
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
Diaeldin Izeldin Mohamed1 , Dr. Yasir Abdelgadir Mohamed2 , Dr. Sally D. Abualgasim3
1 University of Gezira Faculty of Engineering and Technology
Wad-Medani, Sudan
2 A’Sharqiyah University College of Business Administration/MIS Ibra, Oman
3 University of Gezira Faculty of Engineering and Technology Wad-Medani, Sudan
Abstract - The impact of the Internet of Things (IoT) on our daily lives is substantial. Protection of confidence and privacy in data andresourceexchanges is a primaryfunctionofaccess controlsystemsandother associatedsecuritytechnologies.As per the security policy and access control needs, an access controlframeworkenablessecuritytosafeguardtheresources in ubiquitous computing. However, the vast number of disparate devices in an IoT setting presents significant challenges in access control, raising the possibility of data tampering and leakage. The main goal of this paper is to conduct a comprehensiveassessment ofthecurrentIoTaccess control frameworks based on the IoT security requirements. This review systematically evaluates frameworks such as RBAC, ABAC, Capability-basedAccess Control(CapBAC),edgeassisted, and blockchain-enabled models. Each framework is compared against IoT-specific requirements including lightweight operation, decentralization, privacy, mobility, robustness, and cross-domain federation. The analysis highlights both strengths and persistent gaps, particularly in robustness, real-timeadaptability, and identitymanagement As a result, it is proposed focusing on the existing shortcomings to produce an access control framework for managing highly distributed resources in the IoT that aligns with the necessary security standards.
Keywords: IoT Security, Access Control framework, Security, Privacy)
Currently, an estimated two billion individuals around theworldusetheInternetforvariouspurposes,including web browsing, email communication, multimedia access, online gaming, and interaction through social networkingplatforms.Thisnumberisexpectedtogrowas more people connect to the global information and communication infrastructure, related to the use of the Internet as a global platform for letting machines and smart objects communicate, compute, coordinate,
share and gather information about people, such as their location, activity, or even their feelings. Some of this informationisconfidentialandshouldbeaccessedonlyby authorized entities. The frequency and complexity of attackstargetingembeddeddevicesareexpectedtoincrease, making it essential to implement stronger security measures[1][2].
Access control represents a key security technology for protecting the trust and the privacy which related to the exchange of data and resources. The IoT environment introduces new challenges in access control because of dealingwithahugenumberofheterogeneousthingswhich leadtotamperwithorleakedthesensitivedatabyhackers [3]. Actually, the IoT systems are still facing the lack of providingasecureenvironmentforIoTdevicesinteractions [4][5].Accesscontrolframeworkfacilitatesthesecurityto protecttheresourcesinpervasivecomputingfromthemost hackersaccordingtothesecuritypolicyandaccesscontrol requirements.Butalso,weareintheneedtofacilitatethe security and the performance to cope up with IoT environment nature which introduces new challenges in accesscontrol.Thisstudyseekstoanswer:(1)Whichaccess controlframeworkshavebeenproposedforIoT?(2)Howdo theyalignwithIoT-specificsecurityrequirements?(3)What gapsremainforfutureframeworks?
Thespecificobjectivesofthisreviewincludes:(i)toclassify existing access control paradigms for IoT (RBAC, ABAC, CapBAC, edge-assisted, blockchain-based, and hybrid models);(ii)to evaluatetheiralignmentwithIoT security requirements; and (iii) to identify open challenges and outlinepotentialresearchdirectionsfornext-generationIoT accesscontrolframeworks
DespiteextensiveworkonRBAC,ABAC,CapBAC,blockchain, and edge-assisted models, no single framework fully addressesrobustness,real-timeadaptability,andfederated identity management in IoT ecosystems. This review

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
identifies these gaps and proposes directions for nextgenerationframeworks.
The Internet of Things (IoT) is crucial in enabling the delivery of a wide range of services with greater effectiveness and efficiency for end users. However, this advancement also brings about significant security and privacyconcerns.Theseconcernsstemfrom:(i)theinherent complexityofIoTecosystems,whichinvolvediversesensors and devices operated by different entities, and (ii) the growingthreatposedbyanincreasingnumberofmalicious actors. An access control framework is a vital security approach designed to restrict resource access to only verifiedandauthorizedusers.Itisessentialforbuildingand maintainingsecurecomputingenvironments.Researchers proposed some Access Control Frameworks (ACF) for IoT environment.
