CYLAB YEAR IN REVIEW



2021–2022
LETTER FROM THE DIRECTOR

DEAR FRIENDS
We had a busy year in CyLab as we undertook, for the first time in our almost-19-year history, a comprehensive self-study and external review. CyLab faculty, staff, and students contributed their thoughts to the self-study, identifying our accomplishments and impact as well as our challenges and opportunities. Our eight-member external review panel visited us right after graduation and spent two days meeting with small groups of CyLab community members as well as university leadership. Now we are discussing the insights from our self-study and recommendations from the review panel and working towards ways to continue to increase our impact. My hope is that we will soon develop a strategy for strategic growth that will include a plan for expanding our space and building our endowment, enabling us to work with the academic departments to hire more security and privacy faculty in targeted areas.
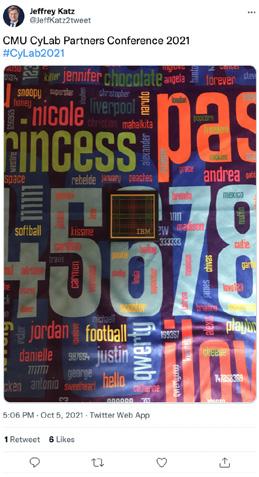
CyLab faculty and students were well represented at conferences this past summer, with multiple papers presented at USENIX Security (including two distinguished paper awards), the Symposium on Usable Privacy and Security (including the IAPP SOUPS privacy award), the Privacy Enhancing Technologies Symposium, and the ACM CHI conference (including an honorable mention). In addition to presenting our research, a team of CyLab students and alumni won the DEF CON Capture the Flag competition for the sixth time. Our CyLab partners team had a great year, increasing our number of partners and sponsors to an all-time high of 34. We said goodbye to two members, each taking on exciting opportunities, and welcomed two new members to the team. The partners team worked with our partners and faculty to launch our Future Enterprise Security Initiative and Secure Blockchain Initiative. In addition, our partners team has been working with our CyLab-Africa Security and Privacy Initiative, which will host the CyLab-Africa Summit on Digital Public Goods in October. Our CyLab partners conference will be back in person this October and I’m hoping to see many of you there. I’m also looking forward to celebrating our 20th anniversary with you next year!
On a personal note, the little free time I had this year was filled with gardening, pickup soccer, bass flute, and sewing. While the Pittsburgh urban wildlife decimated my cilantro, spinach, and corn, I harvested a bumper crop of tomatillos and basil. I expanded my homemade dress collection to include several research-themed dresses: soup (for the Symposium On Usable Privacy and Security), cups (for the CyLab Usable Privacy and Security Laboratory), and eyes (for privacy or the lack thereof).
It was great to have people back in CyLab this year and to welcome lots of undergraduate researchers to CyLab this summer. I am especially enjoying lively in-person research discussions with my students and colleagues!


 Director and Bosch Distinguished Professor in Security and Privacy Technologies, CyLab FORE Systems Professor of Computer Science and of Engineering & Public Policy
Director and Bosch Distinguished Professor in Security and Privacy Technologies, CyLab FORE Systems Professor of Computer Science and of Engineering & Public Policy
4
Here’s a System to Guarantee Smart Home Privacy
Many internet-connected devices—smart speakers for example—share data to the cloud when you interact with them. How do you know your speaker isn’t always listening? How do you know it’s not sharing more information than is necessary to fulfill your request?

5
Rotem Guttman’s Cyber Forensics Course is an Immersive Experience
The course earned Guttman a CMU Andy Award for “innovative and creative contributions.”
7
CyLab researchers investigate Apple’s privacy labels
Roughly a year after Apple rolled out its privacy label requirements, CyLab researchers have gained a comprehensive look at the state of iOS privacy labels.
11
“Adulting” for cybersecurity, GANs, and more: CyLab’s 2022 seed funding awardees
Over $400K in seed funding has been awarded to 18 differ ent faculty and staff across seven departments at Carnegie Mellon to support security and privacy research. Funding was awarded based on projects’ intellectual merit, original ity, fit towards CyLab’s priorities, and potential impact.
Cookie Consent Notices are Actually Unusable, According to Science
CyLab Seminar Series
Towards Having Your Privacy and Security and Exchanging Crypto Too
Over 18,000 People Hacked Their Way Through picoCTF 2022
Building Cybersecurity Talent
Carnegie Mellon’s Hacking Team Wins DEF CON CTF
2022 CyLab Presidential Fellows
Security and Privacy Degree Programs Offered at CMU
CyLab Executive Education Offerings
2022 CyLab Distinguished Alumni Award
CyLab Core Faculty
CYLAB 2021-22 YEAR IN REVIEW | 3
CONTENTS
9
10
12
13
16
17
18
19
20
22
23
24
27 Featured
28
29
30
31
32
35
8
CyLab Staff
Featured Speaking Engagements by Faculty
Grants Received by Faculty
Featured CyLab Recognitions
Graduated CyLab Ph.D. Students
Partners Shaping a Safer Future
CyLab Partners Conference
CyLab News Briefs
CyLab Media Mentions
PEEKABOO! HERE’S A SYSTEM TO GUARANTEE SMART HOME PRIVACY
Many internet-connected devices—let’s use smart speakers as an example—share data to the cloud when you interact with them. How do you know your speaker isn’t always listening? How do you know it’s not sharing more information than is necessary to fulfill your request?
There’s currently no way to check, but CyLab researchers are close to a solution.
“People are concerned that their devices are capturing and sharing too much data,” says CyLab’s Haojian Jin, graduate of the Human Computer Interaction Institute’s Ph.D. program. “Companies want to tell users that they only collect certain pieces of information, but they currently have no way to actually prove it.”
Introducing: Peekaboo!
Jin and a team of researchers have developed a new privacy-sensitive architecture for developers to build smart home apps, which the team refers to as “Peekaboo.” The system takes requests from developers to share certain pieces of data and ensures only the essential pieces of data to fulfill their request are shared with them.

The system, described in a paper titled, “Peekaboo: A Hub-Based Approach to Enable Transparency in Data Processing within Smart Homes,” was presented at the IEEE Symposium on Security and Privacy in June 2022. “In the privacy world, we have a principle called ‘data minimization,’” says Jin. “The companies that collect the data should only be collecting the minimum amount of data to fulfill their objectives.”
This concept is even written into the EU’s General Data Protection Regulation (GDPR), Jin points out. Article 5 (1) (c) of the GDPR reads, “Personal data shall be limited to what is necessary in relation to the purposes for which they are processed.”
Under the Peekaboo architecture, developers first declare all the data they intend to collect and under what conditions, where that data is being sent, and the granularity of the data itself—for example, whether they’d like to collect the number of hours watched on a smart TV per week, per month, per quarter, etc. Then, an in-home hub mediates between all devices in the home and the outside Internet.
“The hub enforces the sharing of only data declared by the developer,” says Jin. “And users and third-party auditors can inspect the incoming data requests as well as the outgoing data flows.”
Giving users more control of their privacy in smart homes
The essence of the Peekaboo architecture, Jin says, is that users can have more control over their data. If a developer sends in a request to collect a piece of information—let’s pretend they want to know the number of hours of spent watching a smart TV in a single day— the user can modify the request on the hub to only share the number of hours spent watching their smart TV over a whole month, if they’re more comfortable with that.
In addition, Peekaboo in the future could help make privacy nutrition labels—which are now being deployed by both Apple and Google—more accurate. Right now, there is no way to enforce and verify that apps are behaving consistently with their privacy nutrition labels,
4 4
“People are concerned that their devices are capturing and sharing too much data. Companies want to tell users that they only collect certain pieces of information, but they currently have no way to actually prove it.”
Haojian Jin, Ph.D. student in the Human-Computer Interaction Institute, CyLab
which are produced manually by developers and have been found to be inaccurate at times. But since Peekaboo both enforces and verifies data sharing in accordance with developers’ requests, privacy nutrition labels could be automatically generated and updated to accurately portray data collection and use.
Lastly, as the Internet of Things continues to grow and people accumulate hundreds of IoT devices in their homes, Peekaboo can help manage the smart home holistically.

