
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072


International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
Prakash Velusamy
Principal Software Development Engineer, CVS Health, Arizona, USA
Abstract - As more healthcare systems have started leveraging cloud services, it has become critical to secure Protected Health Information (PHI) and Payment Card Industry (PCI) data. This paper has evaluated more than 15 studiesinhealthcarethatemphasizetheprotectionofPHIand PCIdata,andfoundthateventhoughmanysolutionsaddress specific issues such as encryption and access control, significant gaps still remain. For example, there is no comprehensiveframework,andhealthcareresearchdoesnot focusenoughonPCI.Inaddition,itishardtofollowtherules of the Health Insurance Portability and Accountability Act (HIPAA) and the Payment Card Industry Data Security Standard (PCI DSS) when data crosses multiple domains. Therefore,thisarticleoffersacomprehensiveframeworkthat combinesprotectionsforPHIandPCIwithexistingstandards such as HIPAA Security Rule and PCI DSS. The proposed framework has steps for data classification and continuous monitoring, which arespecifictocloudhealthcare.A unified strategy is offered by the framework for protecting the confidentialityandavailabilityofPHIandPCIdataincloudbased healthcare settings by addressing the identified vulnerabilities.
Key Words: Healthcare systems, Protected Health Information, Payment Card Industry, HIPAA Security Rule, Cloud Security
Whilecloudadoptionoffersunprecedentedflexibilityand cost savings for healthcare enabling services like telehealth and advanced analytics it simultaneously introduces significant, complex security, privacy, and regulatorychallenges[1].Whenbillingpatients,forexample, PHImustbeprotectedbyhealthcaresystemsunderHIPAA andpaymentcarddataunderPCIDSS.Itisimportanttonote thattheHIPAASecurityRulerequirescoveredentitiesand business associates to implement specific administrative and technical safeguards for keeping all electronic PHI confidentialandaccessible[2].Inaddition,PCIDSSlists12 high-level requirements that range from firewalls to monitoring for protecting environments that store or transmitpaymentaccountdata[3].Becausetheserulesare similarbutdifferent,cloudhealthcareprovidersoftenmust followbothsetsofrules.
Manyisolatedsolutionsandframeworksareprovidedbythe currentbodyofliteratureforhealthcarecloudsecurity.For
example, encryption and access control are highly recommended,andcloudplatformsoftensupportrole-based accesscontrol(RBAC)andmulti-factorauthentication(MFA) forrestrictingaccesstoPHI[4].Rodriguesetal.discovered thatcloud-basedsystemsforElectronicHealthRecord(EHR) mustusestrong encryptionanddetailedaccesslogging to maintaindataconfidentiality.Similarly,Al-Issaetal.confirm that contemporary methods typically tackle only specific subsets of issues and support a comprehensive security solution that addresses and meets all requirements [1]. Shojaei et al. note that healthcare organizations are still hesitanttousecloudservicesbecausetheyarestillhaving difficultiesincomplyingwithHIPAArulesanddonothave much control over data that is transferred to other companies[4].Thesesurveysshowtheneedforacohesive frameworkthatisaimedatsafeguardingPHIandPCIwithin cloudhealthcareenvironments.
Adetailedframeworkisoutlinedinthispaperforprotecting PHIandPCIdataincloudhealthcaresystems.Tofindoutthe securitymethodsandvulnerabilitiesthataremostcommon, acomparativereviewofrecentstudieswascarriedout.The “KeyFindingsandGaps”sectionsummarizesthesefindings andhighlightsthecriticalgapsincurrentapproaches.The Proposed Framework section presents a comprehensive security framework that integrates best practices from HIPAA,PCIDSS,andcloudsecuritystandardstoaddressthe gapsidentifiedintheanalysis.Thispervasivefragmentation andthenotedscarcityofresearchfocusingonthePHI/PCI complianceintersectiondemonstrateanurgentneedfora unified,comprehensivesecurityframework.
Thispapercarriedoutaliteraturereviewofstudies,mainly journal articles, related to cloud security in healthcare, focusing on the protection of PHI and PCI data. Multiple databases were searched, such as PubMed, IEEE Xplore, ACMDigitalLibrary,andGoogleScholar(2015–2025).The search terms included "cloud computing," "healthcare," "PHI,""HIPAA,""PCIDSS,""datasecurity,"and"framework." Finally, more than 15 relevant works were selected after reviewing the titles and abstracts. These works either discussed how to protect PHI or payment data in cloudbased health systems or examined compliance requirements(HIPAA,PCI)inthiscontext.