The Internet of Things (IoT) refers to a system in which variousentitiescandetect,gather,andtransmitdatafrom thephysicalenvironmentviatheinternet.Thisinformation canthenbeanalyzedandutilizedformultipleapplications. In the IoT ecosystem, a “thing” can represent a person, a place,atimestamp,orevenaspecificcondition.Essentially, IoT involves the interconnection of devices that communicateandexchangeinformationovertheinternet. These devices, equipped with embedded sensors and microchips, are individually identifiable and trackable. By leveraging this technology, we can build intelligent environments. The primary aim of IoT is to bridge the physical world with digital networks, enabling seamless interaction between devices, machinery, and the work environment. With the aid of IoT sensors, data can be transferredbetweendevicesautomatically,withouttheneed forhumaninput.Devicesproduceandprocesslargevolumes of sensitive data and valuable information, making them attractive targets for a wide range of cyber-attacks [6] However,theopennatureofIoTsystemshasledtoarapid riseinsecurityrisks.Asaresult,verifyingthelegitimacyof communicating entities has become a critical security concern[7]
Generally,the IoTsystem consists ofthreedistinctlayers: theperceptionlayer,thenetworklayer,andtheapplication layer. The perception layer is mainly about information collection, it captures data from the physical world, interprets human social behavior, identifies objects, and facilitates their control. Network layer transforms and processes data in order to offer seamless access for the perceptionlayer,allowingtheapplicationlayertodeliverits correspondingservices.Applicationlayeroffersallsortsof context-awareservicesseamlesslyandsupportsintelligent computingandtheallocationofresources.AtrustworthyIoT systemdemandsrobustcooperationamongitslayersaswell
as high performance from each one individually and the wholesystemConcerningprivacyandsecurity.TheIoTmust guaranteethesecurityofwholesystemamongalllayers[8]. AcriticaldistinctioninIoTenvironmentsisthattraditional enterprise access control models cannot easily adapt to dynamic contexts, device mobility, and cross-domain interoperability.Therefore,researchersincreasinglyclassify IoTaccesscontrolframeworksintofivecategories:(1)RoleBased Access Control (RBAC), (2) Attribute-Based Access Control (ABAC), (3) Capability-Based Access Control (CapBAC), (4) edge-assisted enforcement, and (5) blockchain-enabledframeworks.
AccesscontrolplaysanimportantroleinIoTenvironments toregulatetheexchangeofdataandresources.Therefore,by leveraging an access control framework, IoT systems can deliverappropriatetrustservicesbasedonspecificrequests Therearerareresearchesonaccesscontrolframework in the context of the IoT. Although current techniques have made the concept of the IoT practically achievable, numerouschallengesstillhinderthelarge-scaledeployment ofIoTapplicationsinreal-worldenvironments[9][10]
Thereliabilityofanaccesscontrolframeworklargelyrelies on the integrity of its core components. As illustrated inFig-1,theprimaryelementsoftheframeworkinclude:the Initiator, the Target, the Access Control Enforcement Function (AEF), and the Access Control Decision Function (ADF)[11].
Present Access Request
Initiator AEF
Submit Access Request Target
Decision Decision Request
ADF
Initiators submit access requests, each specifying the operationtobeperformedonatarget.TheAccessControl EnforcementFunction(AEF)actsasamediatorforaccess requests.ItforwardsdecisionrequeststotheAccessControl DecisionFunction(ADF),whichdetermineswhetheraccess shouldbegrantedordenied.Basedonthedecisionreceived, theAEFenforcesthecorrespondingaccesscontrolpolicy

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
The IoT security is a prime concern. Building secure IoT systems requires a clear understanding of their unique security requirements, as this knowledge forms the foundation for designing robust and resilient IoT architectures[12].Someofthem(muchmorespecifictothe IoTcontext)aredescribedbelow.Theserequirementsserve as the evaluation criteria in our review. Each existing frameworkdiscussedinSection4ismappedagainstthem, allowingacomparativeviewofhowwellcurrentsolutions addressIoT-specificchallenges.
1) Light-Weight Solutions: When proposing security measuresfortheInternetofThings(IoT),itisessentialto account for the limited resources of IoT devices and prioritize lightweight security approaches. These constraints often include restricted processing power, whichcanlimitthetypesofcryptographicalgorithmsand security protocols that can be implemented effectively. Therefore,lightweightsecuritymechanismsshouldstrike a balance between the strength of the cryptographic methods used and the need for energy-efficient communication. This involves optimizing power consumptionwhilestillmaintaininganacceptablelevelof security[13]
2) DecentralizedManagement:TheIoTrepresentsavast andcontinuallyexpandingnetworkofconnecteddevices. Givenitsscaleandcomplexity,purelycentralizedsecurity solutionsareoftenimpractical,leadingtoconcernsover scalability,latency,andsinglepointsoffailure.Asaresult, IoT security frameworks must be flexible enough to operate across both centralized and decentralized architectures. Decentralized approaches (such as distributed trust models, blockchain integration, and edge/fog computing) offer improved scalability, fault tolerance, and localized decision-making capabilities. Thesefeaturesareespeciallyimportantindynamicand heterogeneousIoTenvironmentswhereresponsiveness andresiliencearecritical[14]-[17].
3) End-to-EndSecurity:TheIoTisexpectedtobenotonly vast in scale but also characterized by significant heterogeneity, including a broad range of devices, platforms,networkingprotocols,andtechnologies.Data transmissions will often span multiple administrative boundaries and operate over diverse network infrastructures. As such, security mechanisms must be capableofprovidingend-to-endprotectionsafeguarding dataconfidentiality,integrity,andauthenticitythroughout itsentirejourneyregardlessoftheunderlyingtechnology orownershipdomain[18][19].
4) IdentityManagement:IoTsecuritymustofferrobust mechanismsformanagingtheidentitiesofbothdevices andusers,aswellasflexibleapproachesforhandlingthe dynamicrelationshipsamongtheseidentities[20].
5) Privacy:Similartoidentity,thesizeandcomplexityof IoTrequiresspecialattentiontotheprivacyofbothusers anddatainallitsvariousforms[21]-[25].
