked Systems Subject to Attacks," in IEEE Transactions on Systems,Man,andCybernetics:Systems,vol.50,no.11, pp. 4643-4654, Nov. 2020, doi: 10.1109/TSMC.2018.2856819.
[9] Y. Zhou, M. Bi, X. Zhuo, Y. Lv, X. Yang and W. Hu, "PhysicalLayerDynamicKeyEncryptioninOFDM-PON System Based on Cellular Neural Network," in IEEE PhotonicsJournal,vol.13,no.2,pp.1-14,April2021,Art no.7200314,doi:10.1109/JPHOT.2021.3059369.
[10] A. Aydeger, M. H. Manshaei, M. A. Rahman and K. Akkaya, "Strategic Defense Against Stealthy Link FloodingAttacks:ASignalingGameApproach,"inIEEE TransactionsonNetworkScienceandEngineering,vol. 8, no. 1, pp. 751-764, 1 Jan.-March 2021, doi: 10.1109/TNSE.2021.3052090.
[11] C. Peng, J. Wu and E. Tian, "Stochastic EventTriggered H∞ Control for Networked Systems Under Denial of Service Attacks," in IEEE Transactions on Systems,Man,andCybernetics:Systems,vol.52,no.7, pp. 4200-4210, July 2022, doi: 10.1109/TSMC.2021.3090024.
[12] D. Du, C. Zhang, X. Li, M. Fei and H. Zhou, "Attack DetectionforNetworkedControlSystemsUsingEventTriggered Dynamic Watermarking," in IEEE TransactionsonIndustrialInformatics,vol.19,no.1,pp. 351-361,Jan.2023,doi:10.1109/TII.2022.3168868.
[13] J. Lian and X. Huang, "Resilient Control of Networked Switched Systems Against DoS Attack," in IEEETransactionsonIndustrialInformatics,vol.18,no. 4, pp. 2354-2363, April 2022, doi: 10.1109/TII.2021.3097722.
[14] X.Chen,S.Hu,Y.Li,D.Yue,C.DouandL.Ding,"CoEstimation of State and FDI Attacks and Attack CompensationControl for Multi-Area LoadFrequency Control Systems Under FDI and DoS Attacks," in IEEE Transactions on Smart Grid, vol. 13, no. 3, pp. 23572368,May2022,doi:10.1109/TSG.2022.3147693.
[15] L.Qiu,L.Dai,U.Ahsan,C.Fang,M.NajariyanandJ. Pan,"ModelPredictiveControlforNetworkedMultiple Linear Motors System Under DoS Attack and Time Delay,"inIEEETransactionsonIndustrialInformatics, vol. 19, no. 1, pp. 790-799, Jan. 2023, doi: 10.1109/TII.2021.3139127.
[16] M. Zhang et al., "Control Plane Reflection Attacks and Defenses in Software-Defined Networks," in IEEE/ACMTransactionsonNetworking,vol.29,no.2, pp. 623-636, April 2021, doi: 10.1109/TNET.2020.3040773.
[17] L. Zha, R. Liao, J. Liu, X. Xie, E. Tian and J. Cao, "DynamicEvent-TriggeredOutputFeedbackControlfor NetworkedSystemsSubjecttoMultipleCyberAttacks," inIEEETransactionsonCybernetics,vol.52,no.12,pp. 13800-13808, Dec. 2022, doi: 10.1109/TCYB.2021.3125851.
[18] D. Liu and D. Ye, "Pinning-Observer-Based Secure Synchronization Control for Complex Dynamical NetworksSubjecttoDoSAttacks,"inIEEETransactions onCircuitsandSystemsI:RegularPapers,vol.67,no. 12, pp. 5394-5404, Dec. 2020, doi: 10.1109/TCSI.2020.3016994.
[19] J. Wang, Y. Tan, J. Liu and Y. Zhang, "Topology Poisoning Attack in SDN-Enabled Vehicular Edge Network,"inIEEEInternetofThingsJournal,vol.7,no. 10, pp. 9563-9574, Oct. 2020, doi: 10.1109/JIOT.2020.2984088.
