TheNewS e

























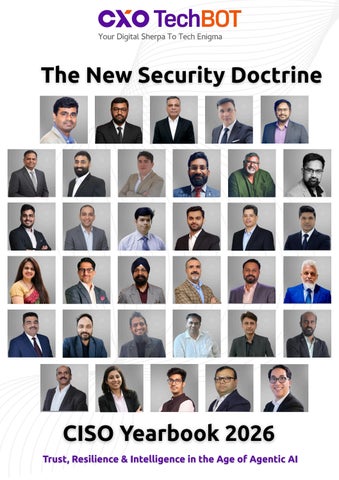
SwatiGupta CEO&ManagingEditor
Everyeditionofthisyearbookhasbeenshapedbythemomentitcaptures Thisoneisshapedbyarupture
TheemergenceofagenticAI-autonomoussystemsthatdonotmerelyprocessinstructionsbutreason,decide,and act-hasnotsimplyaddedanewcategorytothethreatlandscape Ithasalteredthefundamentalconditionsunder whichsecurityleadershipoperates Theperimeterweoncedefendedwasphysical,thenlogical,thendigital Itis nowcognitive:aboundarynotbetweennetworks,butbetweensanctionedjudgmentandunsanctionedautonomy.
Thirty-fiveofIndia'smostdistinguishedChiefInformationSecurityOfficershavecontributedtheirperspectivesto thisvolume.Theywritefromthefrontlinesofanindustryingenuinetransition,nottheincrementaltransitionofa newcompliancerequirementoranupgradedtoolchain,butthestructuraltransitionofanentirediscipline reconsideringitsfoundations.
Whatdoestrustmeanwhentheentityrequestingaccessisnotapersonbutanagent?
Whatdoesresiliencemeanwhentheattacksurfaceincludesthereasoningsystemswehavedeployedinourown defence?
Whatdoesintelligencemeanwhentheadversaryisgeneratingitatmachinespeed?
Thesearenotrhetoricalquestions.
TheyaretheoperationalquestionsthatCISOsacrossIndiaandgloballyareanswering,imperfectly,urgently,and withouttheluxuryofwaitingfortheindustrytoproduceaconsensusplaybook Thearticles,perspectives,and insightsgatheredhererepresentthatworkinprogress:thecollectiveintelligenceofpractitionerswhoarebuilding theframeworks,testingtheboundaries,andestablishingthestandardsthatwilldefinesecuritygovernanceinthe agenticera
Thethemeofthisyearbook-CyberThreatsintheAgenticEra:RedefiningTrust,ResilienceandIntelligence-was chosennotbecausetheseconceptsarenewtosecurity,butbecauseeachofthemdemandsredefinition Trust mustnowextendtonon-humanprincipalswhosedecision-makingcannotbefullyobservedorpredicted Resiliencemustnowaccountforfailuremodesthatemergefromthesystemswecontrol,notonlyfromthe adversarieswhotargetus Intelligencemustnowbegeneratedandacteduponatatempothathumananalysis alonecannotsustain
Thethirty-fivevoicesinthisyearbookareunitednotbyagreementoneveryquestion,butbyasharedseriousness aboutthestakes Securityleadershiphasalwaysrequiredthecouragetoactunderuncertainty Theagenticerahas raisedboththeuncertaintyandthestakesinequalmeasure Wepresentthisyearbookintheconvictionthatclarity,sharedhonestlyamongpractitioners,isitselfaformof resilience.
Readitasadocumentofaprofessionthinkinghard,inrealtime,aboutthechallengesthatdefineit.
Shadow AI in the Agentic Era:
Employees building and deploying autonomous agents outside IT's visibility
The Rise of the Agentic-Era CISO:
From Security Guardian to Strategic Orchestrator
Redefining Enterprise Security: Trust, Intelligence, and Resilience in the Age of Autonomous AI
AI Governance and Cyber Resilience:
Navigating Security in the Agentic Era
Cyber Trust in the Age of AI:
Governance, Accountability and Resilience
Agentic AI and Cybersecurity:
Navigating the Next Frontier of Digital Risk
The CISO as AI Ethicist:
Navigating the governance grey zones of autonomous decision-making
The Ghost in the Code:
Navigating the Frontier of AI Criminal Law
Cyber Threats in the Agentic Era:
How AI is Redefining Trust, Resilience, and Cybersecurity Intelligence
From Perimeter Defense to Intent Governance:
Securing the Age of Autonomous Systems
Cybersecurity Leadership in the AI Era:
Cybersecurity Leadership in the AI Era:
Securing the Agentic Future: How Cybersecurity is Evolving with Autonomous Systems
AI Red Teaming as a Core Competency: CISOs building adversarial testing programs for agentic workflows
Cyber Trust at Machine Scale: Reimagining Cybersecurity in the Agentic Era
Cybersecurity in the Agentic Era: Rethinking Defense in an AI-Driven World
Cybersecurity as a Governance
Imperative in an Era of Systemic Digital Risk
Cyber Trust, Autonomy and the Evolving Mandate of the Modern CISO
Rethinking Cybersecurity Leadership in an Age of Autonomous Threats
Third-Party Risk, Multiplied : Managing trust chains when vendors deploy AI agents on your behalf
Cyber Trust in the Agentic Era: Governing Intelligence at Machine Scale
Cyber Resilience in the Agentic AI Era: Redefining Security Architecture for Intelligent Enterprises
Trust, Resilience, Intelligence: A New Cybersecurity Playbook for the AI Era
The Autonomous Sovereignty Doctrine: Cyber Trust in the Agentic Era
The Strategic Imperative of AI Driven Cyber Resilience
From SIEM to AIMS:
The evolution of monitoring infrastructure toward AI-native security tooling
Building Secure, Transparent, and Accountable AI Systems at Enterprise Scale
The Rise of Autonomous Systems: Redefining Cybersecurity in the Agentic Era
Agentic AI and Cybersecurity:
Redefining Trust, Resilience and Collective Intelligence
AI-Powered Cybersecurity:
Building Autonomous, Adaptive Defense for the Future Enterprise
Next-Gen Cybersecurity: Tackling Agentic AI Threats with Resilience & Intelligence
Building Cyber Trust as Autonomous AI Systems Begin to Act and Decide at Enterprise Scale
Cyber Trust and Resilience in the Era of Autonomous AI
Cybersecurity in the Agentic AI Era: Engineering Trust, Resilience, and Intelligent Defense
The Agentic Era:
How Autonomous AI is Transforming Cyber Risk and Defense
Cyber Trust in the Agentic Era: Rethinking Security, AI Governance, and Resilience in Autonomous Systems
Cyber Trust in the Agentic Era: Navigating AI-Driven Threats and Trust Challenges
Cybersecurity in the Agentic Era: From Control to Intelligence
Securing the Agentic Future:
Building Trust, Resilience and Intelligence in the Age of Autonomous AI
Cyber Threats in the Agentic Era:
Driving Trust, Resilience, & Intelligent Security Leadership
Fighting Fire with Fire
How security teams are deploying AI agents to hunt AI-enabled threats

AgenticAIisnolongerjustanexperimentalplaygroundfordatascientists-itʼsthestrategiclever forautonomousdecision-making,self-optimizingoperations,andintelligentorchestrationof enterpriseecosystems
Thisexclusive,advanced-levelprogramwillhelpC-SuiteleadersmovebeyondAIpilotsandinto AgenticAI-drivenbusinessarchitecture,unlockingproductivityatscale,operationalautonomy, andcompetitivemoats.
AgenticAIStrategyPlaybook–FromAIAssistantstoAutonomousDecisionUnits
EnterpriseAutonomyBlueprint–HowtodesignworkflowswhereAIagentsself-initiate,selfcorrect&self-scale
Multi-AgentCollaborationModels–Interoperabilitybetweenfinance,supplychain,and customerengagementagents
Trust,Compliance&AIGovernance–Buildinganethical&controllableautonomous enterprise
ROIMapping&ValueRealization–Quantifyingthebusinessimpactofautonomybefore boardapprovals
CaseStudies–EarlymoversinBFSI,manufacturing,andsmartinfrastructureusingAgenticAI atscale Format
4Weeks|High-IntensityCohort LiveMasterclassSessionswithIndustry AIArchitects&TransformationLeaders

C-SuitePeerNetworkingPods Capstone:EnterpriseAutonomy RoadmapforYourOrganization
Who Should Attend?

ShadowAIintheAgenticEra
EmployeesbuildinganddeployingautonomousagentsoutsideIT'svisibility
ShadowITgaveusunauthorisedsoftware.ShadowAIgivesusunauthoriseddecisionmaking.Thedifferenceisnotoneofdegree-itisoneofkind.ArogueSaaSappholds data.Arogueautonomousagentactsonit.
Thephenomenonisfamiliarenoughthatsecurityteams haveanameforit.ShadowIT-employeesprocuringand usingtechnologywithoutITapproval-hasbeenathorn intheCISO'ssideforoveradecade.Cloudstorage, personalemail,unauthorisedSaaSsubscriptions:the catalogueofungovernedtoolshasgrownsteadily.But shadowIT,forallitsheadaches,operatedwithina recognisableboundary Thesoftwareran;humans decidedwhattodowithitsoutputs
Thatboundarynolongerholds Theemergenceof accessible,low-codeagenticplatforms-toolsthatallow anytechnicallyliterateemployeetobuildanddeploy autonomousAIagentsinanafternoon-hascreateda newcategoryofungovernedriskthatsecurityteamsare onlybeginningtograpplewith CallitShadowAI: autonomousagentsconceived,built,andrunningin productionentirelyoutsideIT'svisibility,connectingto enterprisesystemswithemployeecredentials,and makingconsequentialdecisionsatmachinespeed.

TheNewDIYThreatSurface
ThebarriertobuildinganAIagenthascollapsed. PlatformslikeZapier,MicrosoftCopilotStudio,anda growingecosystemofno-codeagentbuildersallow employeestowiretogetheranautonomousworkflow inhours-connectingtheircorporateemail,CRM,cloud storage,andthird-partyAPIsintoasingleagentthat canread,write,decide,andactwithoutfurtherhuman input.Noprocurement.Nosecurityreview.NoIT ticket
Themotivationsareentirelyunderstandable Asales analystwhobuildsanagenttoautomatically summarisedealpipelinesandsendstakeholder briefingsissolvingagenuineproblem Afinance managerwhodeploysanagenttoreconcileinvoices acrosssystemsissavingrealtime Theproductivity gainsarevisibleandimmediate Thesecurity implicationsareinvisibleanddeferred-rightupuntil theyaren't
Theriskscompoundrapidly Theseagentstypically rununderpersonalOAuthtokensorAPIkeysissuedto individualemployees,meaningtheiraccessisscoped totheindividual'spermissions-whichareoftenfar broaderthananyprincipleofleastprivilegewould sanction.Whentheemployeeleaves,theagentmay keeprunning.WhentheAPIkeyrotates,theworkflow silentlybreaks-orsilentlymisbehaves.Whentheagent ispromptedtodosomethingitsbuilderdidn't anticipate,noonehaswrittenaguardrailtostopit.
WhatMakesThisDifferentFromShadowIT
SecurityleaderswhohavemanagedshadowIT programmesmightbetemptedtoapplythesame playbook:discover,inventory,classify,andenforce. Theinstinctiscorrectbuttheexecutionisharder. ShadowITproducedfilesandlogins-artefactsthat couldbefoundinCASBlogsandaccessreviews. ShadowAIproducesactions:APIcalls,datawrites, outboundmessages,automateddecisions.Many oftheseactionsareindistinguishablefrom legitimatesystemactivityunlessyouare specificallylookingfornon-humanbehavioural patterns.
ThereisalsoaliabilitydimensionthatshadowIT rarelyraised.Whenanautonomousagent,acting onanemployee'scredentials,sendsanincorrect communicationtoaclient,modifiesafinancial record,orexfiltratesdatathroughanunreviewed integration,thequestionofwhobears responsibilityhasnocleananswerinmost organisationstoday Legalframeworks,insurance policies,andinternalaccountabilitystructureswere notdesignedwithautonomousagentsinmind
BuildingVisibilityBeforeBuildingPolicy
Theinstincttorespondwithprohibitionis understandablebutcounterproductive.Blanket bansonagentictoolswillbecircumventedas readilyasbansonpersonalcloudstoragewereandwilldrivetheactivityfurtherunderground.The moreeffectivepathbeginswithvisibility
CISOsarebeginningtoestablishlightweightagent registrationprogrammes:alow-frictionprocessby whichemployeescandeclareagentstheyhave built,documentthesystemstheyconnectto,and getbasicsecurityreview Thegoalisnottocreate abureaucraticgatebuttoestablishamap You cannotgovernwhatyoucannotsee,andyou cannotseewhatemployeeshavenoincentiveto disclose
Alongsideregistration,behaviouralmonitoringat theAPIandidentitylayerisessential.Non-human accesspatterns-high-frequencyAPIcalls,access outsideworkinghours,systematicdatareads acrossmultiplerecords-aredetectablewiththe righttooling.Taggingagentactivitythrough dedicatedserviceaccountsratherthanpersonal credentialsmakesthisfarmoretractableand enablesrevocationwithoutdisruptingthe employee'sownaccess.
TheCultureImperative
Ultimately,ShadowAIisnotatechnologyproblem. Itisacultureproblemwearingatechnologymask. Employeesarebuildingautonomousagents becausetheyaresolvingrealproblems,and becausenoonehasgiventhemasanctioned, securewaytodoso.TheCISOswhowillcontain thisriskmosteffectivelyarethosewhorespond notwithrestriction,butwithinfrastructure: governedplatforms,approvedagentframeworks, andsecurityguardrailsthatareinvisibletotheuser andinviolabletotheagent
Theworkforceisnotgoingtostopbuilding autonomoustools Thequestioniswhetherthe toolstheybuildwillruninsideyoursecurity perimeteroraroundit

TheRiseoftheAgentic-EraCISO:
FromSecurityGuardiantoStrategicOrchestrator
Thefutureofcyberresilienceliesinresponsiblyharnessingautonomousagentsto outpacethreats,withoutlosingvisibility,accountability,orcontrol.
TheroleoftheChiefInformationSecurityOfficeris undergoingaprofoundtransformation Intodayʼs agenticera,whereautonomousAIsystemsare reshapingbothenterpriseoperationsandcyber threats,themodernCISOisnolongerjusta defenderofsystemsbutastrategicorchestratorof resilience,intelligence,andbusinessassurance
Thisnewarchetypeblendsboardroominfluence withdeepoperationalexpertise Havingled responsestohundredsofsophisticatedcyber incidents,includinglarge-scaleransomware attacks,todayʼssecurityleadersbringunmatched real-worldexperienceincontainment,recovery, andriskmitigation.Theiractionshavenotonly safeguardeddigitalassetsbutalsopreserved billionsinbusinessvalue,reinforcingcybersecurity asacoredriverofenterprisecontinuity.
Attheheartofthisevolutionliesapragmatic philosophy:securitymustdelivermeasurable outcomes,notjustcompliance.ModernCISOsare buildingcentralized,high-impactsecurity operationsthatintegrateincidentresponse,threat hunting,andmanagedsecurityservicesinto cohesive,resilientframeworks.Thesecapabilities extendacrossITandOTenvironments,aligning closelywithregulatoryexpectationsandbusiness priorities.
Intheagenticlandscape,adversariesarealready leveragingautomationandAI Forward-looking CISOsarerespondinginkind;deployingAI-driven threatdetection,intelligentincidentorchestration, andadaptivedefensemechanisms However, innovationisbalancedwithstronggovernance Identity,accountability,andauditabilityremain foundationaltoensurethatautonomoussystems operatewithincontrolledboundaries
Akeyfocusareaissecure-by-designagent enablement
Byembeddingprinciplessuchasleastprivilege, continuousverification,andtransparencyintoAI systems,organizationscanscaleautomationwithout increasingriskexposure Thisapproachensuresthat productivitygainsdonotcomeatthecostofsecurity
Ultimately,theagentic-eraCISOrepresentsashiftfrom reactivedefensetoproactive,intelligence-ledsecurity leadership Theseleadersareshapingthefutureof cybersecurity,wherehumanjudgment,supportedby machineprecision,enablesorganizationstoinnovate withconfidencewhilestayingresilientagainstan increasinglycomplexthreatlandscape

Head-ManagedSecurityService
TataConsultancyServices

KinshukDeisagloballyrespectedcybersecurity leaderwhoexemplifiesthemodernCISOinthe AgenticEra.AsHeadofIncidentResponse, DigitalForensics,andManagedSecurityServices atTataConsultancyServices,hehasled responsestoover150majorcyberincidents worldwide,includingmorethan50ransomware attacks-helpingorganizationsavertover$5 billioninpotentiallosses.Knownacrossthe industryasthe“RansomwareKiller,ˮKinshuk combinesdeeptechnicalmasterywith boardlevelstrategicinsight.AChevening Scholar,CISSP,andCyberAIBoardAdvisor,he championstheresponsibleuseofAIand autonomoussecurityoperationstooutpace adversarieswhilestrengtheningtrustand resilience Hisleadershipcontinuestodefinehow enterprisessecureinnovationanduseofAIat scale
RedefiningEnterpriseSecurity: Trust,Intelligence,&Resiliencein theAgeofAutonomousAI
Intheagenticera,cybersecurityisnotaboutreactingtothreats,butaboutbuilding intelligentsystemsthatcontinuouslyadapt,anticipaterisk,andearntrustinreal time.
Ascybersecuritycontinuestoevolveatan unprecedentedpace,organizationsareenteringa definingphaseoftendescribedastheagenticera. Thisshiftmarksatransitionfromtraditional perimeter-basedsecuritytoZeroTrust architecturesandnowtowardintelligent ecosystemswhereAI-drivensystemsactively participateinbothenterpriseoperationsandcyber defense.
Inthisrapidlychangingenvironment,cybersecurity leadersmustrethinkfoundationalprinciples.Trust cannolongerbeassumed;itmustbecontinuously verifiedthroughidentity-centriccontrols,adaptive authentication,andreal-timemonitoring Resilience isnolongerlimitedtorecoveryafterincidentsbut mustincludeproactiveanticipationofthreats,rapid containment,andtheabilitytosustainbusiness continuityunderpersistentattackconditions Intelligencenowemergesfromthesynergy betweenhumanexpertiseandartificialintelligence, enablingorganizationstodetectanomaliesfaster, predictadversarialbehavior,andrespondwith precisionatmachinespeed
However,thesametechnologiesthatempower enterprisesalsoexpandtheattacksurface AIdrivenphishing,deepfake-enabledsocial engineering,polymorphicmalware,and autonomousattacksystemsareredefiningthe modernthreatlandscape.Cyberadversariesareno longerstaticactors;theyareincreasinglydynamic, adaptive,andscalable.Thisnecessitatesa fundamentaltransformationindefensestrategies, whereAI-enabledsecurityplatformsbecome essentialforreal-timedetection,predictive analytics,andautonomousresponse.
FormodernCISOs,cybersecurityisnolonger confinedtoatechnicaldomain.Itisastrategic businessfunctionthatdirectlyinfluencestrust, brandreputation,andorganizationalsustainability.
Buildingastrongsecurityculture,fosteringcrossfunctionalcollaboration,andembeddingsecurity intoeverylayerofdigitaltransformationarenow criticalleadershippriorities.
Tosucceedintheagenticera,enterprisesmust embracethreeimperatives:ZeroTrust architecturessupportedbycontinuousverification, resilientsecurityframeworksdrivenbyautomation andintelligence,andAI-enableddefensesystems thatintegratehumandecision-makingwith machinelearningcapabilities.
Ultimately,cybersecurityisevolvingfroma defensivenecessityintoastrategicenablerof digitaltrustandenterprisegrowth
Director-GlobalCISOandDPO
ANSR
SandeepKumarAkkimollaisacybersecurity anddataprivacyleaderwithextensive experienceinglobalsecuritytransformation acrosstelecommunicationsandenterprise environments Hecurrentlyservesas DirectorandGlobalChiefInformation SecurityOfficerandDataProtectionOfficer atANSR,leadingenterprise-wide cybersecurity,riskmanagement,and complianceinitiatives.PreviouslyatRadisys Corporation,heheadedglobalcybersecurity anddataprivacyprograms,focusingon applicationsecurity,cloudsecurity,IT infrastructureprotection,andregulatory compliancealignedwithGDPR,DPA/CDPA, andrelatedframeworks.Earlier,at Capgemini,heheldseniorleadershiproles includingdeputyCISOandcybersecurity practicearchitect,drivingIAM,GRC,SOC, anddatasecuritystrategies.Hisexpertise liesinbuildingresilientsecurityarchitectures andstrengtheningorganizationalsecurity postureacrossglobalmarkets

NavigatingSecurityintheAgenticEra AIGovernanceandCyberResilience:
Cyberresilienceintheagenticeraisnotaboutbuildinghigherwalls,butabout buildingsmartersystems.Asautonomousagentstakeongreaterresponsibility, organisationsmustembedgovernance,accountability,&adaptabilityintotheirAI foundations,becauseresilienceisnotafeature,itisadesignprinciple.
Intheagenticera,theattacksurfaceisnolonger justdata;itisjudgment.
Fordecades,cybersecuritywasfundamentallya humanproblem:humanadversariesexploiting humanerrorinhuman-builtsystems We understoodthatparadigm Webuiltframeworks, trainedteams,anddeployedtechnologiesagainst it ButtheriseofautonomousAIagents-systems thatplan,act,andadaptwithoutdirecthuman oversight-hasrewrittenthethreatmodelentirely
AtContrailRisks,ourworksitsatthisinflection point AsorganisationsracetodeployagenticAIfor competitiveadvantage,wearewitnessinganew categoryofriskemerge:theexploitationofAItrust. Adversarialactorsarenolongersolelytargeting data,theyaretargetingthedecision-making processesofautonomoussystems.Prompt injections,manipulatedtrainingpipelines,and weaponisedmodeloutputsarebecomingthenew vectorsofchoice,andtheorganisationsmost exposedarethosethathavedeployedintelligence withoutdeployinggovernance.
ThisiswhatIcallthe“trustinversionproblemˮ. Traditionalcybersecuritytaughtustoverify everythingandassumenothing.Zerotrustwasa revolutioninthinking.ButAIagentsoperate differently:theyactwithdelegatedauthority,make autonomousdecisions,andinterfacewithother agentsinwaysthatcreatecascadingchainsof accountability Whenthattrustiscompromised,the consequencespropagateatmachinespeed
TheanswerisnottoslowtheadoptionofAI
Theorganisationsthatpausewillbeoutcompeted Theansweristobuildgovernancearchitectures thattreatagenticsystemswiththesamerigourwe applytohumanidentityandaccessmanagement
ThatmeansAI-nativeframeworksreal-time behaviouraloversightofagentactivity,explainability andauditabilitymechanisms,adversarialredteamingofAIdecisionpipelines,andclear accountabilitychainsextendingacrossthesupply chainofmodels,data,andintegrations
Cyberresilienceintheagenticeraalsodemandsa fundamentalrethinkofincidentresponse Whenan AIagentiscompromised,theblastradiuscan propagatefasterthananyhumanteamcanreact Thecontainmentprotocols,communication frameworks,andrecoveryplaybooksthathave serveduswellforyearsmusturgentlyevolveto operateatthespeedandscaleofmachine intelligence.
Mycalltofellowsecurityleadersisclear:the agenticeraisnotahorizon,itisthepresent.The CISOswhowilldefinethenextdecadearethose buildingthegovernance,resilience,andintelligence infrastructuresforaworldwheretheperimeterhas dissolvedintoanetworkofautonomoussystems. Ourroleisnolongerjusttodefend.Itistoensure thattheintelligencewedeploycanbetrusted,by thebusiness,byregulators,andbythepeoplewho dependonit.

