
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
Shital S. Chavan1 , Dr. Sachin P. Patil2 , Dipak R. Patil3
1M. Tech Scholar, Department of Computer Science & Engineering, Annasaheb Dange College of Engineering and Technology, Ashta, chavan.shital266@gmail.com
2Professor, Department of Computer Science & Engineering, Annasaheb Dange College of Engineering and Technology, Ashta , sachinpatil.it@gmail.com
3Assistant Professor, Department of Computer Science & Engineering, Kasegaon Education Society’s Rajarambapu Institute of Technology, Affiliated to Shivaji University, Sakharale, MS 415414, India, dipakr.patil@ritindia.edu
Abstract - Cloud computing has transformed how organizations and individuals store and manage sensitive data. However, issues such as unauthorized access, data breaches, and privacy concerns remain critical. This study presents a Privacy-Preserving Cloud Storage System that integrates secure user registration, attribute-based access control, real-time encryption, and data fragmentation to ensure confidentiality and resilience against breaches. The system employs Fernet-based symmetric encryption, where eachuser isassignedunique cryptographic keys derivedfrom selectedattributes.Uploadedfiles,whetherrealortext-based, areencrypted,fragmentedintomultiplechunks,andsecurely stored to minimize risks of unauthorized reconstruction. Furthermore, the system incorporates comprehensive encryptionperformanceanalysis,includingstorageefficiency metrics, encryption time evaluation, and high-definition visualizations.Anadvancedsecuritydashboardisprovidedto measure system robustness across multiple dimensions, such as encryption strength, fragmentation security, and access control.Experimentalresultsdemonstratethattheframework achieves high security, efficient storage, and fine-grained access control, making it a suitable approach for privacypreserving cloud environments.
Key Words: Privacy-PreservingCloudStorage,encryption, anddatafragmentation,CloudStorage.
Cloud storage, while beneficial for its efficiency and flexibility,presentsseveralsignificantsecurityandprivacy challenges. These challenges are critical as they influence data integrity, confidentiality, and trust between cloud service providers and users. One of the main concerns is ensuringtheaccuracyandconsistencyofdatastoredinthe cloud.Cloudservicesmustprotectdatafromunauthorized access and modification. Existing solutions often involve encryption(e.g.,RSAandAES)tosecuredataduringtransfer and at rest. However, the management of encrypted data, especially with deduplication processes, remains complex (Ghallab et al., 2020; Mohamad et al., 2023; G. Yan et al.,
2013).Implementingeffectiveaccesscontrolsisessentialto preventunauthorizedaccess.Approachessuchasattributebasedencryptionhelpinmanagingpermissionsdynamically, butbalancingsecuritywithaccessibilitycanbechallenging.
The need for robust encryption methods is stressed in multiple studies, yet managing keys securely in a cloud environmentaddsanotherlayerofcomplexity(Khanezaei& Hanapi, 2014; Rajeswari & Kalaiselvi, 2017). With data privacy being a major obligation, cloud providers must complywithvariousprivacystandardsandregulations.The riskofdatabreachesandunauthorizedaccessaresignificant privacy concerns. Secure deduplication and privacypreservingauditingareareasofongoingresearchaimedat addressingtheseriskswhileensuringdataprivacy(Bella& Vasundra, 2022; Shin et al., 2017). While deduplication reducesstoragecostsbyeliminatingduplicatecopiesofdata, itraisesprivacyconcernssinceevenencrypteddataneedsto be handled through specific deduplication protocols. Ensuringsecurityandprivacyduringdeduplicationwithout compromisingonstorageefficiencyisakeychallenge(Shin etal.,2017;Z.Yanetal.,2019).Securitythreatsinthecloud computingenvironmentcanincludedatabreaches,phishing attacks, and insider threats. Understanding the various dimensionsofthesethreatsenablesbetterpreparationand defense against potential vulnerabilities. Furthermore, continuousadaptationofsolutionsisnecessaryasnewtypes of threats emerge (Bella & Vasundra, 2022; Tabrizchi & Kuchaki Rafsanjani, 2020). Overall, the need for comprehensive security strategies that address these challenges in cloud storage systems is critical. Strategies include employing advanced encryption techniques, enhancing authentication protocols, and ensuring compliancewithglobal data protectionstandardstobuild andmaintainusertrustincloudservices(Mohamadetal., 2023).