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
All the work was reviewed to identify their focus (for example,anEHRcloudsystem,atelemedicineplatform,ora hospital billing system), the security measures they suggested,andanyproblemstheyfound.Whenpossible,this paper also examined case studies of healthcare cloud deployments[5].Thequalitativeanalysisfocusedmainlyon persistentsecuritycontrolsandidentifyinggapsincurrent solutions. Table 1 below shows a summary of the most important studies that were reviewed and the gaps they revealed. From this evaluation, the main themes and vulnerabilitieswereidentified,whichguidedtheframework proposal[6].
Table 1: KeyStudiesonPHIandPCISecurityinCloud Healthcare
Author (s) (Year)
Focus Area Key Contributions / Methods Identified Gaps
Mia et al. [7]
PHI, HIPAA, Mobile Health
Houser etal. [8]
PHI, Teleheal th, Privacy
Staticcodeanalysisof 12 HIPAA technical safeguardsinAndroid mHealth apps; identified common vulnerabilities in authorization, encryption, and data transmission(for200 topapps).
Systematic review of telehealth privacy/security studies(2020–2022); categorizes risk factors into environmental (e.g. lackofprivatespace), technological(security issues, connectivity), and operational (billing,training).
Developers limited HIPAA awareness; evaluation confined to Android apps; no user studies.
Mostly qualitative studies; focuses on COVID-19 period; regulatory/pol icy solutions underexplored.
Esposit o et al. [10]
PHI, Blockcha in/Cloud
noting that “state-ofthe-art solutions addressonlyasubset ofconcerns”.
Conceptual study on using blockchain to secure cloud-stored healthcare data; proposes blockchainbaseddatatraceability and integrity mechanisms, noting limitsofconventional encryption.
validation lacking.
Purely theoretical; performance andregulatory implications not assessed; practical deployment challenges remain.
Mehrta k et al. [9]
PHI, Healthca reCloud
Al-Issa etal. [1]
PHI, Cloud Computi ng
Systematic review of cloud security in healthcare; identifies majorchallenges(data confidentiality, integrity, availability, networksecurity)and typical solutions (encryption, authentication,access controlAPIs).
Survey of cloud securityinhealthcare; highlights fragmentation of current solutions,
Solutionsoften address individual challenges; no holistic framework is evaluated.
Calls for a unified,holistic security approach; empirical
Cobrad o et al. [11]
PHI,EHR Access Control
Systematic review of access-control schemesinelectronic healthrecords(EHRs); documents use of RBAC, ABAC, cryptographic methods, etc., and notes many schemes lack 2-factor authentication or comprehensive regulatoryalignment. No single model fits all; mostproposals handle access control partially; MFA and audit controls are often missing (a “lack of synthesis” in solutions).
Selvi & Sakthiv el[12]
PHI, Cloud Encrypti on
Proposes a hybrid ECC–AES encryption framework (SymECCipher) for cloud-based health data (e.g. mental health records); uses symmetric-keysharing and ECC to speed encryption and supports ML-based analyticsonencrypted data.
Focus on performanceat cost of complexity; needsstudyin varied healthcare settings; quantum‐resili ence and device (e.g. wearable) support are futurework.
Alsolam i[13]
PHI, IoMT Intrusio n Detectio n
Evaluates ensemble machine-learning (stacking, bagging, boosting)forintrusion detection in IoMT networks; shows stackingwithRandom Forest/SVM achieves ≈98.9% accuracy on WUSTL-EHMSdataset.
Limited to offline data sets;real-time effectiveness and compliance with privacy standards not evaluated; no discussion of U.S.regulatory context.
Mudass ar etal. [14]
PHI, IoMT Data Privacy
Develops a privacypreserving data analytics scheme for IoMTusingdifferential privacy;appliesnoise tosmart-meterhealth
Evaluated on smalldatasets; trade-off between privacy (εparameter) and utility;

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
data to allow safe aggregateanalytics
Kumar et al. [15]
PHI, Cloud EHR Security
Proposes PA2C (Privacy-AwareAccess Control) for secure EHR sharing: uses blockchain smart contractsandCP-ABE encryption, plus an improvedRBFneural network (IntVORBNN) for network attack detection.
Achieves high accuracyonhealthcare intrusiondata.
cloud integrationand compliance (eg. HIPAA) implications are not addressed
Heavy complexity (blockchain and ML); prototype evaluated on limitedattacks; scalabilityand regulatory compliance (like HIPAA auditability) not fully addressed.