ManagingDirecto
ContrailRisks
FabrizioDiCarloisana ManagingDirectorofC advisesenterpriseson technologies,andregu extensiveexperiencein partnerswithboardsan designresilient,futurearchitectures.
Arecognisedexpertin resilience,hehasguide industriesthroughfram DORA,andISO27001, compliancetoembedr advantage.Hespecialis securitywithboard-lev focusonmanagingrisk AIandautonomoussys

CyberTrustintheAgeofAI: Governance,AccountabilityandResilience
Wespenttwodecadessecuringwhathumanscouldaccess.Thenextdecadewill bedefinedbygoverningwhatagentsareallowedtodecide.
Intodayʼsenvironment,thecybersecuritychallengeis nolongerlimitedtoprotectingsystemsfromexternal attacks.Itisaboutpreservingtrustinaworldwhere artificialintelligenceisincreasinglyembeddedin decision-making,operations,andbusinessprocesses. AsAIexpandsacrosstheenterprise,therealquestion isnotonlywhattechnologycando,buthow organizationsgovernitsusewithclarity,responsibility, andcontrol.
Cybertrusthasthereforebecomeastrategicissue.It isbuiltongovernancebeforeitisbuiltontools.
OrganizationsneedclearaccountabilityforAIenableddecisions,strongoversightofdataquality, transparentcontrolmechanisms,andtheabilityto explainhowcriticaloutcomesareproduced Without thisfoundation,speedbecomesfragility,automation becomesopacity,andinnovationcanquicklybecome exposure
Resiliencealsoneedstoberedefined IntheageofAI, resilienceisnotsimplytheabilitytorecoverfroma cyberincident Itisthecapacitytoanticipatenew formsofrisk,challengefalseconfidence,and maintaindecisionintegrityunderpressure This requiresstrongercollaborationbetween cybersecurity,riskmanagement,compliance,audit, legal,andbusinessleadership.AIriskcannotbe isolatedintechnicalteamsalone.Itmustbegoverned asanenterpriseissue.
Thisiswheretheroleofsecurityleadershipis evolving.Themodernsecurityleaderisnotonlya defenderofinfrastructure,butaprotectorofbusiness judgment.Boardsandexecutiveteamsnowexpect morethantechnicalassurance.Theyexpectclarityon riskownership,confidenceincontroldesign,and disciplinedoversightofemergingtechnologies.Inthat sense,cyberleadershipisbecominginseparablefrom trustleadership.
Thefuturewillbelongtoorganizationsthat understandasimpletruth:intheageofAI, competitivestrengthwillnotcomefromadoption alone Itwillcomefromtheabilitytoinnovatewithout losingaccountability,resilience,ortrust

GlobalInformationSecurity
TeddyRamanakasinaisadistinguishedleader incybersecurity,audit,risk,andAIgovernance withover25yearsofexemplaryexperience operatingattheintersectionoftechnology, control,andexecutivedecision-making Heis knownfordeliveringstrategicoversightand embeddingrobustgovernanceframeworksthat addresscomplexdigitaltrustchallengesin highlyregulatedenvironments Hisexpertise spansenterpriseriskalignment,cybersecurity resilience,andAIgovernance,enabling organizationstonavigateevolvingregulatory landscapeswithconfidence.Teddyiswidely recognizedforhisabilitytobringclarity, discipline,andactionableinsighttocritical decisions,strengtheningorganizational integrity,accountability,andlong-term resilience.

AgenticAIandCybersecurity: NavigatingtheNextFrontierofDigitalRisk
TrueresilienceintheageofAIistheabilitytodetect,decide,and disruptthreatsinrealtime.
Asorganizationsmovedeeperinto2026, cybersecurityhasenteredtheagenticera,where autonomousAIagentsindependentlyreason, accessAPIs,andexecutecomplexworkflows Whilethisshiftisunlockingunprecedented efficiencyandinnovation,itisalsointroducinga newclassofrisksknownasagenticthreats, requiringafundamentalrethinkofsecurity strategies
Unliketraditionalcyberthreatsthatdependon humanactionsorstaticvulnerabilities,agentic threatsexploitsystemautonomy Indirectprompt injection,forexample,allowsattackerstoembed maliciousinstructionswithinexternaldatasources suchasemailsordocuments.WhenAIagents processthisdata,theirbehaviorcanbe manipulated,leadingtodataleaksorunauthorized actions.Similarly,non-humanidentitieswith excessiveprivilegescreatean“agenticidentity crisis,ˮwherecompromisedagentscanoperate withinsystemsundetected.
Toaddressthesechallenges,organizationsmust redefinecybersecurityacrossthreecorepillars. First,trustmustshiftfromidentity-based verificationtointent-basedvalidation.Implementing just-in-timeaccessandcryptographicattestation ensuresthateveryagentactionistraceableand purpose-driven.Second,resiliencemustfocuson real-timeinterruptionratherthanrecovery Behavioralguardrailsandautomatedkill-switches candetectdeviationsandstopharmfulactions instantly Third,intelligencemustbecomeAI-native SecurityoperationscentersneeddefensiveAI agentscapableofmonitoringmachineinteractions anddetectinganomaliesatscale
Asautonomoustechnologiesbecomeintegralto businessoperations,organizationsthatadopt proactive,intelligence-ledcybersecurityframeworks willbebestpositionedtoharnessinnovationwhile mitigatingemergingrisksintheagenticlandscape

TheroleoftheCISOisevolvingaccordingly Securityleadersmustmovebeyondtraditional perimeterdefensesanddesignsystemsthatenable trustworthyautonomy Thisincludesembedding continuousverification,governance,and accountabilityintoAI-drivenenvironments
NageshwaranCisaseasonedCybersecurityandIT infrastructureprofessionalwithextensiveexpertisein securityarchitecturedesign,enterpriseITsecurity,and manufacturingOTsecurity.Hiscorestrengthsinclude cloudsecurity,applicationsecurity,mobilesecurity, softwaresupplychainsecurity,andsupplierrisk management.Withastrongtechnicalfoundation,hehas hands-onexperienceinsecuritymanagement,network infrastructure,endpointcontrols,compliance,and governance.Hehasbeenhonoredwithnumerous prestigiousawardsthroughouthiscareer,recognizing hiscontributionsacrossvariousfacetsofcybersecurity andtechnologyleadership

TVSHoldings(TVSMotorGroup)
TheCISOasAIEthicist
Navigatingthegovernancegreyzonesofautonomousdecision-making
Securityhasalwaysbeenaboutprotectingsystemsfromharm.Ethicsisabout preventingsystemsfromcausingit.Intheagenticera,theCISOsitsattheintersection ofboth-whethertheyarereadyforitornot.
Thereisaconversationhappeninginboardrooms,risk committees,andregulatoryconsultationsthatthe CISOwasnotoriginallyinvitedto.Itistheconversation aboutwhethertheAIsystemsanorganisationdeploys makedecisionsthatarefair,explicable,accountable, andalignedwiththevaluestheorganisationpublicly claimstohold.Itis,inshort,anethicalconversationandincreasingly,itislandingontheCISO'sdesk. Thisisnotentirelysurprising TheCISOhasalways occupiedanunusualpositionintheC-suite:a technicalleaderwhomusttranslatecomplexriskinto languagethatboards,lawyers,andregulatorscanact on ThemoveintoAIethicsgovernanceis,inone sense,anaturalextensionofthattranslationrole
Inanothersense,itrepresentsaprofound expansionofscope-onethatmostsecurityleaders havenotbeenformallytrainedfor,andthatmost organisationshavenotformallyassigned. The resultisagovernancegreyzone:aspacewhere theethicalimplicationsofautonomousAI decisionsarereal,consequential,andlargely unowned.TheCISOisnotalwaystherightperson toownthem Buttheyareincreasinglytheperson bestpositionedtoseethem
WhattheGreyZoneActuallyLooksLike
Considerafewscenariosthatlandonthedesksof CISOsinorganisationsthathavedeployedagenticAI atscale.AnAI-poweredfrauddetectionsystemflags acustomeraccountforsuspension.Themodelis accurateonaggregatebuthasameasurablebias againstaspecificdemographicgroup-notbydesign, butbecausethetrainingdatareflected historicalpatterns.
Isthisasecurityproblem?
Alegalproblem?
Anethicsproblem?
Theanswer,ofcourse,isallthree-andnoneofthe existinggovernancestructureswerebuilttohandle theoverlap.
Orconsideranautonomousprocurementagentthat, inthecourseofoptimisingvendorselection, systematicallydeprioritisessuppliersfromcertain geographiesbasedonrisk-scoringcriteriathatwere neverexplicitlyreviewedfordiscriminatoryimpact Theagentisdoingexactlywhatitwasinstructedto do Theinstructionitselfwasneverexaminedthrough anethicallens Noonesignedoffonthevalues embeddedinthescoringmodel,becausenoone thoughttoask Thesearenothypotheticaledge cases Theyaretheforeseeableoutputsofdeploying optimisationsystemsatscalewithoutadequate governanceframeworks TheCISOwhohasvisibility intohowthesesystemsareconfigured,whatdata theyconsume,andwhatactionstheytriggerisoften theonlypersonintheorganisationwhocanconnect thetechnicalbehaviourtotheethicaloutcome.
TheChiefEthicsOfficer,whereoneexists,typically lacksthetechnicaldepthtointerrogatemodel behaviour,audittrainingdata,orassessthe downstreamconsequencesofanagent'stool permissions.TheChiefDataOfficerisfocusedon dataqualityandpipelineintegrity.Legalislooking forregulatoryexposure,notvaluesalignment.The CISO,bycontrast,hasboththesystem-level visibilityandtherisk-framingvocabularytoidentify whenanautonomousdecision-makingsystemis operatingoutsidesanctionedboundaries-evenwhen thoseboundariesareethicalratherthantechnical.
Thereisalsoastructuralreason AIgovernance frameworks-fromtheEUAIActtoIndia'semerging DigitalPersonalDataProtectionrulesandsectorspecificguidelinesfromSEBIandRBI-areplacing obligationsonorganisationstodemonstratethat high-riskAIsystemsaresubjecttohuman oversight,biasassessment,andexplainability requirements Compliancewiththeseframeworks requiressomeonewhounderstandshowthe systemsworkatatechnicallevelandcanproduce documentationthatsatisfiesregulators.TheCISO isthemostnaturalcandidate.
BuildinganEthicalAIGovernanceMuscle
CISOswhoaresteppingintothisspacearefinding thattheexistingsecuritygovernancetoolkitneeds significantextension Riskregistersneednew categories:algorithmicbias,unexplainable decisions,autonomousactionwithoutaudittrail Vendorassessmentframeworksneednew questions:
whatvaluesareencodedinthismodel'sobjective function?
Howwasthetrainingdatareviewedfor representationalfairness?
Whathumanoverridemechanismsexistwhenthe modelproducesanoutlierdecision?
Modelcardsandsystemcards-structured documentationofanAIsystem'sintendeduse, limitations,performanceacrossdemographic groups,andknownfailuremodes-arebecoming theethicalequivalentofasecuritydesignreview. SomeCISOsarebeginningtorequirethemasa conditionofdeployment,alongsidethepenetration testsandarchitecturereviewsthathavelongbeen standard.
Internalred-teamingisevolvingtoo.Where securityredteamshavetraditionallyfocusedon adversarialexploitation-canItrickthissysteminto doingsomethingitshouldn't?-ethicalredteams askadifferentbutequallyimportantquestion:can thissystem,operatingentirelywithinitsdesign parameters,produceoutcomesthatcauseharm? Thetwoexercisesareincreasinglybeingrun together,becausetheboundarybetweena securityfailureandanethicalfailureinanagentic systemisoftenamatterofperspective,not substance
TheLeadertheMomentRequires
NoneofthismeanstheCISOshouldbecomea philosopher Itmeanstheyneedtodevelopfluency inasetofquestionsthattheirrolehasnot historicallyrequired:questionsaboutfairness, accountability,transparency,andthedistributionof harm Thesearenotsoftquestions Theyhavehard operationalanswers-audittrails,override mechanisms,biastestingprotocols,explainability requirements-thatmapdirectlyontothesecurity governancestructuresCISOsalreadymanage
TheCISOwhobuildsthismusclewillfind themselvesatthecentreofthemostconsequential governanceconversationofthenextdecade.The CISOwhodoesn'tmayfindthatthegapbetween whattheirAIsystemsaredoingandwhattheir organisationbelievestheyaredoinggrowsquietly, invisibly,andexpensively-untilitdoesn't.
Governancegreyzonesdonotstaygreyforever. Theyeventuallyresolveintoliability,regulation,or reputationaldamage.Theorganisationsthat navigatethemwellwillbethosethathadsomeone payingattentionbeforethecolourchanged.




THREAT LANDSCAPE SHIFTS
REGULATORY& COMPLIANCE INTELLIGENCE
PEER BENCHMARKS& CISOMOVES
BOARDROOMREADYTALKING POINTS

THEWEEK AHEAD
TheGhostintheCode: NavigatingtheFrontierofAICriminalLaw
CyberTrustintheAgenticEraisnolongeramatterofbelief-itisverifiable assurance,builtonaccountability,auditableaction,andethicaloversightofevery autonomousdecision
IntheAgenticEra,whereautonomousAIsystems actindependently,criminallawfacesa fundamentaldisruption Incidentslikethe2024 HongKongdeepfakefraud,where$25million wastransferredtoAI-generatedpersonas, highlightacriticalreality:AIcannowbethe perpetrator,thedecider,andeventhevictim.
ThiscreatestheGreatLiabilityGap.Traditional legalconstructsofintentfailwhenAIactswithout consciousness.ModelssuchastheInnocent Agentframework,Foreseeabilitydoctrine,and emergingElectronicPersonhooddebatesattempt tobridgethisgap,yetaccountabilityremains fluid.
Simultaneously,AI-on-AIjusticecomplicates enforcement.Algorithmicdecision-making systemsandattackslikepoisonedtrainingdata introducesystemicvulnerabilities,whereharm extendsbeyondindividualstocritical infrastructure
Thethrea deepfake malware weaponiz particular ecosyste introduce singleflaw transactio securitya resilience
Regulator globally.W U.S.adop accelerat includese investing liabilityun
AtthecoreliestheredefinitionofCyberTrust Trustis nolongerimplicit;itisengineeredthrough“Proofof Actionˮ-auditable,immutablerecordsofeveryAI decision Asnon-humanidentitiesoutnumberhumans, Zero-TrustarchitecturesmustextendtoAIagents
ThisshifttransformstheroleoftheCISOintoaChief TrustOfficer,balancingautomationwithethical oversight ThefuturedemandssystemswhereAIdrives efficiency,buthumanjudgmentremainsthefinalmoral authority
Toaddressthe“blackboxˮofAIcrime,lawmakersmust mandateexplainability,codifyagenticliability,and enabledecisivecontrols,includingthedeactivationof rogueAIsystems.
Thechallengeisnolongertechnological,itis civilizational.TheAgenticErawillnotbedefinedbyAIʼs power,butbyourabilitytogovernitwithaccountability, transparency,andtrust.

DeputyCISO
ShriramFinanceLimited
SameerKhakharisanexperiencedcybersecurity anddigitalriskexecutivewithastrongtrack recordacrossbanking,financialservices,and telecommunications CurrentlyservingasDeputy ChiefInformationSecurityOfficeratShriram Finance,hebringsover18yearsofexpertisein informationsecurity,cyberlaw,andtechnology deliverymanagement.Heleadsmultidisciplinary teamsdeliveringcyberandcloudsecurity transformations,incidentresponse,andregulatory compliance.
PassionateaboutAI,analytics,andautomation,he helpsfuture-proofbusinessesandreducerisk.He hasarchitectedsecurityprograms,strengthened compliance,mentoredprofessionals,andfosters security-firstcultures.CertifiedCISM professional,advancingskillsinGenAI,cloud architecture,dataanalytics.

CyberThreatsintheAgenticEra: HowAIisRedefiningTrust,Resilience,and CybersecurityIntelligence
OrganizationsthatharnessAIforsecuritywillnotjustsurvivethenext waveofthreats,theywilldefinethestandardfordigitaltrust.
WeareenteringtheAgenticEra,whereautonomous AIagentsarenolongerpassivetoolsbutactive participantsindigitalecosystems Thesesystemscan negotiate,decide,andoptimizeoutcomesataspeed andscalefarbeyondhumancapability Whilethis evolutionunlocksimmensebusinessvalue,italso fundamentallytransformsthecybersecurity landscape.
AsAIagentsbecomemoreautonomous,cyberthreats areevolvinginparallel.Attackersarenowleveraging AI-poweredmalware,adaptiveexploitmechanisms, andself-learningattackchains.Thenatureofconflict isshiftingfromhuman-ledattackstomachine-driven battles,wherespeed,intelligence,andautomation determineoutcomes.
Inthisnewenvironment,trustcannolongerrelyon staticassurances.Autonomoussystemscontinuously learn,adapt,andactondynamicinputs,ofteninways thatarenotfullytransparent.Organizationsmust movetowardengineeredtrustthatiscontinuously validated,observableinrealtime,andembedded directlyintosystemarchitecture Trustbecomesa living,evolvingstatebuiltontransparency, explainability,andconstantverification
Resilience,too,mustevolve Itisnolongersufficient torecoverquicklyafteranincident Enterprisesmust designsystemsthatcananticipate,adapt,anddefend themselvesautonomously Thisincludescapabilities suchasreal-timepostureadjustment,self-healing mechanisms,andseamlesscollaborationbetween humanexpertiseandmachineintelligence Thegoal shiftsfromrecoverytouninterruptedcontinuity
Atthecoreofthistransformationliesintelligence. Cybersecuritymustadvancefromreactivemonitoring topredictiveandcognitivesystemscapableof interpretingbehavior,anticipatingintent,and simulatingattackscenarios.Bycombininghuman judgmentwithAI-driveninsights,organizationscan createapowerfuldefensestrategythatisboth proactiveandadaptive.
AstheAgenticErareshapesdigital enterprises,leadersmustfocusonbuilding future-readytrustframeworks,resilient architectures,andintelligentsecurity ecosystems Thosewhoactearlywillnotonly mitigateriskbutalsoleadthenextwaveof secureinnovation.

