Issue 14, 2022 THE MAGAZINE FOR AUSTRALIAN INFORMATION SECURITY PROFESSIONALS | www. australiancybersecuritymagazine.com.au @AustCyberSecMag Cybersecurity professionals burning out Why industry consultation is vital in Cyber Security We’re still terrible at password management The art of data protection in Formula 1 MysecTV weekly episode highlights PLUS Australian Government eyes cyber security strategy overhaul Protecting SMEs against cyber threat Zero Trust: Past, present and a call to action for the future AustCyber’s Australian cyber week’s national tour WHY BUSINESSES ARE WILLING TO PAY
Siloed IT teams and isolated point solutions are leaving organisations exposed, with ransomware attacks occurring every 11 seconds.
Only Tanium protects every team, every endpoint and every workflow from cyber threats by integrating IT operations, security and risk management teams into a single platform. This provides complete endpoint visibility in a single pane of glass with a common taxonomy to protect critical information and infrastructure, regardless of organisation size.


Find every endpoint with Asset Discovery and Inventory.
Find and fix vulnerabilities at scale in seconds with Risk and Compliance Management.
Track sophisticated attacks in real time with Threat Hunting.
Automate operations, from identification to management, with Client Management.
Index and monitor sensitive data at scale with Sensitive Data Monitoring.
© Tanium 2022
www.tanium.com
Organisations are spending more money on cybersecurity, yet it’s getting worse. It’s time for a new approach.
Bill Nelson is the Chair of Global Resilience Federation (GRF). GRF is a nonprofit association dedicated to helping ensure the resilience and continuity of critical and essential infrastructure and organizations against threats, incidents and vulnerabilities.


Previously, Nelson was the President and CEO of the Financial Services Information Sharing and Analysis Center (FS-ISAC). In his 12 years, Nelson led FS-ISAC in its response to major cyber and physical threats and vulnerabilities that affected the financial services industry, including partnering with Microsoft to take down four major botnet infrastructures. He was also responsible for creating the Sector Services Division of FS-ISAC, which was established to assist other sectors and became the genesis for launching Global Resilience Federation.

Nelson was named the fifth most influential person in the field of financialinformation security by the publication Bank Info Security and he also received the prestigious RSA Award for Excellence in Information Security.

Interview with Bill Nelson Chair, Global Resilience Federation, Director, OT-ISAC CYBER-ATTACKS, CRITICAL INFRASTRUCTURE IMPACT AND RESPONSE IN
ASIA
Contents
Cybersecurity professionals burning out 11
Four urgent actions to create a security culture & protect your organisation 12
Industry-first zero configuration data protection 16 Why industry consultation is vital in Cyber Security 18



AustCyber’s Australian cyber week’s national tour 22 What data is most prized by ransomware attackers? 26
Zero Trust: Past, present and a call to action for the future 28 Observing your software vulnerabilities 31 Protecting SMEs against cyber threat 32
Businesses willing to pay double the ransom in 2022 34

Australian Government eyes cyber security strategy overhaul 36

Australian Government to increase data breach penalties 38 Singapore Government Minister calls for multi stakeholder approach to cybersecurity 41


How Asian companies are fighting cybercrime with graph data technology 42
UK Cyber bosses call for client side scanning to help prevent child abuse 44 We’re still terrible at password management 45
The art of data protection in Formula 1 46

Correspondents* & Contributors
Contents
urgent actions to create a security
& protect your organisation
Past, present and a call to
for the future Businesses willing to pay double the ransom in 2022 How
are fighting cybercrime with graph data technology UK
bosses call for client side scanning to help prevent child abuse The art of data protection in Formula 1 CONNECT WITH US
www.youtube.com/user/MySecurityAustralia OUR
Director & Executive Editor Chris
Director David Matrai Art Director Stefan Babij MARKETING AND ADVERTISING promoteme@mysecuritymedia.com Copyright © 2020 - My Security Media Pty Ltd GPO Box 930 SYDNEY N.S.W 2001, AUSTRALIA E: promoteme@mysecuritymedia.com
Like us on Facebook and follow us on Twitter and LinkedIn. We post about new issue releases, feature interviews, events and other topical discussions.
Four
culture
Zero Trust:
action
Asian companies
Cyber
www.facebook.com/MySecMarketplace/ @MSM_Marketplace
CHANNELS www.linkedin.com/company/my-securitymedia-pty-ltd/
Cubbage
the publisher.
the information
All Material appearing in Australian Cyber Security Magazine is copyright. Reproduction in whole or part is not permitted without permission in writing from
The views of contributors are not necessarily those of the publisher. Professional advice should be sought before applying
to particular circumstances.
Jason Trampevski
Sarah Sloan Dave Russell Dean Vaughan
Dale Heath Nik Vora, Jane Lo*
The wild and wonderful world of tech
With the national attention on significant data breaches in recent months, between January to June 2022, the Office of the Australian Information Commissioner (OAIC) observed a 14 percent decrease in reported breaches compared to July to December 2021. This appears in contrast to the ACSC Annual Cyber Threat Report 2022 which reported the ACSC received over 76,000 cybercrime reports, an increase of nearly 13 percent from the previous financial year. This equates to one report every 7 minutes, up from 8 minutes last financial year
In the first half of 2022, the OAIC was notified of 396 data breaches. Of these, 162 notifications (41 percent) were a result of a cyber security incident, of which the top sources were ransomware, phishing and compromised or stolen credentials.
Despite the overall fall in notifications, the data trended upwards in the later part of the period and draws attention to an increase in larger scale breaches and breaches affecting multiple entities. There were 24 data breaches reported to affect 5,000 or more Australians, four of which were reported to affect 100,000 or more Australians. All but one of these 24 breaches were caused by cyber security incidents.
An annual ransomware survey by McGrathNicol Advisory found that almost seven in ten (69 percent) businesses have now experienced a ransomware attack in the past five years which is a significant increase from 31 percent in 2021. In the event of a ransomware attack, four in five (79 percent) businesses chose to pay the ransom and the average cyber ransom amount paid was $1.01 million, consistent with the year prior. The average amount that businesses would be willing to pay almost doubled to $1,288,608 compared to $682,123 in 2021.
The research also found that many businesses are over-confident in their abilities to respond to a ransomware attack, but the reality is that many are still very unprepared. Almost four in five (78 percent) businesses believe that their organisation is ‘well prepared’ to respond to a cyber-attack, with half (51 percent) reporting that they are ‘very prepared’. However, this is at odds with other details in the research, which found that 13 percent of businesses said it took them two days or longer to inform all relevant stakeholders, whilst three in ten (28 percent) are unsure whether an attack would be reported to all stakeholders. Alarmingly, one in five (20 percent) large businesses with more than 1,000+ employees admit that they did not report the attack to all stakeholders. A potential indicator of under-reporting to the OAIC.
Alongside business, analysis of a survey of almost 3,500 adults during October 2022 by the Australian National University determined
that 32.1 percent (or 1 in 3) said that they or a member of their household had been the victim of a data breach.
These statistics are not surprising. The Optus data breach in September was shaping up as Australia’s worst. Optus faced a USD1 million-dollar ransom demand, with the personal information of over 11 million Australians and 3.66 million driving licence numbers compromised.
To coincide, the Australian Government scrambled to introduce reforms and announced an increase to the existing maximum AU$2.22 million set down by the Privacy Act 1988. Under the bill, the penalty will increase to whichever is the greater of an AU$50 million fine; three times the value of any benefit obtained through the misuse of information; or 30 percent of a company’s adjusted turnover in the relevant period.
The significance of the Optus breach coincided with other serious breaches, including against online retailers, energy providers and defence contractors. Then came a tsunami, the Medibank Private breach.
In a series of WhatsApp messages and emails posted online, REvil, a ransomware group with ties to Russia, at war with Ukraine, threatened to “do everything in our power to inflict as much damage as possible for you, both financial and reputational,” if negotiations broke down and the health insurer refused to pay.
The Medibank breach represents the worstcase scenario in terms of the compromise and exposure of civilian personal information and medical records. Not paying the ransom was the correct decision. It is abhorrent to have this data posted onto the Darkweb, but serious questions need to be answered in how this data was stored and vulnerable to attack. This is the ‘Crown Jewels’ of Australia’s individual civilian data and should have been appropriately safe guarded. Allowing this information to be accessible and exfiltrated makes the Medibank Private Board of Directors and CEO culpable. Given recent findings into the Crown Casino business operations and the board, I’d suggest similar interrogation of Medibank Private and Optus is awaiting.
Practically, every relevant Australian Government agency is now involved. The REvil group has been active for some time and successful, including with significant attacks in
the US and elsewhere. The combined operations between the Australian Federal Police (AFP) and the Australian Signals Directorate (ASD) to commence offensive cyber operations is not new either. They have had this cyber offensive capability since 2017. In addition, law enforcement and intelligence operations will be underlined by investigations by the OAIC and Australian Communications and Media Authority. But other than increasing penalties on the business community, the REvil group and ransomware gangs like them, will continue to be a scourge on the internet. This is the modern version of transnational organised crime –something we have been grappling for decades!
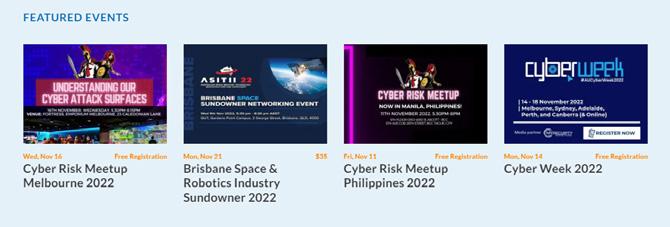
As Official Media Partners for Australian Cyber Week 2022, November 14-18, the national flagship event from Australia’s cyber security growth network, AustCyber, we’re pleased to release this latest digital edition. The week involves events around Australia generating awareness of our national cyber security industry, showcasing local innovation, risk and opportunities, and celebrating one of our most critical industries.
The return of Cyber Week is also centred around the release of AustCyber’s fourth Sector Competitiveness Plan (SCP). Developed with over 60 Australian Cyber Security companies and experts, the SCP represents a critical piece of research that will help shape and inform the cyber security sector in Australia for years to come.
Stay tuned with us and the community via the regular Cyber Risk Meetups and host of event partners across Australia and the Asia Pacific. We otherwise continue to take a deep dive into the cybersecurity domain, corporate risk management and throughout we have links through to our Tech & Sec Weekly Series and the latest Cyber Security Weekly podcasts.
On that note, as always, there is so much more to touch on and we trust you will enjoy this edition of Australian Cyber Security Magazine. Enjoy the reading, listening and viewing!
Chris Cubbage CPP, CISA, GAICD Executive Editor