“The Peekaboo protocol will allow users to manage privacy preferences for all of their devices in a centralized manner through the hub,” Jin says. “Imagine not just a privacy nutrition label for an individual device, but a privacy nutrition label for an entire home.”
This work was funded in part by Cisco, Infineon, the National Science Foundation, and CyLab’s Secure and Private IoT Initiative.
GUTTMAN’S CYBER FORENSICS COURSE IS AN IMMERSIVE EXPERIENCE
ROTEM

The Ambrosian national government was the victim of a crippling cyberattack, sending government officials into a frenzy to get their systems back online and figure out how their network was penetrated. Graduate students in Carnegie Mellon’s Information Networking Institute (INI) have been recruited to help solve the case.
If the country of Ambrosia sounds made up, it’s because it is. INI students in Rotem Guttman’s “Cyber Forensics and Incident Response” capstone course are thrown into this fictional world to figure out what exactly happened in the cyberattack, and how.
“By the end of the course, I want my students to be able to say that they are experienced in building a cyber incident case,” says Guttman, a researcher at the Software Engineering Institute and faculty at the INI who teaches the course. “If there’s a cyber incident on their first day of work, I don’t want the deer-in-headlights
reaction. I want them to be like, ‘Yeah, I’ve got this.’”
Guttman has been teaching the course since 2015, but it wasn’t until the COVID-19 pandemic sent students home to learn remotely that the course rapidly evolved into its
CYLAB 2021-22 YEAR IN REVIEW | 5
CyLab researchers have developed a new privacy-sensitive architecture for developers to build smart home apps.
“Imagine not just a privacy nutrition label for an individual device, but a privacy nutrition label for an entire home.”
Haojian Jin, Ph.D. student in the Human-Computer Interaction Institute, CyLab
Rotem Guttman playing a character related to the cyber incident that students in his course are tasked with solving.
The course earned Guttman a CMU Andy Award for “innovative and creative contributions.”
current form. Previously, most of the course was taught in a traditional lecture-based style. Once remote learning became the new normal, Guttman swiftly adapted.
“I know from my research what works teaching-wise, but I’ve never had the freedom to just go wild,” Guttman says. “When the COVID shutdown began, everyone was asking, ‘How do we make this transition?’ I was like, ‘I’ve got ideas.’”
The idea: immerse the students into a highly-realistic scenario where they must, over the course of a single semester, conduct a formal forensic investigation on a fictional cyber incident, build a case, and present it to a panel of judges. Thus, students were thrust into the Republic of Ambrosia, where the national government tasked them with investigating a massive data breach.
Throughout the investigation, student teams regularly met with a cast of characters related to the incident over Zoom, all played by Guttman himself. The teams asked questions and requested various data that might serve as helpful evidence in their case.
Guttman says that everything in the course ties back to its specific learning objectives, the main one being to “give students the opportunity to actualize the technical skills they have acquired during the prerequisite courses in such a way that they can utilize them in the real world,” according to the course syllabus. Other valuable lessons are sprinkled into the course as
Guttman says that the final grade students receive is based on the students’ work and how it fulfills the learning objectives, not on whether they convicted or acquitted the right people.
“One of the things we’re trying to evaluate them on is: how well can you express yourself? How well can you convey material?” Guttman says. “Communication is so important.”
Crucial to the execution of this highly-realistic immersive experience, Guttman says, was having real-life network data from an actual cyberattack for students to be able to analyze in search of clues and evidence. Without that data, the realism of the investigation would have been missing and students wouldn’t have been able to practice on and analyze real, actual data. To pull it off, Guttman launched an attack on a cluster of servers that his SEI colleague Will Nichols had assembled.
“This course would not have been possible without Will,” says Guttman.
Nichols says that the “garbage cluster,” a nickname both he and Guttman use, is the culmination of a multi-year long process involving the Lion Surplus store at Penn State, which sells non-functioning servers and other parts “for basically scrap value.” He’d look for additional deals online.
Rotem Guttman, Professor, Information Networking Institute, CyLab
well, some of which might be commonly classified as “things they don’t teach you in school.” But Guttman does.
“When I’m role playing as the vice president, I’m acting as one of the worst bosses you’re ever going to have,” Guttman says. “Everyone has a bad boss at some point in their careers, and you need to know how to deal with that and protect yourself.”
At the end of the semester, teams presented their cases to a panel of CTOs, CEOs, and other industry professionals that Guttman brought in to be guest judges.
“This report was the exact type of report—same requirements—as if they were literally submitting it in a civil trial in the United States,” Guttman says. “And now they get to present that work in front of the same people they’re going to be looking for jobs from.”
The result is a server cluster with around one-third of a terabyte of RAM and 128 cores. For comparison, the laptop used to write this story has 16 GB of RAM, twenty thousand times less than the “garbage cluster.”
“The total amount I’ve put into this cluster is about $1,800 after all is said and done, which I think is pretty good,” says Nichols. “I think the going rate right now to build a cluster like this, new, would be around $100,000.”
Thanks to the success of the course, Guttman says that the INI has invested in significant infrastructure upgrades so future instances of the course will be hosted on new equipment on a CMU-hosted datacenter. On top of that, the course itself garnered lots of attention from the University. In December 2021, Guttman received an Andy Award for “innovative and creative contributions.”
“The course is the outcome of a decade of my research combined with Will’s ability to make infrastructure materialize out of nothing,” says Guttman.
6
“When I’m role playing as the vice president, I’m acting as one of the worst bosses you’re ever going to have.”
“If there’s a cyber incident on their first day of work, I don’t want the deer-in-headlights reaction.”
Rotem Guttman, Professor, Information Networking Institute, CyLab
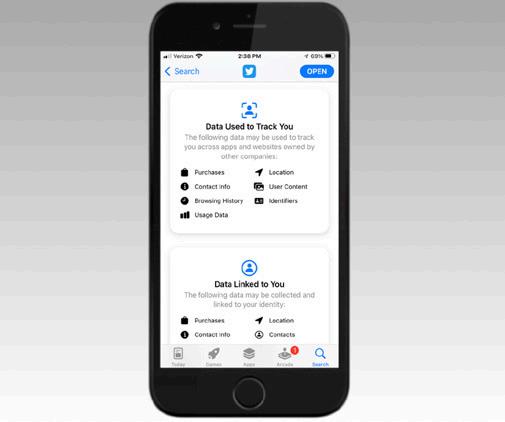
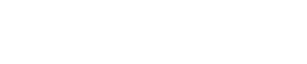
CYLAB RESEARCHERS INVESTIGATE APPLE’S PRIVACY LABELS
“Naturally we had a lot of questions,” says CyLab director Lorrie Cranor, a professor in the Software and Societal Systems and Engineering and Public Policy departments, and the principal investigator of early privacy label research at Carnegie Mellon. “Are the labels conveying accurate information? How easy is it for app developers to make the labels? How well are users able to navigate and interpret them?”
Over the past year, CyLab faculty and students presented new research at the ACM CHI Conference on Human Factors in Computing Systems and the Privacy Enhancing Technologies Symposium (SOUPS) aimed at answering those questions.
Apple introduced privacy “nutrition labels” for apps in its app store in 2020.
in Heinz College’s Master of Information Systems Management program and the lead author on the study.
The researchers crawled the Apple’s US app store every week from April to November 2021, capturing information on privacy labels and metadata for over 1.4 million total apps. Apps that were originally published before December 8, 2020 (just under 1.2 million apps) were not required to create privacy labels unless they release app updates but could voluntarily do so, and apps developed after that date (roughly 275 thousand apps) were forced to do so.
Compliance to create the labels has been so-so.
A close look at compliance and accuracy
In the first paper presented at the ACM CHI Conference on Human Factors in Computing Systems, titled, “Understanding iOS Privacy Nutrition Labels: An Exploratory Large-Scale Analysis of App Store Data,” CyLab researchers examined comprehensive measurements of Apple privacy nutrition labels to learn about the rate of compliance in creating the labels and how accurate existing labels are.
“No one has conducted a large-scale analysis of Apple privacy labels like this before,” says Yucheng Li, a student
“Over half of all apps in the app store still do not have a privacy label,” says Li. “Although the overall compliance rate seems to be steadily increasing, the speed of compliance on older apps is on a downward trend. We speculate that if old apps don’t have a privacy label now, they probably won’t create one in the future.”
The researchers also found that app updates seem to be an important driver of privacy label creation, as 64 percent of the apps released version updates at the same time as they published their privacy label. Lastly, they found that out of the apps that created a label, 43 percent have made at least one update, but under six percent
Continued on page 14
CYLAB 2021-22 YEAR IN REVIEW | 7
CyLab researchers have been studying privacy nutrition labels for over a decade, so when Apple introduced privacy labels in their app store over a year ago, researchers were eager to investi gate them.
“No one has conducted a largescale analysis of Apple privacy labels like this before.”
Yucheng Li, M.S. student, Heinz College
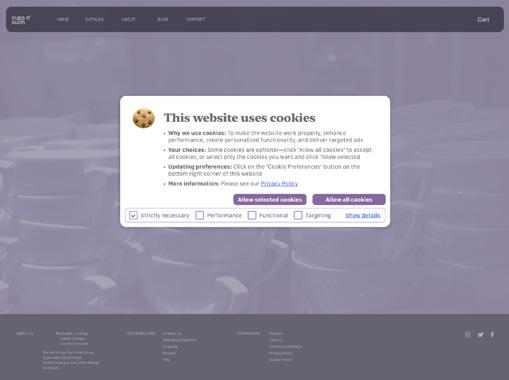
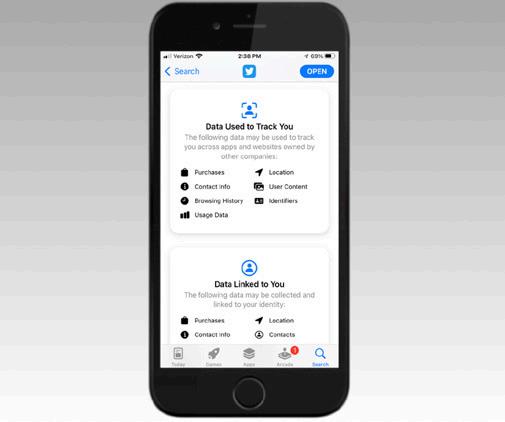
Though your eyes may not notice it before clicking that button, there’s another, perhaps smaller and less bold button that reads, “Cookie settings.” Clicking that button often gives you the ability to customize which cookies you’d like to accept, but only if you click it first.