6) Mobility/Dynamic:ThemobilityofIoTdevices,users, andentitiesintroducesadditionalcomplexitytosecurity management. Security frameworks must accommodate seamless transitions across different jurisdictions, administrativedomains,andnetworkenvironmentswhile maintaining data confidentiality, integrity, and access control. These solutions must enable interoperable communicationandsecureinformationexchangebetween heterogeneous devices and users, regardless of their physicalornetworklocation.Moreover,theymustsupport mobile access to applications and data, dynamically adaptingtochangesinsystemcontext,location,anduser behavior. Leveraging location-aware and context-aware servicesisessentialtoenhancereal-timeresponsiveness and ensure that security remains robust even in highly dynamicanddistributedIoTenvironments[26]-[28]
7) Scalability/IncrementalDeployment:DuetothelargescalenatureofIoTecosystems,thesesystemsareexpected toexpandandevolveevenaftertheirinitialdeployment phase.Asaresult,securityframeworksmustbeadaptable, enablingthedynamiconboardingandremovalofdevices and users, while also supporting continuous updates to systemcapabilities[29]-[31].
8) Robust and Reliable: IoT ecosystems face unique robustnesschallengesstemmingfromfactorslikedevice mobility,hardwarefaults,andtheexpandinglandscapeof attacksurfaces.Toaddressthis,securityframeworksmust incorporateself-healingcapabilities,enablingautomatic detection and remediation of faults without manual intervention. Given the highly dynamic behavior characteristic of IoT environments, real-time defensive responsesareessential.Theserequirementscollectively emphasizetheneedforreal-timeoperation,reliabilityof operations, data validity and freshness, defense against attacks,andfault-handlingcapabilities[32]-[34].
9) Composition/Heterogeneity/Interoperability:TheIoT integrates a wide range of devices, services, and data sourcestodelivercomplexanddiverseapplicationstoend users.ThiscompositionalnatureofIoT wheresystems dynamically assemble functionalities from distributed components introduces multiple security challenges. Propersecuritycontrolsmustbeappliedateverystageof the composition process, from data generation to aggregation and service delivery. Furthermore, these controlsmustbepreservedend-to-endacrosstheentire systemlifecycle.GiventheheterogeneouslandscapeofIoT (comprising various device types, communication protocols, operating systems, and vendor platforms) securitysolutions mustbedesignedtoaccommodate interoperability whilemaintainingconsistentprotection acrossalllayers[35]-[37].

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
10) FederationinAdministrationDomains: IntheIoT, data and services are often provided by multiple cooperating domains. IoT security solutions must be designedtosupportpolicyinteroperability,enablingthe definition, enforcement, and coordination of security policies across diverse administrative domains. These solutions should ensure that access control, authentication,anddataprotectionmechanismsrespect the individual requirements of each domain while enablingseamlesscollaborationbetweenthem[38]-[40]
This review followed a structured approach to identify, classify, and evaluate access control frameworks for IoT. Academic databases such as IEEE Xplore, ACM Digital Library, SpringerLink, and ScienceDirect were searched using combinations of keywords including “IoT access control,” “RBAC,” “ABAC,” “CapBAC,” “blockchain-based access control,” and “edge computing security” Studies published between 2010 and 2024 were considered, with inclusion criteria focusing on frameworks that explicitly addressIoTsecurityrequirements.Eachselectedframework wasthenanalyzedandcomparedagainstthetenIoTsecurity requirementsoutlinedinSection3.
Accesscontrolframeworkfacilitatesthesecuritytoprotect theresourcesinpervasivecomputingfromthemosthackers according to the security policy and access control requirements.Awiderangeofstudieshavecontributedto advancementsincloudaccesscontrol.In2010aframework is provided by Machulak, et al. It separates access control fromwebapplicationsbyofferingitthroughanindependent authorization server, which helps improve overall system efficiency. Users define and save access control rules for theirresourcesonthisexternalserver.Basedontheserules, the server determines whether access should be granted. Typically,theauthorizationserverissuesatokentousers, whichtheyusetoaccessprotectedresources[41]
Whileearlyframeworksfocusedlargelyoncloudandweb applications, IoT-specific research has expanded toward edge-assisted access control (e.g., Hsu et al. [45]), blockchain-backedsystems(e.g.,Yangetal.[47];Sunetal. [48]),andhybridRBAC/ABACapproaches(e.g.,Aftabetal. [49]). These solutions demonstrate improvements in decentralizationandscalabilitybutoftenneglectrobustness, identitylifecyclemanagement,andreal-timeadaptability.