Editor's Desk
"This is a time for all Australians – the community, business and law enforcement –to stand together and refuse to give these criminals the notoriety they seek"
- Statement by AFP Commissioner Reece Kershaw on Medibank Private data breach, 11 November 2022
Movers and Shakers
Cydarm Partners with Retrospect Labs
Cydarm has announced it has partnered with Retrospect Labs to support the 2022 Australian Women in Security Network Response Competition.
The week-long, national incident style response exercise competition run by Retrospect Labs is being held for the second consecutive year from 7-14 November. It aims to test the skills and support the career development of 250 women across all aspects of cyber incident response, from technical remediation and forensics through to security breach reporting and legal requirements.
Each team will be presented with the simulation of a real-world cyber incident exercise developed by Retrospect Labs which will be enabled, enhanced and rolled out to remotely, distributed and located participants using Gauntlet, Retrospect Labs’ cyber security exercise platform. Cydarm’s case management platform will be available for use by participants to enable team collaboration during incident response activity.
Five participants in each team will be composed of individuals with different knowledge foundations and expertise. Indeed, in order to ensure that the competition is as fair as possible, teams will be made up of women based on their individual, self-identified strengths. Teams can move through the competition at their own pace completing tasks along the way, communicate via a Slack channel and access a mentor to support their journey through the exercises at their own moment of need.
The competition will include forensic artefacts that participants can analyse to identify various Indicators of Compromise (IoCs), as well as understand what malicious activities have occurred and how the adversary undertook those activities, including their tactics, techniques and procedures. Teams will have to use common industry tooling, like Cydarm’s case management platform, to investigate, analyse, record, and report on their findings.
Reflecting all the elements of a cyber security incident, teams will also be required to perform tasks that relate to managing the media, providing communications to senior leadership, and providing legal and privacy considerations in response to the incident. Teams will be evaluated on their performance and across the various tasks completed.
Jill Taylor, Head of Marketing, Cydarm, said, “The rise in significant data breaches and
ransomware attacks have raised public awareness about the importance of securing systems and data. However, according to AustCyber, we’ll need an additional 17,000 cybersecurity workers by 2026 to shore up public and private defences.
While recent years have seen the launch of a string of certificates, diplomas and qualifications in higher education, providing access to realworld software and scenarios is a vital component of up-skilling current and potential employees. Cydarm is committed to supporting people and processes in security operations in ways that solve today’s problems, and we’re excited to support the Australian Women in Security Network and Retrospect Labs in building a diverse, highly skilled workforce.”
Ryan Janosevic, Co-Founder and Chief Operating Officer, Retrospect Labs, said, “We train teams in all parts of incident response, from forensic analysis tolegal, communications and media requirements. We are delighted to be able to run this competition for the second year in a row, applying our skills and knowledge to help the nation encourage more women to progress with their careers in cybersecurity and to give women a hands-on opportunity to experience incident response. As in any industry, we need to constantly ensure that the workplace is diverse, welcoming, empathetic and open to a multitude of skill sets while also ensuring that women who are either already in the industry or who are considering entering the industry, have the opportunity to acquire new skills and feel both empowered and confident in their careers. This competition truly reflects this sentiment.”
The competition’s judges this year include Shanna Daly (Cosive), Kevin O’Sullivan (Kinetic IT), Christine Eikenhout (Australian Cyber Security Centre) and Karen Croughan (an experienced Privacy professional). In addition, the competition is also being supported with event sponsors, including the Australian Signals Directorate (ASD) and the Commonwealth Bank (CBA).
The winning team will be announced during a virtual closing ceremony on the 29th of November.
CyberCX Academy Launched to Help Solve Cyber Skills Crisis
CyberCX has launched the largest private sector training academy for cyber security professionals in Australia.
The CyberCX Academy says it will develop
world-class home-grown talent from a diverse range of backgrounds and experiences to help address the chronic skills shortage facing the cyber security industry.
The CyberCX Academy will deliver 500 additional cyber security professionals into the sector over the next three years. This program represents the single largest private sector commitment to cyber security training in Australia.
Successful candidates will graduate with job-ready skills and certifications across several critical cyber domains including security testing, cloud security, cyber governance, risk and compliance, identity management, digital forensics and incident response.
The CyberCX Academy says its commitment to a more diverse cyber workforce includes recruitment targets for female and other underrepresented groups.
The CyberCX Academy’s model combines classroom training with practical experience from the first day.
CyberCX Academy candidates will have the unique opportunity to be mentored by some of Australia’s leading cyber security experts at CyberCX.
CyberCX CEO John Paitaridis said, “At CyberCX our mission is to secure our communities and that is why we are proud to be making the largest private sector investment in the future of Australia’s cyber security workforce.”
“The CyberCX Academy will seek to attract a much broader and diverse pool of talent than traditional early careers programs, with pathways available to university and TAFE graduates, school leavers, veterans, as well as people wanting to change careers or re-enter the workforce.”
“The current scarcity of a cyber trained workforce is one of the biggest issues facing the economy. We need a step change in investment and approach, which the CyberCX Academy will deliver.”
“We look forward to working with government and industry to develop more pathways for Australians to move into this exciting industry characterised by smart, secure jobs,” added Paitaridis.
The CyberCX Academy’s Director, Rosemary Driscoll noted that “The cyber security industry needs to make itself more attractive and more accessible to a wider range of workers. We believe the CyberCX Academy will achieve this.”
“The inaugural CyberCX Academy cohort includes a former chemist, a retail worker, and a teacher alongside university and TAFE graduates
06 | Australian Cyber Security Magazine
Michael Kirby Appointed Patron of Cyber Mental Health Initiative
The Hon. Michael Kirby AC CMG has been appointed as the inaugural patron of Cybermindz. org. As a former Justice of the High Court of Australia and, as at the time of his retirement Australia’s longest serving judge, Michael has long championed human rights and many causes ennobling of humanity.
He was Chairman of the OECD Expert Groups on Privacy (1978-80) and Data Security (1991-2) and has a longstanding interest in the interplay between technology and humanity.
In welcoming his decision to serve as patron, Cybermindz.org founder Peter Coroneos stated: “We can’t think of a more fitting development for our not-for-profit, dedicated to alleviating the suffering of cyber teams — as we enter both Mental Health and Cybersecurity Awareness Months — than to make this announcement on behalf of the Cybermindz.org board.”
“We are deeply grateful for Justice Kirby’s recognition of the significance of our mission and his role as an advocate, as we move rapidly to bring relief, restoration, healing and resilience to embattled cyber teams and those who support them.”
“He clearly understands the relationship between the protection of personal information, for which he has been a champion, and the need for the cyber teams who are charged to protect it to be effective in their work. Managing their stress and avoiding burnout are fundamental to this mission.
Cloudera Makes a Mark with Former Crayon CEO Appointment
Cloudera has appointed Keir Garrett as its new Vice President for Australia and New Zealand (ANZ), based in Sydney. This appointment comes at a key time for Cloudera as it continues to accelerate its hybrid data footprint across the region through the rollout of new hybrid data capabilities that will allow organisations to have access to fast, self-service analytics and exploratory data science on any type of data cloud.
Garrett brings more than 20 years of management, strategic consulting, and digital
transformation experience to Cloudera. She has successfully developed lines of business in global markets and across multiple industries, both directly with customers, and in collaboration with the partner ecosystem.
Cloudera’s Vice President of Asia Pacific and Japan, Remus Lim comments, “The ANZ region is one of the world’s earliest adopters of hybrid data technologies and our customers are focused on achieving bold growth strategies within their cloud and on-premises environments. However, this desire for accelerated growth also comes at a time of increased pressure to meet higher data security and governance standards. We are extremely pleased to welcome Keir to our senior leadership team at this pivotal time and her knowledge will be invaluable in helping our customers move forward at speed with their data transformation journeys.”
Most recently, Garrett spent two years at Crayon in the role of Chief Executive Officer and prior to this was Head of Software, Cloud, Advisory, Professional & Managed Services Sales at Datacom. Prior to this, she held several senior positions at Microsoft, SAP and Infor.
Garrett comments, “It’s fantastic to be joining a talented group of people, customers and partners. Today’s data savvy organisations know they need to do more with their data to remain competitive. Our customers are looking for the flexibility that allows them to scale their data workloads at speed, across any cloud environment, from multiple data sources. However, this needs to be delivered in a way that drives business efficiencies, cost optimisation and is secure. The team at Cloudera understand this and I’m looking forward to working with them and our expanding channel ecosystem, to help our customers achieve accelerated growth as part of their transformation journeys.”
In line with plans for customer growth, Cloudera is continuing to expand its channel partner ecosystem, announcing Atturra as its newest channel partner in Australia.
Today also sees Cloudera unveiling new hybrid data capabilities in the Cloudera Data Platform across Australia and New Zealand. From today, organisations can improve efficiencies in moving data, metadata, data workloads and data applications across clouds and on premises to optimise for performance, cost and security. Cloudera’s portable data services enable simple, low-risk data workload and data application movement for ultimate data lakehouse optionality. The company’s new secure data replication simplifies and secures movement of data and metadata, the latest SDX enhancement in Cloudera’s unified data fabric.
Lim comments, “Cost or performance is not a choice companies want to make as these are
tightly interlinked. Organisations that choose a data-first strategy can focus on how they deliver value, while being cost-efficient. Being able to move data and workloads anytime and anywhere throughout a modern data architecture is key in allowing organisations to meet evolving business requirements. Cloudera has always provided consistent data security and governance across hybrid cloud, and with these updates will do so between all data services across all infrastructures.”
The new Cloudera data analytics and data management innovations for hybrid data include:
Portable Data Services enable data analytics and the data applications that are built with them to be moved quickly and efficiently between different infrastructures without costly redeveloping or rearchitecting the data applications. CDP Data Services – Data Engineering, Data Warehousing and Machine Learning – are each built on a unified code base and offer identical functionality on AWS, Azure and on-prem Private Cloud. This makes it easier for users, administrators and developers to turn data into value and insight, while providing users with a consistent data experience, irrespective of where the data is stored or where the data applications run.
Secure Data Replication enables data and the metadata to be copied or moved quickly and securely between different Cloudera deployments in data centers and public clouds. Only Cloudera’s replication manager moves the metadata that carries data security and governance policies with the data wherever it goes, eliminating the need to reimplement them and enabling hybrid data flexibility.
Universal Data Distribution enables companies to take control of their data flows, from origination through all points of consumption both on-premises and in the cloud, in a universal way that’s simple, secure, scalable and cost-effective. Universal data distribution is enabled by Cloudera DataFlow, the first data ingestion solution built for a hybrid data world. A true hybrid data ingestion solution that addresses the entire diversity of data movement use cases: batch, event-driven, edge, microservices and continuous/streaming, Cloudera Data Flow turns any data source into a data stream, supporting streaming scale, and unlocking hundreds of thousands of datagenerating clients.
– it’s a group as diverse as the community we seek to safeguard and serve.”
WRITE FOR US!
The Australian Cyber Security Magazine is seeking enthusiastic cyber security professionals who are keen on writing for our magazine on any of the following topics:

• Digital forensics in Australia
• Workforce development
• Security in the development lifecycle
• Threat management and threat hunting
• Incident management
• Operational security
• Security book reviews
• Risk management
• True crime (cybercrime)
If you are interested in writing for us, please send your article pitches (no more than 200 words) to the editors’ desk at: editor@australiancybersecuritymagazine.com.au

You may or may not be familiar with our website, which also provides daily infosec news reviews, as well as our weekly newsletters. We’d like to hear from anyone who’d be interested in contributing blog posts for our platform that reaches out over 10,000 industry
professionals per month, where you can express your opinions, preferences, or simply rant about the state of the cyber security world. If you stay on topic and stick to the facts, we’ll be happy to publish you. If interested, email the editors at : editor@australiancybersecuritymagazine.com.au
08 | Australian Cyber Security Magazine
in Blogging?
Interested


Australian Cyber Security Magazine | 09 www.australiancybersecuritymagazine.com.au DOWNLOAD NOW! App now available on iTunes &
We

Cole provides valuable insight into how they are assisting startups on their DevSecOps journey and the need for a more holistic application of security for clients operating in the broader market.