“A common reaction is to dismiss the interface as quickly as possible,” says CyLab’s Hana Habib, a postdoctoral researcher. “This suggests that these interfaces have usability problems.”
Habib presented a new study titled, “‘Okay, whatever’: An Evaluation of Cookie Consent Interfaces,” at the ACM CHI conference in New Orleans.

In the study, Habib and her co-authors reviewed 191 cookie consent banners from five consent management platforms and used them to identify common design parameters. They then developed 12 different cookie consent banners spanning a range of usability from what they believed to be “best practices” to “worst practices.”
Seven different aspects of usability in cookie consent interfaces the team considered were:

• Whether the choice interface meets user needs
• The ability and effort required to use the choice interface
• Awareness of the interface and available choices
• Comprehension of choices
• Users’ sentiments towards the interface
• Their ability to reverse or change their decisions
• The presence of dark or nudging patterns
The researchers asked over 1,300 user study participants to complete a shopping task on a website prototype, during which they were exposed to one of the 12 consent interface designs the researchers developed. After completing the task, participants were asked to fill out a survey about their experience.
“We observed that some of the design parameters we explored had a significant impact on one or more usability aspects, while others did not have much impact,” Habib says.
The researchers found that if a consent interface wasn’t prominent enough, users exhibited poor awareness of available choices, measured by the post shopping task survey. Zero participants who were exposed to the interface in which a “Cookie Preferences” button was displayed in the bottom-right corner of the browser window actually interacted with the button at all.
Zero study participants who were exposed to this interface actually interacted with the “Cookie Preferences” button at all.
8
COOKIE CONSENT NOTICES ARE ACTUALLY UNUSABLE, ACCORDING TO SCIENCE
“ACCEPT ALL COOKIES,” reads a bright, shiny button on a lot of websites you visit these days.
“A common reaction is to dismiss the interface as quickly as possible.”
Hana Habib, postdoctoral researcher, CyLab
“Compared to those in best practices, participants were significantly less aware that there was a privacy decision on the website, and were less aware of available cookie options,” says Habib.
Related to user sentiment, the researchers found that the absence of inline options in the initial screen of the interface led to lower investment in decision making. Participants presented with this consent design, where options were available through a link embedded in the text, were more likely to report choosing the easiest option.
2021-2022 CYLAB SEMINAR SERIES
October 11, 2021
Eleanor Birrell
Associate Professor, Pomona College, Visiting Professor, CyLab Prospect-driven Security and Privacy




October 25, 2021
Emma Dauterman
Ph.D. Student, UC Berkeley
Snoopy: Surpassing the Scalability Bottleneck of Oblivious Storage
November 15, 2021
Tara Whalen
Privacy Research Engineering Lead, Cloudflare
Let the Right One In: A Better CAPTCHA Alternative
March 14, 2022
Neil Gong Assistant Professor, Duke University Secure Federated Learning

April 4, 2022

Noopur Davis
This “best practices” cookie consent design gives users the ability to make specific consent decisions immediately and meets several design objectives.
The researchers suggest that browser-based consent management mechanisms, including browser extensions that could automatically communicate users’ preferences, have the potential to alleviate some of the burden users face with cookie consent interfaces. However, they argue that until these mechanisms become widely adopted, it remains important to improve the usability of existing schemes.
Habib’s co-authors included CyLab director Lorrie Cranor and two undergraduate students who participated in CMU’s Research Experience for Undergraduates in Software Engineering (REUSE) program in Summer 2021.
Executive Vice President / Chief Information Security and Product Privacy Officer, Comcast Corporation and Comcast Cable
Comcast’s Secure Development Lifecycle (SDL): Building in Strong Cybersecurity
April 21, 2022
Steve Hanna

Distinguished Engineer, Infineon Technologies
The Matter Standard - Raising the Bar for Smart Home Security and Privacy
May 2, 2022
Tim Roughgarden
Professor, Columbia University
The Long Arm of Theoretical Computer Science: A Case Study in Blockchains/Web3
CYLAB 2021-22 YEAR IN REVIEW | 9
Privacy and security and control of those things are paramount in the world of cryptocurrencies.
“The whole cryptocurrency decentralized business is about giving control of the digital coins to you,” says Aravinda Thyagarajan, a postdoctoral researcher in the Computer Science Department advised by CyLab’s Elaine Shi. “You should control your coins, and you don’t want to leak any information about them.”
Thyagarajan presented the new paper, “Universal Atomic Swaps: Secure Exchange of Coins Across All Blockchains,” at the 2022 IEE Symposium on Security and Privacy, outlining a new protocol towards better privacy and security protections when swapping cryptocurrencies.

Right now, if two people or entities want to swap one cryptocurrency for another—say, one Bitcoin for one Ethereum—they can swap directly between themselves, but there’s always a chance one of the two parties will be dishonest and not hold up their end of the deal. Another option, then, is to have a third-party exchange service mediate the deal. But what if the exchange service is an adversary and steals both parties’ coins?
“In the wild west of cryptocurrency, no one should be trusted,” says Thyagarajan.
There’s also an issue of privacy. If an e-commerce website only accepts one specific cryptocurrency, and you only have coins in a different cryptocurrency, you must perform an exchange into the compatible currency before purchasing from the website. That exchange can reveal sensitive information.
“You lose a bit of your privacy,” says Thyagarajan. “Using sophisticated mechanisms, people can learn to some probability information about your assets.”
Thyagarajan’s paper outlines a protocol that addresses these security and privacy concerns. First, the protocol
is universal—it allows for exchanges across all current and future cryptocurrencies. Second, the swap protocol ensures that the swap will happen honestly or it won’t happen at all, meaning no one will maliciously lose coins, without relying on third parties. And lastly, the protocol supports the exchange of multiple types of coins—e.g. Bitcoin, Ethereum, Dogecoin, etc.—in a single swap.
“With this protocol, you can shop on that e-commerce website using a coin that is not the coin that they accept, and keep your privacy,” says Thyagarajan. “You’re able to do that because you’re not relying on third-party services, and also because it doesn’t rely on any special features of the underlying currency.”
All of this requires an enormous amount of computing power, Thyagarajan says, so one currently can’t do this on a laptop or phone, presenting an opportunity for future work. However, for current major currencies, like Bitcoin, Ethereum, etc., Thyagarajan’s paper presents an efficient solution for the exchange that can be run now even on low-end devices.
10
TOWARDS HAVING YOUR PRIVACY AND SECURITY AND EXCHANGING CRYPTO TOO
“You should control your coins, and you don’t want to leak any information about them.”
Aravinda Thyagarajan, Postdoctoral researcher, Computer Science Department
“In the wild west of cryptocurrency, no one should be trusted.”
Aravinda Thyagarajan, Postdoctoral researcher, Computer Science Department
“ADULTING” FOR CYBERSECURITY, GANS, AND MORE: CYLAB’S 2022 SEED FUNDING AWARDEES
Funding was awarded based on projects’ intellectual merit, originality, fit towards CyLab’s priorities, and potential impact.
“We’re excited to be able to support security and privacy researchers across a range of disciplines,” says CyLab director Lorrie Cranor. “The projects we are supporting this year are representative of the diverse research found in CyLab.”
The awards selection committee, made up of CyLabaffiliated faculty and representatives from partner organizations, prioritized the following aspects in no particular order when making their selections:
• Collaboration between CyLab faculty in multiple departments
• Projects led by or having significant involvement of junior faculty
• Seed projects that are good candidates for follow-on funding from government or industry sources
• Projects that are making good progress but reaching the end of their previous funding and need funding to finish or to continue the project until other sources of funding are obtained
• Efforts to transition research to practice, e.g. by preparing software for release as open source projects, conducting field trials, or deploying research results in real-world applications
• Projects that can get started quickly and make significant progress with a small amount of funding
• Non-traditional projects that may be difficult to fund through other sources
• Education or outreach projects aimed at broadening participation in the security and privacy field Recipients of the awards are required to submit brief quarterly reports outlining the progress of the project and present a talk or poster at the annual CyLab Partners Conference this Fall.
This year’s project titles and affiliated faculty are listed on the right.
Combining Program Synthesis and GANs for Automatic Test Case Generation
• Giulia Fanti, Assistant Professor, Electrical and Computer Engineering (ECE)
• Limin Jia, Associate Research Professor, ECE Automatically Identifying Security Property Violations in Protocol Implementations
• Limin Jia, Associate Research Professor, ECE
• Corina Pasareanu, Principal Systems Scientist, CyLab Towards Achieving Secure and Private Distributed Computing: Random K-out Graphs to the Rescue
• Osman Yagan, Associate Research Professor, ECE Towards an Extensible, Automatically Tailored, and Optimized Compiler for Secure Multi-Party Computation
• Wenting Zheng, Assistant Professor, Computer Science Department (CSD)
Zero Knowledge Proof Taxation
• Bryan Routledge, Associate Professor of Finance, Tepper School of Business
• Ariel Zetlin-Jones, Associate Professor of Economics, Tepper School of Business Privacy-preserving computational cameras
• Lujo Bauer, Professor, CMU-Africa, ECE, and Software and Societal Systems (S3D)
• Aswin Sankaranarayanan, Associate Professor, ECE Standing the Test of Time: Long Term Economic Impact of Privacy Regulation
• Alessandro Acquisti, Professor, Heinz College
• Ryan Steed, Ph.D. student, Heinz College Assuring safety and resilience in affordable IoT systems
• Yorie Nakahira, Assistant Professor, ECE
• Anthony Rowe, Professor, ECE Thirty-Day Adulting Challenge for Cybersecurity
• Laura Dabbish, Associate Professor, Human-Computer Interaction Institute (HCII)