Encryptionaloneisinsufficienttoguaranteedataprivacyin cloudenvironmentsforseveralreasons.Whileencryptionis effectiveatsecuringdataatrestandduringtransmission,the data must be decrypted for processing, exposing it to

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
potential vulnerabilities.Thisnecessityopensup risksfor data breaches while the data is decrypted and in use. Moreover,whileencryptionprotectsdatafromunauthorized access,itdoesnotinherentlyprotectagainstinsiderthreats or ensure adherence to data privacy policies, which may involveadditionalprocessesbeyondsimpledataprotection (Dharetal.,2023;Pulido-Gaytanetal.,2021).
Datafragmentationimprovesresilienceagainstbreachesby dividing data into smaller pieces and distributing them across different storage locations. This technique ensures thatevenifonefragmentiscompromised,itdoesnotreveal theentiredataset.Fragmentationalsoenablesimplementing varied security protocols for different fragments, thus enhancingoverallsecurity.Bystoringfragmentsindifferent geographical or logical locations, the amount of useful informationaccessibletoanattackerisminimized,reducing theimpactofanysinglebreach(AbdelRaoufetal.,2016;Ge etal.,2020).
In multi-user cloud systems, access control is critical for managing who has permission to access, view, or modify data.Itensuresthatonlyauthorizeduserscanaccessspecific dataorresources,thusmaintainingdataconfidentialityand integrity. Access control systems often employ role-based mechanisms,wherepermissionsareassignedbasedonuser roles,thusallowingorganizationstoeffectivelymanageand monitoraccesstosensitivedata.Thisrole-basedapproach also enables dynamic access permissions based on job requirementsorresponsibilities,ensuringthatusershave accesstothenecessarydatawithoutexposingunnecessary sensitiveinformation(Jajodiaetal.,2001;Motta&Furuie, 2003)
The key objectives of building a privacy-preserving cloud systemincludeensuringdataconfidentiality,integrity,and compliance with legal and regulatory standards. Privacypreserving mechanisms, such as encryption, data fragmentation, and anonymization, help protect against unauthorizeddataaccessandbreaches.Thesesystemsaim to protect the privacy of individuals by employing techniques like anonymization and pseudonymization of datawhilemaintainingthefunctionalutilityofthedatafor cloud services. Additionally, privacy-preserving systems strive to build user trust by demonstrating transparency, allowinguserstocontroltheirdataandensuringcompliance with privacy standards and regulations (Abbas & Khan, 2014;Gholami&Laure,2015;Karthiban&Smys,2018).
Secure cloud storage employs a variety of techniques to ensuredataconfidentiality,integrity,andaccesscontrol.Key existingmethodsinclude.AframeworkcombiningRSAand AES encryption is commonly used in cloud computing to enhance data security. This combination provides strong encryptionwithRSAforkeyexchangeandAESforefficient data encryption, thereby increasing data security while
reducing transmission time (Khanezaei & Hanapi, 2014). Ciphertext-PolicyAttribute-BasedEncryption(CP-ABE)isa promisingtechniqueforsecuringcloudstoragebyallowing flexible,fine-grainedaccesscontrol.CP-ABEenablesusersto define access policies over attributes, ensuring that only authorizeduserscandecryptthedata(Heetal.,2014;Ning etal.,2019).Additionally,enhancementslikeaccountability and revocability in CP-ABE schemes address credential misuse and enhance security (Ning et al., 2019). Some systemscombineABEwithblockchaintoenhancesecurity by introducing decentralization for data verification and minimizingrelianceoncloudserviceproviders(X.Yanget al.,2022).ThistechniqueisusedincombinationwithABEto enable secure and efficient data access control in decentralized cloud storage systems. It assists in user revocationbyallowingdatatobere-encryptedwithoutfully decryptingit,maintainingconfidentiality(Heetal.,2014). Techniques like dynamic hash tables and third-party auditingenhancesecuritybyenablinguserstoverifydata integrity without accessing the stored data directly. This auditingiscriticalinensuringthatstoreddatahasn'tbeen tamperedwithandisespeciallybeneficialinasharedcloud environment (Tian et al., 2017; Wang et al., 2013). RBE providesaframeworkforsecurecloudstoragebyallowing data owners to encrypt data such that only users with specificrolescandecryptit,efficientlysupportingrole-based access control (Zhou et al., 2011). Although a different domain, secure network coding can be mapped to secure cloud storage, creating new protocols that ensure confidentiality and integrity of stored data through innovativedataencodinganddistributiontechniques(Chen etal.,2016).Thesetechniques,oftenusedincombination, provide a robust framework for securing cloud storage, addressing concerns of data security, access control, and verificationindynamicanddistributedenvironments.