Shojaei et al. [19]
PHI, Health IT (Review)
Systematic review of security/privacy tech inhealthinfosystems (blockchain, IoT, cloud, ML, etc.); highlightsthebenefit of cloud (access control,cost)butnotes persistent HIPAA/GDPR compliancehurdlesin cloudenvironments.
Find “healthcare organizations arehesitant”to fully adopt clouds due to privacy/regula toryconcerns; lacksfocuson PCIcontext.
Madhu mathi& Kumar [16]
PHI, IoMT & Blockcha in
Shakil et al. [20]
PHI, Cloud Access Control
Bhasker et al. [17]
PHI, IoMT/Fe derated Learning
Introduces “Provable Partitioned Secure Blockchain”(PPSBCP) forIoThealthcaredata sharing:classifiesdata sensitivity, applies a specialencryptionand blockchain-based audit (Hash Index Policy and provable keyhandover).
Develops an IoMT monitoringframework (FBCI-SHS)combining federatedlearningand blockchainforsecure dataaggregation,plus an IDS for network threats. Reports ~98.7% data privacy and97.1%intrusiondetectionaccuracy.
Novel, but highly complex; performance overhead and real-world implementatio n concerns; impact on emergency access not studied.
Complexmultitech solution; potential latency and interoperabilit y issues; assumes high device capability; regulatory compliance (HIPAA/GDPR) mentionedbut not deeply analyzed.
Griebel et al. [21]
PHI, Cloud Computi ng (Review)
Designs “BAMHealthCloud”: a cloud system with biometric(fingerprint) and password authentication for ehealthdata;usesfuzzy vault for fingerprint keymanagement.
Scoping review of healthcare cloud projects (pre-2015); emphasizes encryption and anonymization (“as few data as possible” incloud)forprivacy.
Prototype only; userfriendliness anderrorrates (e.g. fingerprint variability)are notevaluated; no discussion of legal/regulator yreadiness.
Early stage: many applications didnotclearly define“cloud”; trust issues (data control, deletion) persist.
Most studies focus on PHI protection (HIPAA context) in cloud-based health data (EHRs, mHealth, IoMT), with far fewer examining PCI data in healthcare clouds. Common solutionsincludedataencryption(symmetric,public-key,or blockchain-based) [10], fine-grained access control and authentication (RBAC, ABAC, multi-factor auth) [11], and intrusion detection using ML/AI [13]. Emerging methods like blockchain are proposed for auditability and tamperproof logging (Esposito and Bhasker), and federated learning is proposed for decentralized analytics (Bhasker 2025). Many studies build analytical or prototype frameworks(forexample,Mia2022’sHIPAA-audittool[7], Selvi2025’sSymECCipher[12]).
Arora [18]
PHI, Supply Chain (Cloud)
Analyzescloud-based healthcare supply chains;findscommon misconfigurationsand proposesamulti-layer privacy framework (encryption, adaptive access control, blockchainauditlogs, automatedcompliance monitoring).
Framework is conceptual; lacksempirical validation; integrating such layers acrossdiverse stakeholdersis challenging.
However,gapsanddivergencesareclear.Nostudyoffersa truly holistic solution: Al-Issa et al. (2019) explicitly note thatexisting“state-of-the-artsolutionsaddressonlyasubset of concerns.” In practice, most proposals handle narrow slices for example, only encryption or only access control and integration of multiple safeguards is rare. Multi-factorauthenticationandauditabilityarefrequently missingorunder-evaluated(e.g.,Cobrado2024findslittle adoptionof2FA/MFA).Performanceandusabilityoftentake a backseat to technical novelty; for instance, complex

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
schemesusingblockchainordeepML arerarelytested in realhealthcaredeployments,andemergencyaccesslatency isunexamined.