• Jason Hong, Professor, HCII Beyond Local Pseudo-random Generators with applications to Program Obfuscation
• Pravesh Kothari, Assistant Professor, CSD
• Aayush Jain, Assistant Professor, CSD A Secure Speculative Execution Abstraction Across Hardware and Software
• Dimitrios Skarlatos, Assistant Professor, CSD
CYLAB 2021-22 YEAR IN REVIEW | 11
Over $400K in seed funding has been awarded to 18 different faculty and staff across seven departments at Carnegie Mellon to support security and privacy research.
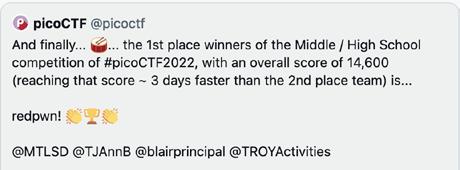
OVER 18,000 PEOPLE HACKED THEIR WAY THROUGH PICOCTF 2022
Companies everywhere are struggling to fill cybersecurity jobs as the industry faces a severe talent shortage. The good news is, more than 18,000 people participated in Carnegie Mellon University’s annual cybersecurity competition—including more than 6,000 middle and high school students.
“Our goal has always been to attract more young people to cybersecurity,” says CyLab’s Hanan Hibshi, an assistant teaching professor in the Information Networking Institute and a faculty advisor for picoCTF, the annual cybersecurity competition and year-round education platform. “The countless headlines we’re seeing about the latest data breach or cyberattack stem from an inadequate pipeline of talent into the field. Our hope is that many of these students will go on to pursue a career in cybersecurity.”

their own residents by sponsoring picoCTF and hosting their own country-specific leaderboards during the competition, including Canada, Japan, and for the first time ever, Africa.
Team “redpwn” took the top spot in this year’s US middle/high school competition, with its five members located all over the US, and team Thinker28 took the top prize in the middle school competition.

Teams “redpwn” and “b1c_waves” both finished with the maximum number of points, but “redpwn” was named the official 1st place winner because they reached that maximum number of points roughly three days faster than “b1c_waves.”
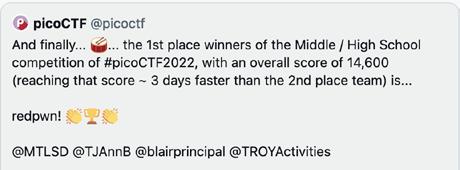
The top US middle and high school teams were awarded cash prizes and were invited to attend picoCTF’s 2022 awards ceremony in August.

Over a two-week period starting March 15, participants of picoCTF worked through 68 challenges that started out relatively easy, and gradually increased in difficulty. If participants found themselves stumped, they could access hints that nudged them towards the solution.
Many of the challenges were written by members of Carnegie Mellon’s internationally acclaimed competitive hacking team, the Plaid Parliament of Pwning. The team has won the so-called “Superbowl of Hacking”—DefCon’s Capture the Flag competition six times in the past ten years.
While many participants were from the United States, this year more than 11,000 participants were international, indicative of picoCTF’s efforts toward a more global reach. Several countries have leveraged CyLab’s competition for
12
“Our goal has always been to attract more young people to cybersecurity.”
Hanan Hibshi, Assistant teaching professor, Information Networking Institute
BUILDING CYBERSECURITY TALENT
The digital future of Africa depends on contextaware security and privacy solutions, trusted technology, and strong cybersecurity talent. CMU-Africa and CyLab-Africa are dedicated to addressing these challenges and creating a more resilient African cyberspace.
In March, CyLab-Africa held the first-ever picoCTFAfrica cybersecurity competition in order to excite young Africans to pursue a career in the field of cybersecurity. Participants of picoCTF-Africa were ranked on an Africanonly leaderboard within CyLab’s larger, annual picoCTF competition.
“We are proud that we had almost 1,000 African students participate in the first picoCTF-Africa,” says Assane Gueye, co-director of CyLab-Africa. “Their performance was impressive and globally competitive. The team leading the African scoreboard was also in the top 60 teams globally.”
The free event encouraged students from all over Africa to create virtual teams, practice skills, and compete. CyLab-Africa, in partnership with CMU-Africa’s Women in Tech club, also held frequent training and information sessions to prepare students for the event.

Over a two-week period, participants worked through 68 challenges that started out relatively easy, and gradually increased in difficulty. If participants found themselves stumped, they could access hints that nudged them towards the solution.
Many of the challenges were written by members of Carnegie Mellon’s internationally acclaimed competitive hacking team, the Plaid Parliament of Pwning. The team has won the so-called “Superbowl of Hacking”—DefCon’s Capture the Flag competition six times in the past ten years.
Prizes were awarded to first, second, and third-place teams in both the high school and college categories. A “Women in Cybersecurity Award” was presented to a winning team to celebrate Africa’s female hackers. In addition, CyLab-Africa partnered with several countries (including Rwanda, Sierra Leone, Burkina Faso, and Uganda) to award country-specific prizes to eligible teams.
Continued on page 14
Gueye, co-director of CyLab-Africa

CYLAB 2021-22 YEAR IN REVIEW | 13
Almost 1,000 students participate in first-ever picoCTF-Africa.
Co-Director of CyLab-Africa Assane Gueye presents at the picoCTF-Africa awards ceremony.
“We are proud that we had almost 1,000 African students participate in the first picoCTF-Africa.”
Assane
Team Ov3rfl0w is recognized as the top high school team during picoCTF-Africa’s 2022 award ceremony.