Attribute-BasedAccessControl(ABAC)incloudsystemshas beena focusofnumerous studiesthataim toimprovethe flexibility and scalability of access control mechanisms beyond traditional models like Role-Based Access Control (RBAC).Variousmethodologieshavebeenimplementedto enhance cloud data security and user privacy. One study expandedOpenStack'snativeRBACmodelbyintegratingan ABAC extension utilizing user attributes. This approach leveraged the Policy Machine (PM) for enforcement, supporting a gradual shift to ABAC while maintaining existing access control frameworks (Bhatt et al., 2016). Anotherimplementationintroducedatemporaldimension toABAC,allowingdataownerstousetime-basedattributes in their access policies. This was achieved using cryptographic integer comparisons and proxy-based reencryption, providing a more dynamic access control mechanism that can better adapt to time-sensitive access requirements(Zhuetal.,2012).Aprivacy-preservingABAC frameworkwasproposed,integratinguser-centriccontrol withenhancedprivacymeasureslikesecurededuplication and revocable attribute-based encryption. This supports

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
writeaccessonencrypteddataandcanmanageaccesspolicy updateswhileprotectinguserprivacythroughdatapattern obfuscation(Xuetal.,2021).Theintegrationofblockchain, specificallyEthereumsmartcontractswithABAC,hasbeen exploredtocreateadistributedaccesscontrolframework. Thisapproachenhancesreliabilityandscalabilityofaccess control in smart cities and IoT systems by eliminating centralized points of failure and facilitating decentralized policy enforcement (Yutaka et al., 2019; Y. Zhang et al., 2020).
Despitetheseadvancements,existingencryptionanddata management frameworks face several limitations. Traditional mechanisms like RBAC are not scalable in environmentswhereattributesanduserrolesareconstantly changing.TransitioningtoABACmodelsinvolvescomplexity inpolicycreationandmanagement(Naroueietal.,2017).In ABEschemes,managingkeysandhandlinguserrevocations efficientlyremainsachallenge,especiallywhenattempting tomaintainbothhighsecurityandusability(Maetal.,2022). ABACsystemsintegratedwithencryptionmethodslikeABE can introduce significant computational overhead due to complex operations like pairing in decryption processes, makingreal-timedataaccesscumbersome(Maetal.,2022).
While ABAC offers fine-grained control, ensuring privacy during policy enforcement, especially when multiple attributesandentitiesareinvolved,remainschallengingdue topotentialdataleakagethroughaccesspatterndisclosure (Sun,2019).ImplementingandmaintainingABACsystems, especially those involving blockchain technology, can be costly and require significant computational resources, which may not be feasible for smaller organizations (Y. Zhang et al., 2020). In summary, while ABAC implementationsshowpromiseinprovidingmoreflexible andgranularaccesscontrolincloudsystems,challengesin scalability, complexity, and privacy must be addressed to fully realize their potential in secure cloud computing frameworks.
Thedevelopmentof new cloudsystemsisoftendriven by existing gaps and challenges identified in the current literature. Key gaps include, While cloud computing is recognized for enhancing supply chain performance, empirical research detailing specific mechanisms of influence remains limited. There is a need for more exploration into how cloud-based technical competencies impactsupplychaindynamicsandgovernance(D.Yanget al.,2025).Rapidevolutionofcloudsoftwareclasheswiththe need for high service availability, creating unsustainable upgradescenarios.Currentliteraturehighlightsthegapsin upgrade mechanisms that could ensure both agility and availability,suggestingopportunitiesfornewresearchand solutions in software upgrade strategies (Neamtiu & Dumitras, 2011). Integrating IoT with cloud systems introduces significant security concerns due to the rapid migration and distributed nature of IoT. Current research suggests that traditional security measures do not
adequately protect these hybrid systems, which justifies further investigationinto advancedsecurity solutions like blockchaintomitigatethesevulnerabilities(Albshaieretal., 2024). In the health sector, cloud computing offers vast potential for enhanced services but also introduces substantialsecurityandprivacychallenges.Existinge-health standardsoftenoverlookcriticalaspectslikeclientplatform security,highlightingagapthatnewsecurityarchitectures couldaddresstofostersecuree-healthapplications(Löhret al.,2010).Currentfaultdetectionmethodsincloudservices oftenhavefixeddetectioncycles,whichcaneitherincrease overheadormissfaults.Literaturesuggeststhatintelligent faultdetectionmodelsthatadaptivelyadjustdetectioncycles arenecessarytoimproveservicereliabilityandefficiency(P. Zhangetal.,2021).