To address the identified gaps, this paper proposes a comprehensivesecurityframeworkforcloudhealthcarethat explicitlyprotectsbothPHIandPCIdata(seeFig-1)
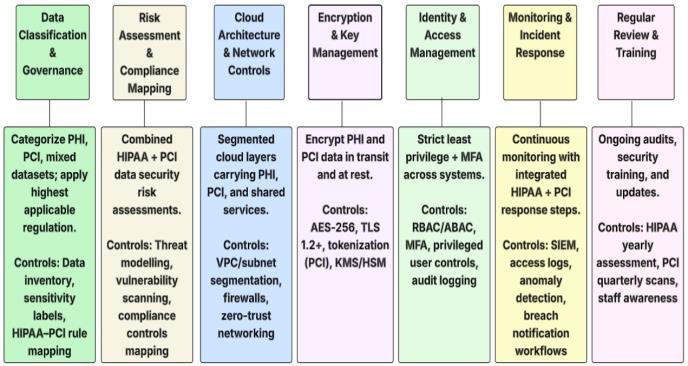
It is necessary to ensure that there are clear rules that separatePHIandPCIdata.Forinstance,HIPAAprotectsall electronic health data (ePHI), while PCI controls apply to payment data that is not part of another system. Thus, healthcare organizations should maintain a list of the different types of data they have and apply the stricter standard.Forexample,ifmedicalrecordsandpatientcredit card information are stored together, the credit card informationisprotectedbyHIPAA[3].Ifnot,itneedstobe tokenized or encrypted according to PCI rules. A single complianceprogramshouldconnecteachdatacategoryto therelevantHIPAAandPCIrules.
As per the HIPAA Security Rule, organizations need to conduct a risk analysis of cloud assets that contain PHI and/orPCIdata.Threats(likeunauthorizedaccessordata leaks)shouldbeidentified,andhealthcarefirmsshouldalso evaluatethecontrolsthatarealreadyinplace.Atthesame time,itisrecommendedtoconductaPCIDSSassessmentof paymentworkflows,likecardreadersandclouddatabases. The results should be used to develop plans for security measures.Therearenotmanystudiesthatclearlycombine these assessments, but this framework requires such integration to ensure that PHI and PCI protection are not separated.
Firms should design the cloud environment with segmentation.PHIdatabasesshouldbehostedonhardened
instances or private subnets that are not connected to services that are open to the public. Besides that, cloudbasedcardholderdataenvironments(CDE)shouldalsobe segmented and utilize network setups that meet PCI standards.Allnetworkconnectionsneedtouseencryption (TLS)andfirewallrulesthatonlypermitnecessarytraffic. To prevent tenants from accessing each other's data in multi-tenant cloud settings, virtual network isolation and dedicatedhostsarerequired.
Organizationsshouldusestrongencryptionfordataatrest andintransit.Forinstance,clouddatabasesthatstoreePHI should utilize encryption algorithms that meet NIST standards. It is implied by the rules of PCI DSS that cardholderdata,suchasSSN(SocialSecurityNumber)and authentication data, must be encrypted or tokenized. For generating and storing keys, a secure Key Management Service(KMS)orHardwareSecurityModule(HSM)should be used. As identified by Rodrigues et al., all EHR data fragmentsshouldbeencryptedanddistributedsothatifone partiscompromised,itdoesnotrevealPHI.Thisprinciple appliesequallytopaymentdatacomponents.
Organizations must implement strict controls for authenticationandauthorization.Forinstance,MFAshould be required for anyone who accesses PHI or CDEs. RBAC should be used so that users, like clinicians and billing clerks,canonlyaccesstheinformationtheyneed.Aspointed out by Shojaei et al., misconfigured access rights are a common risk [4]. For both PHI and PCI systems, it is importanttoensurethatallaccessisloggedinawaythat cannotbechanged.Third-partycloudproviders(asbusiness associates) must be legally required to follow HIPAA securityrulesandundergoPCIvendorassessments.
Organizationsshouldutilizetoolsforcontinuousmonitoring and logging. For example, access to ePHI or CDE must be logged(accesslogs,alerts).SecurityInformationandEvent Management(SIEM)shouldbeusedforcorrelatingevents such as anomalous logins or data downloads. Audit trails should be reviewed regularly to detect any breaches. It is indicated by PCI DSS that logging access to card data is required, and HIPAA requires audit controls as well. An incident response plan must include steps for addressing breaches of either PHI or PCI data, as well as roles and notificationproceduresthatcomplywiththeHIPAABreach NotificationRuleandguidelinesforPCIbreachreporting.
The framework requires that controls be reviewed periodically.Whenevertherearechangestothesystem,itis

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072
important to do a HIPAA risk assessment. Once every quarteroraftermajorupdates,itisimportanttocarryouta PCIre-scan.Organizationsshouldensurethatpoliciesevolve withtechnology(forexample,whennewcloudservicesare introduced).EmployeesshouldbetrainedtokeepbothPHI andpaymentdatasafe,whichisequallyimportant.Afterall, oneofthemainproblemsinHISsecurityishumanerror[4]. Awareness programs should address phishing and data handling,amongothertopics.