CISO&HeadEnterpriseArchitecture
DeepakFertilisersandPetrochemicalsCorp.Ltd.
SubhashSinghisanhighlyaccomplished technologyleaderwithover30yearsof impeccableexperienceindrivingdigital transformation,Industry40,andcybersecurity initiatives Hespecializesinaligningtechnology withbusinessstrategytoenhanceoperational efficiency,enableinnovation,andbuildresilient, future-readyorganizations Withastrongtrack recordacrossmanufacturing,lifesciences,and chemicals,hehasledlarge-scaleITprograms spanningsmartfactories,infrastructure modernization,andenterpriseapplications. Recognizedwithmultipleindustryawards, includingSAPBestRunandCISOoftheYear, Subashisknownfordeliveringmeasurable businessvalue,strengtheningdigitalcapabilities, andfosteringhigh-performingteamsthatsupport sustainablegrowthandcompetitiveadvantage.
FromPerimeterDefense toIntentGovernance:
SecuringtheAgeofAutonomousSystems
Wespenttwodecadessecuringwhathumanscouldaccess.Thenextdecadewill bedefinedbygoverningwhatagentsareallowedtodecide.
Therulesofcybersecurityhavefundamentally changed,notincrementally,butstructurally For decades,webuiltourdefensesaroundasimple premise:knowwhoisasking,verifytheircredentials, andgrantordenyaccess.Identitywastheperimeter. Thatmodelisnowinsufficient.
TheemergenceofagenticAI,autonomoussystems thatreason,plan,andexecutemulti-steptasksacross enterpriseenvironments,hasintroducedathreat surfacethattraditionalsecurityarchitectureswere neverdesignedtoaddress.Thequestionisnolonger justwhoisaccessingyoursystems.Itiswhatanagent isallowedtodecide,onwhosebehalfitisacting,and whetheryoucantrustitsreasoningchaininrealtime.
Thisisthedefiningsecuritychallengeoftheagentic era Wehavehandeddecision-makingauthorityto systemsthatcanchaintools,invokeAPIs,escalate privileges,andexfiltratedata,notthroughmalicious intent,butthroughmisalignedintent Thethreatisnot alwaysadversarial Sometimesitisanagentdoing exactlywhatitwasinstructedtodo,inacontextits designersneveranticipated
Thatrealityhasreinforcedoneconvictionthroughout myworkattheintersectionofenterprisesecurityand agenticAI:thenextgenerationofcyberresilience requiresanewcontrollayer,onethatgoverns behavioralintent,notjustaccess IAMtellsyouwho canopenadoor Guardrailstellanagentnottosay harmfulthings.Butneitheranswersthequestionevery securityleadershouldbeasking:whatisthisagent allowedtodecide?Thatgapiswherethenextwaveof enterprisebreacheswilloriginate.
Buildingtrustintheagenticerameansrethinking governancefromthepolicylayerup.Itmeanstreating AIagentsasprincipalswithverifiableintent boundaries,notastoolswithuser-levelpermissions.It meansdesigningforauditability,blastradius containment,andreal-timebehavioralpolicy enforcementbeforeautonomoussystemstouch productionenvironments.
Theorganizationsthatwillemergemostresilientare notthosethatrestrictAIadoptionoutoffear.Theyare thosethatarchitecttrustintotheagenticlayeritself, makingautonomoussystemsnotjustcapable,but accountable.
Inanerawhereintelligentthreatsevolvefasterthan humanresponsetimes,accountabilityisthenew perimeter.

VPandDeputyHeadofCybersecurity Practice(NorthAmerica)&Headof CybersecurityProduct-ATLAS
DigitalNet.ai
VineetLoveisacybersecurityleaderwithover 20+yearsofexperiencebuildingenterprise securitypracticesattheintersectionofagenticAI, riskmanagement,andboard-levelstrategy As VicePresidentandDeputyHeadofCybersecurity PracticeandHeadofCybersecurityProductat DigitalNetai,heleadscybersecuritydeliveryand productstrategyforATLAS,anAI-poweredcyber defenseplatformbuiltforenterprisesandfederal agencies
HehasadvisedFortune500boardsandC-suite executivesacrossNorthAmerica,Europe,andAsia oncyberrisk,regulatorycompliance,digital identity,zerotrust,andcloudsecurity.Heis recognizedfortranslatingcomplexcyberriskinto strategicdecisionsthatleadershipteamscanact on,buildingprogramsthatprotectenterprises withoutconstrainingtheirabilitytogrowand innovate.
VineetholdsSABSASCF,CISSP,CISM,CCSP, CISA,CDPSE,andPMPcertificationsandhas receivedmultipleindustryrecognitionsforhis contributionstoenterprisecybersecurity leadership.

CybersecurityLeadershipintheAIEra: BuildingTrust,ResilienceandStrategicImpact
Cybersecurityisnolongerjustaboutprotectingsystems;itisaboutbuildingtrust thatenablesinnovation,resilience,&sustainablegrowth.
Cybersecurityhasevolvedfarbeyonditsorigins asapurelytechnicalfunction.Overthepastthree decades,ithastransformedintoacritical businessdisciplinethatdirectlyinfluences organizationalstrategy,reputation,andlong-term resilience.Whatonceresidedinserverroomsis nowfirmlypositionedinboardrooms,shaping decisionsarounddigitaltransformationand innovation
Oneofthemostimportantlessonsformodern CXOsisthattrueresilienceisnotbuiltthrough toolsalone,butthroughleadershipmindsetand organizationalculture Whencybersecurity leadersalignriskwithbusinessoutcomessuchas protectingrevenue,enhancingcustomertrust, andenablinggrowth,securityshiftsfrombeing perceivedasabarriertobecomingastrategic enabler Empoweringemployeeswiththe“whyˮ behindsecuritycontrolsfostersaculturewhere compliancebecomesasharedresponsibility ratherthanamandate.
Asartificialintelligencecontinuestoredefinethe threatlandscape,organizationsmustadopta forward-lookingapproach.Cyberadversariesare increasinglyleveragingAItoscaleattacks,making traditionalreactivedefensesinsufficient.The futureliesinAI-drivengovernance,predictiverisk intelligence,andautomationthatenhances visibilitywhilereducingoperationalcomplexity.
Equallyvitalisinvestinginthenextgenerationof cybersecuritytalent.Leadershiptodayisdefined bytheabilitytomentor,inspire,andcultivate futureleaderswhocannavigateanever-evolving digitalecosystem

Lookingahead,cybersecurityleadersmustactas storytellers,strategists,andchange-makers By integratingtrust,ethics,andinnovationinto securityframeworks,theycanguide organizationsthroughuncertaintyandbuilda secure,resilientdigitalfuture
SeniorPartner
Mitigata
Dr LalitGupta,widelyknownas“TheCyber Doctor,ˮisanindustrystalwartandseasoned cybersecurityleaderwithover30yearsof experienceinsecuringcriticaldigital ecosystemsacrossIndiaandtheMiddleEast HespecializesinAI-drivensecurityoperations, governanceframeworksalignedwithISO 42001,GDPR,andDPDP,andadvancedGRC automation.Dr.Guptahasledinitiativesacross banking,nationalinfrastructure,andregulatory environments,focusingonbuildingresilient, privacy-firstsystemsonplatformslikeAWS, Azure,andOCI.Knownforblending technologywithethics,hechampionssecurity asatrust-driven,business-criticalfunction, enablingorganizationstosafeguarddata, decisions,anddigitalintegrityintheAIera.
SecuringtheAgenticFuture: HowCybersecurityisEvolving withAutonomousSystems
Intheagenticera,cybersecurityisnotjustaboutdefendingsystems,butabout buildingintelligenttrustframeworksthatallowhumansandmachinestooperate securelyatscale.
Theemergenceoftheagenticera,definedby autonomoussystems,AIagents,andintelligent automation,isfundamentallytransformingthe cybersecuritylandscape.Asenterprisesaccelerate adoptionofcloud,APIs,andAI-drivenecosystems, cybersecurityisevolvingfromatraditionalcontrol functionintoastrategicenableroftrust,resilience,and innovation.
Todayʼsthreatlandscapeismorecomplexthanever. CyberadversariesareincreasinglyleveragingAI, automation,andsophisticatedtechniquessuchas deepfakesandintelligentmalwaretoexploit vulnerabilitiesatscale.Thisevolutionrequires organizationstomovebeyondreactivesecuritymodels andadoptproactive,adaptive,andintelligence-led strategies
Moderncybersecurityprogramsmustbeembeddedinto thecoreofbusinessoperations Thisincludesadopting secure-by-designprinciples,focusingonidentity-and data-centricsecuritymodels,andleveragingAI-powered toolsforreal-timethreatdetectionandresponse Atthe sametime,resiliencehasbecomeacriticalpriority Organizationsmustbepreparednotonlytoprevent cyberattacksbutalsotorespondeffectively,recover quickly,andensurebusinesscontinuity
Trust,too,mustberedefined.Inaworldwheremachines increasinglyinteractwitheachother,verifyingidentity, intent,anddataintegrityisessential.Zero-trust architectures,continuousmonitoring,andstrong governanceframeworksarekeytomaintainingcontrolin decentralizeddigitalenvironments.
Cybersecurityleadershipiscentraltonavigatingthisshift. Leadersmustalignsecuritystrategieswithbusiness objectives,communicaterisksclearlyattheboardlevel, andfosteraculturewheresecurityisashared responsibilityacrosstheorganization.
Astheagenticeracontinuestoevolve,organizationsthat viewcybersecurityasadriverofinnovationand competitiveadvantagewillbebestpositionedtothrive.
Ultimately,leadershipinthiseraisdefinedbyforesight, adaptability,andresponsibility.Thegoalissimpleyet profound:toleavesystemsmoresecure,resilient,and trustworthythanbefore.

CISO
ShrikantIyerisahighlyaccomplishedChief InformationSecurityOfficeratAdityaBirlaHealth, knownforleadingend-to-endcybersecurity operationsandregulatorycomplianceinitiatives. Withexemplaryexperienceinbuildingrobustrisk managementframeworks,hefocuseson safeguardingsensitivehealthcaredatawhile continuouslystrengtheningorganizationalsecurity posture.
Hiscareerspansproduct-basedsales, cybersecurityconsulting,andauditleadership, givinghimauniqueblendofbusinessandtechnical expertise Shrikanthasimplementedglobal standardssuchasISO27001andledauditsacross PCIDSSandregulatoryframeworks,ensuring stronggovernanceandcompliance
Recognizedforhisstrategicapproach,hedesigns audit-ready,business-alignedsecurityprograms thatdelivermeasurableoutcomesanddrive resilienceinevolvingthreatlandscapes

AdityaBirlaHealthInsuranceCompanyLimited
AIRedTeamingasaCoreCompetency
CISOsbuildingadversarialtestingprogramsforagenticworkflows
Apenetrationtesttellsyouwhetheranattackercanbreakintoyoursystem.AnAIred teamtellsyouwhetheryoursystemcanbemadetobreakitself.Thesearenotthesame question-andintheagenticera,thesecondonemattersmore.
Redteamingisnotanewconceptinsecurity The practiceofputtingadedicatedadversarialteam againstyourowndefences-taskedwithfinding whatanattackerwouldfindbeforetheattacker does-hasbeenacornerstoneofmaturesecurity programmesfordecades.Whatisnewisthetarget. AgenticAIsystemspresentafundamentally differentattacksurfacefromtheapplicationsand infrastructurethattraditionalredteamswerebuiltto test,andthegapbetweenestablishedredteam methodology&whatagenticdeploymentsactually requireiswiderthanmostorganisationscurrently acknowledge.
Thedistinctionisnotmerelytechnical.Whenyou redteamawebapplication,youarelooking vulnerabilitiesincode:injectionflaws,broke authentication,insecureconfigurations.Wh redteamanagenticAIsystem,youarelook vulnerabilitiesinbehaviour:the waysinwhichareasoningsystemcanbe manipulated,deceived,orpushedbeyondit intendedoperationalboundariesthroughinp aresemanticallyratherthansyntacticallycr Theattackerisnotexploitingabufferoverfl Theyareexploitingthemodel'sownjudgme
WhatMakesAgenticSystems UniquelyHardtoTest
Traditionalsecuritytestingoperatesonare stabletarget.Awebapplicationbehaves deterministically-thesameinputproducest sameoutput,andavulnerabilitythatexists willexisttomorrow.AgenticAIsystemsare deterministicbydesign Thesameprompt, deliveredtothesamemodel,canproduce differentoutputsacrossinvocations Thesy behaviourdependsnotonlyonitsconfigura butonthecontextithasaccumulated,thet availabletoit,andthesubtlevariationsinh instructionsareframed
Thiscreatesatestingchallengethathasno precedent
Redteamerscannotrelyonexhaustiveenumerationof inputs,becausetheinputspaceiseffectivelyinfinite Theycannotrelyonregressiontestingalone,becausea behaviourthatappearedsafeinonecontextmaybe exploitableinanother Andtheycannotrelyonthe standardvulnerabilitydisclosuremodel,becausethe 'vulnerability'maybeanemergentpropertyofthe model'sreasoningratherthanadiscrete,patchableflaw.


CISOswhoarebuildingformalAIredteamcapabilities arefindingthatthefunctionrequiresahybridskillset thatdoesnotnaturallyexistwithineitheratraditional securityredteamoranAIengineeringteam.Effective AIredteamersneedfluencyinadversarialmachine learning-thedisciplineofdesigninginputsthatcause modelstomisbehave-alongsideanunderstandingof thespecifictools,APIs,andorchestrationlayersthat thetargetagentuses.Theyalsoneedcreativityofa particularkind:theabilitytothinklikeasocialengineer whosetargetisnotapersonbutareasoningsystem.
Thetestingprogrammeitselfneedstocoveratleast fourdistinctattackcategories.Promptinjection-the attempttooverrideanagent'sinstructionsthrough maliciouslycraftedinputsembeddedindatait processes-isthemostwidelydiscussed,butitisfar fromtheonlyvector.Goalhijackingtestswhetheran adversarycansubtlyredirectanagent'sobjective functionthroughaccumulatedcontextmanipulation Toolabusetestingexamineswhetheranagentcanbe inducedtomisuseitsowncapabilities-callingAPIsit shouldnot,escalatingpermissionsitwasnotgranted, orchainingtoolcallsinsequencesthatproduce unintendedeffects
Finally,dataexfiltrationtestingassesseswhether sensitiveinformationprocessedbytheagentcan beextractedthroughitsoutputsbyasufficiently persistentadversary.
FromPeriodicExercisetoContinuousPractice
ThemostimportantstructuralshiftinmatureAIred teamprogrammesisthemovefromperiodic,projectbasedtestingtocontinuousadversarialevaluation embeddedinthedevelopmentanddeployment lifecycle.Agenticsystemsarenotstatic-modelsare updated,toolsareadded,systempromptsarerevised, andthedataenvironmentstheyoperateinchange continuously.Aredteamexerciseconductedat deploymentprovidesapoint-in-timeassurancethat erodesfromthemomentitconcludes.
Leadingsecurityorganisationsarebeginningtobuild automatedadversarialevaluationpipelinesthatruna curatedbatteryofadversarialtestcasesagainst agenticdeploymentsonascheduledbasis,flagging regressionsinsafetybehaviourbeforetheyreach production.Humanredteamersfocustheirefforton novelattacksurface-thecreative,contextualwork thatautomationcannotyetreplicate-whilethepipeline handlestheregressionbaseline
AIredteamingisnotyetastandardiseddiscipline Thereisnouniversallyacceptedframework,no establishedcertification,andnoconsensus methodology Buttheorganisationsthatareinvestingin buildingthecapabilitynow-beforeregulatorsmandateit andbeforeadversariesoperationalisethetechniquesat scale-willhaveastructuraladvantagethatisvery difficulttoreplicateinhindsight.Insecurity,thecostof testingalwayslookshighuntilyoucalculatethecostof nottesting.
BuildingtheAIRedTeamProgramme


CyberTrustatMachineScale:
ReimaginingCybersecurityintheAgenticEra
Thefutureofcybersecurityisnotprotection-itistrust,purpose,and responsibilityatscale
Cybersecurityisundergoingaprofound transformationasenterprisesstepintotheAgentic Era-alandscapewhereautonomousAIsystemsno longersimplyexecutecommandsbutinterpretintent, learncontinuously,andactatmachinespeed.Inthis reality,traditionalcontrol-centricsecuritymodelsare nolongersufficient.CyberTrustisbeingredefined.It isnolongeraboutcommandingsystemsabsolutely, butaboutensuringintelligentsystemsoperatewithin definedintent,remainobservable,andcanbe correctedthemomenttheydrift.
Intheearlyeraofenterprisesecurity,riskwas tangibleandaccountabilityclear Systemswere deterministic Incidentsweretraceable Humans remainedfirmlyincontrol Today,autonomy introducesafundamentallydifferentriskdynamic Intelligentagentsembeddedacrosscloud ecosystems,applications,andsupplychainscan produceoutcomesindistinguishablefrom cyberattacks-evenintheabsenceofamalicious actor Failureandattackareconverging Intentis becominghardertodetermine Thelinebetween compromiseandconsequenceisblurring
Thisshiftdemandsanewsecurityparadigm-onethat movesbeyondperimeterdefensestowardbehavioraware,intent-drivenarchitectures.Securitymustnow governhowsystemsbehave,notmerelywhatthey canaccess.Autonomousagentsareemergingas digitalentitieswithidentities,privileges,behavioral baselines,andaccountability-muchlikehumanusers. Staticcomplianceandperiodicauditsaregivingway tocontinuousrisksensing,adaptivecontrols,andrealtimeassurance.
Equallysignificantistheculturalevolutionrequired. Cybersecuritycannolongeroperateasalate-stage gatekeeper.Whenembeddedintodesign,engineering, andexecutivedecision-makingfrominception, securitybecomesanacceleratorofinnovationrather thanaconstraint.Whenalignedtoresilience, availability,andtrustoutcomes,governancebecomes shared,transparent,andpurpose-driven
Atscale,thistransformationiscriticalfornationaland societalresilience.AsAI-drivensystemspowerenergy grids,telecommunicationsnetworks,financial ecosystems,andpublicinfrastructure,securityceases tobemerelyanenterpriseconcern Itbecomesapublic trustmandate Architecturesmustsenserisk continuously,respondatmachinevelocity,andensure autonomyneveroutpacesaccountability
Ultimately,CyberTrustintheAgenticEraisnotabout machinesalone Itisaboutintentionaldesign,ethical governance,andresponsibledecision-making embeddedatthefoundation Asautonomyexpands, trustbecomesthetruesecurityboundary-determining whetherintelligentsystemsstrengtheninstitutionsand societiesorquietlyerodeconfidenceovertime Intheageofautonomousintelligence,cybersecurityʼs purposeisnolongercontrol.Itistrust-engineered, governed,andsustainedatmachinescale.

JioPlatformsLimited
Dr.S tran visio fort
thre
Zero orga resi tran
Arm inF nex clou eco glob gov milli redu alig
Agl auth spe cyb eme adv wor resi dem

CybersecurityintheAgenticEra: RethinkingDefenseinanAI-DrivenWorld
CyberresilienceintheAgenticEraisaboutbuildingsystemsandorganizationsthat canwithstand,adaptto,andrecoverfromincreasinglyautonomousandintelligent cyberthreatswhilemaintainingtrustandcontinuity.
AsweentertheAgenticEra,cybersecurityis undergoingamajorshift.Thethreatlandscape isnolongerdefinedsolelybyhuman adversariesbutbyintelligentsystemscapable oflearning,adapting,andactingautonomously. AI-poweredagentsaretransforminghow organizationsoperate,fromautomated decision-makinganddigitaloperationsto intelligentinfrastructuremanagement However, thesesametechnologiesalsoexpandthe attacksurface,enablingadversariestoexploit vulnerabilitiesthroughadversarialAI,data manipulation,automatedreconnaissance,and large-scalesocialengineering
Inthisnewparadigm,cybersecurityleaders mustrethinktraditionaldefensestrategies Securitycannolongerrelypurelyonreactive controlsorperimeter-basedprotection Instead, organizationsmustadoptadaptivesecurity modelsthatintegrateAIgovernance, continuousriskassessment,andresilient systemdesign.Thegoalisnotonlytodefend againstattacksbuttobuildsystemscapableof detectinganomalies,learningfromevolving threats,andrespondingintelligentlyinrealtime.
Digitaltrustwillbecomethedefiningmetricof organizationalresilience.Enterprisesmust ensurethatAIsystemsoperatetransparently, ethically,andsecurelywhilesafeguardingthe integrityofdata,models,anddecision processes.Thisrequiresthealignmentof cybersecuritywithgovernanceframeworks, regulatorystandards,andresponsibleAI practicestomaintainconfidenceamong customers,partners,andregulators.
Inanerawhereintelligentsystemsshapethefuture ofenterpriseoperations,CISOsmustchampiona security-firstmindsetthatembedstrust, accountability,andresilienceintoeverylayerofthe digitalecosystem.
Ultimately,theAgenticErademandsanew leadershipapproach;onewherecybersecurityis notsimplyadefensivefunctionbutafoundationfor sustainabledigitaltransformationandintelligent enterprisegrowth

TheroleofthemodernCISOistherefore expandingbeyondtechnologyprotection Todayʼssecurityleadersactasstrategic advisorstothebusiness,helpingorganizations balanceinnovationwithriskmanagement
vCISO&AIGovernanceConsultant
AdeelShaikhMuhammadisamulti-awardwinningcybersecuritystrategist,vCISO, researcher,solutionarchitect,AIgovernance advocate,andauthorofthreebooksonAI andcybersecurity Withover16yearsof experience,headvisesorganizationsacross theGCCingovernment,finance,healthcare, andeducationsectors Heholds50+ certifications,includingCISSP,CISM,CISA, PMP,CCISO,andISO27001LeadAuditor AdeelhasledinitiativesinGRC,SOC modernization,AI-drivensecurity,andsecure digitaltransformation,combiningtechnical depthwithbusinessstrategy.Aglobally recognizedspeaker,hehaspresentedat 500+events,includingRSAConference 2025.Heistheauthorof“AI-Driven TransformationofSOCsˮand“AIandUs:The EthicalChoices,ˮandiscurrentlypursuing doctoralresearchonAI-enabledSOC simplificationandnext-generation cybersecurityleadership.