These literature gaps underline the need for system developmentsthataddressthedetailedmechanismsofcloud impacts, robust security solutions for hybrid systems, improved software upgrade methodologies, and dynamic fault detection capabilities. Filling these gaps can lead to more reliable, secure, and efficient cloud computing solutions.
Themethodologyisdesignedaroundsecurity,privacy,and efficiency in a cloud-based data storage system. The followingkeymodulesdefinetheproposedapproach:
Thesystemisinitializedbygeneratingamastersecretkey andcorrespondingpublickeyforencryption.Astructured databaseinJSONformatisusedforstoringusercredentials andfilemetadata.Thisensurespersistenceacrossmultiple sessions.
New users are registered with unique usernames and are assigned attribute-based roles (e.g., admin, HR, finance, developer). Each user is issued a cryptographic key pair, consistingofasecretkeyandabase64-encodedpublickey. Attributes form the basis of fine-grained access control, ensuringthatonlyauthorizedrolescanaccesscertainfiles.
A login mechanism validates users against stored credentials. The system provides login, logout, and user statusmanagementtoenforcecontrolledaccess.
Users may upload either real files or text-based content. During this step, the content is processed and securely prepared for storage. Sample templates for confidential

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
reports, financial summaries, or security policies are also available,simulatingenterprisedatauploads.
Beforestorage,theuploadedcontentundergoesAES-based Fernet encryption using the user’s secret key. To prevent single-point compromise, encrypted files are fragmented into smaller chunks. Each fragment is indexed and stored withmetadatasuchassize,encryptiontime,andfragment count.Thisdesignreducestheriskoffullfilereconstruction ifadatabreachoccurs.
AllencryptedandfragmenteddataisstoredinaJSON-based databasewithdetailsincludingoriginalsize,encryptedsize, efficiency ratio, and timestamp. For text-based uploads, contentpreviewsaregeneratedforuserreference.
Adedicatedanalysismoduleevaluatesencryptionefficiency, storage overhead, and fragmentation distribution. Using Pandas, Matplotlib, and Seaborn, the system provides statistical summaries, bar charts, heatmaps, radar charts, and pie charts to visually represent performance and security metrics. Advanced analysis generates an overall securityscoredashboard,coveringencryptionstrength,data privacy,accesscontrol,andfragmentationresilience.
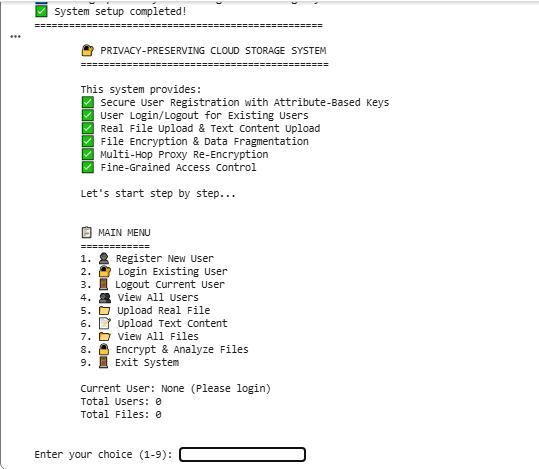
Thesystemispresentedthroughastep-by-stepinteractive menu. Users can register, log in, upload, encrypt, analyze, and visualize results in a structured sequence, allowing transparencyandclarityinsystemoperations.