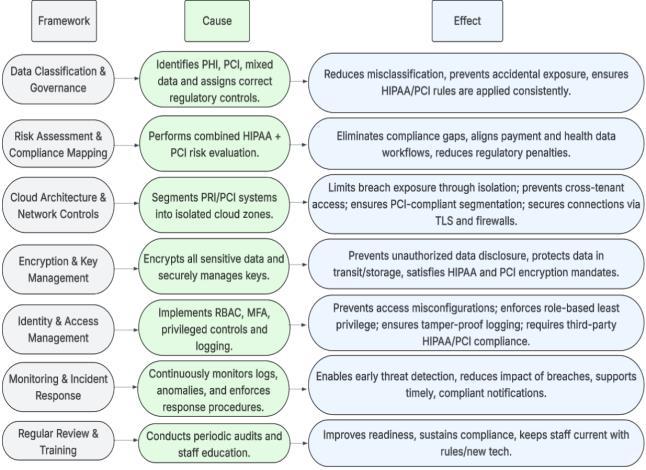
Fig -2:HealthcareSecurityFrameworkCategories:Cause andEffect
It is important to note that this framework integrates the best practices of both HIPAA and PCI DSS (see Fig -2). It combinesHIPAA'sfocusonprivacy(throughencryptionand accesscontrols)withPCIDSS'sdetailedrequirementssuch assecureconfigurationsandmonitoring[3].Additionally,it fillsthegapwherestudiesoftenoverlookoneortheother byexplicitlyaddressingbothareas.Forexample,usingCSA's CloudControlsMatrix or HITRUSTCSF for mappingtasks canhelpimplementthesesteps.ThisisbecauseCSAoffers cloud-specific security controls that can be aligned with HIPAA/PCIgoals(forexample,CCM4.0mapstoPCIDSS4.0 controls). Basically, a healthcare provider using this frameworkwouldfirstclassifyitsdataanddeterminewhich protection to use. It would then configure its cloud deployment to maintain separate health and payment workflowsanduse encryptionasneeded, while requiring MFA.OngoingauditswouldensurethatPHIisonlyaccessed in ways that are compliant with HIPAA and that any card data flows follow PCI rules. Ultimately, the framework createsadefense-in-depthposturebyaddressingallsecurity aspectscomprehensively.
Cloudadoptioninhealthcareoffersmanybenefitsbutalso makesdataprotectionmorecritical.Thisreviewofcurrent researchshowsthatmanysolutionsonlyaddresssomeparts of the problem, leaving gaps where PHI and PCI security intersect. Therefore, a complete framework has been
proposedthatcombinesHIPAAandPCIDSSrequirements with best practices for cloud security. This framework focuses on data classification and continuous monitoring amongothers,allofwhicharespecifictothecloud.Itsgoalis toensurethatsensitivehealthandpaymentdataremainsafe andcompliant.Futurestudiesshouldfocusonvalidatingthis framework in actual implementations and consider its expansion to integrate new technologies such as edge computing in healthcare. Cloud healthcare providers can betteraddressregulatoryrequirementsandprotectpatient informationfromemergingthreatsbyusingthisstructured approach.
[1] Al-IssaY,OttomMA,TamrawiA(2019)eHealthcloud security challenges: a survey. J Healthc Eng. https://doi.org/10.1155/2019/7516035
[2] U.S. Department of Health & Human Services (HHS) (2025)SummaryoftheHIPAASecurityRule.U.S.HHS. https://www.hhs.gov/hipaa/forprofessionals/security/laws-regulations/index.html Accessed12Nov2025
[3] AlderS(2024)WhatisPCIComplianceinHealthcare? HIPAA Journal. https://www.hipaajournal.com/pcicompliance-in-healthcare.Accessed12Nov2025
[4] Shojaei P, Vlahu-Gjorgievska E, Chow YW (2024) Security and privacy of technologies in health information systems: A systematic literature review. Computers13(2):41.