Niel has over 25 years’ experience in technology and Security – ranging from Data Security to Security Operations, Application Security and Identity. Niel has been working with organisations across the UK and APJ to help address Cyber needs that help build business resiliency. Working across different verticals, Niel has been supporting cyber programs from Smart Cities, Digital Citizen to Digital channels.
 speak with Niel Pandya, Chief Technology Officer with Micro Focus and joined by special guest, Cole Cornford, CEO & FOunder of Galah Cyber.
speak with Niel Pandya, Chief Technology Officer with Micro Focus and joined by special guest, Cole Cornford, CEO & FOunder of Galah Cyber.
DEVSECOPS
– SMOOTHING THE JOURNEY Interview with Niel Pandya CHIEF TECHNOLOGY OFFICER and Cole Cornford CEO & FOUNDER
Cybersecurity professionals burning out
Courtesy of
As October’s Mental Health Month and Cybersecurity Awareness Month both end, a new study from not-for-profit cyber mental health support initiative, Cyber-mindz. org is showing early evidence of burnout in cyber professionals, signalling a potential loss of skills to a critical part of the economy.
The organisation is quick to acknowledge that stress and burnout are not unique to cyber but points out that systemic weaknesses in our human cyber defences would tend to im-pact society at mass levels, especially if essential services like water, energy, telecommunications, health, financial services, food distribution and transportation are affected.
As the nation digests the continuing fallout of the Optus, Medibank and MyDeal breaches and others that are coming to light, the organisation has warned that unless policy makers recognise the mental health impacts on Australia’s embattled cyber workforce, a deterioration in the mental health of core defenders may accelerate, creating a cascading effect of reduced effectiveness and increased risk.
While the research is ongoing and will run until year’s end, Cybermindz founder and veteran internet industry leader, Peter Coroneos explained the importance of signalling the emerging trend as he compared it to ‘the canary in the cybersecurity coal mine’. He observed: “Most of our critical systems now have cyber risk exposure — it’s not hard to see that a reduction in our national cyber capability due to psychological burnout may have population-wide downstream effects.
The pandemic, floods and bushfires have shown us the systems we rely upon are not to be taken for granted.
“Cyber-attacks are a daily occurrence and, unlike natural disasters, there is no conceivable endpoint in sight.” Mr Coroneos added: “Cyber workers are the unsung
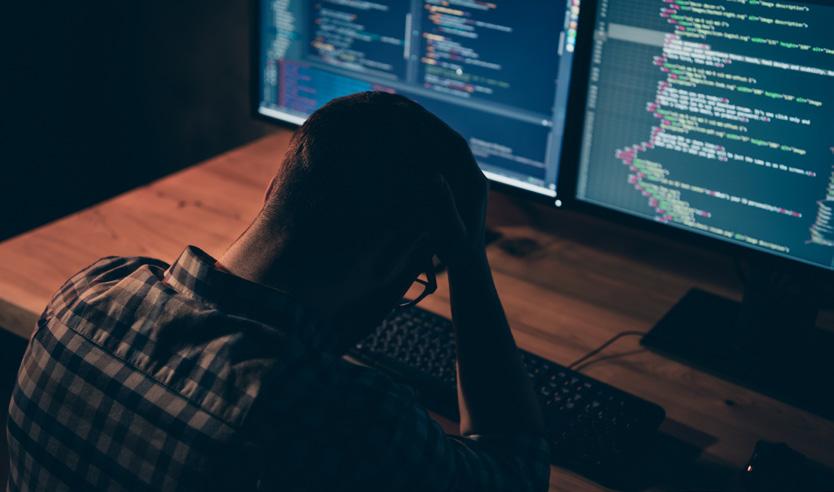
heroes of our time. Their day-to-day work is invisible, but a single failure through a breach which can affect millions of people makes headlines. The rapidly evolving and relentless attack environment defies any sense of ‘job well done’. The one successful attack that could end their career could be around the corner. They are mission-driven with a strong protective ethos. But a sense of hope-lessness will eventually take its toll on even the most committed worker. So it’s important we recognise their efforts and invest in their wellbeing. We must build a strong and resilient cyber workforce. If they fall, we all fall.”
Cybermindz.org Director of Organisational and Behavioural Research, Dr Andrew Reeves is leading the study.
Dr Reeves stated: “Although these are preliminary results, they point to a worrying trend. On the key burnout metric of ‘professional efficacy’ – or how well cyber workers think they are performing in their current roles – they scored significantly worse than the general population. We also compared their rates of burnout on this metric to another highly burnt-out industry: that of frontline healthcare workers, and found that the cyber professionals score considerably lower than even this group on this metric.”
Dr Reeves added: “This is worrying as this metric is a predictor of intention to resign. As a result, I think we are seeing early indications of a cohort of professionals who are questioning their own effectiveness and concluding their efforts are in vain. When good people leave the industry, we lose so much knowledge and expertise. It then increases the pressure on those who remain behind. As a psychological driver of burnout, it’s something we should all be concerned about.”
More Organisations who are concerned about the mental well-being of their cyber teams are invited to participate in the study. There is no cost to participate.
Australian Cyber Security Magazine | 11
Four urgent actions to create a security culture & protect your organisation
By Jason Trampevski, Field Chief Technology Officer, Sekuro
The latest annual report from ACSC found a 13% increase in cybercrime incidents representing yearly losses totalling AU$33 billion. Some headline-making recent attacks on larger Australian organisations actually occurred during Cyber Security Awareness Month in October, a timely reminder that we all need to remain vigilant.
Mere compliance with basic data security guidelines isn’t enough in the current climate. It’s clear that we need to take action against threats at an organisation-wide level.
To properly protect our online ecosystems, we need to act urgently on the four pillars of cyber security preparedness:
• Threat Modelling,
• Human Vulnerabilities,
• Incident Response Planning, &
• Technology Strategy.
Threat Modelling Is The Foundation Of Cyber Security
Information security experts can analyse an organisation and determine from past experience what kinds of attacks are most likely and the vectors that display the greatest vulnerability.
Cyber-attacks take many forms and come from a wide range of different sources. Understanding what specific threats your organisation is most likely to face means you can take a strategic approach to defence, rather than just throwing resources into a generalised defence and crossing your fingers. Threat modelling is the process involved in
establishing these key defensive priorities.
Ultimately, effective cyber security demands a comprehensive, multi-layered approach. However, using threat modelling, we can make good tactical choices about which vulnerabilities we address first, and how we allocate resources to have the greatest positive effect.

Human Vulnerabilities In Your Organisation Can Be Catastrophic
Not everyone in your organisation is cyber security savvy. Most people assume that if they have basic “virus protection” software installed on their computer, then they’re beyond the reach of cyber-attacks. Unfortunately, the reality is very different. People are often the unwitting vectors for destructive cyber incursions. It was the simple mistake of clicking a link in a malicious email that landed the Clinton election campaign boss, John Podesta, in hot water in 2016. From that one simple human error erupted a major cybercrime attack and a damaging political scandal.
Thinking defensively about protecting the people in your office from phishing and hacking attacks can make a crucial difference, but it means making positive changes in your organisational culture as well as your technology. We need to start addressing cyber security as a whole-ofbusiness challenge, rather than just relegating the problem to the IT department.
Communication, planning and active cyber security training are essential first steps. Do your team members know what to look for to identify suspect emails? Are they
12 | Australian Cyber Security Magazine
in the habit of thinking twice before clicking on links? These are the sort of basic educational outcomes to strive for.
Of course, having a rigorous backup system and response plan is still essential. Cyber-attacks do happen, no matter how careful we are, so having failsafe measures in place is vital.
Practice Your Incident Response Plan
Drafting a comprehensive cyber security response plan is an essential basic step, but like any plan, it’s only as good as the amount of time you spend educating your team about it and practising. That’s why we do fire drills; putting a memo up on the wall doesn’t mean much when the building is burning down around you. Everyone needs to understand what they need to do in an emergency, and practice so that they feel confident it will work.
To make a cyber security response plan work, we need to conduct regular reviews so that it doesn’t get out of date. Make sure you do regular training activities, too. Over time teams change, and anyway, people are more likely to remember what they need to do if their training is fresh in their minds.
It can’t be emphasised enough how important it is to educate your team about the cybercrime threats the organisation faces, as well as their role in defence. The magnitude and severity of cybercrime consequences are surprising for most people outside the security industry. If people understand that the very survival of the company they work for can depend on their online behaviour,
they are much more likely to take the threat seriously. Encourage your team members to feel empowered as well as responsible, and make sure there are established communication channels for incident reporting so that vital intel finds its way to the security team before it’s too late.
Technology Strategy: Think Before You Buy
There’s a widely held misconception that the answer to all cyber security challenges is more and better technology. There are thousands of software companies building their business model on promoting this idea, so it’s no wonder many people seem to think that throwing money at the problem is a real solution.
Before you invest in a new cyber security platform, tool or service, make sure it can really address the specific problems faced by your organisation. Do you need it? Or can you simply use the tools you already have to better effect?

Does your technology portfolio integrate properly to give a complete umbrella of protection? Is that defensive perimeter multi-layered, or are you hanging all your hopes on a single product? These are the sort of questions that anyone responsible for cybersecurity decisions should be asking themselves. Technology can give a false sense of security. Putting a shiny software package in place, and ticking boxes on a compliance sheet will feel satisfying, but without continuous maintenance and review, no security measures will stay effective for long.
Digital Trust: What Is It & Why Is It So Important?
All our efforts as cyber security-conscious people are directed toward the ultimate goal of digital trust. This concept – digital trust – is a culture of reliability and resilience that acts as a cohesive productive force within an organisation and then extends outward to embrace all our users, customers & partners.
As Forbes recently reminded us, consumers and people, in general, are “more worried than ever about the privacy of their sensitive data.” We only need to look at the disastrous hacking events that have hit highprofile Australian businesses in recent weeks to see what happens when digital trust is broken. There’s nothing in the world we live in today that can hurt an organisation like the perception that it can’t be trusted with people’s sensitive data. When cybercrime hits an organisation it’s an irrevocable blow to reputation, business value and future earnings alike; not to mention the adverse effects on the broader economy and consumer confidence.
If we plan carefully and involve every member of our teams in the project of cyber resilience, we can turn around the cyber-attack trend.
To learn more about how to robustly protect your entire digital ecosystem and unify Cloud to the Endpoint with a holistic Zero Trust Architectural strategy, watch the on-demand webinar ‘Beyond the Perimeter: Enhancing Access Control’ featuring speakers from Sekuro, Zscaler and CrowdStrike.
Australian Cyber Security Magazine | 13
MITCH KELLY











This session will discuss how to shift your capabilities beyond baseline security, by unifying the Cloud to the Endpoint as part of a holistic Zero Trust Architecture strategy. You can shrink your attack surface drastically via enhanced access control, leveraging the latest integrations announced between Zscaler and CrowdStrike.




JASON TRAMPEVSKI Field CTO | Sekuro Jason is an experienced technology leader and evangelist, with a passion for innovation and creating business value through technology. He leads, advises and consults across a broad range of clients, including ASX-listed companies, government agencies, and household brands. As Field CTO at Sekuro, Jason helps our clients transform their digital and security postures, co-innovating with our global, best-of-breed vendor partners to design and architect fully integrated solutions. MITCH KELLY Practice Build Consultant | Zscaler For over 18 years, Mitch has built deep expertise as a Network, Systems and Security specialist. A veteran with operational experience in Afghanistan, he has built and managed communications networks in some of the most hostile environments in the world. Mitch is Zscaler's Practice Build Consultant in ANZ and advises Zscaler's partners on building industry-leading solutions andservicesfortheirclients. SEN PHILLIP Security Solutions Architect Crowdstrike Sen Philip is a Staff Solutions Architect at CrowdStrike and works with the Channel and Alliances team. Sen has more than 15 years of IT/Security experience in operations, technical sales, architecture and consulting. At CrowdStrike, Sen is responsible for providing technical expertise and guidance in Cyber Security for CrowdStrike's partners and clients. REGISTER FOR FREE BEYOND THE PERIMETER Enhancing Access Control
Field CTO Sekuro
JASON TRAMPEVSKI
Practice Build Consultant Zscaler Security Solutions Architect,
ANZ Crowdstrike
ORGANISED BY
SEN PHILLIP
Zero





ZERO TRUST
MATURING
THE BUZZ
LEVEL 2: PRAGMATIC LEVEL 3: ADVANCED Fundamental capabilities / technology to set the
Zero Trust Environment
DEMYSTIFYING
LEVEL 1:
WE GO BEYOND
WORD
baselines for a
Trust is not just an overused industry term. It’s a vital concept that needs to be considered across an organisation’s technology, people, and process landscape Sekuro’s approach to Zero Trust removes the confusion
your
Implementation of pragmatic ZT protocols; prioritising controls that give strong protection while balancing resourcing and focusing on mitigating biggest risks Implementation of advanced ZT controls with a strong focus on protection, monitoring, automation, orchestration and reduction of all levels of risk Modernise your security program Security as your business enabler A holistic view of your entire security posture Sekuro has developed three maturity levels to allow all organisations to align with a Zero Trust target state, completely customised to their needs. A BESPOKE ROADMAP Start your journey today info@sekuro.io 1800 SEKURO (1800 735 876) sekuro.io
Sekuro’s Zero Trust Strategy encompasses 8 key pillars across 3 maturity levels Sekuro’s Zero Trust Strategy takes a holistic look at
organisation’s entire cyber security posture delivering a formal review and tailored strategy that’s clear, realistic, beneficial, and actionable.
Industry-first zero configuration data protection
Courtesy of
Zscaler has announced new data protection innovations that build upon a rich heritage of securing data across all cloud apps for data in motion, data at rest, and BYOD assets with unprecedented accuracy and scale. The new advancements accelerate data protection programs from months to hours with zero configuration for data loss prevention (DLP). This mitigates security risks by unifying data protection across all channels, simplifying operations by automating workflows.
In today’s highly-mobile and cloud-centric world, data is created and distributed across hundreds of applications and workloads, escalating organisations’ risk of data loss. Enterprises’ inability to protect distributed data is reinforced in the findings of the new 2022 Data Loss Report by the Zscaler ThreatLabz research team. ThreatLabz found that 36% of cloud application data is accessible via the open internet. Analysis of nearly 6 billion data loss policy violations revealed that organisations experience an average of 10,000 potential data loss events daily resulting in losses greater than $4.35 million.¹
Traditional DLP solutions can’t secure distributed data and require a massive amount of resources to configure, maintain and manage, which can be costly and result

in months to implement, putting organisations at risk. Concurrently, the lack of automated workflows prevents security teams from managing critical risks leading to elongated mitigation timelines and unresolved incidents. To make matters worse, the reliance on separate point products for different channels causes increased risk, reduced visibility and inconsistent policies. Organisations that have not deployed a unified zero trust strategy suffer an additional $1 million loss on average¹, indicating that data protection cannot be a standalone endeavor.
“Building on eight years of data protection innovations, Zscaler has employed advanced auto-classification capabilities to accelerate setup and reduce security team overhead and costs,” said Moinul Khan, Vice President & General Manager, Data Protection, Zscaler. “Unlike other data protection solutions, this ensures that Zscaler Data Protection works for the IT administrator, rather than having the IT administrator work for it. In addition, the technology we acquired from the recently announced ShiftRight acquisition allows organisations to manage hundreds of potential risks and incidents in a simple yet very sophisticated way to reduce case resolution time significantly.”
The recently introduced security category, security
16 | Australian Cyber Security Magazine
service edge (SSE), reinforces the market’s need for unified data protection as part of a larger, purpose-built security platform. These advancements to the Zero Trust Exchange, aligned to SSE principles, further Zscaler’s position as a leader in data protection by empowering security teams with: Expedited Deployment Cycles with Zero Configuration
DLP: Utilising the scale of the world’s largest security cloud that processes 170 million files per day, the new zero configuration DLP capabilities auto classify all organisational data, thereby accelerating the deployment of data protection programs.
Mitigated Security Risks by Unifying Data Protection
Across all Channels: The addition of endpoint, and email data protection capabilities adds to the existing support of web, SaaS, IaaS, PaaS and private apps. This removes the need for point products, decreasing security risks and management complexity by unifying policies across channels.
Simplified Operations through Automated Workflows: Advanced closed-loop incident management delivers actionable insights and automates workflows to respond to potential security risks in a timely and effective manner.