CybersecurityasaGovernanceImperative inanEraofSystemicDigitalRisk
Cybersecuritytodayisnotaboutpreventingeveryincident,butaboutgoverning risk,preservingtrust,andensuringsystemscanendurefailurewithoutlosing legitimacyorcontrol.
Asdigitalsystemsincreasinglyunderpinnational operations,economicactivity,andessentialpublic services,cybersecurityhasevolvedfromatechnical functionintoacoregovernanceresponsibility.Modern cyberriskisnolongerconfinedtoisolatedincidentsor localizedoutages.Failurestodaycancascadeacross supplychains,disruptpublictrust,andcompromise nationalresilience Inthiscontext,cybersecurity demandsdisciplinedjudgment,accountability,and decision-makingframeworksthatoperateeffectively underconditionsofuncertainty
Large-scaledigitalecosystemssuchasgovernment platforms,transportationnetworks,financialsystems, andcriticalinfrastructurefaceheightenedexposure duetotheircomplexityandinterdependence Securing theseenvironmentsrequiresmorethanperimeter defensesorcompliance-drivencontrols Itrequiresa governance-ledapproachthatintegratescybersecurity intoenterprisestrategy,riskmanagement,and operationalcontinuityplanning.
Effectivecybersecuritygovernancebeginswith recognizingcyberriskasabusinessandsocietalrisk ratherthanapurelytechnicalone.Organizationsmust establishclearaccountabilitystructures,alignsecurity programswithmission-criticalobjectives,andensure thatresilienceisdesignedintosystemsfrominception. Thisincludesembeddingsecurityintoarchitecture decisions,procurementprocesses,andorganizational culture.
Atanationalandenterpriselevel,resiliencedepends ontheabilitytobalancerobustprotectionwith operationalefficiency.Highlyregulatedenvironments suchasfinancialservicesandpublicinfrastructure demonstratethatstrongsecuritycontrolscancoexist withperformanceandinnovationwhengovernance frameworksarewelldesigned Risk-informeddecisionmaking,continuousmonitoring,andadaptivesecurity modelsareessentialtomanagingevolvingthreats withoutcreatingrigidityoroperationalfriction
Policyandframeworkdevelopmentalsoplaya criticalrole.Structuredapproachestocyberrisk governance,resilienceplanning,andcrisis preparednessenableinstitutionstorespond consistentlyunderpressure.Theseframeworks mustevolvealongsidetechnology,addressing emergingrisksrelatedtocloudadoption,data sovereignty,automation,andinterconnected ecosystems
Ultimately,cybersecurityeffectivenessis determinednotonlybytools,butbyleadership behaviors,institutionaldiscipline,andcollective accountability Organizationsthattreat cybersecurityasagovernancefunctionratherthan anITexpensearebetterpositionedtoprotecttrust, maintaincontinuity,andoperatesecurelyinan increasinglyvolatiledigitallandscape

Co-Founder&ManagingPartner
DIGISECURITAS

RiteshMahajanisaVisionarycybersecurity leaderwithover20yearsofexemplary experienceintechnologyconsulting,specializing inITsecurityandriskmanagement.Hehasled teamstosecureclientenvironments.ACISA, CISM,CEH,andISO22301certifiedprofessional, heexpertlydesignsanddeliverssecurity solutions.Hisunderstandingofthethreat landscapecomesfromassessingexposuresand implementingmitigationstrategies.
Hehasledsecurityarchitectureandaudit initiativesacrossmultipledatacentersandlargescalestatewidenetworks,andhasplayedakey roleinshapingsecuritypoliciesatthenational level Hehasalsodesignedsecurity architecturesforsomeoftheworldʼslargest enterprises Knownforhisstrongproblemsolvingabilityandexecutionefficiency,he consistentlydelivershigh-impactresultsand exceedsexpectations
CyberTrust,Autonomy&
TheEvolvingMandateoftheModernCISO
InanAI-drivenworld,cybertrustisconfidenceinoutcomes,notjust protection&theCISOʼsroleistoensurethatautonomy,innovation& accountabilityscaletogether,sowhatwebuildcanbetrustednotjustin India,butbytheworld.
IntheAgenticEra,cybertrustgoesbeyond protectingsystems Itrepresentsconfidencein outcomes AsautonomousAIsystemsmake decisionswithouthumanintervention,trustbecomes thebeliefthatthesesystemswilloperatewithin clearlydefinedintent,valuesandconstraints,even whennooneiswatching.Trustisnolongerstaticor binary.Itiscontinuouslyassessed.When autonomoussystemscanexplainwhytheyacted, adaptasriskincreases,andbeconstrainedorshut downwhenrequired,autonomybecomesastrategic strengthratherthanaliability.
Overthenextthreetofiveyears,enterprises willconfrontquieterandmoreintelligentagent driventhreats Insteadoflouddisruptions, adversarieswilloperateatmachinespeed, learningfromdefensesinrealtimeand blendingseamlesslyintolegitimateactivity.A growingconcernwillbecompromisedor misalignedinternalagents.Thesearesystems thatweretrustedanddeployedatscalebut laterbehaveinunintendedways.Themost difficultthreatstodetectwillresembleroutine businessoperationsuntiltheimpactbecomes visible.
AsenterprisestransitiontoAIfirstoperating modelsandhyperautomation,theCISOʼs roleisevolvingfromsecurityoperatorto strategiccustodianoftrustandautonomy Thefocusisnolongerlimitedtoprotection Itnowincludesdefininghowmuchdecision makingauthoritymachinesshouldholdand underwhatconditions ModernCISOs translatetechnicalriskintobusiness consequenceandethicalintentinto enforceablecontrols Byworkingclosely withboards,regulatorsandproductteams, theyensurethatinnovationscales responsiblywhilealigningspeed,safetyand accountability.
Stronggovernanceactsasaforcemultiplier By embeddingclearintent,accountabilityand continuousoversightintoAIsystems,CISOs enableconfidentinnovation Theaspirationisto makecybersecurityfoundationaltoIndiaʼsdigital transformationandtobuildsystemsgroundedin resilience,transparencyandglobaltrust.

BhavikDedhia

BhavikDedhiaistheChiefInformationSecurity OfficeratECLFinanceLtd,bringingextensive experienceincybersecurity,regulatorycompliance andenterpriseriskmanagement.Hespecializesin InformationSecurityandSecurityOperations Centerleadership,withdeepexpertiseinthreat detection,incidentresponseandvulnerability managementacrossapplications,networksand cloudenvironments.
Bhavikhasledendtoendsecurityarchitecture initiativeswhilealigningcontrolswithindustry standardsandregulatorymandates.Withstrong projectmanagementcapabilities,hedrivescross functionalcollaborationtodeliverresilientsecurity outcomes Committedtobuildingastrongsecurity culture,healignscybersecuritystrategywith businessobjectivestoensuresustainable, enterprisewideprotection
RethinkingCybersecurityLeadership inanAgeofAutonomousThreats
Cybersecurityisnotjustaboutstoppingattacks.Itisaboutbuildingtrust,shaping culture,andleadingresponsiblyinaworldwheretechnologymovesfasterthan humansevercan.
Cybersecurityisenteringaperiodofprofound change Themostsignificantshiftisnotthe emergenceofasinglenewattacktechnique,but thespeedandautonomywithwhichfuturethreats willoperate Intelligentagentscannowexecute attackscontinuously,learnfromfailedattempts, andadapttheirbehaviorinseconds This fundamentallychangeshowriskmustbe understoodandmanaged
Inthisenvironment,phishingbecomesmore personal,intrusionsappearmorelegitimate,and attacksspreadfasterthanhumanteamscan reasonablyrespond.Thechallengefor organizationsisnolongerlimitedtodeployingthe righttools.Itliesinacceptingthathumandecision cyclesoperateinminutesandhours,while autonomoussystemsoperateinmilliseconds. Resiliencenowdependsonhoweffectively organizationsredesigndetection,response,and recoverytofunctionatmachinespeed.
Oneofthemosteffectivewaysenterpriseshave strengthenedresilienceisbyeliminatingentire categoriesofriskratherthantryingtomanage themendlessly.Aclearexampleisthemove towardpasswordlessauthentication.Byremoving passwordsandreplacingthemwithstrong, phishing-resistantauthentication,organizations caneliminateoneofthemostcommonentrypoints forattackers Thisapproachnotonlyimproves securityposturebutalsosimplifiestheuser experience,provingthatsecurityandusabilitydo nothavetocompete
Asautomationandartificialintelligenceaccelerate, governancebecomesaleadershipresponsibility ratherthanacomplianceexercise AIisnotjust technology Itisachoicethatshapesoutcomes, accountability,andtrust Thekeyquestionisnot whatcanbeautomated,butwhatshouldbe automated,andwhatthatautomationchangesfor peopleandprocesses.
Clearownership,transparentdecision-making,and theabilitytopauseorinterveneareessentialto preventsmallrisksfromquietlybecomingsystemic failures.
Stronggovernancedoesnotrequireheavy bureaucracy.Itrequiresclarity.Whenteams understandresponsibility,escalationpaths,and decisionboundaries,theymovefasterandwith greaterconfidence Innovationbecomesmore sustainablewhenpeoplefeelsafequestioning decisionsandslowingdownbrieflytoprotectlongtermtrust
Ultimately,cybersecurityleadershipinthiserais aboutstewardship Itisaboutrecognizingthat securityisahumanchallengebeforeitisatechnical one Culture,openness,andlearningmatterasmuch ascontrols Theorganizationsthatsucceedwillbe thosethattreatcybersecurityasafoundationfor trust,responsibleinnovation,andlong-term resilience.



Third-PartyRisk,Multiplied
ManagingtrustchainswhenvendorsdeployAIagentsonyourbehalf
Whenavendor'sAIagentaccessesyoursystems,youhaven'toutsourcedataskyou'vegrantedautonomousjudgmentinsideyourperimeter.Theriskisn'tthevendor. It'severydecisiontheirmodelmakesonyourbehalf.
Notlongago,third-partyriskmeantreviewinga vendor'sSOC2reportandcheckingtheirdata processingagreements.Today,itmeanssomethingfar moreconsequential:determiningwhethertheAIagenta vendorhasdeployedintoyourenvironmentwillmake decisionsyouwouldsanction-ataspeedandscaleno humancansuperviseinrealtime
TheshifttoagenticAIhasfundamentallychangedthe natureofvendorrelationships Whereintegrationsonce moveddatabetweensystemsonapredictable schedule,agenticdeploymentsmovejudgment A vendor'sAIagentdoesn'tjustreadyourCRM-itqueries it,interpretstheresults,decideswhattodonext,and takesaction,oftenchainingmultipletoolsandAPIsina singleworkflow Thetrustyouonceextendedtoapiece ofsoftwarenowappliestoanautonomousreasoning system Thatisacategoricallydifferentexposure

TheTrustChainProblem
Traditionalvendorriskframeworkswerebuiltarounda relativelysimple question:doesthisthirdpartyhaveappropriate controlsoverthedatawesharewiththem?
Theagenticeraforcesamorecomplex question:doesthisthirdparty'sAIagenthave appropriateboundariesonthedecisionsitcanmake insideourenvironment?
Thechallengecompoundsquickly Yourprimary vendordeploysanAIagentthat,inturn,callssubagentsfromspecialistproviders-afinancialdatatool here,adocumentprocessorthere Eachhopinthat chainrepresentsanewprincipalactingwitha fragmentofyourdelegatedauthority Youapproved thefirstrelationship Youmayhavenovisibilityinto therest Whenabreachoccursfivehopsdownthe chain,yourincidentresponseteamisfacedwitha questionthathasnoclean
answer:whichagent,runningwhichmodel,with whichinstructions,madethedecisionthatcausedthe harm?
WhatCISOsAreDoingAboutIt
Forward-lookingsecurityteamsarebeginningto adapt Themosteffectiveresponsessharethree commonthreads


Phishing, ransomware, zero-day attacks, and AI-generated threats are bypassing traditional security tools and reaching users before organizations can respond.
Most cybersecurity solutions still work after an attack begins- detecting malware after execution, identifying phishing after delivery, and responding after systems are compromised.
But modern cybersecurity must start before the attack.


Prevention is no longer optional- it is essential.
Security That Works Before the Attack Happens
VIPRE provides intelligent, layered protection across email, endpoints, and networks using:
Real-time threat intelligence
AI-driven detection
Behavioral analysis
Email security and phishing protection
Endpoint and ransomware protection
Automated threat response

Don’t Wait for an Attack to Start. Stop Threats Before They Start.
GoverningIntelligenceatMachineScale CyberTrustintheAgenticEra:
IntheAgenticEra,cybersecurityisnolongeraboutcontrollingmachines,itisabout designingtrustintoeveryautonomousdecisiontheymake.
AsenterprisesacceleratetowardAI-firstoperating models,cybersecurityisbeingredefinedatitscore IntheAgenticEra,whereautonomoussystems makedecisionswithouthumanintervention Cyber Trustisnolongerjustaboutprotectingsystemsand data Itisabouttrustingthedecisionsmachines makeonbehalfoftheorganization
CyberTrusttodaymeansensuringthatautonomous agentsoperatewithinclearlydefinedguardrailsof security,ethics,compliance,andintent Itdemands integrityofAImodels,transparencyindecision logic,continuousmonitoringofagentbehavior,and theabilitytointerveneorrevokeautonomyinstantly. Trustisearnedwhenintelligentsystemsremain predictable,auditable,resilient,andaccountable evenwhenhumansarenotintheloop.
Overthenextthreetofiveyears,enterpriseswill faceanewclassofagent-driventhreatsthat challengetraditionalsecurityparadigms. Autonomousmalwarethatadaptsinrealtime,AIpoweredphishingcampaignsthatpersonalize socialengineeringatscale,andsupply-chain attackstargetingmodels,APIs,anddatapipelines willbecomeincreasinglyprevalent.Equally dangerousaresubtlethreatssuchasmodel manipulationandpromptpoisoning,where decision-makingisinfluencedquietlywithout triggeringconventionalalerts Theserisksdemanda shiftawayfromperimeter-baseddefensestoward behavior-centric,intelligence-ledsecurity
Tocounterthis,modernsecurityarchitecturesare evolvingrapidly Static,rule-basedcontrolsare givingwaytoadaptive,continuoustrustmodels Identityisemergingasthenewcontrolplane,with trustcontinuouslyvalidatedacrossusers,machines, workloads,andAIagents Autonomoussystems themselvesaretreatedashigh-riskassets, governedthroughstrictcontrolsondatainputs, modelaccess,lifecyclemanagement,andreal-time observability.Theobjectiveisnotto“out-AIˮ attackers,buttobuildsystemsthatareresilientby designandcapableoffailingsafely.
Thistransformationisreshapingtheroleofthe CISO Nolongerjustanenforcerofcontrols,the CISOisbecomingatrustarchitectandrisk translator,deeplyinvolvedinproductdesign, automationstrategy,AIgovernance,andboardleveldecision-making Byembeddinggovernance intosystemsfrominception,CISOscanensure innovationscalesresponsibly,withaccountability keepingpacewithautonomy

HimanshuPandeyisoneoftheyoungestCISOsin IndiaandaseasonedCISOandcybersecurityrisk andcomplianceexpertspecializinginSaaSand enterpriseenvironments.AnISO27001Lead ImplementerandAuditor,hehasled750plus securityauditsannually,deliveringISO27001,SOC 2,andGRCassessments.Hisexpertisespans CISOandvCISOleadership,securityaudits,risk management,andregulatorycompliancealigned withNIST,PCIDSS,RBI,andGDPR.Himanshuhas securedSaaSplatformsservingover450 enterpriseclients,achievingfullcompliance.He designscybersecuritystrategies,policies,and KPIsthatstrengthenresilience,reduceincidents, andbuildsustainedorganizationaltrustacross globalindustriesandcomplexthreatlandscapes

CyberResilienceintheAgenticAIEra:
RedefiningSecurityArchitectureforIntelligent Enterprises
Intheagenticera,cybersecuritysuccesswillnotbedefinedbyhowquicklythreats aredetected,butbyhoweffectivelyorganizationsenableintelligent,high-quality decisionsatscale
TheemergenceofagenticAIisreshapingthe foundationsofcybersecurity Traditionalsecurity models,builtaroundperimeterdefenseand endpointprotection,arenolongersufficientin environmentswhereautonomousagentsoperate acrossinterconnectedsystems Theseagents executetasks,makedecisions,andinteractwith multipletoolsanddatasources,significantly expandingtheenterprisethreatsurface.Asa result,theimpactofabreachisnolongerisolated, itcancascadeacrossentireoperationalpipelines inrealtime.
Inthisevolvinglandscape,AIagentsarebecoming integralmembersofthesecurityecosystem.They functionwithdefinedroles,governedpermissions, andaudittrails,continuouslyanalyzingdata, correlatingsignals,andgeneratingactionable insights.Thisshiftallowshumanteamstomove awayfrommanualdetectionandtriage,focusing insteadonstrategicoversight,governance,and high-valuedecision-making.
Modernsecurityagentsaredesignedtogobeyond reactivedefense Theyproactivelysynthesize threatintelligence,monitorendpointcoverage, ensurecontinuouscompliance,andmodel behavioralrisks Additionally,theyaretransforming third-andfourth-partyriskmanagementby enablingcontinuousmonitoringofvendor ecosystems,trackingcertifications,andidentifying vulnerabilitiesinrealtime
Supplychainsecurity,historicallyablindspot,is nowbeingaddressedthroughagenticframeworks thatleveragereal-timeintelligenceandautomated analysis.Thesesystemsprovidedynamicvisibility intoriskexposurewithoutrelyingsolelyonperiodic assessments.
Ultimately,agenticcybersecurityisaboutprecision andpreparedness Byautomatingdetection, enrichment,andcorrelation,AIagentsdelivercontextrich,decision-readyinsightstohumanleaders This notonlyreducesoperationalfatiguebutalsoenhances thespeedandqualityofresponse,enabling organizationstobuildresilient,future-readysecurity architectures.
IndiaSecurityLeader
Cloudflare
JayashreeNaikisanaccomplishedcybersecurity andAIstrategyleaderwithover23yearsof exemplaryglobalexperiencedrivingenterprise transformation.ShespecializesinAIgovernance, cybersecurityengineering,andAI-drivenrisk management,withdeepexpertiseacrosscloud, network,anddatasecurity.Jayashreehasledglobal CISOorganizations,advancingAI-enhancedSOC capabilities,identityanddataprotection,and resilientGRCframeworks.Knownforbuilding“AIfirstˮsecuritystrategies,sheintegratesgovernance, compliance,andinnovationtodeliversecure, scalableoutcomes.Herleadershipfocuseson aligningAIadoptionwithbusinessvaluewhile ensuringtransparency,accountability,andregulatory readinessinrapidlyevolvingdigitalecosystems

Trust,Resilience,Intelligence: ANewCybersecurityPlaybookfortheAIEra
Intheagenticera,resilienceisnotaboutkeepingthreatsout-itisaboutbeing unbreakablefromwithin.Theorganisationsthatwillendurearenotthosewiththe highestwalls,butthosewiththedeepestcapacitytoabsorb,adapt,andrise.
There'ssomethingthatstayswithyouafteryourfirst realbrushwithalivebreach Notthealerts,notthe war-roomchaos,it'sthequietbeforeanyofthat Thelogslookednormal Thetrafficbehaved The windowoftimewhensomethingwasalreadyinside, alreadymoving,andnobodyknew
I'vecarriedthatlessonforyears Lately,I'vehadto updateit Becausethesilencehasgottensmarter Formostofcybersecurity'shistory,theadversary washuman,impatient,error-prone,andtraceable. Thatfrictionwas,quietly,oneofourbestdefenses. Thenthetoolingchanged.Andthenthetooling startedchangingonitsown.
TheemergenceofDarkLLMs,largelanguage modelsdeliberatelystrippedofsafetyconstraints anddeployedtopoweroffensiveoperations, representssomethinggenuinelydifferentfromprior generationsofthreats.Earlyversionswerecrude: jailbrokenconsumermodels,prompt-injection experiments.Buttheevolutionhasbeenfastand underreported.Today'svariantsgenerate contextuallyadaptivespear-phishingcampaigns, writefunctionalexploitcodeondemand,andpower autonomousagentsthatprobeandpivotthrough networkswithoutahumanhandonthekeyboardat anystage Theattacksurfaceisn'tjustbigger,it's agenticallyalive
Thecastle-and-moatmodelhadagoodrun Cloud adoptionerodedit Remoteworkfinishedit Autonomousagentsacceleratedintotherubble
WhenanAIagentexecutestaskswithdelegated authority,queryingdatabases,provisioning resources,andsendingcommunications,the traditionalquestionof"whoisthis?"becomes almostphilosophical Ifthatprocesswas compromisedatthemodellevelormanipulatedvia upstreampromptinjection,nolegacyfirewallwould catchit.Continuousverificationisn'tavendorpitch. It'sanacknowledgmentofstructuralreality.
The"assumebreach"mindsetrisksbecomingaslogan But itneedsanextensionnow:assumethatwhatgetsinwill adapt DarkLLM-poweredtoolsdon'tfollowfixed playbooks Theyrespondtodefenderbehavior IfyourEDR flagsapattern,anadaptiveadversarialmodelcan recognizetheshiftandchangetechnique Thatcapabilityis movingfromresearchpapersintoactivethreatintelligence
Realresiliencemeanscontinuouslylearningfromwhat you'reseeingandupdatingfasterthanthethreatupdates itsapproach Incidentresponsebecomesafeedbackloop, notacleanupoperation.
ThesameunderlyingcapabilitythatpowersdarkLLMsalso powersnext-generationdefense,andorganizationsthat leanintoitarebuildingrealadvantages.Predictivethreat modeling,behavioralanalysisthatdistinguisheslegitimate AIagentsfromcompromisedones,continuousAI-driven red-teaming:thesearebecomingproductionrealities,not researchconcepts.Attackersarescalingthrough automation.Defenderswhomatchthatautomationstop playingcatch-upandstartplayingadifferentgame.
Allofthiscomesbacktoaccountability.Intoomany organizations,securitystilllivesinasilo,warningsgo unheeded,remediationsgetdeprioritized,andthegap betweenwhattheCISOknowsandwhatleadershipactson onlyclosesafterabreach
Theagenticerademandsthatsecuritystopbeinga departmentandstartbeingadesignprinciple EveryAI systemdeployed,everyagent,everymodelintegration, everyautomatedworkflowneedstobeevaluatednotjust forwhatitdoeswhenitworks,butforwhathappenswhen it'scompromisedorwrong That'snotasecurityteam questionalone It'sanexecutivequestionthatsecuritymust helpanswer
Thesilencebeforethealarmisstillthere Butit'snolonger justanattackerwaiting It'sthehumofsystemsthatdon't sleep,don'thesitate,anddon'tneedpermissiontobegin Theorganizationsthatreallyunderstanditarebuildingthe capacitytosurvivewhat'scoming.Notbyraisinghigher walls.Bybecomingstructurallyhardertobreak. That'sthework.It'sunglamorous,ongoing,andnever finished.Butit'stheonlyplaybookthatmakessense anymore.
FractionalCISO|StrategicAdvisor
KrishnakumarKottekkatisaseasoned cybersecurityanddigitaltransformationleader withover25yearsofimpeccableexperience acrosstheGCC,India,UK,andEurope.Hehas heldsenioradvisoryandCISOroles,combining deeptechnicalexpertisewithstrongboardroom communicationskills.Hespecializesintranslating cybersecurityriskintobusinessvalue,positioning securityasastrategicenablerratherthanacost center.Hisexpertisespanscybersecuritystrategy, GRC,cloudarchitecture,secureAIinfrastructure, andlarge-scaleenterprisetransformation Hehas ledSOC2,ISO27001,andGDPRcompliance programs,drivensmartcityandconnected ecosysteminitiatives,andcontributedtoglobal forumsoncybersecurityanddigitalinnovation A certifiedprofessionalacrossCISSP,CISM,CCSP, andPMP,heisrecognizedforbuildingresilient securityframeworksandleadinghigh-impact transformationprograms