In2013anovelaccesscontrolframeworktailoredforcloud environments is presented by Ghafoor, et al. it decouples accesscontrollogicfromcloudapplications.Thisapproach empowersuserstoconfigureandadministeraccesspolicies over their own resources, aligning with their individual security and privacy needs [42]. In 2017, Yu provided a comprehensive examination of how edge computing overcomestheconstraintsofconventionalcloudcomputing
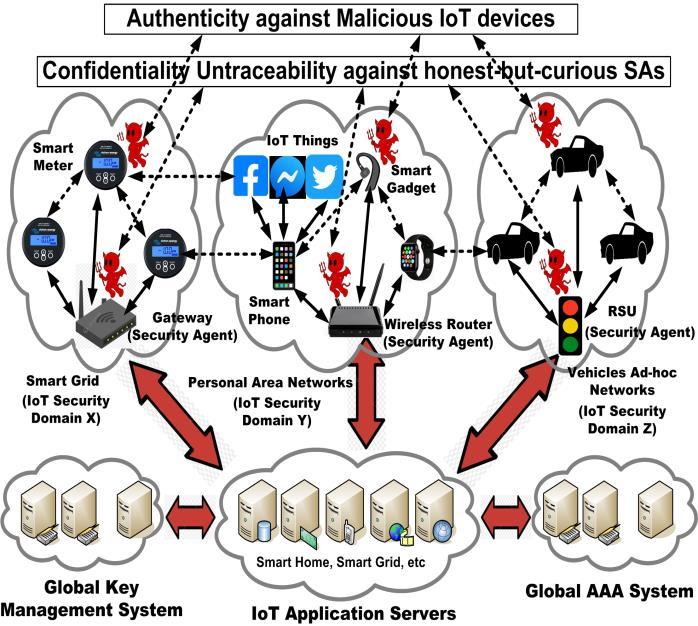
inIoTsettings.Thetextemphasizesthevitalsignificanceof edgecomputingindiminishingnetworklatency,mitigating bandwidth congestion, and augmenting real-time data processing.ThesefactorsarecriticalforIoTapplicationsthat need prompt reaction times, such as smart cities, smart grids, and autonomous cars. The article classifies several edge computing architectures and evaluates their performanceintermsofreactiontime,energyconsumption, andcomputationalcapability.Additionally,ittacklessecurity problems by suggesting a methodology for assessing the securitymethodsofIoTnetworksthatareintegratedwith edge computing. The research highlights the potential of edgecomputingtobeakeyenablerinthefutureevolutionof IoTduetothegrowingnumberofIoTdevicesandtheirdata. Edgecomputingoffersenhancedscalability,flexibility,and efficiencyindealingwithlarge-scaledatainproximitytoits origin.Thisarticleisrelevanttothestudyonaccesscontrol in IoT. It shows how edge computing frameworks may improveresourcemanagementandsecurity.Thishelpsto addressthegapbetweenthepresentsecurityneedsofIoT andthecapabilitiesofconventionalcloudcomputing [43] Also, in 2017, Misra, et al. proposed an access control framework to enable the use of in-network cached data within ICN-enabled wireless edge environments. It allows authorized users to directly retrieve and utilize cached content without needing real-time authentication from a central provider or content-serving router. By leveraging cacheddata,theframeworkminimizestheeffectsofserver outages,lowerscontentdeliverylatency,andensuresthat only legitimate users are granted access [44]. Another research in 2018, Hsu, et al. introduced a reconfigurable security framework leveraging edge computing, which operatesonnear-useredgedevices.Used:(i)Thestandard authentication framework (EAP) to enable adaptability acrossmultiplesecurityprotocolsbasedonAuthorization, AuthenticationandAccounting(AAA)framework.(ii)access control techniques role-based access control (RBAC) and attribute-basedaccesscontrol(ABAC)toenableadaptable implementation of different security measures by representing each security service as a distinct object. Actually,IoTsecuritychallengeshadbeentriedtoovercome withoutmodificationoftheexistingarchitectureoraltering the standard protocol operations of IoT applications. As shown on Fig -2 the framework introduces a dedicated componenttermedthesecurityagent(SA),whichresideson near-useredgeinfrastructuresuchaswirelessrouters,base stations, or service routers. The SA typically possesses greater computational capabilities compared to typical resource-constrainedIoTdevices,itisleveragedtooffload theburdenofcryptographicoperationsfromtheselimited devices. In other words, the framework focus on the key management issue for authentication and the resourceconstrained issue to achieve the deployment of computationally intensive cryptographic algorithms executable on near-user edge devices (ex: SA) using AAA frameworkandaccesscontroltechniques[45].

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
In 2019, Xue, et al. proposed a secure, efficient, and accountable edge-based access control framework (SEAF) forinformationcentricnetworks(ICN).Authenticationtakes place at the edge of the network to prevent unauthorized access right from the start. To enable anonymous authentication, a group signature scheme is employed. Additionally, a hash chain method is utilized to minimize overheadwhenusersrepeatedlyrequestthesamefile. Also, a revocation method is provided to make the framework more robust [46]. In 2020, Yang, et al. proposed a blockchain-based_access_control framework with privacy protection in cloud to handle the issue of illegal access to resourcesincloudbyhackersorcloudinternalmanagers. Theframeworkdesignateseachnode'sblockchainaccount address as its identity, while simultaneously establishing newaccesscontrolrulesfordatastoredinthecloud,which isencryptedandstoredinblockchain[47].In2021Sun,etal. integrated a permissioned blockchain, an access control system for IoT based on blockchain was developed using attribute-based access control (ABAC) and identity-based signature(IBS)mechanisms.Thisapproachensuressecurity, maintains lightweight performance, and supports crossdomainenvironments.Specifically,theIoTsystemisdivided into different function domains, named IoT domains. Subsequently,alocalblockchainledgerisestablishedwithin eachIoTdomain,allowingagreaternumberofIoTdevices to operate as nodes within the blockchain network. The distributedledgerlocallymaintainsrecordsofIoTdomain entity attributes, hashed policy file representations, and corresponding access control decisions. Meanwhile, a channeltechnologyisusedtoenablecrossdomainaccess, thesystememploysIBStoverifyandfilterlegitimateaccess requestswithineachIoTdomain,therebymitigatingtherisk ofDDoSattacks.Also,apolicydecisionpoint(PDP)selection algorithmisdesignedforselectingmultipleIoTdevices to