Continued from page 13
Although this was the first year for picoCTF-Africa, CyLab has been running picoCTF for over a decade. It has become the world’s largest online hacking competition, with over 18,000 people participating this year.
“Our goal for picoCTF-Africa 2023 is to get every country in Africa to take an active role in encouraging young learners to challenge themselves in CTFs and building cybersecurity capacity in Africa,” says Gueye.
Congratulations to the picoCTF-Africa 2022 winners
AFRICA-ONLY LEADERBOARD
• Ph0n1x
• Localmen
• Sol0HIGH SCHOOL AWARDS
• Ov3rfl0w
• W4RH34D
• k4r4
WOMEN IN CYBERSECURITY
• Ov3rfl0w
SIERRA-LEONE-ONLY LEADERBOARD
• Fourah Bay College
• Njala University
BURKINA FASO-ONLY LEADERBOARD
• tedious_crusaders
• greyhat
UGANDA-ONLY LEADERBOARD
• Mak_Team
• Reconaisence_red_team
RWANDA-ONLY LEADERBOARD
• Ov3rfl0w
• W4RH34D
Continued from page 7
made an update to the label. This means the current privacy label may not reflect the most up to date information.
Challenges faced by developers
A second paper presented at the conference, titled, “Understanding Challenges for Developers to Create Accurate Privacy Nutrition Labels”—which earned an Honorable Mention recognition from the conference organizers—identified some key challenges for developers to create privacy labels, which may explain some of the findings of Li’s paper.
“If the labels are not accurate, they will probably do more harm than good to users,” says Tianshi Li, a Ph.D. student in the Human-Computer Interaction Institute and lead author of the study. “We currently have little understanding of developers’ ability to create privacy nutrition labels.”
The researchers observed 12 iOS developers create privacy labels using a replica of Apple’s developer tool, and then followed up with an interview, asking them about their apps’ data practices and the developers’ understanding about the terms in their privacy labels.
“Developers generally felt positive about privacy nutrition labels,” says Li. “But despite those positive reactions, errors and misunderstandings were still prevalent.”
Nine out of the 12 developers made errors in the label that weren’t corrected before being prompted by the interviewer. Among eight apps that already had a privacy label, six were re-created inconsistently.
Other challenges developers faced included limitations of Apple’s documentation about creating privacy labels— some developers reported being confused by jargon used in the documentation while others complained the documentation used vague, ambiguous terms or provided ineffective examples—and information overload.
“Developers complained that they had to read a lot of text,” says Li. “This information overload could have further implications than just the time spent on the task of creating labels.”
One developer, for example, admitted that they might not always update their privacy labels in a timely manner because “upgrading it, or at least reviewing it on every update would be tiresome.”
The researchers argue that in order for privacy labels to achieve more widespread adoption, there needs to be better support for developers, including better design and evaluation of developers’ tools to create the labels to serve a wider range of developers who span a spectrum of skills.
14
Privacy Label Usability
In the third paper, presented at SOUPS, titled “How Usable Are iOS App Privacy Labels?” researchers investigated lay iPhone users’ awareness, understanding, and perceptions of Apple’s privacy labels. Participants were asked to review the information provided by two food delivery apps and offer feedback about how they interpreted their disclosures.
“The concept of privacy nutrition labels aims to standardize and summarize this information into something users can easily digest,” says Shikun Zhang, a Ph.D. student in the Carnegie Mellon School of Computer Science’s (SCS) Language and Technologies Institute (LTI).
While the study’s participants largely agreed on the importance of making this information available to users,
the findings reveal significant misconceptions and general difficulty in understanding what the IOS privacy labels, in their current form, are really saying.
“There are a number of reasons why people are having trouble understanding these,” says Cranor.
“One is that the terminology is confusing. Apple uses words like ‘tracking,’ and people make assumptions about what that means based on everyday life. However, that definition typically doesn’t match what Apple means when it says tracking.”
Cranor also says users assume that if a privacy label doesn’t mention a specific data type, it isn’t being collected; however, companies are allowed to omit certain information from these labels if they meet requirements in the fine print.
A lack of awareness of the labels’ existence is another major issue.
“Currently, privacy labels are listed so far down in the app descriptions that users rarely scroll far enough to notice them,” says Norman Sadeh, co-director of CMU’s Privacy Engineering Program and head of the Usable Privacy Policy Project
“As a result, few participants reported being aware of their existence, let alone using them when deciding whether to download an app on their phone.”
Sadeh adds that because the labels are only accessible in the app store, users do not benefit from the information they contain when managing other aspects of their privacy, such as controlling the privacy settings (or “permissions”) that determine what sensitive information each app can access.
In order to improve Apple’s iOS privacy nutrition labels, the study’s authors suggest implementing an easier-tounderstand design making definitions and contextualized examples of the data collected more accessible and embedding actions and controls that allow users to manage their privacy settings.
Faculty and students who authored these studies are part of the CyLab Usable Privacy and Security (CUPS) Lab, the Computer Human Interaction: Mobility Privacy Security (CHIMPS) Lab, the Systems, Networking, and Energy Efficiency (Synergy) Lab, and the Language Technologies Institute, at Carnegie Mellon University, along with faculty from the University of Vermont and University of Maryland, Baltimore County.

CYLAB 2021-22 YEAR IN REVIEW | 15
“If the labels are not accurate, they will probably do more harm than good to users.”
Tianshi Li, Ph.D. student, Human-Computer Interaction Institute
CMU HACKING TEAM WINS WINS DEF CON CTF
Carnegie Mellon showed off its computer security talent by winning DEF CON’s Capture the Flag competition, the “Superbowl of hacking,” for the sixth time. The team was composed of CMU students in the Plaid Parliament of Pwning, who joined forces with CMU Alum Professor Robert Xiao’s Maple Bacon (at the University of British Columbia) and CMU Alum startup Theori.io.
Together the teams formed a new squad under the name Maple Mallard Magistrates (MMM), finishing in the top spot on the leaderboard at the end of days one and two, and holding on during the competition’s final day to take this year’s crown.
Carnegie Mellon’s (CMU) Plaid Parliament of Pwning (PPP) won five hacking world championships between 2013 and 2019, the most victories by any team in the competition’s history. Although playing as an expanded team this time around, PPP has now earned its sixth title in the past ten years. Winners each year get 8 “black badges” – the most elite recognition in hacking. PPP now has a total of 48 “black badges”.

“If you’re wondering who the best and brightest security experts in the world are, look no further than the Capture the Flag room at DEF CON,” says David Brumley, an Electrical and Computer Engineering professor at CMU and the faculty advisor to the team.
Over the course of the 72-hour hacking spree, sixteen qualifying teams made up of students, industry workers, and government contractors from around the world attempted to break into each other’s systems,
stealing virtual “flags” and accumulating points while simultaneously trying to protect their own.
“The hacking challenges this year spanned many different formats, exploring different skills and giving us all the chance to both showcase and stretch our abilities,” said Jay Bosamiya, PPP’s team captain, a Ph.D. student in Carnegie Mellon’s Computer Science Department, and member of CMU’s CyLab Security and Privacy Institute.
Carnegie Mellon’s hacking team first formed in 2009 and began competing at DEF CON in 2010. The team previously won the contest in 2013, 2014, 2016, 2017, and 2019.
The victory builds on CMU’s prowess in cybersecurity, a strength shared with the rising generation through picoCTF, a free and robust computer security education program that hosts the world’s largest high school hacking competition.
16
“If you’re wondering who the best and brightest security experts in the world are, look no further than the Capture the Flag room at DEF CON.”
David Brumley, Professor, Electrical and Computer Engineering
CYLAB NAMES 2022 PRESIDENTIAL FELLOWS
Each year, CyLab recognizes high-achieving Ph.D. students pursuing security and/or privacy-related research with a CyLab Presidential Fellowship that covers one year of tuition.
This year’s CyLab Presidential Fellowship recipients are:
Jay Bosamiya
Ph.D. student in the Computer Science Department (CSD)
Advised by Bryan Parno, professor in the Electrical and Computer Engineering (ECE) and Computer Science (CSD) departments
Bosamiya’s research focuses on the intersection of security, software systems, and programming languages. He works to fundamentally improve the security of practical software systems by developing high-assurance solutions, often with provable safety. Bosamiya has taken on a number of different research directions throughout his Ph.D., working to improve the safety of cryptographic primitives, network protocols, software sandboxing, and more.
“My goal is to explore the difficult problems in security that arise from the complexities of real-world software and try to make a significant practical impact.”
Alejandro Cuevas Villalba
Ph.D. student in Societal Computing
Advised by Nicolas Christin, professor in the Software and Societal Systems (S3D) and Engineering and Public Policy (EPP) departments
Cuevas’s research measures various types of phenomena within dark web marketplaces. While he says not all websites on the Tor network (i.e., hidden services) have ill intent, the anonymity of the Tor network enables the commercialization of drugs and other illegal services. Cuevas’s work looks to find new ways to gather and validate data from these services to help provide law enforcement officials and policymakers with valuable knowledge.
“My goal is to understand the nuanced societal impact these marketplaces have by collecting information, designing experiments to test various hypotheses, and drawing insights.”
Ke Wu
Ph.D. student in CSD
Advised by Elaine Shi, associate professor in CSD and ECE
Wu’s research interests lie in the intersection of cryptography and game theory. With cryptocurrency and blockchains now offering quick and easy payments, as well as innovative financial services, Wu says there are strong incentives to explore the security and fairness of these applications to build safe crypto ecosystems.
“My goal is to lay down a solid theoretical background for the fairness of blockchain, and more broadly decentralized applications, so they can be implemented successfully in the real world.”
Sichao (Jeff) Xu
Ph.D. student in CSD
Advised by Pravesh Kothari, assistant professor in CSD