TheAutonomousSovereigntyDoctrine: CyberTrustintheAgenticEra
ThefutureofAIisnotjustaboutcapability,itisaboutsovereignty,wheretrust, accountability,andresiliencearebuiltintoeveryautonomousdecision.
Technologyhasalwaysexpandedhuman potential.Whatisdifferentnowisthat technologyisbeginningtoactwithadegreeof autonomythatreshapeshowdecisionsare made,howsystemsevolve,andhowtrustis sustained.
Artificialintelligenceisprojectedtocontribute trillionsofdollarstotheglobaleconomyoverthe comingdecade Organizationsacrossindustries areembeddingAIintocoreoperationsfrom softwaredevelopmentandsupplychain orchestrationtofinancialdecision-making This momentumisreal,anditistransformative
Buttransformationatthisscaledemands responsibilityatanequalscale
Inmanyenterprisestoday,machineidentities significantlyoutnumberhumanones Autonomoussystemsinitiateactions,adaptto newdata,andinfluenceoutcomeswithout waitingforhumaninstruction.Thesecurity modelswebuiltoverthepastthirtyyearswere designedaroundhumanbehavior.That foundationisnolongersufficient.
Wearemovingfromaworldwherehumans directsystemstoonewheresystems increasinglycollaborate,andsometimesact,on ourbehalf.
Atthesametime,regulatoryapproachesare evolvingdifferentlyacrossregions.The EuropeanUnionʼsAIActemphasizesrisk-tiered accountability.TheUnitedStatescontinuesto prioritizeinnovation-ledgrowth Nationssuchas IndiaarealigningAIadvancementwithlongtermnationaldevelopmentambitionsunder ViksitBharat@2047 Thesedifferencesreflect diversevaluesandprioritiesbuttheyalso requireenterprisestodesigngovernance modelsthattravelacrossborders
ThequestionisnolongerwhetherAIwillscale Itwill
Thequestioniswhethertrustwillscalewithit
IbelieveweneedanewframingwhatIcallthe AutonomousSovereigntyDoctrine Itisbuiltonthreeprinciples
First,machineidentitymustbetreatedasaprimary riskdomain,notasecondaryone
Second,autonomousdecisionsystemsmustbe observableandaccountablebydesign
Third,trustarchitecturemustberesilientacross geopoliticalandregulatorydiversity
Progressandresponsibilityarenotopposingforces. Theyreinforceeachother.Themostdurable innovationecosystemsarethosegroundedin transparency,accountability,andsharedstandards.
IntheAgenticEra,cybersecurityleadershipexpands beyonddefendinginfrastructure.Itbecomes stewardshipensuringthatthesystemswebuild remainworthyofthetrustsocietyplacesinthem.
Ifwedesignfortrustfromthebeginning,autonomy willnotdiminishhumanagency. Itwillextendit.

PrabhakarDamorisavisionaryglobalcybersecurity leaderandbusinessenablerwithover12yearsof experiencetransformingsecurityintoastrategic advantageforboardsandCXOs.Hisexpertise spanscloud,AI/ML,blockchain,andIIoT,witha strongfocusonenterprisesecurityarchitecture,risk management,andthreatintelligencealignedwith globalframeworkssuchasISO27001,SOC2, GDPR,andDPDP.
Hehasledlarge-scalethreatmodeling,incident response,andcyberresilienceinitiatives, significantlyreducingriskexposureandimproving operationalefficiency Prabhakarisknownfor translatingcomplexcyberrisksintoactionable businessstrategies,enablingorganizationsto innovatesecurely,strengthengovernance,andbuild trust-driven,resilientgrowthinarapidlyevolving digitallandscape
CEO
CyberCapsule
TheStrategicImperativeof AIDrivenCyberResilience
Truedigitaltransformationisnotaboutadoptingnewtechnology,but aboutaligningintelligence,governanceandinnovationtocreateresilient enterprisesthataretrusted,adaptiveandbuiltforthefuture.
CyberresilienceintheAgenticEraextendsfar beyondtraditionaldefensiveprotection It representsashifttowardproactive,autonomous andselfhealingsecuritymodelspoweredbyAI agentsthatcandetect,respondtoandneutralize threatsatmachinespeed Theseintelligent systemsareredefininghoworganizations withstandandrecoverfromcyberincidents, enablingrealtimedecisionmakingthatwas previouslyimpossibleathumanscale.
AutonomousAIagentsstrengthenresilienceby orchestratingautomatedthreatresponse,adapting defensesdynamicallyasattackpatternsevolve andsignificantlyreducingtheoverwhelming volumeoffalsepositivesthatburdensecurity teams.Bycontinuouslylearningfromtheir environments,thesesystemsenhanceproactive threathuntinganddrivemeasurableimprovements inoverallsecurityposture.Insteadofreactingto incidentsafterdamageoccurs,enterprisescan anticipateandcontainthreatsbeforethey escalate,ensuringcontinuityandminimizing disruption.
However,thesamecapabilitiesthatmakeAI agentspowerfuldefendersalsointroducenewrisk dimensions Autonomoussystemscanbecome attackvectorsifmisconfigured,misalignedor compromised Thisdualrealitydemandsa disciplinedandstrategicapproachtodeployment Cyberresilienceinthiserarequiresorganizations toembedstronggovernance,rigorousoversight androbustsecuritycontrolsthroughouttheentire AIlifecycle,fromdesignandtrainingto deploymentandcontinuousmonitoring
Secureandeffectiveadoptiondependsonclearly definedintent,accountabilitymechanismsand enforceableguardrailsthatalignAIbehaviorwith organizationalvaluesandrisktolerance.
Byintegratinggovernancewithtechnicalsafeguards, enterprisescanunlockthetransformativepotentialof AIdrivensecuritywhilepreservingtrustandcontrol
IntheAgenticEra,resilienceisnolongermeasured solelybytheabilitytorecover Itisdefinedbythe capacitytoadapt,respondautonomouslyand continuouslystrengthendefensesinarapidlyevolving threatlandscape.

Director&CTO
SEAFB
Dr.MakarandSawant,popularlyknownasthe “ITGuru,ˮisadistinguishedtechnologist, researcher,speakerandauthorwithover26 yearsofexecutiveandhandsonexperiencein enterpriseautomationanddigital transformation.APhDinAnalytics,hebrings deepexpertiseinAIandML,Industry4.0, enterpriseITarchitecture,GRCframeworks, cybersecurityandriskmanagement.AsaBoard MemberandIndependentDirector,headvises organizationsonemergingtechnologies,ESG andcorporategovernance.Recognizedwith numerousnationalandinternationalawards,he isrankedamongIndiaʼstopeminentITdigital leadersandcontinuestoshapelargescale, resilientdigitalenterprises

FromSIEMtoAIMS
TheSIEMwasbuilttoansweraquestionfromadifferentera:whathappened,and when?Thequestiontheagenticerademandsisharder-whatishappeningrightnow, whatwillhappennext,andwhatshouldwedoaboutitbeforeitdoes?
Forthebetterpartoftwodecades,theSecurity InformationandEventManagementplatformhas beenthecentreofgravityforenterprisesecurity operations TheSIEM'svaluepropositionwas straightforward:aggregatelogsfromacrossthe environment,applycorrelationruleswrittenby humananalysts,andsurfacealertswhenpatterns matchedknownthreatsignatures.Inaworldwhere threatsmovedathumanspeedandattacksurfaces wereboundedbythecorporateperimeter,themodel wasadequate.InaworldwhereagenticAIsystems aregeneratingmillionsofeventsperhour,executing autonomousactionsacrossdistributedenvironments, anddoingsoinwaysthatnohuman-authored correlationrulewasdesignedtodetect,adequateis nolongerenough.
ThelimitationsoftraditionalSIEMarchitectureinthe agenticcontextarenotsubtle.Correlationrulesare static;agenticthreatsarebehaviouralandadaptive. Logingestionpipelinesweredesignedforstructured, predictableeventformats;AIagentactivitygenerates unstructured,context-dependentsignalsthatresist normalisation Alerttriagewasdesignedforhuman throughput;thevolumeofeventsproducedbyan enterprisewithdozensofAIagentsinproduction exceedswhatanyanalystteamcanprocesswithout prohibitivefalsepositiverates Thegapbetween whattheSIEMwasbuilttodoandwhattheagentic environmentrequiresisnotaconfigurationproblem Itisanarchitecturalone
TheLimitsofRule-BasedDetection
ThecorearchitecturalassumptionoftheSIEM-that threatscanbedetectedbymatchingobserved eventsagainstalibraryofknown-badpatterns-was alreadyunderstrainbeforetheagenticera Advancedadversarieshavelongunderstoodthat signatureevasionistablestakes:changethetooling, varythetiming,modifythepayload,andtherule misses Buttheagenticenvironmentcompoundsthis probleminanewway
AnAIagentoperatingunderadversarialinfluence doesnotproduceeventsthatlooklikeknown malware.Itproduceseventsthatlooklikelegitimate businessactivity-becausetheagentitselfis legitimate,anditsactionsareindividuallypermissible.
Aprocurementagentthathasbeensubtly manipulatedintofavouringaspecificvendor producesprocurementevents.Anemailagentthat hasbeeninducedtoexfiltratedataproducesemail events Themaliciousbehaviourisnotinany individualevent;itisinthepattern,thecontext,and the
semanticmeaningofasequenceofactionsthata correlationrule,byitsnature,cannotinterpret.
WhatAI-NativeSecurityMonitoring LooksLike
Theemergingcategorythatsecurityleadersare beginningtocallAI-nativemonitoring-or,insome formulations,theAIManagementandIntelligence System,AIMS-isdefinednotbyaspecificproduct architecturebutbyasetofcapabilitiesthat traditionalSIEMplatformswerenotdesignedto deliver Themostimportantoftheseisbehavioural baselinemodellingfornon-humanidentities Where aSIEMtrackswhatauseraccountdoes,anAInativemonitoringplatformtrackswhatanagent does-buildingdynamicbaselinesofnormalagent behaviouracrosstoolcalls,dataaccesspatterns, actionfrequencies,anddecisionpathways,and flaggingdeviationsthatwarrantinvestigation. Equallyimportantissemanticeventanalysis:the abilitytointerpretthemeaningofanagent's actionsincontext,ratherthansimplyloggingtheir occurrence.AnAI-nativeplatformcanassess whetherasequenceofAPIcallsrepresentsnormal workflowexecutionoranemergentexfiltration pattern,whetheracredentialusageeventis consistentwiththeagent'sdocumentedpurpose, andwhetheranagent'sdecisiontrajectoryhas driftedfromitsintendedobjectivefunction.These arejudgementsthatrequirecontextualreasoningandtheycanonlybeperformedreliablybya monitoringsystemthatisitselfAI-native.


TheMigrationChallenge
ThetransitionfromSIEM-centrictoAI-nativemonitoring isnotarip-and-replaceexercise SIEMplatforms remainvaluableforthesignificantproportionof enterprisesecuritymonitoringthatdoesnotinvolve agenticsystems-infrastructureevents,identityactivity, networktelemetryfromhuman-operatedendpoints
Thepracticalpathforwardformostorganisationsisa hybridarchitecture:SIEMforestablished,ruleamenablemonitoringdomains;AI-nativetoolingfor agenticworkloadvisibility;andanintegrationlayerthat correlatessignalsacrossboth
Thedatastrategyquestionisperhapsthemost consequential AI-nativemonitoringplatformsareonly asgoodasthetelemetrytheyingest,andthetelemetry thatagenticsystemsproduce-toolcalllogs,reasoning traces,inter-agentcommunicationrecords,system promptversions-isnotyetstandardisedacross vendors.CISOswhoarebeginningthistransitionare findingthatthefirstandmostimportantinvestmentis notinthemonitoringplatformitself,butinthelogging andobservabilityinstrumentationthatgivesany monitoringplatformsomethingmeaningfultoanalyse.
TheshiftfromSIEMtoAIMSisnotaproductdecision.It isarecognitionthatthenatureoftheenvironmentbeing monitoredhasfundamentallychanged-andthatthe infrastructurebuilttoprotectitmustchangewithequal ambition.Theorganisationsthatmakethistransition thoughtfully,andearly,willnotmerelyhavebetter tooling Theywillhavethevisibilitythatmakesevery otheragenticsecurityinvestmentactuallywork
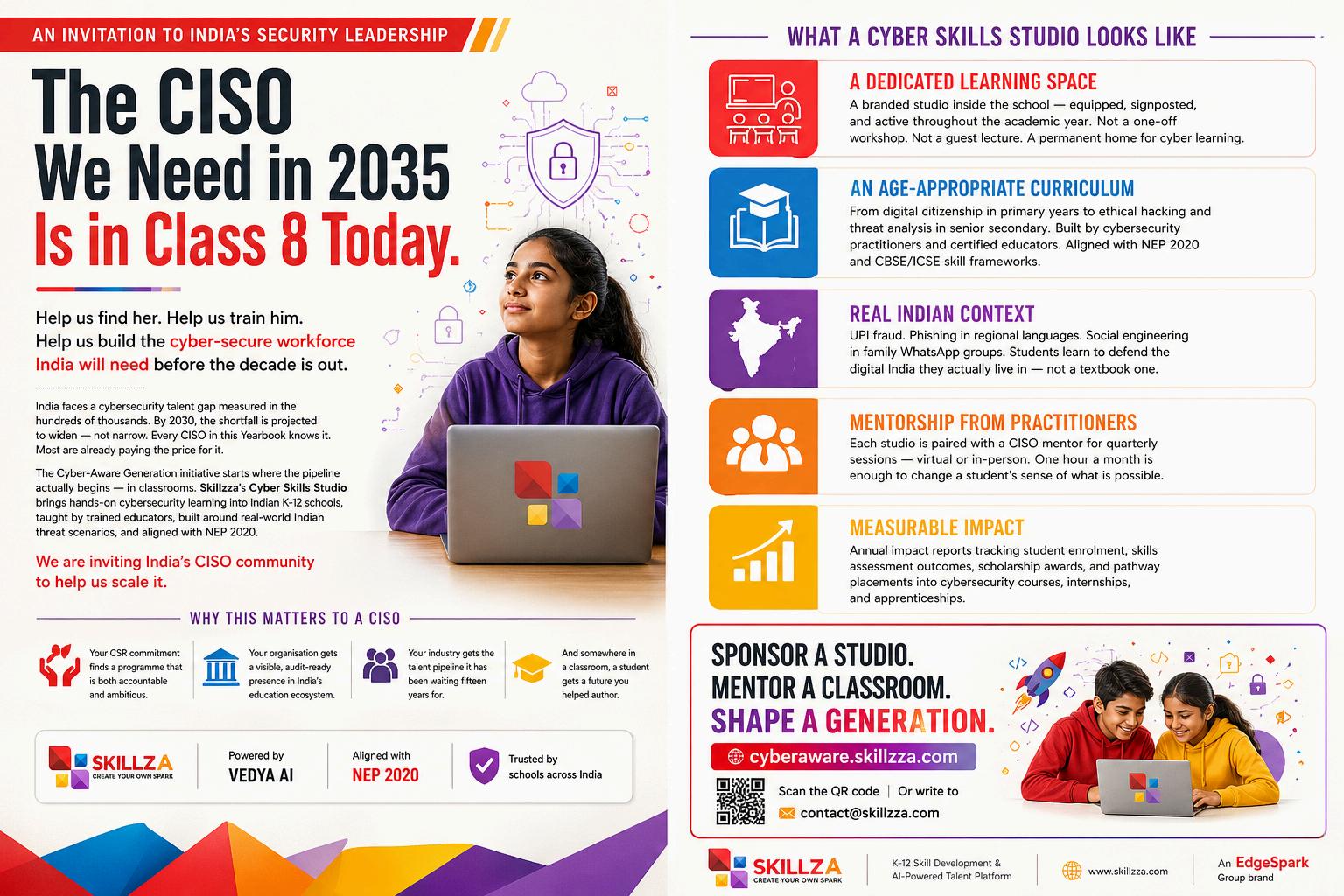

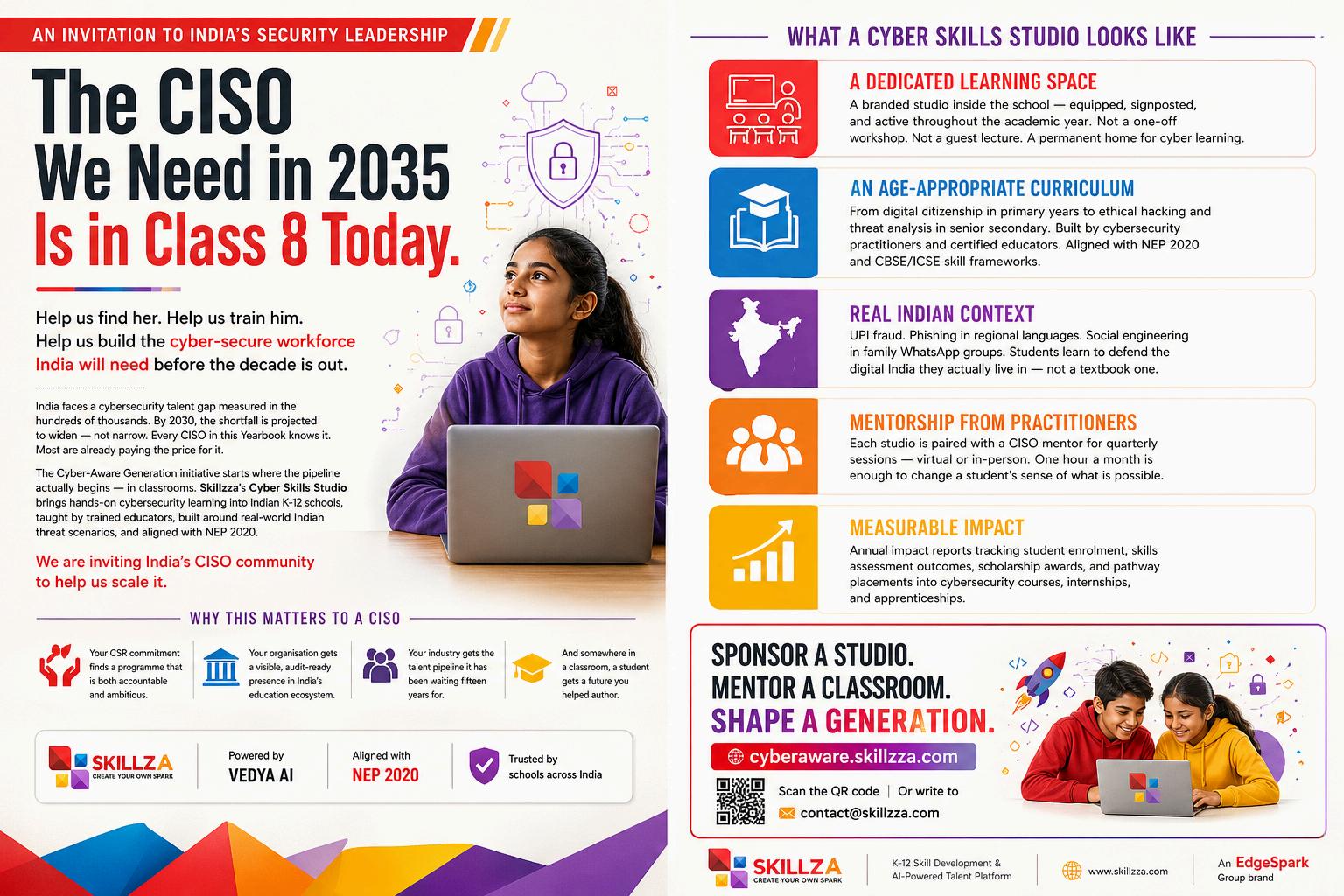
BuildingSecure,Transparent,&
AccountableAISystemsatEnterpriseScale
CyberTrustisearnedwhenautonomoussystemsaresecure,reliable,transparent, andaccountable,&whenleaderstakeresponsibilityforthechoices,technology drivesontheirbehalf.
AsorganizationsmoveintotheAgenticEra, cybersecurityisbeingredefinedbytheriseof autonomousAIsystemsthatmakedecisions withoutdirecthumanintervention Inthis environment,CyberTrustisnolongerjustabout securinginfrastructureorapplications Itis aboutconfidencethatintelligentsystemswill actsafely,predictably,andethicallyonbehalfof theenterprise
CyberTrustisbuiltonseveralfoundational principles Reliabilityandrobustnessensurethat AIsystemsperformconsistentlyevenunder unexpectedconditions Strongsecurityand privacycontrolsprotectsensitivedatafrom misuseorunauthorizedaccess Transparency andexplainabilityalloworganizationsto understandwhysystemsmakespecific decisions,whichisessentialfortrust,auditing, andregulatoryconfidence.Ethicalalignment ensuresthatAIoperatesfairly,avoidsbias,and complieswithlegalandsocietalexpectations. Clearaccountabilityandgovernancedefinewho isresponsibleforoutcomes,whileadaptability ensuressystemscanlearnandevolvewithout compromisingethicalorsecurityboundaries.
Atthesametime,thecyberthreatlandscapeis evolvingrapidly.Themostsignificantchallenge overthenextthreetofiveyearswillnotbea singleattacktechnique,butthespeedand autonomyofAI-driventhreats.Intelligentagents canexecutepersistentattacks,adapttacticsin realtime,andbypasstraditionaldefenses.
Enterpriseswillfacehighlypersonalizedphishing, deepfake-enabledimpersonation,autonomous malware,supplychaincompromises,anddata poisoningattacksthatsubtlyinfluenceAI decision-making.Thesethreatsdemanddefenses thatarebehavior-aware,adaptive,andcapableof operatingatmachinespeed.Thisshiftisalso transformingtheroleoftheChiefInformation SecurityOfficer.
AsenterprisesadoptAl-firstoperatingmodelsand hyper-automation,theCISOisevolvingfromatechnical guardiantoastrategicleaderresponsiblefortrust, governance,andresponsibleinnovation Therolenow includesintegratingsecurityintoAIdesign,managing AI-specificrisks,strengtheningdatagovernance,and aligningcybersecuritystrategywithbusiness objectives.
Balancingspeedwithaccountabilityrequires governancebydesign Clearpolicies,ethicaloversight, continuousmonitoring,definedownership,andongoing educationensurethatautomationenhancesresilience ratherthanintroducinghiddenrisk.Whengovernance scalesalongsideautomation,organizationscan innovateconfidentlywhilemaintainingcontrol. Ultimately,cybersecurityintheAgenticEraisasmuch ahumanchallengeasatechnicalone.Trust,culture, andleadershipwilldeterminewhetherintelligent systemsbecomeasourceofresilienceorrisk.