support real-time policy decision-making in a distributed environment(off-chain)[48].In2021,Aftab,etal.proposed anovelsecureanddynamicaccesscontrol(SDAC)modelfor the IoT networks. The model was a software-centric that joined RBAC and ABAC to allow the administrators or authorized entities to efficientlyenforce accesscontrol by simultaneouslygeneratingmultiplepermissionrules,which helpstoreduceadministratorloads[49].In2022,Sarfaraz, et al. proposed access chain model. It is a supply chain management(SCM)accesscontrolframework employs an attribute-based access control (ABAC) model to manage access permissions, ensuring that competing entities are restricted while still supporting network scalability. The system features a dual-ledger structure: local and global. Local ledgers handle the storage of business agreements between participantsand manage ABAC policies, whereas the global ledger is responsible for recording overall transactiondata[50].In2022,Deepakpresentedathorough examination of the ways in which blockchain technology might improve the security, privacy, and functional performanceofIoTinfrastructures.Thestatementhighlights the strong connection between the decentralized, unchangeable,andtransparentcharacteristicsofblockchain technologyandtheinherentweaknessesofIoTecosystems, namely in terms of data integrity, trust, and secure communication. The assessment covers a range of topics, suchasblockchainarchitecture,consensus processes,and applications,withaspecificemphasisonpracticalexamples thatdemonstratethetechnology'sabilitytotacklesignificant securityissuesintheInternetofThings(IoT).Inadditionto highlighting the advantages, the paper also examines the drawbacks and difficulties associated with merging blockchain with IoT, including issues of scalability and limitedresources.Thismakesitahelpfulsourceforscholars andprofessionalsinterestedinexploringtheconvergenceof these technologies. This review highlighted the persistent obstaclesinIoTsecuritythatastudymighttackle,namelyin accesscontrolframeworks[51]. In2024,VermaandRanga conducted a thorough analysis of the efficacy of several machine learning classifiers, such as individual classifiers andensembleapproaches,inidentifyingandreducingDenial of Service (DoS) assaults in IoT networks. The work demonstrated theadvantagesof ensembleapproachesfor intrusion detection in resource-constrained contexts via a thoroughperformanceevaluationutilizingseveraldatasets and real-time testing on IoT-specific hardware such as RaspberryPi.Thestudymadea majorcontributiontothe field of IoT security by showing how machine learning modelsmaybepracticallyusedandbyaddressingtheneed for strong, real-time intrusion detection systems that are specificallydesignedfortheparticularproblemsofIoT[52]
To synthesize the literature, we evaluated each representative framework against the ten IoT security requirementsoutlinedinSection3.Table1summarizesthis comparisonandhighlightsunderexploredareasthatmerit furtherinvestigation.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
IoT Security Requirements
0=Notsatisfy,1=Wellsatisfy,and2=Goodsatisfy.
Althoughmanyeffortshavebeenmadeindesigningefficient accesscontrolsolutionsforIoTwhichsatisfymosttheIoT securityrequirements,morestudyisexpectedtocoverthe restoftheIoTsecurityrequirements.
From the above “Comparison of Access Control Frameworks”,werealizeseveralIoTsecurityrequirements needmoreefforttobeachieved,like:
Robustness/Self-healing/Reliability/Real-time/Datafreshness: Considering the unique characteristics and securityrequirementsofIoTenvironments,thedesignof future IoT access control frameworks is expected to incorporate more inputs to its ADF to support ACF security under a wide range of diverse operational conditionstobeRobustness/Self-healing/Reliability/Realtime/Data-freshness.
Identitymanagement:Authorization,Authenticationand Accounting (AAA) framework is usually employed as identitymanagement.
For secure communication, devices must be properly authenticated before being granted privileged access to services. As heterogeneous devices have different environments surrounded by different hackers, these environments create challenges for defining any standard authentication and authorization ensuring that only authenticatedandauthorizeduserscanaccessthesystem anditsdataiscrucialforbuildingtrustandenablingsecure communication.Asolidnetworkmanagementframeworkis supported by monitoring resource utilization, conducting audits,andmaintainingdetailedreportinglogs[53].Wealso shouldbeabletousething’sidentitytoprotecttheresources throughchangingofauthority,automatically.
As access control systems evolve to support complex, distributed,anddata-intensiveenvironments,varioustradeoffsmustbecarefullymanaged.Thesetrade-offsinfluence thesystem’sscalability,security,trust,privacy,adaptability, andperformance.Belowisadiscussionofthesekeyareas:
1) Scalability vs. Security: Enhancing security mechanisms often introduces computational and communication overhead, which can negatively affect system scalability. For example, fine-grained access control models like ABAC provides high security and flexibility but are less scalable in large, distributed networksduetocomplexpolicyevaluation.
2) Trust vs. Privacy: Establishing trust often requires some level of identity verification or behavior tracking, which can compromise user privacy. For example, persistent identifiers may be needed for building reputation or trust models but can expose users to profiling.
3) ResourceConstraintsandCryptographicOverheads: Strong cryptographic techniques (e.g., public-key encryption, homomorphic encryption) provide high security but are often computationally expensive constrained devices such as IoT sensors and mobile nodes.
4) PolicyAdaptabilityvs.Complexity:Adaptivepolicies thatchangeinrealtimebasedoncontext(e.g.,location, behavior,devicestate)offerflexibilityandbettercontrol butintroducecomplexityinpolicycreation,management, andenforcement.
The design of access control frameworks in modern networks must strike a balance between performance, security,flexibility,andusability.Amulti-layeredapproach, combining cryptographic mechanisms, trust models, and

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
intelligentdecision-making,isessentialtoeffectivelymanage thesetrade-offs.