“Securing data is always a challenge due to complex
workflows and inconsistent protection strategies and coverage across users and devices,” said Bashar Abouseido, CISO, Charles Schwab. “With Zscaler, that has all changed, as we now have one unified platform with full visibility and policy control while drastically streamlining our processes.”
“Zscaler is one of the most seamless, straightforward deployments I’ve seen in a while,” said Thomas Likas, Head of Cyber & Digital Trust Enterprise Architecture, Takeda. “Their comprehensive and unified approach to protecting data across all channels helps us transform and evolve our data protection program, ensuring sensitive data remains secure from accidental loss or malicious exfiltration.”
“The DLP market has long suffered from complexity and efficacy issues due to the need for time-intensive, manual configuration and management,” said John Grady, Senior Analyst, Enterprise Strategy Group (ESG). “Zscaler’s massive data set, garnered from the 250 billion transactions its security cloud processes every day, provides impressive scale and a key differentiation in the market. This scale enables greater visibility and accuracy, which translates into ease of use, better efficiencies, and lower costs for customers.”
Australian Cyber Security Magazine | 17
“Zscaler is one of the most seamless, straightforward deployments I’ve seen in a while,”
Why industry consultation is vital in Cyber Security
 By Sarah Sloan Head of Government Affairs and Public Policy, ANZ.
By Sarah Sloan Head of Government Affairs and Public Policy, ANZ.
The dust is yet to settle following the unfortunate Optus data breach, and the nation’s Minister for Cyber Security, Claire O’Neil, has already flagged plans for reform.
The Government’s continued commitment to improving Australia’s cyber security resilience and data security is laudable and should be welcomed. When a major data breach occurs, it is reasonable for governments and citizens to ask whether our current laws are adequate and fit for purpose.
Last week, the Government announced that banks and other financial institutions would be informed of data breaches when they occur to help identify and prevent fraudulent activity. These measures could be a major and much-needed boost to enhancing consumer protections in the face of future data breaches, so long it is underpinned by cyber security and privacy principles. As with all policy, however, the devil is in the detail.
As noted by ABC News, Minister O’Neil herself has suggested that current data and cyber security requirements need to be fit for purpose. And to make them fit for purpose, it’s essential that the relevant industry stakeholders are in a position to help shape them – or at least contribute to the conversation, so all aspects are considered.
The decision to bring the country’s financial services industry into the breach notification loop may be an appropriate first step to elevating data security across the board. Australia’s banks have done a reliably good job of
sharing information about cyber security threats and best practices between each other.
But any obligations placed on banks or other institutions need to be reasonable and proportionate. Moreover, the scope of any potential regime may need to be expanded to include other companies, as well as state and federal government authorities – such as those that issue driver’s licences or Medicare cards.
Today, Australia’s expectations with respect to data governance and data breaches sit firmly within the Privacy Act, so any review into the adequacy of our laws in the wake of this recent breach, must logically start there. The Privacy Act remains the most appropriate instrument to address the public’s concerns around the management and retention of their personally identifiable information.
The Government has already flagged amendments to the Privacy Act – saying it may look to increase the penalties associated with data breaches and broaden our privacy obligations to better align with international best practice. While this may be the impetus for cultural change across Australia, the Government may also wish to look at incentives for adherence to good practices.
However, precisely what constitutes reasonable and proportionate regulation can only be ascertained through consultation with the industries it may affect.
So it’s important that the Government takes a holistic and considered approach to any policies and regulatory changes it deems necessary by talking and listening to
18 | Australian Cyber Security Magazine
trusted industry stakeholders.
When it comes to cyber security, I think we can all agree on the importance of up-to-date and best practice standards, policies and laws to keep pace with evolving threats.
In April this year, the former Government, with support of the then opposition, passed significant and far-reaching reforms aimed at increasing the cyber security posture and resilience across our critical infrastructure. These new obligations are still coming into legal effect and continue to be implemented by industry in partnership with the Government. While the cyber threat landscape moves quickly, it is important that policy makers understand how regulatory obligations operationalise when considering additional layers of responsibility. We should not move the regulatory goalposts on industry now.
The more industry can work together and with the Government, the greater the chances are of keeping pace with the evolving threat landscape. Such public-private consultation and industry collaboration also support the evolution of the technology that is playing an increasingly important role in providing visibility of, and defending businesses and individuals from cyber attacks in real-time.
As we’ve seen over recent years, cyber attacks can affect anyone, and it is in the interest of all of us to be part of the solution. A hit on one of us is a hit on all of us. On this front, industry has just as much a part to play as the Government, both in the implementation of appropriate technology and the development of new policies and regulations.
This is why the effective collaboration between Government at all levels and the private sector to tackle the rise in cyber attacks has never been more of a priority. And perhaps nowhere does such collaboration make more of an impact than when it comes to creating new policies aimed at protecting businesses and their customers from harm.
The federal Government is already doing some good work in the area of public-private collaboration on cyber defence. This can be seen in initiatives such as the Australian Cyber Security Centre (ACSC) Partner Program, which gives organisations and individuals the opportunity to engage with the nation’s cyber agency and fellow partners to draw upon collective understanding, experience, skills, and capability to lift cyber resilience across Australia. This program could be further utilised to develop new guidance materials and security advisories on important security concepts such as attack surface management and zero trust.
As the above initiatives demonstrate, we’re heading on the right path. Now, we need to further deepen collaboration to the decision-making processes behind the development of new policies and laws to help protect Australia people and businesses against future cyber attacks and data breaches.
After all, cyber security is very much a team sport. By working together, the whole is made more powerful than the sum of its parts. But if the wrong players are left on the bench, it could lead to a lost game. And cyber security is definitely a game we don’t want to lose.

Australian Cyber Security Magazine | 19
Cybersecurity is a complex problem to solve.
20 | Australian Cyber Security Magazine ACSM
www.sophos.com
It’s okay to call a friend.
We speak with Hywel Morgan, Manager, Systems Engineering for ASEAN and Korea, Sophos.




Cybersecurity has become too complex for most organisations. While every organisation wants the best cyber defences, few have the skilled resources to deliver them.
Almost every organisation has a strategic initiative driving their digital transformation journey. Customers need to be served digitally and remotely, rather than visiting physical locations. Employees need to remain productive despite needing to work from home. The nature of an organisations network changed fundamentally, and a much larger and more vulnerable attack surface was exposed to attackers using more sophisticated methods. The traditional response is to buy yet more cybersecurity technology further overwhelming security operations teams, which in many SME is a single person also responsible for many other IT tasks.
Despite organisations spending record budgets on cyber-defences, attackers are more successfully infiltrating networks and remaining undetected for longer. The current model isn’t working for most organisations.
Interview with
Manager, Systems Engineering for ASEAN and Korea, Sophos CYBERSECURITY COMPLEXITY IN THE DIGITAL TRANSFORMATION JOURNEY
Hywel Morgan
AustCyber’s Australian cyber week’s national tour
Cyber Week, the national flagship event from Australia’s cyber security growth network, AustCyber, is returning in 2022. Running from November 14-18, this year’s event will travel around Australia generating awareness of our national cyber security industry, showcasing local innovation, risk and opportunities, and celebrating one of our most critical industries.
As part of the Stone & Chalk Group, AustCyber will be hosting Cyber Week 2022 at Stone & Chalk’s state-ofthe-art startup hubs across the country. For the first time since its inception in 2017, Cyber Week will be travelling to Melbourne, Sydney, Perth, Adelaide and Canberra, offering in-person and virtual world-class events. Supported by industry leaders from government, corporates, entrepreneurs and small businesses, Australia’s best experts will share their knowledge and experience to drive robust discussion, solutions and debate.

The return of Cyber Week is also centred around the release of AustCyber’s fourth Sector Competitiveness Plan (SCP). Developed with over 60 Australian Cyber Security companies and experts, the SCP represents a critical piece of research that will help shape and inform the cyber security sector in Australia for years to come. The week’s activities follow unprecedented levels of high-profile cyber security incidents in Australia, highlighting the critical
need for increased attention on cyber security maturity, investment and resilience.
AustCyber’s new Group Executive, Jason Murrell, said: “We’re delighted to bring Cyber Week back alongside the release of the fourth annual SCP. Cyber security is an area of increasing national concern, and we look forward to bringing together the country’s cyber leaders to reinforce the growing resilience of our local industry, explore opportunities for local innovation and international growth, and enable wider industry collaboration and connection at Cyber Week 2022.”
Stone & Chalk Group CEO, Michael Bromley, said: “Cyber security impacts all areas of our digital lives as recent events have shown us. Cyber security is fundamental to every business and to building a sustainable technology driven economy. Cyber Week 2022 will be a fantastic opportunity for all businesses, not just in cyber security, to participate and learn.”
Cyber Week will showcase Australia’s cyber security capability and address the increasing demand for highly skilled technology workers. Expert panels and workshops featuring industry leaders including Martin Boyd, former Executive Manager of Cyber Security for CBA and
Founder of Vertex Cyber Security, and Susie Jones, co-Founder of Cynch Security, will discuss the biggest pain
22 | Australian Cyber Security Magazine
Courtesy of
points impeding the growth of the sector, and the steps required to skill and educate Australia’s future workforce.
In collaboration with the Australian Women in Security Network (AWSN), AustCyber will also delve into the diversity issues holding the sector back and its wider implications for the ongoing sector skills shortage. The work of other industries and professions that have successfully diversified their workforces will be analysed to determine how the cyber security sector must move forward to create a diverse and inclusive environment.
Below is the list of Cyber Week 2022 events available to attend:
• Monday 14 November — Hosted at Stone & Chalk’s Melbourne Startup Hub, AustCyber will explore key findings from its Sector Competitiveness Plan (SCP), the risk of a sustained attack on Australia’s critical infrastructure, and partner with the Australian Women in Security Network (AWSN) for a panel discussion on diversity issues holding the sector back.
• Tuesday 15 November — Hosted at Stone & Chalk’s Sydney Startup Hub, panellists will delve into the biggest pain points facing the industry including skilling, reskilling, upskilling and educating our future workforce.
• Wednesday 16 November — Hosted in Perth in
partnership with the Joondalup Business Forum, this event will focus on Australia’s export market looking at how we can leverage our international partnerships and alliances to enable growth.
• Thursday 17 November — Hosted at Stone & Chalk Adelaide Startup Hub, AustCyber will discuss the current growth of Australia’s cyber security ecosystem and future trajectory under the SCP.
• Friday 18 November — Hosted in Canberra, AustCyber will share details on the National Missing Persons Hackathon and how OSINT is helping law enforcement around the world.
Free tickets are now available in-person and online, however registration is essential at www.cyberweek2022. austcyber.com.
MySecurity Media is proud to be Official Media Partners of Cyber Week 2022.

Australian Cyber Security Magazine | 23
Cyber Week explores the full breadth of the cyber security sector, providing an opportunity to learn and celebrate one of Australia's most critical industries.
As part of the Stone & Chalk Group, AustCyber will be hosting Cyber Week 2022 in Stone & Chalk's state-of-the-art startup hubs across Sydney, Melbourne, and Adelaide. The Perth event will be held at the Joondalup Business Forum and our Canberra event will be hosted at Hotel Rydges Canberra.

We speak with Michael Brom ley, CEO Stone & Chalk Group and get an overview of the week of events and AustCy ber's flagship publication - The Sector Competitiveness Plan (SCP), which has been devel oped with over 60 Australian Cyber Security companies and experts.