Xu’s research is focused on developing new general-purpose techniques to ascertain algorithmic thresholds for foundational average-case computational problems arising in cryptography and machine learning.
Much of his work has centered around studying sum-of-squares optimization, a powerful general technique that captures almost every tool applied to a wide class of average-case problems.
“I hope to provide rigorous evidence for algorithmic hardness especially in the average-case setting. My daily research has been mainly theoretical, and receiving this award reassures me of the importance and the potential of our theoretical work in making an impact for real life.”
Shikun (Aerin) Zhang
Ph.D. student in the Language Technologies Institute (LTI)
Advised by Norman Sadeh, professor in S3D and co-director of the Privacy Engineering Program
Zhang explores the many challenges associated with empowering people to effectively exercise their right to be informed and control the collection and use of their data. Her current research aims to improve the design and increase the adoption of privacy nutrition labels, providing users with the tools to manage and understand how their data is being utilized.
“I love working on privacy in an academic setting where we have the freedom to ask important questions and develop creative solutions to help users protect their privacy. Privacy is very challenging and requires a lot more research.”
CYLAB 2021-22 YEAR IN REVIEW | 17
SECURITY AND PRIVACY DEGREE PROGRAMS OFFERED AT
CMU
Security and privacy courses and degree programs are offered across many departments at Carnegie Mellon and include courses for both undergraduate and graduate students. We offer courses for computer science and engineering students, as well as courses suitable for policy management students. Both full-time and part-time programs are available, with new programs being added this year.
New this year: Master of Science in Artificial Intelligence Engineering - Information Security
For the first time, Carnegie Mellon College of Engineering’s Information Networking Institute (INI) is offering an Artificial Intelligence Engineering-Information Security Master’s degree that will enable students to gain a deep understanding of AI methods, systems, tool chains and cross-cutting issues, including security, privacy and other ethical, societal and policy challenges. Students will apply AI to the design and implementation of information security systems, including networks, software, and services.
Undergraduate Minor in Information Security, Privacy, and Policy
The Undergraduate Minor in Information Security, Privacy, and Policy offers students from any major an opportunity to take a deep dive into policy issues related to security and privacy. The program is offered jointly by the Software and Societal Systems (S3D) and Engineering and Public Policy (EPP) departments.
Undergraduate Concentration in Security & Privacy
The Security and Privacy concentration for undergraduates is designed to expose both Electrical and Computer Engineering (ECE) and Computer Science students to the key facets of and concerns about computer security and privacy that drive practice, research, and legislation. Upon completing the curriculum, students will be well prepared to continue developing their interests in security or privacy through graduate
One can now browse all of CMU’s security and privacy course offerings in one centralized location on the CyLab website.”

study; to take jobs in security or privacy that will provide further training in applicable areas; and to be informed participants in public and other processes that shape how organizations and society develop to meet new challenges related to computer security or privacy.
Master’s Programs
• INI’s Master of Science in Information Security (MSIS) degree offers a technical focus in security and computer systems, further developed through research opportunities. MSIS students may choose to earn a Cyber Defense concentration, a set of courses that follows guidelines from the U.S. National Security Agency, and a certificate in Cyber Operations (Cyber Ops).
• In INI’s bicoastal Master of Science in Information Technology-Information Security (MSIT-IS) degree, students divide their studies between Pittsburgh and Silicon Valley campuses. During their time in Silicon Valley, students gain unparalleled exposure in the nation’s top tech hub by participating in hackathons, working alongside industry in the practicum project, and networking with leaders in the field.
18
• The Master of Science in Information Technology - Privacy Engineering degree, offered in the School of Computer Science’s Software and Societal Systems department, is a 12 or 16-month graduate program for computer scientists and engineers who wish to pursue careers as privacy engineers or technical privacy managers. A remote part-time option is also available.
• Heinz College’s Master of Science in Information Security Policy and Management provides students with background and insights into general and technical coverage of information security, while equipping them with the analytical methods and management practices necessary to succeed as managers in the field of information security.
Ph.D. Programs
While there is no Ph.D. program at CMU dedicated specifically to security and privacy, there are several programs that enable students to focus on these areas of study. These programs include: School of Computer Science Human-Computer Interaction, Language Technologies, Machine Learning, Software Engineering, Computer Science, Societal Computing College of Engineering Electrical and Computer Engineering, Engineering and Public Policy
CyLab Executive Education Offerings
The rapidly evolving landscape of technology-related security and privacy challenges requires an understanding of the business application and the ability to apply best practices to create solutions. From open enrollment to bespoke training programs, CyLab educators and researchers will empower you and your organization to solve critical challenges.
CyLab offers training in these topics and more:
• Artificial Intelligence (AI), Machine Learning, Security and Privacy
• Behavioral Cybersecurity
• Biometrics and AI
• Blockchain and Cybersecurity
• Cyber Workforce Development
• Darkweb, Security Economics, Crime, and Fraud
• Ethical Issues in AI and Cybersecurity
• Internet of Thins (IoT) Connected Products Security and Privacy
• Privacy Engineering

• Social Cybersecurity and Social Network Analysis
• Software-Defined Security for Next Generation Networks
• Usable Privacy and Security
Interested in learning more about these offerings or designing your own program?
Contact the CyLab partnerships team at partnerships@cylab.cmu.edu to learn more.
New Privacy Engineering Certificate Program
The Carnegie Mellon School of Computer Science now offers a new Privacy Engineering Certificate Program, designed to accommodate students working in industry who cannot afford to leave their jobs. The program is offered entirely online over four weekends and includes a combination of mini-tutorials, class discussions, and hands-on exercises designed to ensure that students develop practical knowledge of all key privacy engineering areas. In the process, students learn about legal and public policy considerations, fundamentals of information security, privacy-by-design concepts, methodologies for engineering privacy in software, usable privacy and security, privacy-enhancing technologies, as well as mathematical and logic foundations of privacy.
For more information about the program, visit privacycert.cs.cmu.edu.
CYLAB 2021-22 YEAR IN REVIEW | 19
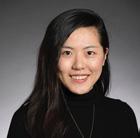
MICHELLE MAZUREK RECEIVES 2022 CYLAB DISTINGUISHED ALUMNI AWARD
Mazurek earned her Ph.D. from Carnegie Mellon’s Department Electrical and Computer Engineering in 2014 after completing her dissertation, “A Tag-Based, Logical Access-Control Framework for Personal File Sharing,” in which she worked to find a balance between the ideal access control policy and what users are willing and able to manage.
Upon graduation, Mazurek headed to the University of Maryland (UMD), where she began her career as an assistant professor. She was promoted to associate professor in 2020 and became the Director of the Maryland Cybersecurity Center the following year.
Michelle Mazurek, a CyLab alum, Director of the Maryland Cybersecurity Center, and Associate Professor at the University of Maryland’s Department of Computer Science and Institute for Advanced Computer Studies, has been selected to receive the 2022 CyLab Distinguished Alumni Award.

“I’m flattered,” says Mazurek. “I wasn’t expecting this, and it means so much because of my immense respect for everyone at CyLab.”
Nominated by her former Ph.D. advisor Lujo Bauer, a professor in Carnegie Mellon’s Department of Electrical and Computer Engineering, Software and Societal Systems (S3D) and CMU Africa, and Nicolas Christin, professor in CMU’s Department of Engineering and Public Policy and S3D, the award recognizes Mazurek’s excellence in usable security and privacy research as well as her professional leadership in the field.
“Michelle was a star Ph.D. student at CMU,” says Bauer. “Since becoming a professor, she has distinguished herself as a researcher, educator, and leader.”
Her human-centered research explores how users make decisions around security and privacy and the factors that lead to those choices. Through these efforts, she’s collaborated with industry partners to develop and improve secure solutions for application programming interfaces (APIs), is developing new access control models for IoT devices, and is currently working to debunk misleading VPN advertisements and understand how misinformation is affecting users’ understanding of security and privacy.
“Most real-world problems in computer security and privacy are arguably caused by systems that don’t account for the needs or capabilities of the humans that build, use, or operate them,” says Christin. “Michelle has been extremely successful as a researcher in this area and is easily on par with the best of her peers.”
Lujo Bauer, Professor in Electrical and Computer Engineering, Software and Societal Systems, and CMU Africa
20
“Michelle was a star Ph.D. student at CMU. Since becoming a professor, she has distinguished herself as a researcher, educator, and leader.”
One of Mazurek’s favorite things about being a professor is the opportunity to mentor students. She says the support she received in CyLab, from advisors Greg Ganger and Lujo Bauer, as well as the rest of the institute’s faculty, gave her the confidence to tackle challenging research topics and present her work in front of peers.