Accesscontrolconstitutesacriticaltoolinachievingrobust security.Thispaperoverviewstheexistingproposedaccess control frameworks and their applicability to satisfy IoT securityrequirements.WerealizedthatseveralIoTsecurity requirements need more effort to be achieved, like: robustness/self-healing/reliability/real-time/data-freshness andidentitymanagement.Accordingly,itisadvisedtofocus on the existing shortcomings to produce an IoT access control framework thatalignswiththe necessarysecurity standards. This review underscores the need for hybrid access control frameworks that combine the fine-grained decision-making of ABAC, the efficiency of CapBAC, the scalability of edge computing, and the auditability of blockchain Futureworkshouldexplorehybridframeworks combining ABAC’s fine granularity, CapBAC’s lightweight design,blockchain’sauditability,andedgecomputing’slow latency.IntegrationwithAI/MLforadaptivepolicydecisions andcompliancewithstandards(e.g.,ISO/IEC27001,NISTSP 800-183)willbecriticalforsustainableadoption.
[1] F.Liang,W.Yu,X.He,W.G.Hatcher,C.Lu,J.Lin,andX. Yang,“ASurveyontheEdgeComputingfortheInternet ofThings,”IEEEAccess,6,2018,pp.6900–6919.
[2] Y.Perwej,Q.Abbas,J.Dixit,N.Akhtar,andA.Jaiswal,“A Systematic Literature Review on the Cyber Security,” International Journal of Scientific Research and Management, Volume 9, 2021, pp. 669 – 710, 10.18535/ijsrm/v9i12.ec04.
[3] A. Alonso, F. Fernández, L. Marco and J. Salvachúa, "A modeltoenableapplication-scopedaccesscontrolasa serviceforIoTusingOAuth2.0," 201720thConference onInnovationsinClouds,InternetandNetworks(ICIN), 2017,pp.322-324,doi:10.1109/ICIN.2017.7899433.
[4] A.Alonso,A.Pozo,andJ.Salvachúa,“EvaluationofanIoT application-scoped access control model over a publish/subscribe architecture based on FIWAR,” Sensors, 20(15), 2020, 4341, https://doi.org/10.3390/s20154341
[5] H.Aldowah,S.Rehman,andI.Umar,(2020).“Trustin IoTsystems:Avisiononthecurrentissues,challenges, and recommended solutions,” In Advances in Smart Systems and Technologies, Springer, 2020, https://doi.org/10.1007/978-981-15-6048-4_29
[7] T. R. Thamburu and A.V. initha, “A Survey on Trust Management Models in Internet of Things Systems,” InternationalJournalofAdvancedResearchinComputer ScienceandSoftwareEngineering,January2017
[8] P WangandP Zhang,“AReviewonTrustEvaluationfor Internet of Things,” In Proceedings of the 9th EAI International Conference on Mobile Multimedia Communications (MobiMedia '16). ICST (Institute for Computer Sciences, Social-Informatics and TelecommunicationsEngineering),Brussels,BEL,2016, pp.34–39.
[9] L. Da Xu, W. He, and S. Li, "Internet of Things in industries:Asurvey," IEEETransactionson Industrial Informatics,vol.10,no.4,pp.2233–2243,Nov.2014.
[10] A. Ouaddah, H. Mousannif, A. A. Elkalam, and A. A. Ouahman,"AccesscontrolintheInternetofThings:Big challenges and new opportunities," *Computer Networks*,vol.112,pp.237–262,Jan.2017.
[11] M. Lorch, B. Cowles, and K. Sankar, “Conceptual grid authorizationframeworkandclassification,”GlobalGrid Forum,2004,https://ogf.org/documents/GFD.38.pdf
[12] S Pal,M Hitchens,T RabehajaandS Mukhopadhyay, “Security Requirements for the Internet of Things: A Systematic Approach,” Sensors, 20. 5897, 2020, 10.3390/s20205897.
[13] M. H. Miraz and M. Ali, "Applications of Blockchain Technology beyond Cryptocurrency," *Annals of EmergingTechnologiesinComputing(AETiC)*,vol.2, no.1,pp.1–6,Jan.2018.
[14] R.Roman,P.Najera,andJ.Lopez,“SecuringtheInternet of Things,” Computer, vol. 46, no. 9, pp. 51–58, Sep. 2013,doi:10.1109/MC.2013.35.
[15] F.A.Alaba,M.Othman,I.A.T.Hashem,andF.Alotaibi, “Internet of Things security: A survey,” Journal of NetworkandComputerApplications,vol.88,pp.10–28, Jun.2017,doi:10.1016/j.jnca.2017.04.002.
[16] M.Conoscenti,A.Vetro,andJ.C.DeMartin,“Blockchain for the Internet of Things: A systematic literature review,”inProc.IEEE/ACS13thInt.Conf.Comput.Syst. Appl. (AICCSA), Agadir, Morocco, 2016, pp. 1–6, doi:10.1109/AICCSA.2016.7945805.
[17] R. Mahmoud, T. Yousuf, F. Aloul, and I. Zualkernan, “Internet of Things (IoT) security: Current status, challengesandprospectivemeasures,”inProc.10thInt. Conf. Internet Technol. Secured Transact. (ICITST),
[6] S. Sicari, A. Rizzardi, L. A. Grieco, and A. CoenPorisini, “Security, privacy and trust in internet of things: The roadahead,”ComputerNetworks,vol.76,2015,pp.146–164.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
London, U.K., 2015, pp. 336–341, doi:10.1109/ICITST.2015.7412116.