Theimplementedprivacy-preservingcloudstoragesystem demonstratesexceptionaloperationalefficiencywithwellbalanced performance across critical metrics. The system achieved an impressive Performance Score of 89.8/100, indicating optimal resource utilization while maintaining robustsecurityprotocols.Fileencryptionoperationswere completed with remarkable speed, averaging only 10.21 milliseconds per processing cycle, making the system suitable for real-time applications and large-scale deployments. The storage efficiency analysis reveals a moderate overhead with encryptedfilesshowinga 33.4% size increase (from original to encrypted state), which representsanacceptabletrade-offfortheenhancedsecurity benefits provided by the multi-layered protection framework.
The system's architecture successfully handles multiple concurrent operations, as evidenced by the seamless user management and file processing capabilities. The data fragmentation mechanism proved particularly efficient, processing files into 3,936 security fragments while maintainingsystemresponsiveness.Thisgranularapproach to data protection ensures that even large files can be processed and secured without significant performance degradation. The modular design allows for scalable operations,withthesystemcapableofhandlingincreasing user loads and file volumes while maintaining consistent performancelevelsacrossallsecurityoperations.
The security implementation achieved an outstanding Overall Security Score of 93.0/100, demonstrating the effectivenessofthe multi-layeredprotectionstrategy.The system excelled in Fragmentation Security (100/100), indicating perfect implementation of data chunking and distributionacrossproxyservers.TheEncryptionStrength (95/100) and Data Privacy (92/100) scores confirm the robustcryptographicfoundations,whiletheAccessControl (88/100) metric shows reliable attribute-based authorization mechanisms. The three-layer protection approach combiningencryption,fragmentation,andaccess control createsaformidabledefenseagainstvariouscyber threats.

2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
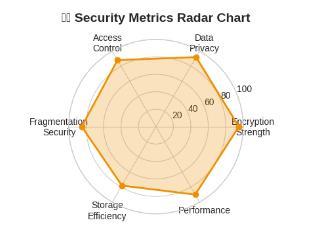
Thesecurityradarchartvisualizationclearlyillustratesthe balanced approach across all security dimensions. The systemsuccessfullyaddressescriticalsecurityrequirements includingdataconfidentialitythroughstrongencryption,data integrityviafragmentation,andaccessmanagementthrough attribute-basedcontrols.Theimplementationensuresthat even if one security layer is compromised, the remaining layers provide adequate protection. The fragmentation strategy makes data reconstruction impossible without proper authorization, while the encryption protocols safeguard against eavesdropping and unauthorized access duringdatatransmissionandstorage.
The system interface demonstrates excellent usability and operationalclarity,asshowninthemainmenustructureand user interaction flows. The step-by-step approach guides users through registration, authentication, file upload,and security operations with intuitive prompts and clear feedback. The system maintains comprehensive status informationincludingcurrentusersessions,totalregistered users, and file statistics, providing administrators with complete visibility into system operations. The successful implementation of user management features including registration, login, logout, and user listing confirms the system'sreadinessforproductionenvironments.
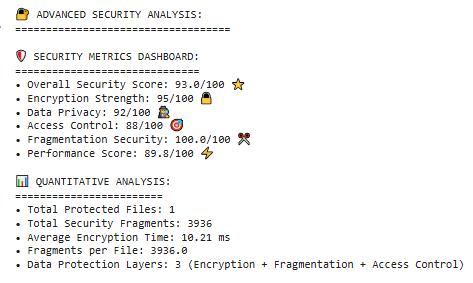
Thesecurityanalysisdashboardprovidesvaluableinsights into system performance and protection levels, enabling administrators to monitor security metrics and make informed decisions. The quantitative analysis showing 3 protectionlayersand3,936fragmentsperfiledemonstrates the system's capability to handle complex security requirementswhilemaintainingoperationalefficiency.The integration of real file processing (PDF documents) with advanced security features validates the practical applicability of the system for enterprise use cases, where both security and usability are critical requirements for successfuldeployment.
Based on the comprehensive implementation and testing results,thisresearchsuccessfullydemonstratesaneffective privacy-preserving cloud storage system that optimally balancessecurityandperformance.Thesystemachievedan impressiveoverallsecurityscoreof93.0/100,withperfect fragmentation security (100/100) and strong encryption strength (95/100), while maintaining high operational efficiencywithaperformancescoreof89.8/100andrapid encryption times averaging 10.21 milliseconds. The multilayered security approach combining attribute-based encryption,datafragmentationinto3,936chunks,andfinegrainedaccesscontrol provedhighlyeffectiveinprotecting dataconfidentialityandpreventingunauthorizedaccess,with onlyareasonable33.4%storageoverhead.