We speak with Jason Murrell on his role as Group Executive and the focus of AustCyber nationally on raising cyberse curity awareness, workforce development and the out comes of the Sector Competi tiveness Plan (SCP).
To find out more - visit www.austcyber.com #AUCyberWeek2022
24 | Australian Cyber Security Magazine ACSM
We speak with Jacqui Loustau, Founder of the Australian Women in Security Network (AWSN) and some of the key trends in developing diversity and opportunities for women in the cybersecurity sector.



We speak with Kate Pounder, CEO of the Technology Coun cil of Australia and discuss the challenges of developing a skilled workforce for the technology and cybersecurity industries. To
We speak with Linda Cavana gh, Chief Operating Officer of Cybermerc and the founder of the Missing Person Hackathon.
Australian Cyber Security Magazine | 25 ACSM
w
#AUCyberWeek2022
find out more - visit
ww.austcyber.com
What data is most prized by ransomware attackers?
Anew report by Rapid7 investigates the trend, pioneered by the Maze ransomware group, of double extortion, examining the contents of initial data disclosures intended to coerce victims to pay ransoms.
“Pain Points: Ransomware Data Disclosure Trends” reveals how ransomware attackers think, what they value, how they approach applying the most pressure on victims to get them to pay, and insights on the data threat actors prefer to collect and release.

With access to a network and holding that data for ransom, ransomware is now one of the most pressing and diabolical threats faced by cybersecurity teams. Causing billions in losses across most industries, it has stopped critical infrastructure like healthcare services in its tracks, putting at risk the lives and livelihoods of many.
Threat actors have upped the ante by using “double extortion" as a way to inflict maximum pain on an organisation. Through this method, not only are threat actors holding data hostage for money, but they also threaten to release that data (either publicly or for sale on dark web outlets) to extract even more money from companies.
In a first-of-its-kind analysis using proprietary data collection tools to analyse the disclosure layer of doubleextortion ransomware attacks, Rapid7 has identified the types of data attackers initially disclose to coerce victims into paying ransom, determining trends across industry and geography. Australia was positioned eighth in the rankings for distribution of ransomware incidents in the top 12 countries.
The report examined all ransomware data disclosure incidents reported to customers through its threat intelligence platform between April 2020 and February 2022, and incorporates threat intelligence coverage and institutional knowledge of ransomware threat actors. This analysis determined the following:
• The most common types of data attackers disclosed in some of the most highly affected industries and how they differ
• How leaked data differs by threat actor group and target industry
• The current state of the ransomware market share among threat actors and how that has changed over time
Overall, trends in ransomware data disclosures pertaining to double extortion varied lightly, except in pharmaceuticals, financial services, and healthcare. In general, financial data was leaked most often (63%), followed by customer/patient data (48%).
In the financial services sector, customer data was the most leaked, rather than financial data from the firms themselves. In the healthcare and pharmaceutical sectors, internal financial data was leaked some 71% of the time, more than any other industry. In the pharmaceutical industry the prevalence of threat actors to release intellectual property (IP) files stood out, where 43% of all disclosures included IP.
The report provides a clearer understanding of the state of ransomware threat actors. We can pinpoint the evolution of ransomware groups, what data the individual groups value for initial disclosures, and their prevalence in the market. The top five groups in 2021 made up 56% of all attacks, with a variety of smaller, lesser-known groups responsible for the rest.
While there is no silver bullet to the ransomware problem, there are best practices organisations can take to protect against threat actors and minimise the damage, should they strike. To download the latest Ransomware Report, visit. https://information.rapid7.com/rs/411-NAK-970/ images/Ransomware-Data-Disclosure-Report.pdf
26 | Australian Cyber Security Magazine
Courtesy of
Be Future Ready
Innovate without slowing down. Get the visibility, analytics, automation and expert guidance you need to stay ahead of attackers, ahead of the competition, and future ready for what’s next.



Download
latest Ransomware Report
Shutdown attacks with clarity and confidence
Learn how we can help: Visit us at www.rapid7.com or email us at anzsales@rapid7.com the
Zero Trust: Past, present and a call to action for the future
By Dave Russell
Vice President of Enterprise Strategy, Veeam and Rick Vanover, Senior Director of Product Strategy, Veeam.
A recent study by CyberRisk Alliance revealed some surprising statistics about zero trust security. While the term has been around for the last 30 years, only 35% of the security leaders polled were familiar with the practice. More surprisingly, despite the gradual rise of security incidents the same percentage were highly confident in their zero trust capabilities.

While interest in zero trust has grown, many security leaders appear to be confused on how they should implement it. There is a misconception that zero trust is a plug-and-play feature, but the reality is far from that – it essentially changes the way people work.
The concept of zero trust is simple: “never trust, always verify.” It may seem harsh to users that are used to having easy access to information, but it’s a sound policy. We prefer to use the phrase “mutually suspicious,” which is similar. It means, in effect, “Here’s who I am; you prove to me who you are.”
The truth is that to a certain degree, this practice and term is old, dating back to the era of mini computers and mainframes. It’s all about requiring good digital hygiene. What has changed is, our environment has shifted and expanded. Now, with cloud, edge devices, and data centers opening up more endpoints to attack,
organisations have to rely on more than firewalls to keep intruders out and data safe.
Organisations need to align their processes and people, along with their products, to achieve true zero trust.
Implementing such products are a straight-forward step. Essentially, what’s needed is a full line of security technologies that verify identity, location and device health. The main objective is to minimize the blast radius and limit segment access. While there is no single product or platform that accomplishes all these goals, a successful zero trust program will incorporate elements of identity management, multifactor authentication and least-privileged access, setting restrictions and additional steps to access information.
Involving People
Today, zero trust technologies are available to cover all attack surfaces and protect organisations, but they are as useful as the people using them, so aligning company success and security with employee success and security is critical. This means prioritising a culture of open communication, implementing policies, transparency, trust in the process and faith in each other’s ability to do good.
To successfully implement zero-trust technology into a corporate culture, organisations need to involve employees across all levels in the process. Don’t just roll out a topdown mandate and expect it to click. Employees should be
28 | Australian Cyber Security Magazine
properly briefed on the process of zero trust, how it impacts their workflow and the benefits it brings to the company. Setting them up for success and educating them on what to watch out for can move the adoption of zero trust.
By engaging employees and challenging them to embrace a healthy dose of skepticism towards potential threats, employers form a level of defense when it comes to protecting data. Once employees understand what’s going on and the value of zero trust, they too begin to feel trusted and are empowered to be part of the broader cybersecurity network. This empowers employees to proactively identify insider and outsider threats to the enterprise, covering all surfaces and fostering good security hygiene.
Reassessing Processes
One of the most important moves an organisation can make is to define and assess every aspect of its data security environment. From identifying where all the organisation’s unstructured data is stored to what business purposes specific data stores serve, knowing who has access to it and what kind of security controls are in place helps to allow for better security.
A thorough permissions assessment will help guide the development of a comprehensive access management policy. Some assets will require zero trust protection; others won’t. All devices that connect to a network will
need to be accounted for, so they can fend against outside phishing attacks.
One key tech mechanism that can help organizations in a zero-trust world is immutability – creating data copies that can’t be modified or deleted. This ensures organizations don’t lose data or allow it to end up in the wrong hands.
An overlooked practice is to define a common zerotrust framework for the whole organisation. Teams should be aligned on what zero trust is and ensure that this definition is applied across all projects and employee levels.
Last, and perhaps most important, is the need to reassess and revise their zero trust processes. Zero trust is an ongoing process and should be treated as a regular routine. Think of it like going to the gym: Exercise becomes a way of life, and active people tweak their workout routines all the time. Same with security. Zero trust is a continuum. You’re never done.
Staying Flexible
Threatscapes will continue to evolve over time. Organisations taking a zero-trust approach will need to continue to develop a comprehensive plan – and then continually revise their technologies, processes and people practices to meet their future needs.

Australian Cyber Security Magazine | 29
















KPMG.com/au
© 2022 KPMG, an Australian partnership. All rights reserved.
Observing your software vulnerabilities
When the engine warning lights come on in a car, one typical reaction for many drivers is to be startled, then continue to drive off, if the car still works. Some may go buy a coupon or voucher later to change the engine oil. Others might schedule a check-up at the workshop.
By eliminating false positives and with no performance impact, it is ideal for in-production use and addresses the rapidly increasing enterprise risk around software supply chain attacks.
By Dean Vaughan, Vice President of Asia Pacific, Azul

Yet, many more will procrastinate and wait until a real issue – say, if the engine stalls or if the car stops moving – to get a fix. By then, the problem might have become more serious than when the first warning light went off. This could mean hefty repair costs if the damage has become extensive.
The same applies to cybersecurity. With such complex IT systems and often numerous cybersecurity tools in place today, the first reaction for many IT teams looking at a warning light or alert on a dashboard is to shut it down or wish it away, especially if they are busy.
Just like with a car, if the “warning light” for a cybersecurity issue is generic and does not specifically show what the problem is, human operators often respond with apathy. After all, if you do not know what to fix, how do you fix it? That is one of the biggest challenges today, as cybersecurity teams are overloaded with notifications and dashboards and suffer from alert fatigue.
Worryingly, software supply chain vulnerabilities, which expose organisations to attacks through third-party code, are becoming more prevalent and harder to overcome. By 2025, 45 per cent of organisations worldwide will have experienced attacks on their software supply chains, a threefold increase from 2021, according to research firm Gartner.

For example, organisations continue to grapple with Log4Shell, a critical vulnerability found in a widely used Java-based logging component (Log4j). This vulnerability impacted countless servers and applications that used Java software. It exposed so many organisations to cyberattacks simply because Java is used widely in today’s modern IT infrastructure.
The Log4Shell loophole enabled threat actors to run code on a victim’s system and take control. In another incident last year, a major flaw in the Atlassian Confluence collaboration software, a Java application, also enabled hackers to take over a server remotely and steal data.
The challenge is finding a way to zoom in on the specific piece of Java software or code that is vulnerable, instead of manually sieving through the entire stack to find a problem.
This is where Azul Vulnerability Detection, a new SaaS product that continuously detects known security vulnerabilities that exist in Java applications, comes in.
Azul Vulnerability Detection uniquely identifies code run using sophisticated, highly granular techniques inside Azul JVMs and maps against a curated Java-specific database of common vulnerabilities and exposures (CVEs). This produces more accurate results, even for custom code and shaded components.
Doing so means greater visibility for teams to proactively resolve an emerging problem. By focusing the detection on the production environment where the Java code is deployed, Azul Vulnerability Detection shows users what is running in real time, and where exactly the vulnerabilities are.
What’s different from previous tools here is the Java virtual machine (JVM), which provides highly accurate runtime-level visibility into what code is actually running and whether it is vulnerable. This enables faster remediation of vulnerabilities with significantly less operational overhead. Additionally, because the tool is agentless it avoids the performance penalty commonly associated with other security tools that require teams to install and maintain a separate piece of software. Taken together, Azul Vulnerability Detection makes security a by-product of simply running Java software.
Azul Vulnerability Detection enables ongoing detection at the point of use in production, the critical end step of the software supply chain. It applies intelligence while overlaying knowledge of what components are vulnerable, enabling a deep inspection of what constitutes a threat.

Even with shading, which can be used to change the name of a component, say, from Log4j to app.jar, the Azul service will find the component. This is something that a simple file-based scan might fail to catch. Key here is Azul’s deep Java roots, which go back more than 20 years. It understands Java conventions like shading, and it properly recognises what those components are.
Any organisation running Java should be asking where their Java applications are vulnerable and where the efforts to fix these vulnerabilities should be directed towards.
The exploits are out there, and threat actors are using them but for the good guys, a patch is often scheduled for “later”, much like a driver postponing a check after seeing an engine light warning. Well, later has to become now, starting with visibility into one’s system and taking action early.
Australian Cyber Security Magazine | 31
Protecting SMEs against cyber threat
Australia’s biggest bank and telecommunications company have joined forces with the Council of Small Business Organisations Australia (COSBOA) in a new initiative to help protect small businesses from cyber threats and scams which cost the economy an estimated $29 billion a year.