“I received such great support as a grad student. There was no end to the amount of time Lujo and Greg would take to read over my work and make sure I was on track,” says Mazurek.
“I try to do the same for my students, providing as much feedback as possible, giving them confidence in their work, and encouraging them to go out and talk about their research.”
Mazurek is the recipient of a number of awards, including the DARPA Young Faculty Award and NSF’s CAREER Award. She is an author of over 60 publications and has presented her work at some of the field’s most prestigious conferences and symposiums, such as the IEEE Symposium on Security & Privacy, the USENIX Security Symposium, and the ACM Conference on Human Factors in Computing Systems. She is currently program co-chair of the Privacy Enhancing Technologies Symposium (PETS) and was previously program cochair for the Symposium on Usable Privacy and Security (SOUPS).
Michelle Mazurek, CyLab alum and Director of the Maryland Cybersecurity Center
“I had the pleasure of collaborating with Michelle on several usable security projects when she was a Ph.D. student,” said Lorrie Cranor, CyLab director and professor in CMU Engineering’s Department of Engineering and Public Policy and SCS’s Software and Societal Systems department. “I have been delighted to see her leadership in this field and to see what a great mentor she is for her own students.”
In the CyLab Distinguished Alumni Award’s third year, Mazurek joins 2020 winner and Associate Professor in CMU’s Computer Science and Electrical and Computer Engineering departments, Elaine Shi, along with 2021 winner and co-founder/CEO of DataVisor, Yinglian Xie. Mazurek will give a talk as part of CyLab’s seminar series on December 5, 2022, at 12 pm.
CYLAB 2021-22 YEAR IN REVIEW | 21
Mazurek poses for a photo with professors Lujo Bauer, Greg Ganger and Lorrie Cranor before CMU’s 2014 doctoral hooding ceremony.
“I received such great support as a grad student. There was no end to the amount of time Lujo and Greg would take to read over my work and make sure I was on track.”
CYLAB CORE FACULTY
CyLab’s faculty bring security and privacy expertise from across the University. In addition to our core faculty, we have over 80 affiliate faculty.
Alessandro Acquisti
Trustee Professor of IT and Public Policy, Heinz College
Yuvraj Agarwal
Associate professor, Software and Societal Systems (S3D)
Ehab Al-Shaer Distinguished Career Professor, S3D
Lujo Bauer
Professor, Electrical and Computer Engineering (ECE), S3D, CMU-Africa
Shawn Blanton
Associate Department Head of Research and Joseph F. and Nancy Keithley Professor, ECE
Fraser Brown Assistant professor, S3D
David Brumley Professor, ECE
Nicolas Christin
Professor, Engineering and Public Policy (EPP), S3D

Lorrie Cranor
Director and Bosch Distinguished Professor in Security and Privacy Technologies, CyLab, FORE Systems professor, S3D, EPP
Sauvik Das Assistant professor, Human-Computer Interaction Institute
Giulia Fanti Assistant professor, ECE
Matt Fredrikson Assistant professor, CSD, S3D
Virgil Gligor Professor, ECE
Dena Haritos Tsamitis
Director and Barbara Lazarus professor in Information Networking, Information Networking Institute (INI), Founding director, education, training and outreach, CyLab
Hanan Hibshi
Assistant Teaching Professor, INI
Jason Hong Professor, Human-Computer Interaction Institute
Aayush Jain Assistant professor, CSD
Limin Jia Associate research professor, ECE
Aleecia McDonald Assistant director, Privacy Engineering, S3D
Jema Ndibwile
Assistant teaching professor, CMU-Africa
Bryan Parno Associate professor, CSD, ECE
Corina Pasareanu Principal systems scientist, CyLab
Joanne Peca Associate director, associate professor of the practice, INI
Raj Rajkumar George Westinghouse professor, ECE
Norman Sadeh Professor, S3D Co-director, Privacy Engineering Program
Marios Savvides
Bossa Nova Robotics professor of artificial intelligence, ECE, director, CyLab Biometrics Center
Vyas Sekar Tan Family Professor, ECE
Elaine Shi Associate professor, CSD, ECE
Asim Smailagic Research professor, ECE
Patrick Tague Associate teaching professor, INI
Conrad Tucker
Arthur Hamerschlag Career Development Professor, Mechanical Engineering
Riad Wahby Assistant professor, ECE
Osman Yagan Research professor, ECE
Ding Zhao Assistant professor, Mechanical Engineering
Wenting Zheng Assistant professor, CSD
22
2021-2022
BUSINESS OPERATIONS
















CYLAB 2020-21 YEAR IN REVIEW | 23
CYLAB STAFF
Belka Chief Morale Officer
Ashley Bon Business Manager
Brigette Bernagozzi Student Life and Office Coordinator
Toni Fox Research Administrator
Megan Kearns Special Projects Administrator
Brittany Frost Senior Administrative Coordinator
Omen Chief Information
Danyel Kusbit Administrative and Financial Coordinator
Paw-ficer
Chelsea Mendenhall Administrative Coordinator
Tina Yankovich Manager of Personnel and Student Services
Isabelle Glassmith Project Manager
Ryan Gent Associate Director of Partnerships
Michael Lisanti Director of Partnerships
Ryan Noone Communications Manager
Jamie Scanlon Project Administrator
PARTNERSHIPS COMMUNICATIONS
Priyanka Kochhar Administrative Assistant
SUPPORT
FEATURED SPEAKING ENGAGEMENTS
Alessandro Acquisti
• “Where is the Economics of Privacy Going?”



Keynote talk, Conference on the Economics of Information and Communication Technologies. July 2022.
• “Privacy, Social Media, and Con sumer Welfare.” Keynote talk, University of Maryland Workshop On AI & Analytics For Social Good. May 2022
• Keynote Speech. CyberSec&AI Con nected International Conference. November 2021.
Lujo Bauer
• “Attacks on Real-World uses of Machine Learning.” Invited talk, International School on Foundations of Security Analysis and Design. September 2021.

Kathleen Carley

• “Influence, On-line Harms, and Social-cybersecurity.” Sandia In tel Science Seminar Series. March 2022.
• “Dynamic High Dimensional Net works and Emotional Intelligence for Social Cybersecurity.” Invited talk, Cynovative Incorporated. Janu ary 2022
• “Orchestrating Change with Disin formation and Influence.” Keynote talk, IEEE. December 2021
• “Online Terrorism and Insider Threat.” Invited Plenary talk, 7th Workshop on Research for Insider Threats. December 2021.
• “Disinformation in the Digital Envi ronment.” Invited Talk, Progressive. August 2021
Yuejie Chi
• “Understanding the Efficacy of Reinforcement Learning Through a Non-asymptotic Lens.” Keynote talk, IEEE Data Science and Learning Workshop. May 2022.

• “Model-Free Reinforcement Learning: Non-asymptotic Statistical and Computational Guarantees.” Keynote talk, MIT LIDS Student Conference. January 2022.

Nicolas Christin
• “From “Monopoly Money” to billion-dollar derivatives markets.” Invited talk, University College London. June 2021
• “Introducing the billion-dollar crypto currency derivatives trading ecosystem through a deep dive into BitMEX.” Invited talk, Ripple UBRI Connect. October 2021
• “A deep dive in the deep web: Insights from ten years of online anonymous marketplace measure ments.” Keynote talk, Workshop on Attackers and Cyber-Crime Opera tions. September 2021.
• “The Billion-Dollar Cryptocurrency Derivatives Trading Ecosystem.” Invited talk, INFORMS Annual Meeting. October 2021

• “How do home computer users browse the web?” Invited talk, Security and Human Behavior Workshop. May 2022.
Lorrie Cranor
• “Keeping it real and accounting for risk: usable privacy and security study challenges.” Keynote talk, GameSec. October 2021.
• “Designing Useful and Usable Pri vacy Interfaces.” Keynote talk, The 19th ACM International Conference on Mobile Systems. July 2021.
• Public Hearing on Broadband Consumer Labels. U.S. Federal Communica tions Commission. April 2022.
• Smart Homes Virtual Town Hall with PA State Representative Dan Miller. January 2022.
Lori Flynn
• “Machine-Learning Classifiers to Prioritize Static-Analysis Results and Automated Repair.” DoD AI/ML Technical Exchange Meet ing. October 2021.
• “SEI SCAIFE: Automat ed Code Repair (ACR).” DoD/NNSA Software Assurance Community of Practice. September 2021.
Virgil Gligor
• “Formal Methods for Cyber-Physical Sys tems.” Invited talk, Cyber Experimenta tion and Science of Security Workshop. November 2021.
• “How to defend against a remote adversary even on a compromised computer system.” Invited talk, Center for Cyber-Defense and Information Security. March 2022.
24
• “Zero Trust in Zero Trust?” Keynote talk, Semi-Annual conference of Center for Cyber-Defense and Information Security. May 2022.
Hanan Hibshi
• “Why Cybersecurity is Important Today?” Visiting American Professionals Program. November 2021.
Carlee Joe-Wong
• “Optimizing Contributions to Distrib uted, Networked Learning.” Invited talk, Catching, Computing, and Deliv ery in Wireless Networks Workshop. October 2021.
• “Optimizing Contributions to Distributed, Net worked Learning.” Invited talk, Confer ence on Information Sciences and Systems. March 2022
Pravesh Kothari


• “Efficient High-Dimension al Robust Statistics via Algorithmic Certificates of (Anti)-Concentration.” EPL Workshop on Learning: Optimization and Stochas tics. June 2022.
• “Three Lectures on High Dimension al Statistical Estimation via sum-ofsquares.” ARC-ACO Lecture Series, Georgia Tech. February 2022.
Swarun Kumar
• “Towards a City-Scale Battery-Free Inter net.” Invited talk, UC RiversideECE Colloquium. November 2021.
Joanne Peca
• Moderated “CIO Insights: Arconic, MSA Safety, and Foundation Ra diology.” Pittsburgh Technology Council, CIO Insights Series. March 2022.
• “Mobile Digital Contact Tracing for COVID-19: A Review of Some Suc cesses and Failures Beyond the U.S. and Their Data Privacy Implications.” Wireless Telecommunications Sym posium. April 2022.
Sam Perl
• “Dealing with Block chain Technology for Incident Re sponders.” FIRST Regional Sympo sium Latin America and Caribbean. May 2022.
Ryan Riley
• “Password Policies: Do’s and Don’ts in an Interna tionally Diverse Envi ronment.” Community Partner Lecture. March 2022.