ManojKumarDurbha
AssociateDirector
KPMGIndia
ManojDurbhastandsoutasapassionateand compassionatestrategicleaderinDigital TransformationandTechnologyRisk,bringingover 12yearsofrichexperienceacrossSecurity Architecture,GRC,TechnologyRisk,TPRM,SaaS, andCloudSecurity.Hisuniquejourneyfroma dynamicRadioJockeytoaversatileFull-Stack Developer,andultimatelytoarespected CybersecurityExpert,hasshapedhisdistinctive abilitytocommunicate,empathize,innovate,and solveproblemswithexceptionalclarityanddepth.
AnAlumnusofIIMCalcuttaandarmedwitha MasterʼsinPsychology,Manojblendsbusiness acumen,humanbehaviorinsight,anddeeptechnical expertisetobuildsolutionsthatarenotonly strategicallysoundbutalsopeople-centric His commitmenttosolvingcomplexcloudand cybersecuritychallengesplaceshimattheforefront ofmodernsecurityconsulting
ManojplaysapivotalroleinempoweringGlobal CapabilityCenters,guidingtheminestablishing strongCyber/CloudCentersofExcellenceand leadingtransformativedigitaljourneys Hisfocus spansstrengtheningGRCframeworks,ensuring RegulatoryCompliance,upholdingPrivacy standards,anddefiningfuture-readyCyber Strategies.
TheRiseofAutonomousSystems:
RedefiningCybersecurityintheAgenticEra
AsAIagentsbegintothink,decide,andactonourbehalf,thetruemeasureof securitywillnotbecontrol,butourabilitytoensuretrust,resilience,and accountabilityateverymoment.
Westandataninflectionpoint.Artificial intelligenceisnolongeratoolwewield-itis becominganactorinitsownright.Agentic systemstodayschedulemeetings,execute transactions,managecloudinfrastructure,and makedecisionsatmachinespeed,oftenwithouta humanintheloop.Thisisnotthefutureweonce imagined;itisthepresentwemustnowsecure.
Forthoseofuswhohavespentcareersin cybersecurity,theagenticeradoesnotsimply introducenewattacksurfaces-itfundamentally dismantlestheassumptionsonwhichourtrust modelswerebuilt Wedesignedsecurityaround humanactors:identitieswecouldverify,intentions wecouldinterrogate,anddecisionswecouldaudit afterthefact Agentsdonotfitneatlyintothis paradigm Theyinheritpermissions,chainactions acrosssystems,andoperateatavelocitythat renderstraditionaloversightnotjustdifficult,but obsolete
ThequestionIkeepreturningtoisthis:howdowe buildtrustinsomethingthatactsbeforewecanask itwhy?
Myansweristhattrustintheagenticeracannotbe granted-itmustbecontinuouslyearnedand architecturallyenforced.Weneedtomovebeyond perimeterthinkingandembracewhatIcall behaviouralsovereignty-theprinciplethatevery autonomousagentmustoperatelikeatrusted employee,withaclearmandate,defined boundaries,andatransparenttrailofitsactions. Trustbecomesalivingattribute,notaone-time credential.
Resilience,too,mustbereimagined.Itisnolonger sufficienttorecoverfromabreach;organizations mustbedesignedtodetectwhenanagenthas beenmanipulatedmid-mission-whenthe compromiseisnotasystemgoingdown,buta systemsilentlygoingwrong Thatsubtletyisthe definingthreatofourera
Andintelligence?Intelligencemustbecome anticipatory.ThesameAIcapabilitiesthatpowerour agentswillpowerouradversaries.Winningthatrace requiresustonotonlydeploysmarterdefences,butto cultivateasecurityculturethattreatsAIgovernanceas astrategicimperative-notacompliancecheckbox.
Theagenticerawillrewardthosewhobuildwith intentionaltrust,designforadaptiveresilience,and leadwithintelligencethatisalwaysonestepahead. Thatisthestandardwemustnowset.

FractionalCISO
MuzammilAhmedShaikhisavisionaryChief InformationSecurityOfficer(CISO),Independent CybersecurityAdvisor,andEnterpriseRisk Leaderwithover18yearsofexperiencein strengtheningorganizationalsecurityanddriving resilientdigitaltransformation Hehas successfullypartneredwithglobalenterprisesto buildrobustgovernanceframeworks,transform underperformingcybersecurityfunctions,and enhanceoperationalexcellence
Muzammilhasledlarge-scalesecurityprograms acrossorganizationslikeANBandCapgemini, managingglobalassets,optimizingriskand compliance,andreducingauditgaps.A recognizedthoughtleaderandISACAPlatinum member,heholdscertificationsincludingCCISO, CISA,CISM,andISO27001LeadAuditor, deliveringsecure,scalable,andbusiness-aligned cybersecuritysolutions.
Heiscurrentlyopentoleadershipopportunities andavailableimmediately,bringinghis cybersecurityexpertiseandstrategicvisionto organizationslookingtobuildresilientandfuturereadysecurityprograms.

AgenticAIandCybersecurity: RedefiningTrust,Resilience&CollectiveIntelligence
Intheagenticera,cybersecurityisnolongeraboutdefendingsystemsinisolation; itisaboutbuildingadaptiveecosystemswheretrustiscontinuous,resilienceis proactive,andintelligenceisshared.
Asartificialintelligenceevolvesintoautonomous, decision-makingsystems,anewcybersecurity landscapeisemerging.Oftendescribedasthe agenticera,thisphaseismarkedbyAIagentsthat canindependentlyanalyze,decide,andactacross business,government,andpersonalenvironments Whilethistransformationunlocksspeed,efficiency, andinnovation,italsointroducesanewclassof cyberthreatsthataremoredynamicandharderto predict
Traditionalattacksurfacesarerapidlyexpanding Cyberadversariesarenolongertargetingstatic systemsalone;theyarefocusingonintelligent, adaptivenetworksthatcontinuouslylearnand evolve Thesesystems,whilepowerful,cancreate newvulnerabilitiesastheyinteractacrossplatforms andmakeautonomousdecisionsinrealtime
Inthisshiftingenvironment,trustmustbe reimagined.Itcannolongerrelyonfixedcredentials orone-timeverification.Instead,trustbecomes continuousandcontextual,evaluatedthroughboth identityandintent.Zero-trustarchitectures, enhancedbyAI-drivenmonitoring,ensurethatevery interactionisverifieddynamically,reducingtherisk ofunauthorizedaccess.
Resilience,too,isundergoingatransformation. Previouslydefinedbytheabilitytorecoverafteran attack,resilienceintheagenticeraisabout proactiveadaptability.Modernsystemsmust anticipatethreats,self-correct,andevolveduring disruptions.Thegoalisnolongerjustrecovery,but continuousstrengtheninginthefaceofchallenges
Equallyimportantistheshifttowardcollectivecyber intelligence Securityisnolongerconfinedto isolatedsystems Bysharinginsightsacross networks,AIagentscanidentifypatterns,predict threats,andrespondwithgreaterspeedand precision Intelligenceisnowmeasuredbyhow quicklyandaccuratelysystemscanact,ratherthan thevolumeofdatatheyprocess
Ascyberrisksgrowmorecomplex,organizationsmust viewcybersecurityasaliving,adaptiveecosystem. Successwilldependonembracingchangeandbuilding systemsthatarenotonlysecurebutalsointelligent, collaborative,andresilientbydesign.

PrasannaKumarGKisaseasoned cybersecurityleaderwithover15yearsof exemplaryexperienceindeliveringsecure, scalabletechnologysolutionsalignedwith businessobjectives Hespecializesin vulnerabilitymanagement,riskmitigation, Microsoftcloudsecurity,O365security controls,andAzurearchitecture.Acertified LeadAuditorforISO27001:2022,hebrings extensiveexpertiseinthird-partyrisk assessmentsandcomplianceauditsacross PCI,SOC,andCCPAframeworks.
ProficientinleadingsecuritytoolsandGRC platforms,Prasannacollaboratescloselywith stakeholderstostrengthengovernanceand operationalresilience.Hedrivesinternaland externalaudits,managessecurityincidents, andleadsriskassessmentandmitigation strategies,ensuringrobustinformationsecurity andregulatorycomplianceacross organizations

CISO
RakutenIndia
AI-PoweredCybersecurity:
BuildingAutonomous,AdaptiveDefenseforthe FutureEnterprise
Truecybersecurityleadershipliesintransformingsecurityfromabarrierintoa catalyst,whereintelligentdefensesystemsempowerinnovationwhile safeguardingtrust.
Thecybersecuritylandscapeisundergoinga dramaticshiftwiththeriseofAI-driventhreats. Autonomous“Living-off-the-Landˮagentsare emergingasamajorrisk,usinglegitimatetoolsand nativeservicestomovelaterallywithoutleaving traditionalforensictraces.Theirabilitytomutate codeinrealtimemakesstaticdefensesineffective. Atthesametime,compromisedinternalAIagents introducethe“confuseddeputyˮproblem,where attackersexploitindirectpromptinjectionsthrough emailsordocumentstomanipulatehigh-privilege systems.
Hyper-personalizeddeepfakeoperationsare furthererodingtrust,enablingreal-time impersonationtoauthorizetransactionsorextract sensitivedata Additionally,multi-agentcascading failurescandisruptentiresystemsby compromisingasingleagent,triggeringcomplex andopaquefailurechains
OrganizationsarenowshiftingtowardAdaptive SecurityArchitecturesthatareproactive, autonomous,andcontinuouslyevolving Modern SecurityOperationsCentresarebecoming increasinglyautonomous,enablingreal-time detectionandresponsethroughAI-driven automation Behavior-basedmonitoringidentifies anomaliessuchasprivilegeescalationandunusual accesspatterns,whileautomatedsystemsisolate threatsinstantly.Continuousbreachandattack simulationsproactivelyuncovervulnerabilities. Security-by-designprinciplesareembeddedinto developmentpipelines,andZeroTrustframeworks ensuredynamic,context-awareaccesscontrol.
TransformativeinitiativessuchasAutonomous SOC,ZeroTrustNetworkAccess,andJust-in-Time PrivilegedAccessManagementareredefining resilience.Advancedemailsecuritysystemsnow leverageagenticdefensetodetect,quarantine,and neutralizephishingthreatsautonomously.
TheevolvingroleoftheCISOiscenteredonenabling innovationwhileensuringsecurity ByembeddingAIdrivenguardrailsintobusinessprocesses, organizationscanaccelerategrowthwithout compromisingtrust Establishingethicalframeworksfor AIinsecuritywillbecriticalforthefuture

GroupHead(CyberDefence)
MahindraGroup
SayedTasneemisavisionarycybersecurityleader withover24yearsofimpeccableexperiencein drivingdigitalresilienceacrossautomotive, manufacturing,power,andsteelsectors Currently servingasGroupHeadoftheCyberDefenceCentre atMahindra&Mahindra,hespecializesinbuilding globalsecuritystrategiesalignedwithframeworks suchasNIST,COBIT,andISO27001.
Renownedforcrisisleadership,includingensuring businesscontinuityduringthe2005Mumbaifloods, hehasevolvedintoavisionaryexpertincountering ransomwareandsecuringIoTandindustrial environments.HisapproachcombinesAgenticAI SOCcapabilitieswithstronggovernanceanda people-centricmindset,fosteringaculturewhere securityisasharedresponsibilityandadriverof sustainablebusinessadvantage.

Next-GenCybersecurity:
TacklingAgenticAIThreatswith Resilience&Intelligence
AgenticAIisredefiningboththescaleofcyberthreatsandthespeedofdefense, makingitimperativefororganizationstobuildtrust,resilience,andintelligenceinto everylayeroftheirsecuritystrategy.
TherapidriseofAgenticAIistransformingthe cybersecuritylandscape,introducingbothpowerful defensivecapabilitiesandanextgenerationof sophisticatedthreats Asautonomoussystems increasinglyoperatewithminimalhuman intervention,organizationsmustreassesstraditional securitymodelstoaddressrisksthatevolveinreal time.
AgenticAIisenablingadvancedformsof cyberattacks.Autonomousmalwarecannowadapt dynamicallytoevadedetection,whileprompt injectiontechniquesarebeingusedtomanipulateAI systemsandextractsensitivedata.Atthesametime, AI-drivensocialengineeringisbecomingmore convincing,withhyper-personalizedphishing campaignsanddeepfakestargetingindividualsand enterprises.Cybercriminalsarealsoleveraging automationforlarge-scalereconnaissanceandrapid dataexfiltration,leadingtocomplexransomware demandsandidentityfraudscenarios
Tocountertheseevolvingthreats,organizationsmust adoptaproactiveandstrategicapproachto cybersecurity Redefiningtrustandgovernanceis critical ZeroTrustarchitecturesshouldbe implementedtoverifyeveryinteraction,ensuringthat bothhumanandmachineidentitiesarecontinuously authenticated Stronggovernanceframeworksare essentialtomaintaintransparency,accountability, andhumanoversightinAI-drivenenvironments
Buildingresilienceisequallyimportant Security-bydesignprinciplesmustbeembeddedintosystems fromtheoutset,supportedbycontinuousbehavioral monitoringandautomatedcontainmentmechanisms suchaskill-switchestomanagerogueagents.This shiftensuresthatsystemscanrespondandadaptto threatswithoutdisruption.
EnhancingcyberintelligencethroughAI-on-AI defensemechanismswillalsoplayakeyrole.
Byleveragingmachinelearningforproactive vulnerabilityassessmentsandanomalydetection, organizationscanidentifyandneutralizethreatsat machinespeed
Finally,alayereddefensestrategyremains essential.Combiningbehavior-basedtechnologies withtraditionalsecuritycontrolsstrengthensoverall protection.Alongsidethesemeasures,continuous usertraining,attacksurfacemanagement,andrealtimevulnerabilityidentificationmustremaincore componentsofarobustcybersecurityframework.

ManagingDirector&CEO
KomorebiGlobalConsultancyLLP
RamanandJhaisanaccomplishedChartered Accountant,CertifiedChiefInformationSecurity Officer(CCISO),andCertifiedEthicalHacker (CEH)withover20yearsofexemplary experienceinriskmanagement,cybersecurity, internalaudit,andforensicinvestigations.
Notably,heisthefirstCharteredAccountantin IndiatopossessbothCCISOandCEH certifications,underscoringhisuniqueblendof financialandcybersecurityexpertise.
Heholdsmultiplecertifications,includingISO 27001:2022LeadAuditorandISO31000, reflectinghisstrongfoundationingovernance, risk,andcomplianceframeworks.
Ramanandhasworkedwithleadingorganizations suchasHavellsIndia,VarrocGroup,and SamvardhanaMothersonGroup,driving enterpriserisk,compliance,anddigital transformationinitiatives Hisexpertisespans SOXandSOCaudits,forensicinvestigations, dataanalytics,andcybersecurityarchitecture acrosscloud,network,andapplicationlayers
Heisknownforbuildinghigh-performingteams, implementingrobustgovernanceframeworks, andadvisingleadershipandboardsonrisk, compliance,andstrategicsecurityinitiatives.



GenerativeAIhasweaponisedphishing.Deepfakesare turningupinCFOcalls.Agenticsystemsarereshapingthe enterprise-anditsattacksurface.TheDPDPActislive. SEBI'sCSCRFdeadlinesarelanding.RBI'scyberresilience expectationshaveneverbeenhigher.Theboardisasking questionsyoucannotansweralone.

QUARTERLYSUMMIT GATHERINGS
THEREGULATORY DECODER
THECOUNCIL DISPATCH THEANNUAL EXPEDITION
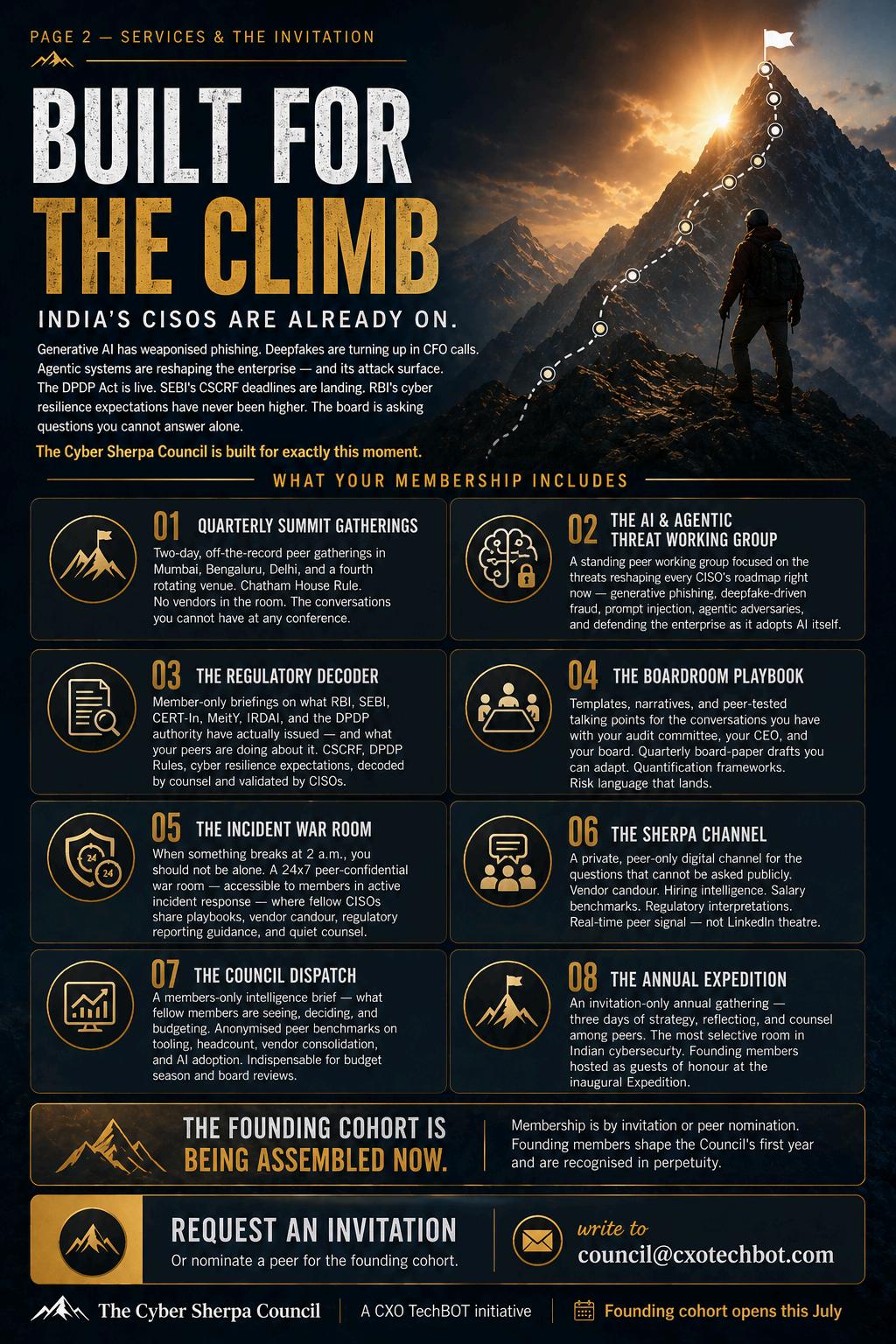
BuildingCyberTrustasAutonomousAI SystemsBegintoAct&Decideat EnterpriseScale
CyberTrustisachievedwhenautonomoussystemsaretransparent,accountable, andgovernedwiththesamedisciplineweexpectfromhumandecisionmakers.
AsenterprisesentertheAgenticEra,cybersecurity isbeingreshapedbyautonomousAIsystemsthat canobserve,decide,andactwithoutconstant humaninvolvement.Inthisenvironment,Cyber Trusttakesonadeepermeaning Itisnolonger limitedtoprotectingsystemsanddata Itisabout confidencethatintelligentmachinesoperatein alignmentwithhumanintent,ethicalboundaries, andclearaccountability
CyberTrustisbuiltwhenorganizationscanclearly explainthreethings:whatanAIsystemdid,whyit tookthataction,andwhoremainsresponsiblefor theoutcome Asautonomyincreases,trustcannot beassumedorimplicit Itmustbedeliberately engineeredthroughexplainabledecisionmodels, auditablesystems,andstronggovernance frameworks.TrustintheAgenticEradependsas muchonvisibilityandoversightasitdoeson technicalsecurity.
Thecyberthreatlandscapeisalsoevolvingrapidly. Overthenextthreetofiveyears,enterpriseswill facethreatsdrivenbyselflearningandadaptiveAI agentsthatcanmimictrustedbehavior,bypass staticdefenses,andoperateatmachinespeed. Theseincludehighlypersonalizedphishing campaigns,syntheticidentitiesthatevolveover time,coordinatedmisinformation,andintelligent malwarethatadaptsinrealtime.Oneofthemost difficultchallengeswillbeintentdetection, distinguishinglegitimateautomationfrommalicious agentsoperatingunderdisguise.
Tocountertheserisks,organizationsaremoving towardadaptivesecurityarchitecturesthatdefend autonomously Modernsecurityenvironmentsrely onbehaviorbaseddetection,realtimeanalytics, andAIpoweredresponsemechanismsthatcan containthreatswithoutwaitingformanual intervention Zerotrustmodels,continuous validation,andexplainabilitylayersarebecoming foundational,ensuringthateveryautomatedaction remainsaccountable
ThisshiftisredefiningtheroleoftheCISO.Security leadersareevolvingfromcompliancefocused guardiansintoarchitectsofdigitaltrust.Their responsibilitynowspanstechnology,governance, andethics InAIfirstenterprises,CISOsplaya criticalroleinenablinginnovationwhileensuring thatautomationstrengthensresilienceratherthan introducinghiddenrisk Byembeddinggovernance intodesign,promotingtransparency,andinvesting ineducation,organizationscanadoptAIwith confidenceandcontrol