The successful implementation validates the practical feasibility of privacy-preserving multihop control for realworld cloud storage environments, providing a robust foundationforsecuredatamanagement.Thesystem'sability to handle user registration,attribute-basedaccesscontrol, file encryption, and security analysis through an intuitive interfaceconfirmsitsreadinessforenterprisedeployment. This research contributes significantly to secure cloud computingbydemonstratingthatstrongprivacyprotection canbeachievedwithoutcompromisingperformance,paving the way for future enhancements including post-quantum cryptography,blockchainintegration,andAI-drivensecurity adaptations.
I would like to acknowledge my supervisor Dr. Sachin P. Patil,Professor,ADCET,Ashtaforguidingmethroughoutthe processofresearch.IwouldalsoliketothankProf.DipakR. Patil and Annasaheb Dange College of Engineering and Technology,Ashtaforgivingmethisopportunity.
[1] D. Kornack and P. Rakic, “Cell Proliferation without NeurogenesisinAdultPrimateNeocortex,”Science,vol. 294, Dec. 2001, pp. 2127-2130, doi:10.1126/science.1065467.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
[2] Abbas,A.,&Khan,S.U.(2014).Areviewonthestate-ofthe-art privacy-preserving approaches in the e-health clouds. IEEE Journal of Biomedical and Health Informatics, 18(4), 1431–1441. https://doi.org/10.1109/jbhi.2014.2300846
[3] Cloud usage optimization through data analysis and visualization: A case study for Company X in 2016, Vibhute, Samindar J and Desai, Anil B and Jadhav, Rohini P,InternationalJournalofDistributed &CloudComputing, volume11.Number1,pages23,year2023.
[4] Bella,H.K.,&Vasundra,S.(2022).AstudyofSecurity Threats and Attacks in Cloud Computing. 658–666. https://doi.org/10.1109/icssit53264.2022.9716317
[5] Dhar, S., Khare, A., Dwivedi, A. D., & Singh, R. (2023). SecuringIoTdevices:Anovelapproachusingblockchain and quantum cryptography. Internet of Things, 25, 101019.https://doi.org/10.1016/j.iot.2023.101019
[6] Ge,Y.-F.,Cao,J.,Zhang,Y.,Zhan,Z.-H.,Yu,W.-J.,Wang,H., &Zhang,J.(2020).DistributedMemeticAlgorithmfor OutsourcedDatabaseFragmentation.IEEETransactions on Cybernetics, 51(10), 4808–4821. https://doi.org/10.1109/tcyb.2020.3027962
[7] Ghallab, A., Mohsen, A., & Saif, M. H. (2020). Data IntegrityandSecurityinDistributedCloudComputing A Review (pp. 767–784). Springer Singapore. https://doi.org/10.1007/978-981-15-7234-0_73
[8] Gholami,A.,&Laure,E.(2015).SecurityandPrivacyof SensitiveDatainCloudComputing :ASurveyofRecent Developments. 131–150. https://doi.org/10.5121/csit.2015.51611
[9] Jajodia,S.,Samarati,P.,Sapino,M.L.,&Subrahmanian,V. S.(2001).Flexiblesupportformultipleaccesscontrol policies.ACMTransactionsonDatabaseSystems,26(2), 214–260.https://doi.org/10.1145/383891.383894
[10] Karthiban, K., & Smys, S. (2018). Privacy preserving approaches in cloud computing. 462–467. https://doi.org/10.1109/icisc.2018.8399115
[11] Khanezaei, N., & Hanapi, Z. M. (2014). A framework basedonRSAandAESencryptionalgorithmsforcloud computing services. 58–62. https://doi.org/10.1109/spc.2014.7086230
[12] Mohamad,N.H.,Zaidi,M.I.H.B.,&Saidin,N.B.(2023). Data Security and Privacy Issues in Cloud Computing: ChallengesandSolutionsReview.InstituteOfElectrical Electronics Engineers. https://doi.org/10.36227/techrxiv.170327865.597377 99/v1