[20] S.Hu,D.Yue,Z.Cheng,E.Tian,X.XieandX.Chen, "Co-DesignofDynamicEvent-TriggeredCommunication Scheme and Resilient Observer-Based Control Under Aperiodic DoS Attacks," in IEEE Transactions on Cybernetics, vol. 51, no. 9, pp. 4591-4601, Sept. 2021, doi:10.1109/TCYB.2020.3001187.
[21] R.Liu,F.HaoandH.Yu,"OptimalSINR-BasedDoS Attack Scheduling for Remote State Estimation via Adaptive Dynamic Programming Approach," in IEEE Transactions on Systems, Man, and Cybernetics: Systems,vol.51,no.12,pp.7622-7632,Dec.2021,doi: 10.1109/TSMC.2020.2981478.
© 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008 Certified Journal | Page445

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072
[22] P.Chen,D.Zhang,L.YuandH.Yan,"DynamicEventTriggeredOutputFeedbackControlforLoadFrequency ControlinPowerSystemsWithMultipleCyberAttacks," inIEEETransactionsonSystems,Man,andCybernetics: Systems,vol.52,no.10,pp.6246-6258,Oct.2022,doi: 10.1109/TSMC.2022.3143903.
[23] R. Biswas and J. Wu, "Optimal Filter Assignment PolicyAgainstDistributedDenial-of-ServiceAttack,"in IEEE Transactions on Dependable and Secure Computing,vol.19,no.1,pp.339-352,1Jan.-Feb.2022, doi:10.1109/TDSC.2020.2987301.
[24] A.Amini,A.Asif,A.MohammadiandA.Azarbahram, "Sampled-Data Dynamic Event-Triggering Control for Networked Systems Subject to DoS Attacks," in IEEE TransactionsonNetworkScienceandEngineering,vol. 8, no. 3, pp. 1978-1990, 1 July-Sept. 2021, doi: 10.1109/TNSE.2021.3070804.
[25] S.J.Yoo,"Neural-Network-BasedAdaptiveResilient DynamicSurfaceControl AgainstUnknownDeception Attacks of Uncertain Nonlinear Time-Delay CyberphysicalSystems,"inIEEETransactionsonNeural Networks and Learning Systems, vol. 31, no. 10, pp. 4341-4353, Oct. 2020, doi: 10.1109/TNNLS.2019.2955132.
[26] Y.Zhouetal.,"HyperSight:TowardsScalable,HighCoverage,andDynamicNetworkMonitoringQueries,"in IEEEJournalonSelectedAreasinCommunications,vol. 38, no. 6, pp. 1147-1160, June 2020, doi: 10.1109/JSAC.2020.2986690.
[27] Z. Niu, Q. Li, C. Ma, H. Li, H. Shan and F. Yang, "IdentificationofCriticalNodesforEnhancedNetwork DefenseinMANET-IoTNetworks,"inIEEEAccess,vol.8, pp. 183571-183582, 2020, doi: 10.1109/ACCESS.2020.3029736.
[28] K.Aida,K.Yamada,R.HotchiandR.Kubo,"Dynamic Network Path Provisioning and Selection for the DetectionandMitigationofDataTamperingAttacksin NetworkedControlSystems,"inIEEEAccess,vol.9,pp. 147430-147441, 2021, doi: 10.1109/ACCESS.2021.3124024.
[29] T.Zhang,C.Xu,B.Zhang,J.Shen,X.KuangandL.A. Grieco, "Toward Attack-Resistant Route Mutation for VANETs: An Online and Adaptive Multiagent Reinforcement Learning Approach," in IEEE TransactionsonIntelligentTransportationSystems,vol. 23, no. 12, pp. 23254-23267, Dec. 2022, doi: 10.1109/TITS.2022.3198507.
[30] Y. Yang, X. Wei, R. Xu, L. Peng and L. Liu, "GameBased Channel Access for AoI-Oriented Data TransmissionUnderDynamicAttack,"inIEEEInternet ofThingsJournal,vol.9,no.11,pp.8820-8837,1June1, 2022,doi:10.1109/JIOT.2021.3116142.