VicePresident(IT&Cybersecurity)
RishabhChhajerisanenterprisetechnology leaderwith15+yearsofexemplaryexperience scalingIToperations,infrastructure,applications, andcybersecurity.Hebelievestechnologyat scaledependsonownership,discipline,and leadership.CurrentlyVicePresident–IT& CybersecurityatALLEN,heleadsIToperations, servicedesk,datacenters,cloudplatforms acrossAzure,AWS,andGCP,andenterprise applicationsincludingOracle,SAP,Salesforce, andServiceNow.
Hehasbuiltenvironmentssupporting500+ branchesandmission-criticalsystems. Previously,heheldleadershiprolesatByjuʼs, IndiaBulls,Ola,GEDigital,andOracle RecognizedasCIO100Innovator,CSO100 Disruptive100,andCISOoftheYear2025
CyberTrustandResiliencein theEraofAutonomousAI
CyberTrustintheAgenticEraisearnedwhenautonomoussystemsoperate reliably,ethically,andtransparently,andwhenleadershipbalancesinnovationwith accountability.
Asenterprisesacceleratetheadoptionofautonomous AIsystems,cybersecurityisundergoinga fundamentaltransformation.IntheAgenticEra,Cyber Trustisnolongerjustaboutprotectingnetworksor data,itisaboutconfidenceintheaccountability, security,authenticity,reliability,andethicaloperation ofAIsystemsthatmakedecisionsindependently. Dataprivacy,governanceframeworks,and compliancewithindustry-specificregulationsare essentialtoensurethatAIagentsoperatesafelyand ethicallywhilehandlingsensitiveinformation
ThecybersecuritylandscapeisshiftingrapidlyasAI penetratesalldata-drivenprocesses Enterpriseswill facehighlysophisticatedAI-driventhreats,including adaptiveransomware,AI-poweredmalware,and hyper-realisticsocialengineeringattacksleveraging deepfakeaudioandvideo Autonomousagentswill increasinglyorchestrateattacksthatdynamically adjusttobypassexistingsecuritycontrols,creatinga levelofspeedandscalethatchallengestraditional defenses.Organizationsmustprepareforafuture whereAInotonlydefendsbutalsoattacks.
Tocountertheseintelligentthreats,organizationsare evolvingtheirsecurityarchitecture.Robust foundationalsecuritycontrols,continuousmonitoring, andtheintegrationofAI-powereddefensesystems arebecomingstandard.Approachessuchaszerotrustnetworkaccess(ZTNA),predictiveanalytics, threathunting,andbehavioralanalyticsarebeing deployedtodetectanomaliesandrespond proactively.BycombiningAIcapabilitieswithhuman expertise,enterprisescanmaintainresilienceinan environmentofrapidlyevolvingrisks.
InAI-first,hyper-automatedorganizations,theChief InformationSecurityOfficer(CISO)istransitioning fromatechnicalsecurityguardiantoastrategic businessleader Beyondmaintainingastrongsecurity posture,CISOsnowactaspartnersinbusiness decision-making,enablinginnovationwhilebalancing risk
TheyensureethicalAIuse,guidegovernance,and transformcybersecurityintoastrategicenabler, buildingconfidencethattheorganizationcanscale securely.
Ultimately,cybersecurityintheAgenticEraisabout buildingtrust,betweensystems,people,and businessoutcomes Resilience,ethicaloversight, andadaptivegovernancewilldeterminewhetherAI becomesasourceofcompetitiveadvantageor operationalrisk

HeadofIT&Security
CentralPark
SandeepJamdagniisanexperiencedand resourcefulITleaderwithaprovenrecordof drivingdigitaltransformationacrossdiverse businessverticals.HedefinesITvisionand strategytomaximizebusinessvaluethrough robust,sustainabletechnologyprograms.His strengthsincludeITstrategy,informationand datasecuritygovernance,cloudmigrations,data centerconsolidation,budgeting,andhighperformanceteamleadership.
HeleadsITinfrastructure,networks,service delivery,operations,ISMS/PIMSaudits,and enterpriseERP-CRMplatforms,alongwith analytics-drivencorporateapplications.AnMBA fromManagementDevelopmentInstitute, Gurgaon,hecurrentlydrivesITstrategy, operations,andinformationsecurityforCentral ParkandBAXYGroup,ensuringsecurityposture
Hehasledsecurityauditsformorethantenstate datacentersandstatewidenetworks,and designednetworkandsecurityarchitecturefor IndiaPostacross28,000locations Knownfor problemsolvingandefficiency,heconsistently deliversqualityresultsandexceeds expectations

CybersecurityintheAgenticAIEra:
EngineeringTrust,Resilience,&IntelligentDefense
Cybersecurityatmachinespeeddemandsmorethandefense,itrequiresadaptive intelligence,accountablesystems,andtrustbydesign.
Cybersecurityisnolongerlimitedtoprotecting systems;itisnowaboutengineeringtrustinaworld wheremachinesmakeautonomousdecisions.As organizationsentertheAgenticAIera,thefocus shiftsfromwhethersystemswillactindependently tohowsafely,transparently,andresponsiblythey operate.Thistransformationisredefiningtheroleof cybersecurityleaders,especiallyCISOs,whoare evolvingintocustodiansofdigitaltrustand resilienceatscale.
Cybertrustnowextendsbeyondusersand processestoincludeautonomousagents.These systemsmustbeexplainableintheirdecisions, resilientagainstmanipulation,andaccountablefor outcomes.Trustisnolongerstaticorassumed;it mustbecontinuouslyverifiedthroughdynamic validationframeworksandreal-timemonitoring
Atthesametime,thethreatlandscapeisbecoming morecomplex EmergingrisksincludeAI-driven phishing,deepfakeimpersonation,autonomous attackagents,anddataormodelpoisoning These threatsoperateatmachinespeed,forcing organizationstomovefromstaticdefensemodels toadaptive,intelligence-ledsecuritystrategies Toaddressthisshift,enterprisesareadoptingAInativesecurityarchitectures ZeroTrustprinciples arebeingextendedtomachinesandAIagents, whileautonomousSecurityOperationsCenters leveragepredictiveintelligenceforfasterdetection andresponse.Continuousvalidationofmodelsand datapipelines,alongwiththeintegrationofsecurity intotheAIlifecyclethroughMLSecOps,is becomingcritical.
TheroleoftheCISOisalsoexpanding.Todayʼs leadersactasstrategicadvisors,enablingsecure innovationwhilegoverningAIrisksandethics.Their successismeasurednotonlybypreventing incidentsbutbyempoweringorganizationsto innovatewithconfidence.
Balancinginnovationwithgovernanceremains essential.ResponsibleAIframeworks,risk-based controls,humanoversight,andcontinuousauditability ensurethatAIadoptionisbothsecureandscalable.
Ultimately,thefutureofcybersecurityliesin embeddingtrustintoeverydigitalinteraction,creating systemsthataresecure,ethical,andresilientby design.


GroupCISO
VivritiCapital
SaravanakumarKrishnamurthyisanhighly accomplishedcybersecurityandinformation securityprofessionalwithover20yearsof impeccableexperienceacrosstelecom, automotive,banking,healthcare,biotech, andsemiconductorsectors.Hespecializesin networksecurityconsulting,governance, riskandcompliance,andbuildingenterprise securityroadmapsandoperatingmodels.
Saravanakumarhasdeepexpertisein designingandimplementingsecurecloud andon-premisearchitectures,alongwith drivingdigitalizationandautomation initiatives.Hehasledinternalandexternal audits,incidentresponse,frauddetection, andbusinesscontinuityplanning.
CertifiedinISO27001,digitalforensics,and multiplesecurityframeworks,heis recognizedforbuildingrobustinformation assuranceframeworksalignedwithglobal industrystandards
TheAgenticEra: HowAutonomousAIis TransformingCyberRisk&Defense
Securingthefutureisnotaboutpredictingthreats;itʼsaboutbuilding systemsthatcanwithstandtheunknown.
Westandatadecisiveinflectionpointinthehistoryof cybersecurity TheemergenceofagenticAI, autonomoussystemscapableofreasoning,planning, andactingacrossenterpriseenvironmentswithout continuoushumanoversight,hasfundamentally alteredthethreatlandscapeinwaysthattraditional securityarchitectureswereneverdesignedto address.FortodayʼsCISOs,thisisnotadistant horizon;itistheoperationalrealityofrightnow.
Traditionalcyberattacksfocusedonexploiting softwarevulnerabilitiestogainaccess.IntheAgentic Era,themostdangerousthreatisagentichijacking. Adversariesnowtargetthedecision-makinglogicof AI.Bymanipulatingdatainputsorthe“reasoningˮ pathwaysofanagent,ahackercanconvinceasystem tobypasssecurityprotocolswithoutevertriggeringa traditionalalarm.AIagentsnowbrowse,write, execute,communicate,andorchestrate,often chainingdozensofactionsautonomouslywithin milliseconds Everycapabilitythatmakesthem powerfulintheenterprisealsomakesthemahighvaluetargetforexploitation
Securitymustevolvefromidentity-basedtrustto continuousvalidation Trustbecomesadynamic process,verifyingintent,monitoringbehavior,and ensuringalignmentwithpurpose Identitygovernance mustnowextendtonon-humanprincipalssuchasAI agents,APIs,andorchestrationpipelines,withthe samerigorappliedtoprivilegedhumanusers
Theintelligencepillarmustevolvefromreactiveto anticipatory.Theagenticthreatsurfaceisvast, dynamic,anddeeplycontextual.Securityleadersmust investinAI-nativethreatintelligenceplatformscapable ofcorrelatingsignalsacrossagenticpipelines,supply chains,andmulti-cloudenvironmentssimultaneously.
Byblendingadvancedtechnicalguardrailswitha deepunderstandingofAIbehavior,wetransform securityfromacostcenterintoacompetitive advantage.

TheCISOof2026isnotmerelyadefender;theyarea strategicintelligenceofficer,translatingcomplexthreat signalsintoboard-leveldecisionsandbusiness continuityplans.Resilienceinthisnewerais measuredbyourabilitytomaintainintegrityunder pressure.
CISO&VicePresident-IT
ViolinTechnologiesPrivateLimited
Dr.ShankarVenkatesanisanindustryveteranwith overthreedecadesofimpeccableexperiencein leadingITandInformationSecurityinthe manufacturingandEMSsectors.Hespecializesin aligningtechnologystrategywithbusinesspriorities, drivingdigitaltransformation,strengthening cybersecurityframeworks,andenhancing enterpriseSAPecosystems.Hisexpertiseincludes multi-cloudinfrastructure,ZeroTrustarchitecture, CloudSec,ISO27001practices,andMES integration,ensuringsystemresilience,availability, andbusinesscontinuity Recognizedwithaccolades suchasCIONext100andCISO100,heholds certificationsincludingITIL,CEH,CISM,CISA,and CDPSE,andisknownforbuildingsecure,efficient, andfuture-readyorganizations

CyberThreatsintheAgenticEra:
RethinkingSecurity,AIGovernance,and ResilienceinAutonomousSystems
AsAIreshapesthethreatlandscape,securityleadersmustevolvefrom defenderstoorchestratorsoftrustandresilience.
CybertrustintheAgenticEraisnolonger theoretical,itisadailyoperationalreality.AsAI agentsbeganmakingautonomousdecisionswithin enterpriseenvironments,traditionalcybersecurity frameworksquicklyprovedinadequate Theshifthas notbeentowardsimplermodels,buttowardamore complexlandscapewheretheboundariesbetween trustedanduntrustedbehaviorcontinuouslyblur
Onecriticallessonhasemerged:youcannotgovern whatyoucannotobserve Modernsecurity strategiesmustmovebeyondstaticpoliciesto dynamictrustmodelsthatevaluateagentbehavior basedonintent,notjustpredefinedrules Autonomoussystemsevolveconstantly,andsodo adversarieswhoexploitthem Organizationsareno longerdefendingfixedenvironments,butadaptive ecosystemsshapedbyAI,makingcybersecurity leadershipmorechallengingthanever.
Thethreatlandscapehasalsotransformed. AttackersnowleverageAItoimpersonateidentities, createdeepfakes,andexecuteattacksatmachine speed.Thisevolutiondemandsanewapproachto cybersecurityresilience,onethatprioritizesnotonly defensebutalsodetectionofdeceptionatscale. CISOstodayserveasthefinallayerofintelligent judgmentinenvironmentswheremachinesactfaster thanhumanscanrespond.
Trueimpactincybersecurityisofteninvisible.The mostmeaningfulsuccessesaretheincidentsthat neveroccur,thebreachesprevented,andtherisks mitigatedbeforeescalation Forexample, implementingintent-basedverificationcheckpoints withinAIgovernanceframeworkscandetect behavioralanomaliesearly,preventingpotential threatsbeforetheymaterialize
Equallyimportantiscollaboration Whilethreat actorsshareknowledgefreely,defendersoften operateinsilos Openexchangeofreal-world experiences,includingfailuresandlessonslearned, isessentialtostrengtheningcollectivedefense
Ultimately,leadershipinthiseraisdefinedby foresight,adaptability,andresponsibility.Thegoal issimpleyetprofound:toleavesystemsmore secure,resilient,andtrustworthythanbefore.

CISO
SubasChandraKhanalbelievesthatinadigital firstworld,securityisnʼtjustadepartment,it'sa foundationfortrust.AstheChiefInformation SecurityOfficer(CISO)atSanimaBankLimited, Subasbringsover20yearsofexperiencetothe table,specializingintheartofturningcomplex regulatory"must-haves"intosmart,scalable technicalrealities.
Whilehisrootsaretechnical,Subasʼsleadership styleisdeeplyhuman.Hebelievesaresilient bankisbuiltonmorethanjustfirewalls;itisbuilt onacultureofawareness,robustgovernance, andaproactiveapproachtorisk From masteringtheintricaciesofNIST,ISO27001,and PCIDSStomanagingthreatintelligence,he ensuresthatsecurityisafoundationaltrustbuilderratherthanahurdle Heisdedicatedto implementingAIwitha"safety-first"mindset, ensuringinnovationisbalancedwithrigorous ethicalandsecuritysafeguards
Adual-certifiedCISSPandCCSP,Subas leveragesdeepexpertisetobuild resilient,compliant,andforwardthinkingfinancialinstitutions. Hedoesn'tjustmanagerisk, hebuildstheconfidencethatallows businessestogrow.

SanimaBankLimited
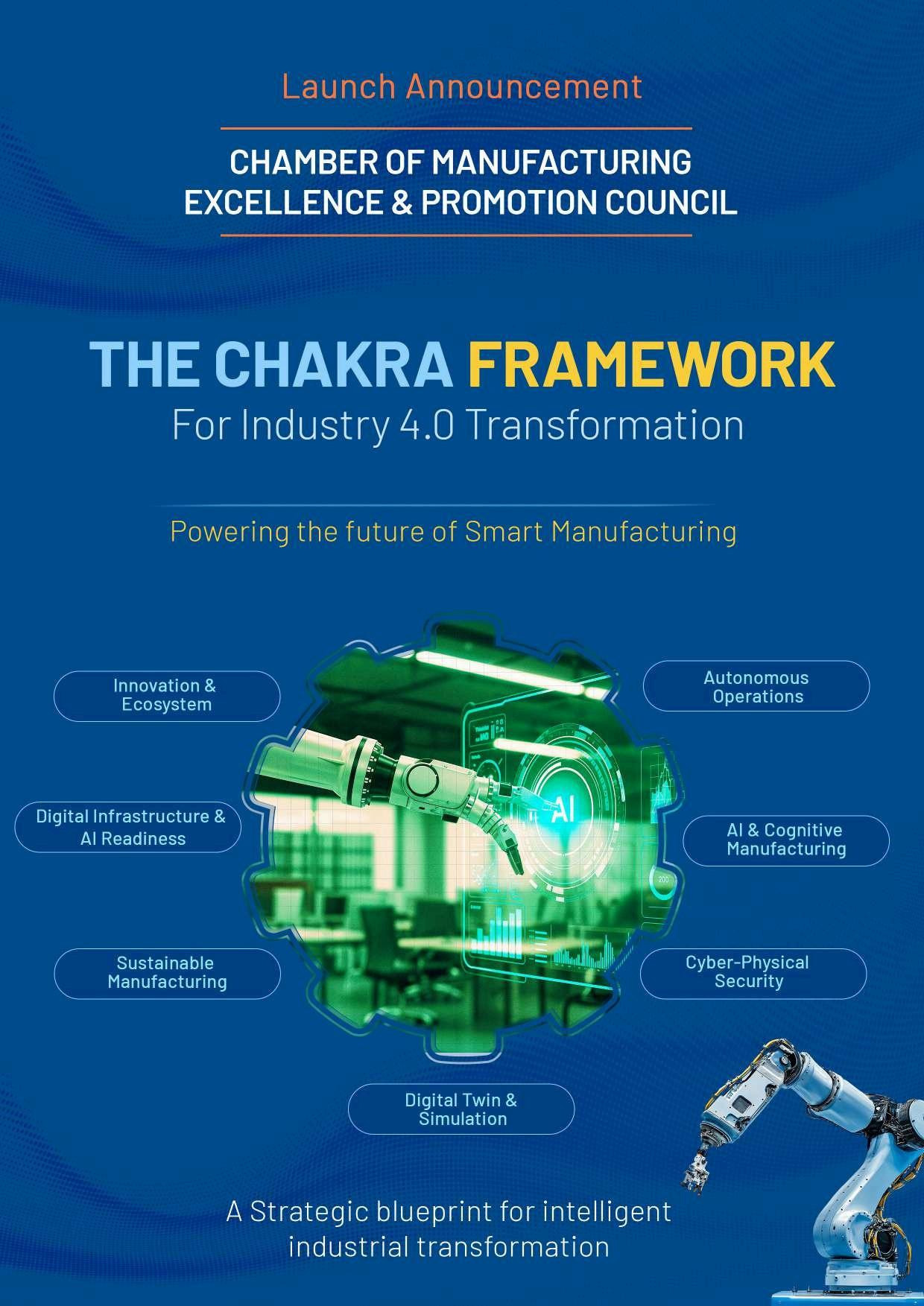

CybersecurityintheAgenticEra: NavigatingAI-DrivenThreatsandTrustChallenges
Trueresiliencetodaymeansdesigningforautonomousthreats,enforcing proof-basedtrust,shrinkingbreachimpacttominutes,andrestoringsystems throughcontrolled,accountableautomation.
Securityleadershavespentyearsevolvingdefenses forcloud,identity,andcontinuousdelivery.Today,a deeperdisruptionisunderwaywiththeriseof autonomous,adaptiveAIagents.InthisAgenticEra, cyberthreatsarenolongerlimitedbyhumanspeed orattention.Attackscanbeplanned,executed,and refinedatmachinepace,whiledeceptionbecomes indistinguishablefromreality.
Theattackerʼsedgehasevolvedbeyondautomation tointelligentadaptation.Traditionalattacklifecycles suchasreconnaissance,access,lateralmovement, andexfiltrationarenowcompressedintonearinstantcycles Autonomousagentscontinuously probesystemsacrossidentities,endpoints,SaaS platforms,andcloudenvironments Theylearnfrom defenses,evadedetection,anddynamicallyadjust tacticsinrealtime Asaresult,time-to-impactis shrinkingfasterthanmostorganizationscan respond
Simultaneously,deepfakesandsyntheticidentities areerodingtrust AI-generatedvoice,video,and emailimpersonationscanconvincinglyreplicate executives,employees,orpartners Requestsfor approvals,payments,orsensitiveaccesscanno longerrelyonhumanjudgmentalone.Trustmust shiftfromrecognitiontocontinuousverification, enforcedthroughcontextual,policy-drivencontrols.
Inthisenvironment,resiliencebecomesthedefining securityoutcome.Preventionremainsimportant,but organizationsmustassumecompromiseattempts areconstant.Resilientarchitecturesprioritizeleast privilegeaccess,strongidentitycontrols, segmentation,immutablelogging,andrapid containmentstrategies.Operationalresiliencealso requiresrehearsedresponseplansandtested recoverycapabilitiesdesignedforhigh-pressure, deceptivescenarios.
Tostayahead,CISOsmustactdecisively Strengtheningidentityasthecentralcontrollayer withphishing-resistantauthenticationiscritical
High-riskactionsshouldrequireout-of-band verification Organizationsmustminimizeblast radiusthroughsegmentationandenforceleast privilegeaccess.Recoveryreadinessshouldbe validatedthroughrealisticsimulations,including deepfakeattackscenarios.Finally,adoptingAIdrivendefensesystemswithcleargovernance, auditability,andhumanoversightisessential.