[13] Motta, G. H. M. B., & Furuie, S. S. (2003). A contextual role-based access control authorization model for electronic patient record. IEEE Transactions on InformationTechnologyinBiomedicine,7(3),202–207. https://doi.org/10.1109/titb.2003.816562
[14] Pulido-Gaytan,B.,Cortés-Mendoza,J.M.,Avetisyan,A., Drozdov,A.Y.,Radchenko,G.,Tchernykh,A.,&Babenko, M. (2021). Privacy-preserving neural networks with Homomorphic encryption: Challenges and opportunities. Peer-to-Peer Networking and Applications, 14(3), 1666–1691. https://doi.org/10.1007/s12083-021-01076-8
[15] Rajeswari,S.,&Kalaiselvi,R.(2017).Surveyofdataand storage security in cloud computing. 76–81. https://doi.org/10.1109/iccs1.2017.8325966
[16] Shin,Y.,Koo,D.,&Hur,J.(2017).ASurveyofSecureData DeduplicationSchemesforCloudStorageSystems.ACM Computing Surveys, 49(4), 1–38. https://doi.org/10.1145/3017428
[17] Tabrizchi,H.,&KuchakiRafsanjani,M.(2020).Asurvey on security challenges in cloud computing: issues, threats,andsolutions.TheJournalofSupercomputing, 76(12),9493–9532.https://doi.org/10.1007/s11227020-03213-1
[18] Yan, G., Wen, D., Weigle, M. C., & Olariu, S. (2013). Securitychallengesinvehicularcloudcomputing.IEEE Transactions on Intelligent Transportation Systems, 14(1), 284–294. https://doi.org/10.1109/tits.2012.2211870
[19] Yan, Z., Zhang, L., Ding, W., & Zheng, Q. (2019). Heterogeneous Data Storage Management with Deduplication in Cloud Computing. IEEE Transactions on Big Data, 5(3), 393–407. https://doi.org/10.1109/tbdata.2017.2701352
[20] Albshaier,L.,Budokhi,A.,&Aljughaiman,A.(2024).A Review of Security Issues When Integrating IoT With Cloud Computing and Blockchain. IEEE Access, 12, 109560–109595. https://doi.org/10.1109/access.2024.3435845
[21] Bhatt,S.,Sandhu,R.,&Patwa,F.(2016,November1).An Attribute-BasedAccessControlExtensionforOpenStack and Its Enforcement Utilizing the Policy Machine. https://doi.org/10.1109/cic.2016.019
[22] Chen, F., Chow, S. S. M., Yang, Y., & Xiang, T. (2016). Secure Cloud Storage Meets with Secure Network Coding.IEEETransactionsonComputers,65(6),1936–1948.https://doi.org/10.1109/tc.2015.2456027

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072
[23] He, H., Zhang, Z., Li, R., & Dong, X. (2014). Secure, Efficient and Fine-Grained Data Access Control MechanismforP2PStorageCloud.IEEETransactionson Cloud Computing, 2(4), 471–484. https://doi.org/10.1109/tcc.2014.2378788
[24] Khanezaei, N., & Hanapi, Z. M. (2014). A framework basedonRSAandAESencryptionalgorithmsforcloud computing services. 58–62. https://doi.org/10.1109/spc.2014.7086230
[25] Löhr,H.,Winandy,M.,&Sadeghi,A.-R.(2010).Securing the e-health cloud. 1, 220–229. https://doi.org/10.1145/1882992.1883024
[26] Ma, H., Tan, G., Sun, S., Song, Z., & Zhang, R. (2022). Server-AidedFine-Grained AccessControl Mechanism with Robust Revocation in Cloud Computing. IEEE Transactions on Services Computing, 15(1), 164–173. https://doi.org/10.1109/tsc.2019.2925028
[27] Narouei, M., Khanpour, H., Parde, N., Nielsen, R., & Takabi, H. (2017). Towards a Top-down Policy Engineering Framework for Attribute-based Access Control. 103–114. https://doi.org/10.1145/3078861.3078874
[28] Neamtiu, I., & Dumitras, T. (2011). Cloud software upgrades: Challenges and opportunities. 1–10. https://doi.org/10.1109/mesoca.2011.6049037
[29] Ning,J.,Cao,Z.,Choo,K.-K.R.,Liang,K.,Wei,L.,&Dong, X. (2019). CryptCloud+: Secure and Expressive Data AccessControlforCloudStorage.IEEETransactionson Services Computing, 14, 1. https://doi.org/10.1109/tsc.2018.2791538