The program will be designed by small business, for small business, aiming to upskill the nation’s small business workforce and give owners and employees the tools they need to stay safe online, through a free and easy to use accredited e-learning platform.
According to the Australian Cyber Security Centre (ACSC), 43 per cent of all Australian cyber crime is directed at small businesses – costing small business owners almost $9,000 on average. As online scams and fraud continue to rise, it is critical that Australia’s almost 5 million small business employees are supported to upskill their cyber safety knowledge.
COSBOA CEO Alexi Boyd says the aim of the Cyber Wardens program is to develop crucial skills training for small business owners who have felt powerless in the digital safety space. She notes that for many small businesses the struggle to upskill is made harder by limited resources, time and technology expertise.
“We believe that having a Cyber Warden on the team will help give small business owners the confidence that their business and customers are protected,” Ms Boyd says.
“With the support of Telstra and CBA, and I hope many more corporate partners, we can provide free, simple and accessible resources to the small business community. We want to foster a culture of self determination and
understanding in cyber safety — no IT degree, excel expertise and cloud wizardry required.”
CBA’s Group Executive for Business Banking, Mike Vacy-Lyle, says it is crucial the small business sector is equipped with the skills it needs to stay safe online.
“Understanding a complex topic like cyber safety can be challenging and we are always looking for ways to better support small businesses in this space. We’re excited to launch the Cyber Wardens pilot program to help demystify cyber safety, instill a cyber-mindset and empower small businesses to identify and manage cyber threats,” Mr VacyLyle says.
For Telstra’s Small and Medium Business Executive, Anne Da Cunha, making cyber safety easy delivers clear benefits for small businesses.
“At Telstra we know that for busy small business owners, defending your business against cyber threats can feel overwhelming. The solution lies not just in protecting devices and your internet connection, but also the cyber safety culture you create,” Ms Da Cunha says.
“Managing small business risks online shouldn’t be like the dark arts — and the Cyber Wardens program will help show that there are easy proactive steps businesses can take that will help protect bottom lines, reputations and customers’ privacy.”
Designed specifically for non-tech employees, the Cyber Wardens pilot program will be rolled out in coming months to safeguard Australia’s 2.3 million small businesses and upskill everyday Australians to become our nation’s cyber security frontline.
32 | Australian Cyber Security Magazine
Courtesy of

Businesses willing to pay double the ransom in 2022
By Dale Heath Head of Solutions Engineering, Rubrik A/NZ
McGrathNicol Advisory today unveiled the findings of its annual ransomware survey, revealing the true extent of ransomware attacks on Australian businesses and the willingness of leaders to make substantial payments to cybercrime groups.
Following on from research conducted in 2021 and in partnership with YouGov, McGrathNicol Advisory surveyed over 500 business owners, partners, directors and C-Suite leaders across Australian businesses with 50 or more employees.
The 2022 research found that almost seven in ten (69 percent) businesses have now experienced a ransomware attack in the past five years which is a significant increase from 31 percent in 2021.

In the event of a ransomware attack, four in five (79 percent) businesses chose to pay the ransom and the average cyber ransom amount paid was $1.01 million which is consistent with the prior year. The average amount that businesses would be willing to pay however, is higher and has almost doubled to $1,288,608 compared to $682,123 in 2021. This shows that businesses are anticipating the financial fallout of a cyber breach far better than they were 12 months ago.
The research reveals further key findings:
• The timeframe for ransom payments has shortened: 44 percent of businesses attacked paid a cyber ransom within 24 hours (up from 23 percent in 2021).
• Negotiation is also less likely to have taken place: Of those business leaders who have paid a cyber ransom, three in five (59 percent) chose to negotiate with cyber criminals to lessen the financial and operational damage to their business, compared to three in four (74 percent) last year.
• Residual uncertainty over consequences of ransom payment: Close to one in five Australian organisations are unaware that paying a ransom funds criminal organisations.
• Email fraud is the most common mode of entry: Known as “business email compromise” or “phishing”, almost 75 percent of all ransomware attacks can be attributed to human error, while the remaining 25 percent are a result of vulnerabilities exploitation and malicious access.
Darren Hopkins, Cyber Partner at McGrathNicol Advisory, said: “Many businesses are under pressure to pay and ‘keep the lights on’ rather than try their hand at negotiating with nefarious cyber-criminal groups. Given that almost a third of businesses are willing to pay more than $1 million in
34 | Australian Cyber Security Magazine
COVER FEATURE
ransom payments, and pay quickly, the research shows that business leaders are starting to treat the ransomware threat as they would any other business risk.”

“This is a challenging environment for business leaders, and while many feel as if they don’t have the luxury of time, we want to assure them that there is always help available. Just as we encourage businesses to review and practice fire drills, we urge business leaders to develop and stress-test their cyber resilience plans. When a ransomware attack inevitably occurs, you and your board will know exactly what comes next.”
The research found that many businesses are overconfident in their abilities to respond to a ransomware attack, but the reality is that many are still very unprepared. Almost four in five (78 percent) businesses believe that their organisation is ‘well prepared’ to respond to a cyber-attack, with half (51 percent) reporting that they are ‘very prepared’. However, this is at odds with other details in the research, which found that 13 percent of businesses said it took them two days or longer to inform all relevant stakeholders, whilst three in ten (28 percent) are unsure whether an attack would be reported to all stakeholders. Alarmingly, one in five (20 percent) large businesses with more than 1000+ employees admit that they did not report the attack to all stakeholders.
Shane Bell, Cyber Partner at McGrathNicol Advisory
said: “With September’s Optus breach and October’s Medibank breach dominating headlines, it’s more important than ever that governments, regulators, and corporate Australia work together to minimise risk to consumers and critical industries, reinforcing Australia’s 2016 strategy to make Australia a hard target for cybercriminals.”
“Building muscle memory around response and recovery is important, but it is only one part of the process of building overall cyber resilience. Organisations really need to understand the current and evolving threat landscape. They need to make decisions about their own risk profile and risk appetite, and then use that information to build a program of continuous improvement geared towards building cyber into business-as-usual practices. Cyber isn’t a new agenda item—it is and should be an established component by now.”
As the debate continues on the need for enhanced ransomware reporting in Australia, McGrathNicol’s research shows that businesses want greater transparency, stronger intelligence sharing and reporting obligations. Three in four (75 percent) businesses believe that it should be mandatory for a business to report a ransomware attack to the authorities (up from 67 percent), with almost three in five (56 percent) believing that it should be reported regardless of whether a ransom payment is made (up from 43 percent).
Australian Cyber Security Magazine | 35
Australian Government eyes cyber security strategy overhaul

Australia’s highly touted 2020 Cyber Security Strategy is set for an overhaul as the new Labor Government settles into office. On Friday, reports emerged that the AU$1.7 billion ten-year strategy would pivot towards building greater sovereign cyber-capabilities and workforce skills.
Countering cyber-threats was a key priority of the previous Morrison Government but their efforts were frequently criticised as tardy, lacking agility, and over-egging future cyber-capabilities such as appropriately skilled workforce numbers.
In addition to the Cyber Security Strategy, the former Australian Government rolled out the Ransomware Action Plan in October 2021 and provided $9.9 billion in the March 2022 budget for the Australian Signals Directorate (ASD) and Australian Cyber Security Centre (ASCS) to hire more staff.
But new Home Affairs Minister Clare O’Neil wants the 2020 Strategy reworked. Besides building up those sovereign capabilities and cyber workforce skills, the Minister wants to improve links with Australia’s Quad partners and reduce Australia’s reliance on China for critical technologies.
“It will be grounded in sovereign capability, with a plan for the future workforce and growth of the cyber security sector, including Australian cyber-SMEs,” Ms O’Neil told The Australian on Friday.
“It will build resiliency, with real engagement and industry alliances to deal with cyber shocks in an assured, not anxious way.”
Aside from dealing with rising numbers of cyber-attacks, there are growing concerns that projected cyber-workforce numbers will not be met and many of those employed in the industry will not be appropriately skilled.
This concern is exacerbated by the low-unemployment numbers in Australia and government agencies such as the ASD losing cyber-workers to better-paid jobs in the private sector, rather than expanding their ranks of skilled and
experienced cyber-workers.
The news the 2020 Strategy would get an overhaul was broadly welcomed, with senior cyber-industry figures saying it was a chance to fix the shortcomings of the wellintentioned but flawed strategy.
“We welcome a revised plan that focuses on the innovation and economic benefits of growing the cybersecurity sector. Securing information sharing will be a vital part of economic development in the next ten years,” says Daniel Lai, CEO of ASX-listed information security provider archTIS.
“By nurturing the cybersecurity sector now, Australia can take a more active role in a massive restructuring of how we do business in the years to come. To make this happen, we’ll need both the funding and the manpower to properly address the challenge of securing the future.”
But Shadow Minister for Cyber Security and former Chair of the Parliamentary Joint Committee on Intelligence and Security, Senator James Paterson, called on the new Labor Government to fully explain what changes they proposed making.
“If the Albanese government really is tearing up the 2020 cyber security strategy, they should urgently clarify which programs they are axing, which powers they are repealing and which funding they are cutting,” Senator Paterson posted on social media.
“Are they pausing implementation of critical infrastructure reforms? How long will the new strategy take? And what should industry do in the meantime while they go back to the drawing board? The cyber realm has never been more contested. The last thing we need is uncertainty.”
With a cyber-crime reported every eight minutes last financial year in Australia, any revised cyber-strategy is likely to incorporate several Labor election policies, including toughening penalties against bad actors and securing better protections for Australian individuals and entities against malicious cyber-activity.
36 | Australian Cyber Security Magazine
Courtesy of


Australian Cyber Security Magazine | 37 ACSM Search and find all upcoming featured security events Plus many more! www.mysecuritymarketplace.com www.mysecuritymarketplace.com
Australian Government to increase data breach penalties
In the wake of two high-profile data breaches, the Australian Government will this week introduce legislation that exponentially increases the financial penalties entities face for repeated or serious privacy breaches.
On the weekend, Attorney General Mark Dreyfus said he would table the Privacy Legislation Amendment (Enforcement and Other Measures) Bill 2022 in Parliament later this week. The bill would significantly increase the existing maximum AU$2.22 million set down by the Privacy Act 1988.
Under the proposed bill, the penalty will increase to whichever is the greater of an AU$50 million fine; three times the value of any benefit obtained through the misuse of information; or 30% of a company’s adjusted turnover in the relevant period.
“Unfortunately, significant privacy breaches in recent weeks have shown existing safeguards are inadequate. It’s not enough for a penalty for a major data breach to be seen as the cost of doing business,” said the Attorney-General
“We need better laws to regulate how companies manage the huge amount of data they collect, and bigger penalties to incentivise better behaviour.”
The new legislation comes after two big data breaches involving telco Optus and health insurer Medibank Private in which the sensitive data of millions of customers was stolen. Other large entities also experiencing data breaches in the last month include Energy Australia, Telstra, G4S, Costa Group, MyDeal, and Dialog.

In addition to increasing penalties, the Privacy Legislation Amendment (Enforcement and Other Measures) Bill will also hand the Australian Information Commissioner (AIC) greater powers to resolve privacy breaches; strengthen the Notifiable Data Breaches scheme to improve
the information provided to the AIC to better enable it to assess the risk of harm; and give the AIC and the Australian Communications and Media Authority (ACMA) greater information sharing powers.
“When Australians are asked to hand over their personal data, they have a right to expect it will be protected,” said Dreyfus. “I look forward to support from across the Parliament for this Bill.”
Prime Minister Anthony Albanese formally added fighting cybercrime to the Attorney-General’s responsibilities only last week, leaving Cybersecurity Minister Clare O’Neil responsible for cyber policy coordination.
The Government’s move also comes just weeks after the Opposition Attorney-General Julian Lesser called for tougher online privacy and data protection laws. Dreyfus had previously flagged that he intended to make changes to the Privacy Act, something the Opposition had welcomed.
“It should not have taken the cyberattack on Optus to wake up this government,” said Lesser. “The protection of Australians’ personal information online must be a high priority for the Albanese Government.”
Notably, the Opposition’s proposed reforms only increased fines up to AU$10 million, and then only for serious, repeated breaches. However, Opposition Home Affairs Minister, Karen Andrews, has recently upped the ante and called for cyber-extortionists to face prison penalties of up to ten years.
While some insiders ask whether it is fair to fine an entity for falling victim to a cyber-attack, others say the increase in penalties will encourage those entities to focus on cyber-defences and re-evaluate what customer data they retain and for how long. Dreyfus says the government is committed to the ongoing strengthening of privacy laws.
38 | Australian Cyber Security Magazine
Courtesy of
In this episode, we speak with Wilson Ang, a dispute resolution lawyer at Norton Rose Fulbright Singapore and head of the Asia regulatory compliance and investigations practice, as well as Jeremy Lua, a dispute resolution lawyer at Norton Rose Fulbright Singapore focusing on regulatory investigations and compliance.