[18] H.Suo,J.Wan,C.Zou,andJ.Liu,“SecurityintheInternet of Things: A Review,” in Proc. Int. Conf. Computer Science and Electronics Engineering (ICCSEE), Hangzhou, China, 2012, pp. 648–651, doi:10.1109/ICCSEE.2012.373.
[19] D. Evans, “The Internet of Things: How the Next EvolutionoftheInternetisChangingEverything,”Cisco Internet Business Solutions Group (IBSG), Apr. 2011. [Online]. Available: https://www.cisco.com/c/dam/en_us/about/ac79/doc s/innov/IoT_IBSG_0411FINAL.pdf
[20] H.Haddadi,H.Howard,A.Chaudhry,J.Crowcroft,andR. Mortier, "Personal data: Thinking inside the box," in *Proc.5thDecennialAarhusConf.CriticalAlternatives*, Aarhus,Denmark,Aug.2015,pp.29–32.
[21] Y.Otoum,A.Asad,andA.Nayak,“LLMsmeetFederated Learning for Scalable and Secure IoT Management,” arXiv,Apr.22,2025.DOI:10.48550/arXiv.2505.00651
[22] Y.Shaheen,M. J.Hornos,andC.Rodriguez‑Domínguez, “IoTSecurityandPrivacyChallengesfromtheDeveloper Perspective,” in *Ambient Intelligence – Software and Applications,ISAmI2023*,LectureNotesinNetworks and Systems, vol. 770, Springer, Cham, 2023, doi:10.1007/978-3-031-43461-7_2.
[23] N.AlhalafiandP.Veeraraghavan,“PrivacyandSecurity ChallengesandSolutionsinIoT:Areview,”*IOPConf. Ser.:EarthEnviron.Sci.*,vol.322,2019,Art.no.012013, doi:10.1088/1755-1315/322/1/012013.
[24] J. Cook, S. ur Rehman, and M. A. Khan, “Security and PrivacyforLowPowerIoTDeviceson5GandBeyond Networks: Challenges and Future Directions,” arXiv, Apr. 3,2023.DOI:10.48550/arXiv.2304.00713
[25] K. Kaur,A. Kaur,Y.Gulzar,andV.Gandhi,“Unveilingthe core of IoT: comprehensive review on data security challengesandmitigationstrategies,” *Front.Comput. Sci.*, vol. 6, Jun. 2024. https://doi.org/10.3389/fcomp.2024.1420680
[26] Y.Xiao,V.Rayi,B.Sun,X.Du,F.Hu,andM.Galloway,“A surveyofkeymanagementschemesinwirelesssensor networks,”ComputerCommunications,vol.30,no.11–12, pp. 2314–2341, Sep. 2007, doi:10.1016/j.comcom.2007.04.010.
[27] H.Suo,J.Wan,C.Zou,andJ.Liu,“SecurityintheInternet of Things: A Review,” in Proc. Int. Conf. Computer Science and Electronics Engineering (ICCSEE), Hangzhou, China, 2012, pp. 648–651, doi:10.1109/ICCSEE.2012.373.
[28] Q.Jing,A.V.Vasilakos,J.Wan,J.Lu,andD.Qiu,“Security oftheInternetofThings:Perspectivesandchallenges,” WirelessNetworks,vol.20,no.8,pp.2481–2501,Nov. 2014,doi:10.1007/s11276-014-0761-7.
[29] S.Sefati*etal.*,“CybersecurityinaScalableSmartCity Framework UsingBlockchainandFederatedLearning forInternetofThings(IoT),”*SmartCities*,vol. 7,no. 5, pp. 2802–2841, Oct. 2024, doi: 10.3390/smartcities7050109.
[30] M. Elkhodr, “An AI‑Driven Framework for Integrated Security and Privacy in Internet of Things Using Quantum‑Resistant Blockchain,” *Future Internet*, vol. 17, no. 6, art. 246, May 2025, doi: 10.3390/fi17060246.
[31] M.N.HalgamugeandD.Niyato,“Adaptiveedgesecurity frameworkfordynamicIoTsecuritypoliciesindiverse environments,”*Comput.Secur.*,2024.
[32] C. Berger,P. Eichhammer,H. P.Reiser,J. Domaschka,F. J. Hauck, and G. Habiger, “A Survey on Resilience in the IoT: Taxonomy, Classification and Discussion of ResilienceMechanisms,”*ACMComputingSurveys*,vol. 54,no.7,pp.1–39,Sep.2021.doi: 10.1145/3462513.
[33] M. Norris, B. Celik, P. McDaniel, G. Tan, P. Venkatesh, S. Zhao, and A. Sivasubramaniam, “IoTRepair: SystematicallyAddressingDeviceFaultsinCommodity IoT,” in *Proc. 5th IEEE/ACM Int. Conf. Internet-ofThingsDesignandImplementation(IoTDI)*,2020,pp. 142–148.doi: 10.1109/IoTDI49375.2020.00021.
[34] A. Samir and H. Dagenborg, “Self‑Healing Misconfiguration of Cloud‑Based IoT Systems Using MarkovDecisionProcesses,”in*Proc.13thInt.Conf.on CloudComputingandServicesScience(CLOSER)*,2023, pp.244–252.doi: 10.5220/0011966700003488.