[5] Pathak V, Jena B, Kalra S (2013) Qualitative research. PerspectClinRes (3):192.https://doi.org/10.4103/22293485.115389
[6] Maher L, Dertadian G (2018) Qualitative research. Addiction113(1):167–172. https://doi.org/10.1111/add.13931
[7] Mia MR, Shahriar H, Valero M, Sakib N, Saha B, Barek MA,FarukMJH,GoodmanB,KhanRA,AhamedSI(2022) A comparative study on HIPAA technical safeguards assessment of Android mHealth applications. Smart Health 26:100349. https://doi.org/10.1016/j.smhl.2022.100349
[8] Houser SH, Flite CA, Foster SL (2023) Privacy and security risk factors related to telehealth services–a systematicreview. PerspectHealthInfManag 20(1):1f. Available at: https://perspectives.ahima.org/privacyand-security-risk-factors-related-to-telehealth-servicesa-systematic-review
[9] MehrtakM,SeyedAlinaghiSA,MohsseniPourM,NooriT, Karimi A, Shamsabadi A, Heydari M, et al. (2021) Securitychallengesandsolutionsusinghealthcarecloud

International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056
computing. J Med Life 14(4):448. https://doi.org/10.25122/jml-2021-0034
[10] EspositoC,DeSantisA,TortoraG,ChangH,ChooKKR (2018) Blockchain: A panacea for healthcare cloudbased data security and privacy? IEEE Cloud Comput 5(1):31–37.
https://doi.org/10.1109/MCC.2018.011791712
[11] CobradoUN,ShariefS,RegahalNG,ZepkaE,Mamauag M, Velasco LC (2024) Access control solutions in electronichealthrecordsystems:Asystematicreview. Informatics Med Unlocked 49:101552. https://doi.org/10.1016/j.imu.2024.101552
[12] SelviP,SakthivelS(2025)AhybridECC-AESencryption framework for secure and efficient cloud-based data protection. Sci Rep 15(1):30867. https://doi.org/10.1038/s41598-025-30867-3
[13] Alsolami T, Alsharif B, Ilyas M (2024) Enhancing cybersecurity in healthcare: Evaluating ensemble learningmodelsforintrusiondetectionintheInternetof Medical Things. Sensors 24(18):5937. https://doi.org/10.3390/s24185937
[14] MudassarB,TahirS,KhanF,ShahSA,ShahSI,AbbasiQH (2024)Privacy-preservingdataanalyticsinInternetof Medical Things. Future Internet 16:407. https://doi.org/10.3390/fi16100407
[15] Kumar A, Batta P, Rathore PS, Ahuja S (2025) Secure healthcaredatasharingandattackdetectionframework usingradialbasisneuralnetwork. SciRep 15(1):15432. https://doi.org/10.1038/s41598-025-15432-8
[16] Madhumathi CS, Vishnu Kumar K (2025) Enhancing privacy in IoT-based healthcare using provable partitionedsecureblockchainprincipleandencryption. SciRep 15(1):29682.https://doi.org/10.1038/s41598025-29682-0
[17] BhaskerB,RaoPM,SaraswathiP,PatroSGK,BhuttoJK, Islam S, Kareemullah M, Emma AF (2025) Blockchain frameworkwithIoTdeviceusingfederatedlearningfor sustainable healthcare systems. Sci Rep 15(1):26736. https://doi.org/10.1038/s41598-025-26736-8
[18] Arora P (2025) Data privacy concerns in cloud-based healthcaresupplychains. Int J Netw Secur 5(2):42–58. https://doi.org/10.5121/ijns.2025.050204
[19] Shojaei P, Vlahu-Gjorgievska E, Chow YW (2024) Security and privacy of technologies in health information systems: A systematic literature review. Computers 13(2):41. https://doi.org/10.3390/computers13020041
[20] ShakilKA,ZareenFJ,AlamM,JabinS(2017)Computer andinformationsciences. ProcediaComputSci 113:607–613.https://doi.org/10.1016/j.procs.2017.08.314
[21] Griebel L, Prokosch HU, Köpcke F, Toddenroth D, ChristophJ,LebI,EngelI,SedlmayrM(2015)Ascoping review of cloud computing in healthcare. BMC Med Inform Decis Mak 15(1):17. https://doi.org/10.1186/s12911-015-0145-7
Volume: 12 Issue: 11 | Nov 2025 www.irjet.net p-ISSN: 2395-0072 © 2025, IRJET | Impact Factor value: 8.315 | ISO 9001:2008

Prakash Velusamy is a Principal SoftwareDevelopmentEngineerat CVSHealth,withovertwodecades of demonstrated excellence in industry-leading Infrastructure and Application Performance Monitoring platforms and strong expertise in the Site Reliability Engineering (SRE). He is a technical leader in Observability, OpenTelemetry, Data Ingestion, Machine learning, Artificial Intelligence,andAutomation