Wilson focuses on strategic governance issues, including conducting internal investigations on business ethics and anti-corruption matters, often involving the US Foreign Corrupt Practices Act, the UK Bribery Act, and the Singapore Prevention of Corruption Act. Wilson has extensive experience designing and implementing compliance programs, conducting integrity due diligence reviews and handling complex and sensitive issues involving bribery, fraud, sanctions, money laundering/terrorist financing, cyber-security attacks, data breach incidents, competition law and financial services regulatory violations in Asia and beyond. Wilson's practice also involves ESG issues like modern slavery and business human rights due diligence, health and safety matters, environmental regulatory disclosures and corporate governance.

Interview with Wilson Ang Dispute resolution lawyer at Norton Rose Fulbright Singapore and head of the Asia regulatory compliance and investigations practice and Jeremy Lua Dispute resolution lawyer at Norton Rose Fulbright Singapore CYBERSECURITY AND DATA PROTECTION REGULATIONS IN ASIA
FUTURE OF THREAT INTELLIGENCE - ASEAN REGION PANEL SESSION

PANEL DISCUSSION
Edwin Tan
HEAD OF INFORMATION SECURITY ASIA, BANK JULIUS BAER
Nan Maguire
HEAD OF INFORMATION SECURITY, PRIVACY & RESILIENCE, APAC, ABRDN
Christopher Lek DIRECTOR,

CYBER SECURITY NTU
Ken Mizota
APJ CTO RAPID7
These cybersecurity leaders share their take on what can be done to help our industry and staying ahead of threats by leveraging on threat intel.

Key panel discussion points:
• Addressing the current threat landscape
• Unpacking our cyber leaders' current approach in dealing with threats and staying ahead
• Finding out what are our business stakeholders mindset and understanding regarding threat intel
• The evolution of the business needs for threat intelligence and how it's here to stay in the future
• Exploring how our cyber leaders can take others within the business along in this journey
For more information visit the Community Sponsor - Rapid7 - https://www. rapid7.com/
Shamane Tan CHIEF GROWTH OFFICER, SEKURO | PRIVASEC ASIA
Singapore Government Minister calls for multi stakeholder approach to cybersecurity

Singapore’s Minister for Communications and Information has used the opening of the Singapore International Cyber Week (SICW) to call for a multistakeholder approach to global cybersecurity architecture as the rate of cyber-attacks on Singaporean entities continues to rise.

Speaking at the October 18 opening of SICW, Josephine Teo said the Singaporean Government believed cybersecurity was a team effort, saying governments couldn’t solve the problem alone.
“Partnerships among stakeholders – governments, industry, academia – are needed to leverage our collective wisdom and action in the digital domain,” the minister said. “We also believe that this approach helps to minimise the spill-over of geopolitical tensions into the digital domain by keeping open channels of communications and building shared expectations and norms on behaviour.”
SICW is one of Asia-Pacific’s top cybersecurity events. This year, the three-day conference is focusing on cybercapacity building and international partnerships. Other Singapore Government ministers scheduled to speak include Janil Puthucheary, Tan Kiat How, and Coordinating Minister for National Security, Teo Chee Hean.
Australia’s Assistant Minister for Foreign Affairs, Tim Watts, is representing the Australian Government alongside Australia’s Ambassador for Cyber Affairs and Critical Technology, Tobias Feakin.
“I will use this opportunity to deepen Australia’s engagement on cyber resilience with Singapore and with private industry, academia and members of the international community,” said Watts. “Competition for cyber and technology dominance is playing out most acutely in the Indo-Pacific region, which is increasingly vulnerable to technology-enabled coercion.”
Software company Cybereason says the number of
Kaspersky notes that there were 1,817,635 web threats detected and blocked against Singapore-based internet users in the second quarter of 2022, a 17.6% increase on the first quarter of the year.
Ensign InfoSecurity’s Cyber threat landscape 2022 found that Singapore’s technology, media, telco, and transportation sectors were the top targets in 2021, with nearly 70% of malicious traffic that year specifically directed towards telcos. Ensign found a 133% increase in the number of Singapore-based entities mentioned on ransomware leak sites and a rise in the rate of cyber incidents in the city state using stolen login credentials.
However, while the frequency and sophistication of cyberattacks has increased, Kapersky says Singaporean authorities have been proactive in detecting and deterring threats.
Against this background, Teo said in her speech that it was important to hear the perspectives and concerns of all stakeholders. The minister said that bad actors were constantly innovating and developing new tools, techniques, and strategies to target newly discovered vulnerabilities and poorly protected existing vulnerabilities.
“Cyber threats do not respect boundaries, whether physical, geographical or organisational,” she told the audience. “Ultimately, we are all better served by having a strong global cybersecurity architecture that gives our people and businesses the confidence and trust to engage in the digital domain. This means all of us doing our part to help our cyberspace remain open, stable, and interoperable.”
Australian Cyber Security Magazine | 41
cyber-attacks, particularly ransomware attacks against Singaporean entities is outpacing the global average. A recent survey by the company found that 80% of Singapore-based respondents had experienced a ransomware attack within the last two years, compared to a global average of 72%.
Courtesy of
How Asian companies are fighting cybercrime with graph data technology
By Nik Vora, APAC vice president, Neo4j.
Fraud costs ASEAN businesses millions of dollars every year. Cybercrime is a particular issue for the South East Asian region, with 25% of respondents surveyed by PWC reporting an increased risk in cybercrime as a result of COVID-19. In The State of Financial Crime 2022: Key Takeaways for Asia Pacific Firms, the UN Office on Drugs and Crime (UNODC) identified a 600% rise in cybercrimes in the region.
A report by AppsFlyer found that Southeast Asia’s losses accounted for 40 percent of the total estimated fraud losses in the wider region, totalling USD$650 million. The leading method of fraud was bot attacks, with Vietnam experiencing the highest number of attacks, followed by Singapore.

Only recently, Singtel’s Optus subsidiary, which operates Australia’s second-largest mobile network, suffered a significant cyberattack that resulted in a major data breach of customer information among its 10 million subscribers. As well as reputational loss, the telco faces costly compensation claims and has also received milliondollar ransom demands. Singtel also just confirmed that the personal data of 129,000 customers and 23 businesses were obtained in a cyber-attack two years ago in 2020.
Conventional enterprise-grade security and methods for preventing cybercrime are clearly no longer working. Part of the problem is the imbalance between defenders and attackers. Security teams have a much bigger job, protecting against every possible attack and patching
every possible vulnerability. They have many different responsibilities. Attackers have just one focus: finding and exploiting a single weak link.
Lists vs graphs
Cybersecurity teams rely on data from a wide range of sources. Large enterprises have an average of 75 security tools deployed, all of them generating constant alerts and logs. Additionally, many other apps and services also generate relevant log files. Large enterprises generate an estimated 10 to 100 billion events per day. This volume of data is nearly impossible to manage through traditional database analysis.
While defenders are working through a list, attackers think in graphs. Modern systems are complexly interlinked webs where only one node needs to be infected to spread across an entire network quickly and easily. Lists and tables may be good for collecting and processing data, but they miss critical relationships between data points. John Lambert, from Microsoft Threat Intelligence Centre, has observed that: “Defenders think in lists. Attackers think in graphs. As long as this is true, attackers win.”
By taking a graph-based approach to security, organisations can map their complex and interlinked infrastructure and enrich it over time. The power of a graph is that it captures different entities but also the relationships
42 | Australian Cyber Security Magazine
and dependencies between them. This creates a digital twin that can be used to test and run different scenarios.
Proactive cyber defences
The nature of many cyberattacks is that they start at one small point and spread. Containing the infection – corralling off infected devices and disconnecting them – becomes a race against time. With a clear model of all infrastructure, it’s much easier to identify the most important assets and better target security investments.
Suspicious behaviour shows up as patterns, reducing the mean time to detection and enabling infected systems to be isolated. Over time, historic patterns of abnormality can be recognised, potentially heading off threats before they break through.
MITRE, a not-for-profit IT firm that works with US government agencies, needed to find more sophisticated ways to assess security posture and attack response. The problem wasn’t a lack of information, but an inability to bring all the data together into an overall analytic picture.
By building a graph database, MITRE has been able to transform cybersecurity information into knowledge. The model evolves with available data sources and desired analytics. Because it tracks the relationships between entities, it provides context for reacting appropriately to attacks and protecting mission-critical assets.
The security graph also incorporates mission dependencies, showing how objectives, tasks and information all depend on other cyber assets. Intrusion alerts can be correlated to known vulnerability paths, suggesting courses of action. It also makes post-attack forensics easier, revealing vulnerable paths that may warrant deeper investigation.
Cybersecurity is always going to be a cat-and-mouse game, with defences and attack methods both continuing to increase in sophistication. It will likely never be possible to guarantee complete security, which makes using a security to detect breaches more critical if measures to limit the attack are to be taken quickly.

Australian Cyber Security Magazine | 43
The nature of many cyberattacks is that they start at one small point and spread. Containing the infection – corralling off infected devices and disconnecting them – becomes a race against time. With a clear model of all infrastructure, it’s much easier to identify the most important assets and better target security investments.
UK Cyber bosses call for client side scanning to help prevent child abuse
Courtesy of
Two senior figures in the UK Government’s cybersecurity establishment have called for social media platforms and tech companies to adopt client side scanning techniques to help mitigate the sharing of online child sexual abuse material.

The UK’s National Cybersecurity Centre (NCSC) technical director Ian Levy and GCHQ’s director of cryptanalysis Crispin Robinson made the controversial call in a research paper published last week.
The paper, Thoughts on Child Safety on Commodity Platforms, examined various techniques tech companies could use to reduce the sharing of child abuse materials on their platforms where the service provider does not have access to user content.
High on the duo’s mitigation list is client side scanning, where companies design and deploy software onto their platforms that automatically scans images, text, and videos for objectionable content before it is sent.
“We’ve found no reason why client side scanning techniques cannot be implemented safely in many of the situations one will encounter,” the paper says. “That is not to say that more work is not needed, but that there are clear paths to implementation that would seem to have the requisite effectiveness, privacy and security properties.”
The technique has many supporters, including within the tech industry. However, privacy advocates and others have long opposed it, saying that, among other things, it would render end-to-end encryption ineffective.
But Levy and Robinson say the trend toward widespread end-to-end encryption in everyday online messaging poses a real problem for law enforcement, including when trying to prevent child abuse. They say their paper, which does not represent UK Government policy, is designed to provoke discussion and awareness that it is possible to provide strong user safety protections while ensuring that privacy and security are maintained.
Apple’s iOS feature NeuralHash is a high-profile example of a client side scanning technique. Last year the tech giant introduced the feature, which used an algorithm installed on phones to detect the transmission of child abuse images.
One big problem with client side scanning is the miscategorisation of images, which can potentially have devastating real-world consequences for people. NeuralHash caused a storm of protest from privacy groups and tech experts who quickly highlighted the software’s security flaws. Apple has subsequently delayed the widespread rollout of the software on its phones.
Levy and Robinson say a series of checks and balances can overcome many of the previous problems preventing the uptake of client side scanning techniques. But the pair face stiff opposition from some influential voices, including Meta, owner of Facebook and WhatsApp. Meta says such client side scanning techniques would fundamentally undermine the internet, privacy and people’s human rights.
A 2021 Columbia University report, “Bugs in our Pockets: The Risks of Client-Side Scanning”, is more specific when condemning client side scanning. That paper says its use opens the way to causing greater harm than it prevents.
“Client side scanning, by its nature, creates serious security and privacy risks for all society, while the assistance it can provide for law enforcement is at best problematic,” the paper said. “There are multiple ways in which client side scanning can fail, can be evaded and can be abused.”
Levy and Robinson acknowledge the challenges of balancing privacy with preventing the production and transmission of child sexual abuse material. But both men also argue it is solvable and that it is a false binary to argue society cannot achieve the two simultaneously.
“We believe these legitimate privacy concerns can be mitigated technically, and it is likely that the legal and policy challenges are harder, but we believe they are soluble.”
44 | Australian Cyber Security Magazine
We’re still terrible at password management
Although passwords are amongst the most important lines of defence against nefarious cyber-attackers seeking access to online accounts or corporate networks, password health continues to be poor, leaving corporate systems vulnerable to opportunistic attackers.
That’s one of the key findings according to a new research report released today by Rapid7, titled ‘Good Passwords for Bad Bots’. Attackers are simply taking advantage of weak password management to gain access to corporate systems via two of the most popular protocols used for remote administration, Secure Shell (SSH) and Remote Desktop (RDP).
With the increasing adoption of both remote work and cloud infrastructures, the number of people accessing corporate information systems across the internet has skyrocketed. Many of these systems leverage RDP and SSH for interaction and management. As a result, the ‘walled garden’ approach that once allowed companies to secure their perimeters and force employees to work only on corporate networks has faded, and the number of untrusted networks they use to connect from has jumped.
This new report is part of Rapid7’s series of research papers that analyse the behaviour of attackers in a risk-free environment in order to study them, with the findings shared to help prepare organisations for the types of cyberattacks they can expect to see in the real world.
“What we found in this research in many ways confirmed our assumptions that attackers aren’t “cracking” passwords on the internet and that despite the muchpublicised risks and threats, we still collectively stink at password management,” says Tod Beardsley, Director of Research at Rapid7.
For this report, Rapid7 used its network of honeypots (a few hundred of them) to monitor SSH and RDP login attempts. After looking at authentication attempts (as opposed to vulnerability exploit attempts, low-touch scans, etc), Rapid7 found 512,002 unique passwords were attempted to be used by attackers. From here, the researchers turned to the rockyou2021.txt list to determine how many of those passwords existed in this industry-
standard list of exposed passwords.
“Prepare to be shocked: nearly all of them were,” adds Beardsley.
“In fact, we found that just 14 of the passwords being brute-forced into our honeypots were NOT part of the rockyou2021.txt file, and we think those were likely errors as they included a string of the honeypots’ IP addresses in them.”
There are approximately 8.4 billion passwords on the rockyou2021.txt file and Rapid7 found less than half a million in its honeypots. Rapid7 says what’s more likely to happen is attackers still rely on the human connection to security infrastructure, which is notoriously one of the weakest links in the chain.
Social engineering tactics, like phishing for passwords and credential stuffing, are still stronger ways for attackers to gain access to passwords than cracking them automatically,” says Erick Galinkin, Principal Artificial Intelligence Researcher at Rapid7.
“What this tells us in practicality is that it’s not terribly hard to avoid this class of attack. In fact, some of the most attacked credentials were ones that should make any internet-literate person facepalm hard.”
Rapid7 found the three most popular usernames for RDP were “administrator,” “user,” and “admin.”, and the three most common passwords were “root,” “admin,” and “nproc.”
“We’re simply not doing well enough with our passwords, and it just doesn’t need to be that way in this day and age,” adds Galinkin.
“It’s not hard to beat this kind of attack and you don’t even have to have a particularly strong password in order to protect yourself; just one with randomness in it, such as a few arbitrary characters.”
Rapid7 advises customers and members of the public to not reuse a password for multiple logins and to avoid default passwords. The company says all of these problems would be covered by the use of password manager services, which create unique, random passwords for users.
“These services are a strong but sadly underutilised way to have good credential hygiene,” concludes Galinkin.
Australian Cyber Security Magazine | 45
ACSM
Courtesy of
The art of data protection in Formula 1
By Jane Lo, Singapore Correspondent.
400 gigabytes of data is generated per event, quite sizable when it all adds up, “said Douglas Goodridge (Chief Information Officer, Williams Racing), at Acronis #CyberFit Day Singapore 2022 (29th September 2022) as the city geared up for the return of world’s original night race after a 2-year hiatus.
Winding around historic and architectural landmarks by the Marina Bay and the downtown core, the 5.063 kilometers of track, illuminated with almost 1,600 floodlights, was once again transformed into a spectacular sight for the Formula 1 Singapore Airlines Singapore Grand Prix 2022.