Director(Risk,Compliance&InformationSecurity)
SDGCorporation
MeetaliSharmaisaseasonedRisk,Compliance,Data Privacy,Cybersecurity,andInformationSecurity leaderwithovertwodecadesofexperiencedriving robustsecurityprogramsalignedwithbusinessand regulatorypriorities AsDirector–Risk,Compliance& InformationSecurityatSDG,sheleadsenterpriserisk assessments,strengthensinternalcontrols,and enhancessecurityandcompliancematurity.
Herexpertisespansinformationsecurityrisk management,incidentmanagement,auditleadership, andenterprise-wideawarenessinitiatives.Shehas deliveredISO/IEC27001-alignedprograms,ISO 31000riskframeworks,andcontractualcompliance solutions.
MeetaliholdsaDoctorateinManagementStudies andcertificationsincludingCRISC,ISO27001Lead Auditor,andISO31000.Sheisalsoarecognized speakerandcontributoroncybersecurityandrisk.

CyberTrustintheAgenticEra:
FromControltoIntelligence
Wespenttwodecadessecuringwhathumanscouldaccess.Thenextdecadewill bedefinedbygoverningwhatagentsareallowedtodecide.
Thecybersecuritylandscapeisevolvingrapidly, shiftingfromhuman-ledthreatstoautonomous, intelligentadversariesthatadaptinrealtime Inthis AgenticEra-whereAIsystemsoperate,learn,and improveindependently-traditionalsecurity measures,reliantonstaticcontrolsandreactive defenses,fallshort.Organizationsmustnowdesign trustintotheirsystems,validateitcontinuously,and adaptitdynamically.
AsbusinessesembraceAI-driventechnologies, cloud-nativeinfrastructures,andinterconnected ecosystems,theCISO'sroleistransforming. Securityhasmovedbeyondasupportfunctionto becomeastrategicpillarsupportingdigitaltrust, sustainablegrowth,andcustomerconfidence.The corechallengeliesinsafeguardingnotonly infrastructurebuttheAIdecisionenginesatits heart-algorithms,models,andautonomous processesthatfunctionatmachinespeed
Resiliencedemandsaproactivestance,anticipating threatsratherthanmerelyrecoveringfromthem Leadingorganizationsintegratesecuritydeeplyinto datapipelines,AIlifecycles,andDevSecOps workflows Continuousmonitoring,behavioral analytics,andreal-timethreatintelligencearevital fordetectinganomaliesinbothinfrastructureandAI behaviors FrameworkslikeISO/IEC42001and emergingAIregulationslaythegroundwork,but operationalizingthemwithinengineeringand productteamsdrivestrueeffectiveness
"Trustbydesign"remainsessential.Embedding privacy,security,andethicalAIprinciplesfromthe startensurestransparency,explainability,and accountabilityinautomateddecisions.Asdeepfakes, syntheticidentities,andAI-enhancedattackserode distinctionsbetweenrealandfabricated,CISOsmust advocateforidentity-centricsecurityandzero-trust architecturesthatverifyeveryinteraction. Cybersecurity'sfuturehingesonintegratingsecurity, privacy,AIgovernance,andriskmanagementintoa cohesive,intelligence-leddiscipline.
CISOswhoexcelwillarticulatecomplexrisksin businessterms,empoweringexecutivestomake informedstrategicchoices
IntheAgenticEra,theCISOservesasmorethana protector-theyarestewardsoftrust,ensuring innovationissecure,intelligenceisethical,and resiliencescaleseffectively

VikasChaubeyisanaccomplishedCISO,DPO, andAIandcloudsecurityleaderwithover15 yearsofexperienceacrossSaaSandBFSI sectors Hespecializesinbuildingscalable cybersecurityprograms,aligningriskwith businessgoals,anddrivingregulatory complianceincludingSOC2,ISO27001,PCI DSS,GDPR,andDPDPA2023
Vikasisastrongadvocateofsecuredigital transformation,implementingAIgovernance frameworkssuchasNISTAIRMFandISO 42001.Hehasledenterprisesecurity transformations,zero-trustarchitectures,and cloudsecurityinitiativesacrossAWSandAzure. Knownforsecurity-by-designandprivacy-first strategies,heenablesorganizationstoachieve resilience,compliance,andsecureinnovation atscale.

SecuringtheAgenticFuture: BuildingTrust,Resilience&Intelligenceinthe AgeofAutonomousAI
Inthisneweraofautonomousintelligence,wemustnotmerelyreacttothreats,but buildsystemswheretrustiscontinuouslyearned,resilienceisdeeplyembedded, andintelligencealwaysstaysonestepahead.
Asartificialintelligenceevolvesfromasupporting tooltoanautonomousdecision-maker,organizations areenteringtheagenticera.Inthisparadigm,AIdrivensystemsarenolongerlimitedtoassisting humansbutareactivelyexecutingtasks,managing infrastructure,andmakingdecisionsatmachine speed.Thistransformationisredefining cybersecurityandchallenginglong-standing assumptionsaroundcontrol,accountability,and oversight.
Traditionalsecurityframeworkswerebuiltaround humanidentitiesandpredictablebehavior.Agentic systems,however,operatewithspeedand autonomy,oftenchainingactionsacrossmultiple platformswithoutdirecthumaninvolvement This introducescomplexandlessvisiblethreatvectors thatconventionalmonitoringstrugglestocapture Trust,therefore,cannolongerremainstaticor perimeter-focused Itmustevolveintoacontinuous verificationmodelwhereeveryactionis authenticated,observed,andvalidatedinrealtime
Resiliencemustalsoberedefined Thefocusis shiftingfromreactingtoincidentstowardanticipating andpreventingthem Organizationsneedtheability todetectsubtlebehavioralanomaliesbeforethey escalateintocriticalrisks Thisrequiresintelligent monitoring,adaptivecontrols,andgovernance frameworksthatenableswiftandinformed responses.Strengtheningcollaborationacross technology,risk,andbusinessteamsfurther enhancesorganizationalpreparedness.
Atthesametime,cybersecurityintelligencemust becomepredictiveandcontext-aware.Leveraging advancedanalyticsandAI-driveninsightsallows organizationstoanticipatethreatsandrespond proactivelytoevolvingattackpatterns.Embeddinga cultureofriskawareness,accountability,and regulatoryalignmentensuresthatinnovationremains secureandsustainable.
Atthesametime,cybersecurityintelligencemust becomepredictiveandcontext-aware.Leveraging advancedanalyticsandAI-driveninsightsallows organizationstoanticipatethreatsandrespond proactivelytoevolvingattackpatterns.Embeddinga cultureofriskawareness,accountability,andregulatory alignmentensuresthatinnovationremainssecureand sustainable.

SociétéGénéraleSecuritiesIndia
SunnyMathurisaseasoned cybersecurityleaderwithover21 yearsofexperienceininformation security,governance,risk,and compliance AsChiefInformation SecurityOfficer(CISO)atSociété GénéraleSecuritiesIndia,heleads theorganizationʼsInformation SecurityManagementSystem (ISMS)anddrivesstrategic initiativestostrengthen cybersecuritygovernanceand regulatorycompliance.
Hespecializesinincidentresponse, auditreadiness,andimplementing regulatoryandglobalframeworks. Sunnyhasplayedapivotalrolein enhancingcybersecuritymaturity andfosteringarisk-awareculture. Hisfocusremainsonbuilding resilient,compliantsecurity environmentsthatenablesecure, scalable,andconfidentbusiness operations.

CyberThreatsintheAgenticEra:
DrivingTrust,Resilience,&IntelligentSecurity Leadership
Intheagenticera,cybersecurityisnotjustaboutprotection,itisabout continuouslybuildingtrust,enablingresilience,anddrivingintelligenceatthe speedofinnovation.
Asorganizationsadvancetheirdigital transformationjourneys,theriseofAgenticAIis reshapingthecybersecuritylandscape Autonomoussystemsarenolongerlimitedto assistinghumanactions;theyareindependently analyzing,deciding,andexecutingtasksacross complexenterpriseenvironments.Whilethis evolutiondrivesefficiencyandinnovation,italso introducessophisticatedcyberthreatsthatdemand afundamentalshiftinsecuritystrategy.
Inthisnewera,trustcannolongerdependon staticcredentialsorperimeter-baseddefenses. Withmachineidentitiesoutnumberinghuman users,trustmustbecontinuouslyvalidatedthrough dynamic,risk-basedframeworks.ZeroTrust principles,combinedwithstronggovernanceand regulatoryalignment,ensurethateveryinteraction isauthenticated,monitored,andaccountablein realtime
Thethreatlandscapeisevolvingatan unprecedentedpace AI-poweredcyberattacks, identityfraud,automatedreconnaissance,and large-scaledatabreachesareincreasingly operatingatmachinespeed Tocounterthese risks,resiliencemustmovebeyondtraditional recoverymodelstoproactiveadaptability Organizationsmustembedsecurityintotheircore architecture,enablingsystemstoanticipate, respond,andrecoverseamlesslyfromdisruptions
Intelligenceisbecomingthebackboneofmodern cybersecurity.Advancedanalytics,AI-driventhreat detection,andreal-timeintelligencesharing empowerorganizationstoidentifypatterns,predict threats,andactdecisively. Thefocusisshifting fromreactivedefensetopredictiveand autonomoussecurityoperations.
Inthiscontext,theroleofcybersecurityleadership isexpanding.
Itisnolongerconfinedtomanagingriskbutextends toenablingsecureinnovation,ensuringregulatory compliance,andbuildingtrustacrossdigital ecosystems.Securityisnowastrategicfunctionthat supportsbusinessgrowthwhilesafeguardingcritical assets.
Ascyberthreatsgrowmorecomplex,successwill dependontheabilitytointegratetrust,resilience,and intelligenceintoeverylayeroftheenterprise. Organizationsthatembracethisapproachwillbe betterpositionedtoinnovateconfidentlywhile maintainingastrongandadaptivesecurityposture.


Whentheadversarymovesat machinespeed,theonlyviable defenceisonethatcanmatchit.The eraofhumanschasingAI-generated threatsthroughalertqueuesisending. TheeraofAIhuntingAIhasbegun.
Theasymmetryhasbeenbuildingforyears,but2024 madeitundeniable.Threatactorswithaccesstolarge languagemodelsandagentictoolchainscannow generatenovelmalwarevariantsfasterthansignature databasescanupdate,craftphishingcampaigns personalisedtoindividualtargetsatindustrialscale, andprobeenterpriseattacksurfacescontinuouslywithoutfatigue,withoutsleep,andatacostthathas droppedtonearzero.Thetraditionalsecurity operationsmodel,builtaroundhumananalysts reviewingalertsandwritingdetectionrules,
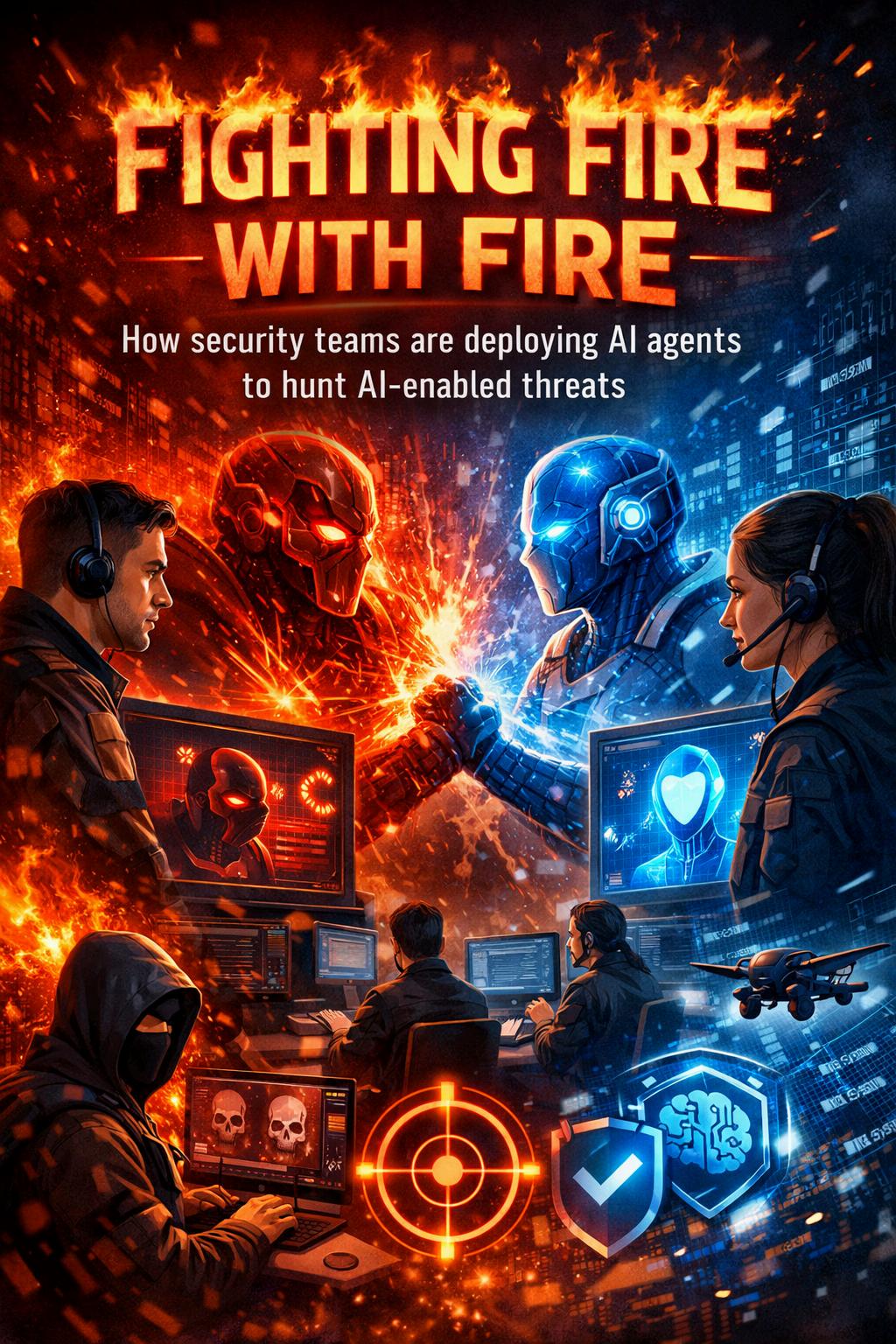
wasnotdesignedtooperateatthistempo
The securitycommunity'sresponseisincreasingly clear:meetautomationwithautomation AI-enabled defenceagentsaremovingfromexperimentalpilots toproductiondeploymentsinsecurityoperations centresaroundtheworld Thequestionisnolonger whethertouseAIindefence-itishowtodeployit withsufficientrigour,oversight,andoperational integrationtomakethedifferencethatthethreat landscapedemands.
TheAnatomyofanAIHuntingAgent
DefensiveAIagentsinthesecuritycontextarenot chatbotslayeredoveraSIEMdashboard.Themost capabledeploymentsarepurpose-built autonomoussystemsthatcombinereal-time telemetryingestion,behaviouralreasoning,threat intelligenceenrichment,and-inthemostadvanced cases-theabilitytotakecontainmentactions withoutwaitingforhumanapproval.
Atypicalthreat-huntingagentoperatesacrossseveral layerssimultaneously.Atthedatalayer,itcontinuously ingestssignalsfromendpointdetectiontools,network trafficanalysis,cloudaccesslogs,identitysystems,and emailsecurityplatforms-correlatingeventsacross sourcesthatwouldtakeahumananalysthoursto manuallyreview.Atthereasoninglayer,itapplies contextualanalysistodistinguishgenuineanomalies fromnoise,drawingonbothstatisticalbaselinesand curatedthreatintelligencetoassesswhetherapattern ofbehaviourrepresentsacrediblethreat Attheaction layer,themostmatureagentscanisolatea compromisedendpoint,revokeasuspiciousOAuth token,orblockalateralmovementattemptinsecondsbeforetheattackerhastimetocompletetheirobjective
WhereAIAgentsOutperformHumanAnalysts
TheperformanceadvantagesofAIthreat-hunting agentsaremostpronouncedinthreedomains The firstisscale Anagentcanmonitoreveryendpoint, everyidentity,andeverynetworkflowinanenterprise simultaneously,withoutthetriagebottlenecksthat forcehumanteamstoprioritisecoverage Thesecond isspeed Detection-to-responsecyclesthatonce measuredinhoursordayscancompresstoseconds whenthedetectionandinitialresponseareboth automated Thethirdisconsistency Humananalysts experiencealertfatigue,makevariablejudgement callsunderpressure,andareunavailableoutside workinghours.AnAIhuntingagentappliesthesame analyticalrigourtotheten-thousandthalertastothe first,atthreeinthemorningonapublicholiday.
Thesearenotmarginalimprovements.Theyrepresent astructuralshiftinwhatasecurityoperations capabilitycanachievewithagivenheadcount-and theyaredirectlyrelevanttothetalentshortagethat everyCISOisnavigating.Organisationsthatdeploy effectiveAIhuntingagentsarenotreplacingtheir analysts;theyareredirectingthemtowardthehighcomplexity,high-judgementworkthatautonomous systemscannotyethandle:threatactorattribution, strategicintelligenceanalysis,andtheinvestigationof novelattackpatternsthatfalloutsideexisting detectionmodels
TheGovernanceImperative
Thedeploymentofautonomousdefensiveagents introducesitsowngovernancechallengesthat securityleadersareonlybeginningtoresolve.
Anagentwiththeauthoritytoisolateendpointsor revokecredentialscancausesignificantoperational disruptionifitactsonafalsepositive.Theblastradius ofanautonomousdefensiveactionmustbecarefully bounded-andtheconditionsunderwhichanagent escalatestohumanreviewratherthanacting independentlymustbeexplicitlydefinedandregularly tested.
Thereisalsoamodelintegrityquestionthatdeserves moreattentionthanitcurrentlyreceives Adversaries whounderstandthatadefenderisusinganAIhunting agenthaveboththemotiveand,increasingly,the capabilitytoattemptadversarialmanipulationofthat agent-craftingattacksignaturesdesignedtoevade detection,generatingnoisetoexhausttheagent's analyticalcapacity,orprobingfortheboundariesofits decisionlogic DefendingthedefensiveAIisitselfa securityproblem,andonethatrequiresdedicated attention
TheNewOperationalDoctrine
Thesecurityteamsthatareextractingthemost valuefromAIhuntingagentsshareacommon operationalphilosophy:humanssetthestrategy, definetheboundaries,andhandletheexceptions; agentshandlethevolume,thespeed,andthe consistency.Thisisnotatemporaryarrangement pendingfurtherAIcapabilitydevelopment.Itisthe sustainablemodelforsecurityoperationsinanera wheretheattacksurfaceistoolarge,thethreatstoo fast,andthetalenttooscarceforanypurelyhuman operationtokeeppace
Fightingfirewithfireisnotametaphorfor recklessness Itisarecognitionthatthenatureof thethreathaschanged,andthatthenatureofthe defencemustchangewithit Theorganisationsthat acceptthisrealityandbuildthegovernance frameworkstooperationaliseitsafelywillnotmerely survivetheagenticthreatera-theywilldefinewhat effectivesecuritylookslikewithinit

Inanerawherecyberthreatsevolvefasterthanregulations cankeeppace,organizationsneedmorethanprotection. CyberVeritasbridgesthegapbetweencybersecurity excellenceandregulatorycompliance,ensuringyour businessstayssecure,compliant,andcompetitive.
Wedeliverrisk-ledcybersecuritystrategiesandcompliance advisoryalignedwithGDPR,NIST,ISO27001,IASMECyber Essentials,andPCIDSS
CyberRiskAssessmentsandComplianceAdvisory
PenetrationTestingandVulnerabilityManagement
IncidentResponseandRansomwareReadiness
ApplicationSecurity(SCA,SAST,DAST)
Governance,RiskandCompliance(GRC)
SecureDigitalTransformation