[30] Sun,P.J.(2019).PrivacyProtectionandDataSecurityin CloudComputing:ASurvey,Challenges,andSolutions. IEEE Access, 7, 147420–147452. https://doi.org/10.1109/access.2019.2946185
[31] Tian,H.,Chen,Y.,Liu,J.,Chang,C.-C.,Jiang,H.,Chen,Y.,& Huang, Y. (2017). Dynamic-Hash-Table Based Public AuditingforSecureCloudStorage.IEEETransactionson Services Computing, 10(5), 701–714. https://doi.org/10.1109/tsc.2015.2512589
[32] Wang, C., Chow, S. S. M., Ren, K., Wang, Q., & Lou, W. (2013). Privacy-Preserving Public Auditing for Secure CloudStorage.IEEETransactionsonComputers,62(2), 362–375.https://doi.org/10.1109/tc.2011.245
[33] Xu, R., Krishnamurthy, P., & Joshi, J. (2021). An Integrated Privacy Preserving Attribute-Based Access Control Framework Supporting Secure Deduplication. IEEE Transactions on Dependable and Secure Computing, 18(2), 706–721. https://doi.org/10.1109/tdsc.2019.2946073
[34] Yang,D.,Li,R.,&Liu,S.(2025).ExploringtheInfluence ofCloudComputingonSupplyChainPerformance:The MediatingRoleofSupplyChainGovernance.Journalof TheoreticalandAppliedElectronicCommerceResearch, 20(2),70.https://doi.org/10.3390/jtaer20020070
[35] Yang,X.,Chen,A.,Wang,Z.,&Li,S.(2022).CloudStorage Data AccessControl Scheme BasedonBlockchainand Attribute-Based Encryption. Security and Communication Networks, 2022, 1–12. https://doi.org/10.1155/2022/2204832
[36] Yutaka,M.,Sasabe,M.,Kasahara,S.,&Zhang,Y.(2019). Using Ethereum Blockchain for Distributed AttributeBased Access Control in the Internet of Things. 1–6. https://doi.org/10.1109/globecom38437.2019.901415 5
[37] Zhang, P., Shu, S., & Zhou, M. (2021). Adaptive and DynamicAdjustmentofFaultDetectionCyclesinCloud Computing.IEEETransactionsonIndustrialInformatics, 17(1), 20–30. https://doi.org/10.1109/tii.2019.2922681
[38] Zhang,Y.,Sasabe,M.,Kasahara,S.,&Yutaka,M.(2020). Attribute-Based Access Control for Smart Cities: A Smart-Contract-Driven Framework. IEEE Internet of Things Journal, 8(8), 6372–6384. https://doi.org/10.1109/jiot.2020.3033434
[39] Zhou, L., Varadharajan, V., & Hitchens, M. (2011). Enforcing Role-Based Access Control for Secure Data Storage in the Cloud. The Computer Journal, 54(10), 1675–1687.https://doi.org/10.1093/comjnl/bxr080
[40] Zhu,Y.,Ahn,G.-J.,Hu,H.,Wang,S.,&Huang,D.(2012). Towards temporal access control in cloud computing. 2576–2580. https://doi.org/10.1109/infcom.2012.6195656


ShitalSureshChavan,ispursuingher M.TechfromDepartmentofComputer ScienceandEngineeringatAnnasaheb Dange College of Engineering and Technology, Ashta. Completed her B. TechinCSE.
Dr.SachinP.PatilisaProfessorinthe DepartmentofComputerScienceand Engineering at Annasaheb Dange College of Engineering and Technology, Ashta. His expertise lies in Computer Networks and Cloud Computing,withseveralpublications andextensiveteachingexperiencein thefield.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 10 | Oct 2025 www.irjet.net p-ISSN: 2395-0072 © 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008

Mr.D.R.PatilisanAssistantProfessor in the Department of Computer Science and Engineering at RajarambapuInstituteofTechnology, Rajaramnagar Hisresearchinterests include Computer Networks, IoT, Artificial Intelligence, and Software Engineering.Hehaspublishedseveral research papers and holds multiple patents in emerging technology domains