Data is King
Tracking the performance of their teams over the race weekend, the fans may appreciate that today’s F1 car is highly instrumented, networked and connected, with hundreds of sensors in each car that generate millions of data points over a race weekend.
But casual observers may not realise that it is a data driven sport where the technological ability to measure, analyse and react on data is crucial to the team’s winning strategy.
There is the “data within the car”, there is the “telemetry information that needs driver inputs”, data about “how the systems in the car are running, such as temperatures,
pressures”, Goodridge said.
These data are captured and analysed real-time in a continuous feedback loop to deliver that fraction of a second advantage in performance over competitors.
Indeed, on race day, while the fans’ attention is riveted on the racetrack action, another battle is playing out behind the scenes.
Here is where engineers and technicians, working with innovative technologies and the team’s race director and headquarters (the “HQ”, for Williams Racing this is Grove, Oxfordshire), race to extract insights from the millions of data points and adjust the race strategy in real-time.
“Data itself is not a new thing, has been going on in F1, and evolving over a period of time. However, we now have huge amounts of data, generated by trackside and back over at HQ”, Goodridge noted.
The quest for perfection continues post-race and during practice runs, up till the race day.
Metrics culled from the chassis, tires and throughout the engines are fed into models and simulations – often said to be as advanced as those used in the Aerospace industry technology.
Combined with historical information, these data are harnessed in predictive models to make design changes to the car before the next race.
Goodridge, pointing out how data is exploited to inform
46 | Australian Cyber Security Magazine
decision making, said: “the important thing is to treat data in a holistic manner.”
“Instead of having an isolated view of say, the car, or the trackside operations, and everything that goes on in the factory, we look at everything as one,” he said.
This is to help understand “how we can leverage the data” and “correlate the data” to “ensure that we have the correct outcome,” he explained.
In this relentless drive to maximise performance, the gigantic amount of data tracked, transmitted, stored and analysed is clearly an important intellectual property.
Securing such a significantly valuable asset is therefore of paramount importance.
While principles to protect the asset (private circuits, encryption, segregation policies, lengthy gardening leave for senior team members to minimise leaks) are standard industry best-practices, the discussions offered insights into practices unique to F1. Here are some highlights.

Cyber threat landscape
Data being such a “crown jewel” for a F1 team is highly attractive to threat actors seeking to exploit any weaknesses in the team’s protection strategy for monetary gains or otherwise.
Indeed, F1 like any other industry, is not immune to say, insider threats. There was the 2007 spygate where a rival team reportedly sought access to a competitor’s data via an insider, or the 2014 Marussia incident where an employee inadvertently visited a malicious website which introduced a trojan into the team’s computer network.
It is also vulnerable to the waves of ransomware attacks that targeted organisations ranging from global multinationals to small medium size enterprises.
When asked about the current cyber threat landscape, Reed said “it is the same, but getting worst.”

Goodridge added, “as you use technology to enable department and sections of the businesses that traditionally were not technologically focused – marketing is one example, social media is another – you are broadening the threat landscape.”
In defending against the increasing threats, Goodridge highlighted the “responsibilities of understanding where your boundaries are.”
Traditional perimeter security and the Zero Trust model
Digitalisation, along with the expanding threat landscape also prompt a “think about perimeter security and the Zero Trust model,” he said.
Today’s explosion of “IoT” devices means that data is increasingly stored, accessed, retrieved, and transmitted remotely – a situation further complicated by the Covid-19 pandemic.
Cyber protection relying on the traditional perimeter security, distinguishing between the “trusted” (inside the perimeter) devices and the “untrusted” (outside), struggles to respond to these challenges.
The Zero Trust model, on the other hand, applies the blanket rule of verifying all devices, including those considered to be inside the trusted perimeter.
Nevertheless, regardless of protection measures, Goodridge stressed the need for “understanding where that data sits, how valuable it is and understanding overall, the threat at risk level.”
Australian Cyber Security Magazine | 47
Continue next page >>
Panel : From Left: Acronis CEO (Patrick Pulvermueller); Acronis CISO (Kevin Reed); Williams Racing CIO (Douglas Goodridge).
Physical security and protection
However, protection is also about physical security, as much as the cyber one.
Typically, a F1 team transports 50 tonnes of equipment – ranging from furniture, panelling to IT and garage equipment, and up to 100 personnel per race, as the team globetrotters to the 22 race locations.

The complex logistics of packing, transporting, and unpacking to set up the team’s home base and garage is a highly tuned plan where each equipment is essential to chasing that incremental boost in speed.
With the latest technological innovations on car design kept under wraps until as late as the flag-off, it is no surprise that physical security is of high priority – as evident from the presence of hundreds of guards – perhaps more so than a typical large entertainment event.
More interestingly, there is the additional consideration of physical protection integral to the overall security.
Goodridge shared that the IT equipment are exposed to variations in temperature and the elements (such as build-up of sand and dust in locations where there are no air-conditioned facilities) as they traverse the world.
Protection of these mobile IT infrastructure against damage, executed in compliance with FIA (Fédération Internationale de l’Automobile) requirements, is another challenge not to be underestimated.
Data recovery and back-ups
With the rising sophistication of threats and the old adage of “no 100% security”, data protection naturally extends to more than proactive defensive measures.
Building in “redundancy” and “resiliency”, according to Pulvermueller, are necessary, and “mean-time-to-restore” is key where back-ups are deployed.
Although these are arguably industry best practices
and data restoration under most circumstances is highly stressful, the time factor in a sport synonymous with speed vastly raises the stakes.
Moreover, while ransomware remains an ever-present threat that can strike on race day, downtime during design and development could also cost the team the vaunted podium finish.
Furthermore, as with all sports, F1 teams have historically used biometric data to monitor athletes’ fitness and performance – the collection and processing of which are set out in the FIA “guidelines for the collection and usage of biometric data in motor sport.”
So, “data retention” and “de-duplication” in back-ups will also need to adhere to FIA’s guidelines (as well as EU’s GDPR), according to Pulvermueller and Reed.
Last words
“Data is the forefront of everything we do, F1 is a data driven sport,” Goodridge said.
“We are learning and evolving forward – that is the key for us to how we need to use data more efficiently in the future,” he added.
But malicious actors are undoubtedly evolving as well. In protecting against the rising sophistication of the adversaries seeking to steal, impair and destroy the crown jewel, “learn from the mistakes of others,” Reed advised.
48 | Australian Cyber Security Magazine
Group: The Singapore Formula 1 2022 Williams Racing garage tour, guided by the Williams racing team.
GLOBAL CYBERSECURITY MEMBERSHIP SERVICES

Interview with Rowland Johnson, President, CREST International.
Rowland focuses on driving initiatives to increase engagement across the 300+ CREST members and all CREST-qualified individuals globally. He is responsible for working internationally with governments, regulators, and other key industry stakeholders to build stronger technical cybersecurity ecosystems. He was instrumental in CREST’s international growth and integral in creating CREST chapters in Singapore, the USA and Hong Kong.
Rowland was a founding director of cybersecurity company Nettitude and oversaw its acquisition by Lloyd’s Register in 2018. Following the acquisition, he worked with the leadership team as a strategic advisor focusing on global growth.
Rowland works closely with international governments and regulators to increase capability, capacity, collaboration, and consistency in cybersecurity ecosystems.


President,
International.
INTERVIEW WITH Rowland Johnson
CREST


ENGAGE WITH LEADING INDUSTRY BRANDS Access exclusive and curated content from the startups to the top brands: Products, resources, events, webinars, updates, interviews & podcasts. THE HUB PROMOTE YOUR BRAND REGISTER FOR ACCESS www.mysecuritymarketplace.com THE HUB Everything about your favorite companies in one convenient place. CHECKOUT THELATEST PRODUCTS























 speak with Niel Pandya, Chief Technology Officer with Micro Focus and joined by special guest, Cole Cornford, CEO & FOunder of Galah Cyber.
speak with Niel Pandya, Chief Technology Officer with Micro Focus and joined by special guest, Cole Cornford, CEO & FOunder of Galah Cyber.
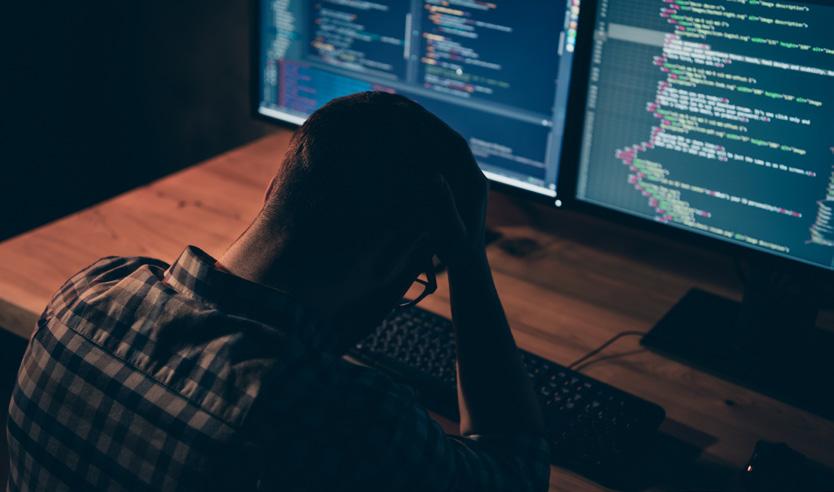


















 By Sarah Sloan Head of Government Affairs and Public Policy, ANZ.
By Sarah Sloan Head of Government Affairs and Public Policy, ANZ.