[31] M. Huang, K. F. E. Tsang, Y. Li, L. Li and L. Shi, "Strategic DoS Attack in Continuous Space for CyberPhysical Systems Over Wireless Networks," in IEEE TransactionsonSignalandInformationProcessingover
Networks, vol. 8, pp. 421-432, 2022, doi: 10.1109/TSIPN.2022.3174969.
[32] L.D.Tsobdjou,S.PierreandA.Quintero,"AnOnline Entropy-BasedDDoSFloodingAttackDetectionSystem With Dynamic Threshold," in IEEE Transactions on Network and Service Management, vol. 19, no. 2, pp. 1679-1689, June 2022, doi: 10.1109/TNSM.2022.3142254.
[33] V. -T. Ngo and Y. -C. Liu, "Distributed Consensus Control of Networked Robotic Systems With Dynamic Leader Under Time-Varying Delays and Denial-ofService Attacks," in IEEE Access, vol. 10, pp. 9266392672,2022,doi:10.1109/ACCESS.2022.3203588.
[34] V. -T. Ngo and Y. -C. Liu, "Distributed Consensus Control of Networked Robotic Systems With Dynamic Leader Under Time-Varying Delays and Denial-ofService Attacks," in IEEE Access, vol. 10, pp. 9266392672,2022,doi:10.1109/ACCESS.2022.3203588.
[35] P. Rani, Kavita, S. Verma and G. N. Nguyen, "Mitigation of Black Hole and Gray Hole Attack Using Swarm Inspired Algorithm With Artificial Neural Network," in IEEE Access, vol. 8, pp. 121755-121764, 2020,doi:10.1109/ACCESS.2020.3004692.
[36] Y. Zhang, C. Peng, S. Xie and X. Du, "Deterministic NetworkCalculus-BasedH∞LoadFrequencyControlof MultiareaPowerSystemsUnderMaliciousDoSAttacks," in IEEE Transactions on SmartGrid,vol. 13, no. 2, pp. 1542-1554, March 2022, doi: 10.1109/TSG.2021.3133961.
[37] Q. Geng, L. Zhao, L. Li and F. Liu, "A Dynamic Controller Design for Trajectory Tracking Control of Wheeled Mobile Robot Under Stochastic Denial of ServiceAttacks,"inIEEETransactionsonCircuitsand SystemsII:ExpressBriefs,vol.69,no.8,pp.3560-3564, Aug.2022,doi:10.1109/TCSII.2022.3168304.
[38] G.Lietal.,"EnablingPerformant,FlexibleandCostEfficientDDoSDefenseWithProgrammableSwitches," inIEEE/ACMTransactionsonNetworking,vol.29,no.4, pp. 1509-1526, Aug. 2021, doi: 10.1109/TNET.2021.3062621.
[39] A. Bhardwaj, V. Mangat and R. Vig, "Hyperband TunedDeepNeuralNetworkWithWellPosedStacked Sparse AutoEncoder for Detection of DDoS Attacks in Cloud,"inIEEEAccess,vol.8,pp.181916-181929,2020, doi:10.1109/ACCESS.2020.3028690.
[40] B.-A.Dao,T.-T.Hoang,A.-T.Le,A.Tsukamoto,K. Suzaki and C. -K. Pham, "Correlation Power Analysis AttackResistedCryptographicRISC-VSoCWithRandom DynamicFrequencyScalingCountermeasure,"inIEEE Access, vol. 9, pp. 151993-152014, 2021, doi: 10.1109/ACCESS.2021.3126703.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sept 2025 www.irjet.net p-ISSN: 2395-0072

Dr. Nikita Bahaley holds a PhD in Computer Science Engineering. With over 13 years of teaching experience, she has made significant contributions to academia.Currently,sheservesas an Assistant Professor, inspiring students and advancing research. Her expertise lies in network secirity. Dr. Nikita is dedicated to fostering innovation and critical thinkinginherfield.Shecontinues to shape the future of computer sciencethrougheducation