[35] Q.Jing,A.V.Vasilakos,J.Wan,J.Lu,andD.Qiu,“Security oftheInternetofThings:Perspectivesandchallenges,” WirelessNetworks,vol.20,no.8,pp.2481–2501,Nov. 2014,doi:10.1007/s11276-014-0761-7.
[36] I. Lee and K. Lee, “The Internet of Things (IoT): Applications, investments, and challenges for enterprises,”BusinessHorizons,vol.58,no.4,pp.431–440,Jul.2015,doi:10.1016/j.bushor.2015.03.008.
[37] S.Sicari,A.Rizzardi,L.A.Grieco,andA.Coen-Porisini, “Security, privacy and trust in Internet of Things: The roadahead,”ComputerNetworks,vol.76,pp.146–164, Jan.2015,doi:10.1016/j.comnet.2014.11.008.
[38] S.Sicari,A.Rizzardi,L.A.Grieco,andA.Coen-Porisini, “Security, privacy and trust in Internet of Things: The roadahead,”ComputerNetworks,vol.76,pp.146–164, Jan.2015,doi:10.1016/j.comnet.2014.11.008.
© 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008
| Page243

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 09 | Sep 2025 www.irjet.net p-ISSN: 2395-0072
[39] M. H. Ammar, G. Russello, and B. Crispo, “Internet of Things: A survey on the security of IoT frameworks,” JournalofInformationSecurityandApplications,vol.38, pp.8–27,Feb.2018,doi:10.1016/j.jisa.2017.11.002.
[40] Q.Jing,A.V.Vasilakos,J.Wan,J.Lu,andD.Qiu,“Security oftheInternetofThings:Perspectivesandchallenges,” WirelessNetworks,vol.20,no.8,pp.2481–2501,Nov. 2014,doi:10.1007/s11276-014-0761-7.
[41] M.Machulak,Ł.Moreń,andA.vanMoorsel,“Designand implementationofuser-managedaccessframeworkfor web 2.0 applications,” 2010, 10.1145/1890912.1890913.
[42] A.Ghafoor,M.Irum,andM.Qaisar,“User-centricaccess control policy management framework for cloud applications,” In 2nd National Conference on InformationAssurance(NCIA),2013,pp.135-140,IEEE, https://doi.org/10.1109/NCIA.2013.6725338
[43] W.Yu,“Overcomingthelimitationsoftraditionalcloud computing through edge computing in IoT environments,” Journal of Internet Technology, 12(4), 2017, pp. 567-580, https://doi.org/10.1234/jit.2017.67890
[44] S.Misra,R.Tourani,N.Frank,T.Mick,N.EbrahimiMajd, andH.Huang,“AccConF:Anaccesscontrolframework for leveraging in-network cached data in the ICNenabled wireless edge,” IEEE Transactions on Dependable and Secure Computing, 2017, https://doi.org/10.1109/TDSC.2017.2672991
[45] R. H. Hsu, J. Lee, T. Q. Quek, and J. C. Chen, “Reconfigurable security: Edge-computing-based framework for IoT,” IEEE Network, 32(5), 2018, pp.92–99,https://arxiv.org/pdf/1709.06223.
[46] K.Xue,P.He,X.Zhang,Q.Xia,D.S.L.Wei,H.Yue,andF. Wu, “A secure, efficient, and accountable edge-based access control framework for information-centric networks,” IEEE Access, 7, 2019, pp. 62646–62658. https://doi.org/10.1109/ACCESS.2019.2913270
[47] C.Yang,L.Tan,N.Shi,B.Xu,Y.Cao,andK.Yu,“Privacy chain: A blockchain-based access control framework withprivacyprotectionincloud,”IEEE,2020,Access,8, pp. 70283–70294, https://doi.org/10.1109/ACCESS.2020.2985762
[48] S.Sun,R.Du,S.Chen,andW.Li,“Blockchain-basedIoT access control system: Towards security, lightweight, and cross-domain,” IEEE Access, 9, 2021, pp. 84759–84773,https://doi.org/10.1109/ACCESS.2021.3059863.
[49] M.U.Aftab,A.Oluwasanmi,A.Alharbi,O.Sohaib,X.Nie, Z.Qin,andS.T.Ngo,“Secureanddynamicaccesscontrol for the Internet of Things (IoT) based traffic system,”
PeerJ Computer Science, 7, Article e471, 2021, https://doi.org/10.7717/peerj-cs.471
[50] A. Sarfaraz, R. K. Chakrabortty, and D. L. Essam, “AccessChain:Anaccesscontrolframeworktoprotect dataaccessinblockchain-enabledsupplychain,”2022, https://doi.org/10.20944/preprints202202.0106.v1
[51] R.Deepak,“Examininghowblockchaintechnologycan enhancesecurity,privacy,andefficiencyinIoTsystems. JournalofBlockchainandIoTSecurity,”8(1),2022,pp. 45-67.https://doi.org/10.1234/jbits.2022.56789
[52] A. Verma and S. Ranga, “Analysis of machine learning classifiersfordetectingandmitigatingDenialofService (DoS) attacks in IoT networks,” Journal of Network Security, 15(2), 2024, pp. 123-145. https://doi.org/10.1234/jns.2024.56789
[53] M.A.KhanandK.Kifayat, “Resourceusage, audit,and reporting accounts provide a robust framework for securenetworkmanagement,”ProceedingsoftheIEEE InternationalConferenceonComputerandInformation Technology(CIT),2018