Norman Sadeh

• “Privacy as a New Tech Sector.” Key note talk, Cyburgh 2022. May 2022.
• Panelist for NSF Panel on Data Privacy Research in the U.S. 2022 Privacy Symposium. April 2022.
• “Why has Usability Become Priva cy’s Biggest Challenge and What Can We Do About it?” Keynote talk, 9th International Conference on Information Systems, Security and Privacy. February 2022.
• “Security and Privacy: Recording the Strengths and Limitations.” Keynote talk, Bright Internet Global Summit. December 2021.
Mario Savvides
• “Unsupervised Disen tanglement of Lin ear-Encoded Facial Semantics.” Confer ence on Computer Vision and Pattern Recognition. June 2021.


• “Powering Fine-Tuning in Few-Shot Learning: Domain-Agnostic Bias Reduction with Selected Sampling.” AAAI. February 2021.
Tom Scanlon
• “Fundamentals of Deepfakes.” ISC2 Security Congress. October 2021.
• “Three Emerging Areas where AI and ML Enable Data-based Solutions to Human Problems.” Keynote talk, IEEE International Conference on Big Data. December 2021.
Mark Sherman
• “Quantum Implications for Cyberse curity.” Panel presentation, ACT-IAC Emerging Technology and Innova tion Conference. May 2022.
• “Introduction to Recognizing Deep Fakes.” Ai4 Cybersecurity Summit. April 2022.
• “Protect Your Machine Learning Applications from SolarWinds’ At tacks.” AI World Government Conference. October 2021.
• “Carnegie Mellon Uni versity Software Engi neering Institute CERT® Division.” World Learning CyberSec Meeting. June 2021.
CYLAB 2021-22 YEAR IN REVIEW | 25
FEATURED SPEAKING ENGAGEMENTS CONT.
Justine Sherry

• Moderated CMU-Portugal Work shop on 5G Security as part of AIDA Webinar Series. June 2022.
Gregory Touhill
Elaine Shi

• “Foundations of Transaction Fee Mechanism.” ACM Conference on Economics and Computation. July 2022.
• “Foundations of Transaction Fee Mechanism.”
IEEE/IFIP Interna tional Conference on Dependable Systems and Networks. June 2022.
Sri Aravinda Krishnan Thyagarajan
• “Efficient CCA Times Commitments in Class Groups.” ACM CCS. November 2021.
• “Building a Lightning Network on Monero.” MonderoTalk. December 2021.

• “Universal Atomic Swaps: Secure Exchange of Coins Across All Block chains.” Cornell Crypto Seminar. February 2022.
• “Universal Atomic Swaps: Secure Exchange of Coins Across All Block chains.” IEEE Security and Privacy. May 2022.
• “Cryptographic Locks for Scriptless Cryptocurrency Payments.” GI Dis sertationspreis 2021. May 2022.
• “The Old Ways Aren’t Good Enough; Best Practices for Cybersecurity. NSF’s JASON Group. June 2021.
• “Complexity is the Bane of Secu rity.” Invited talk, Air Force Cyber College. September 2021.
• “New frontiers in Securing Crypto Financial Systems.” Billington Cybersecurity Conference. October 2021.
• “The Software Supply Chain Future.” Billington Cybersecurity Conference. October 2021.
• “Zero Trust Security.” National Academies of Science, Engineer ing and Medicine Forum on Cyber Resilience. April 2022.
• “Insider Threat: What’s Next?” United States Secret Service Cyber Incident Response Simulation. April 2022.
Dena Haritos Tsamitis

• “Harnessing the pow er of a diverse and inclusive culture in ICT: Empowering women and spark ing innovation.” Keynote talk, POWER Female Tech Entrepreneurs Forum. June 2021.
• Moderated “Transformational CISO Assembly’s Opening Fireside Chat with Rinki Sethi, VP and CISO of Twitter.” Millennium Alliance Fireside Chat. November 2021.

• “Webcast: Hot Topics in Cybersecu rity.” Panelist, RSA Advisory Board Webinar Series. February 2022.
• “Cultivating Your Personal Board of Advisors.” Panelist, RSA Conference. June 2022.
Carol Woody
• “Enhancing Software and Technology Supply Chain Secu rity.” Panel presen tation, NICE Sympo sium. November 2021.
• “Data Development: Educating, Training, and Fielding a Data-Liter ate Workforce to Deliver Actionable Intelligence.” November 2021.

• “A Deep Dive into Mapping Stan dards to Find any Missing Protec tions.” Panel presentation, C SRM Virtual Forum. October 2021.
• “Acquisition Security Framework (ASF): Integration of Supply chain Risk Management Across the DevSecOps Lifecycle.” 19th Annual Acquisition Research Symposium. May 2022.
• “Managing Supply Chain Complex ity with the Acquisition of Security Framework (ASF).” NDIA Virtual Systems and Mission and Engineer ing Conference. December, 2021.
• “DevSecOps Pipeline for Complex Software-Intensive Systems: Ad dressing Cybersecurity Challenges.” July 2021.
26
FEATURED GRANTS
Alessandro Acquisti
Multiple projects related to the “Welfare Effects of Online Consumer Tracking and Behavioral Advertising.”
Funder: MacArthur Foundation
Lujo Bauer
“Toward Safe, Private, and Secure Home Automation: From Formal Modeling to User Evaluation”
Funder: National Science Foun dation
Other CMU researchers on the grant: Limin Jia “Cybersecurity Assurance for Teams of Computers and Humans”




Funder: Army Research Office’s Multi University Research Initiative
Kathleen Carley
“MURI: Persuasion, Identity, & Morality in Social-Cyber Environments”
Funder: Office of Naval Research
Yuejie Chi
“Towards a Theoretic Foundation of Optimal Deep Graph Learning”
Funder: National Science Foundation
Lorrie Cranor
Serving as the PI for the new Center for Distributed Confidential Computing.
Funder: National Science Foundation
Virgil Gligor


KAIST Graduate Student Research
Funder: Korean Ministry of Science and ICT
“Trustworthy Storage Devices, Assured Information Systems”
Funder: Defense Advanced Research Projects Agency, Small Business Technology Transfer
Hanan Hibshi
Serving as PI for the picoCTF GenCyber Teaching Program
Funder: National Security Agency
Jason Hong
“Harnessing Everyday Users’ Collective Power to Audit Algorithmic Bias in AI Systems”
Funder: Cisco
Other CMU researchers on the grant: Motahhare Eslami, Ken Holstein, Adam Perer, Hong Shen, Nihar Shah
“CIF: Medium: Statistical and Algorithmic Foundations of Efficient Reinforcement Learning”
Funder: National Science Foundation
Limin Jia
“DIVINA: Detecting In jection Vulnerabilities In Node.js Applications”
Funder: Exploratory Project CMU Portugal
Other CMU researchers on the grant: Lujo Bauer
Carlee Joe-Wong
“CNS Core: Medium: Data-Centric Networks for Distributed Learning”
Funder: National Science Foundation

Swarun Kumar


“Energy Centric Wireless Sensor Node System for Smart Farms”
Funder: National Science Foundation
“CNS Core: Small: Dynamic Pricing and Procurement for Distributed Networked Platforms”




Funder: National Science Foundation
Norman Sadeh

“Mobile App Privacy Nutrition Labels in Action FPF Policy Maker.”
Funder: Google - PrivacyRelated Faculty Research Award

Other CMU Researchers on the grant: Lorrie Cranor
Marios Savvides
“AI video analytics including behavioral and scene under standing for safety”
Funder: Oosto, Inc.
“Gift for Professor Marios Savvides’s team for $330,000 to conduct research in AI and computer vision”
Funder: Standar Cognition, Inc.
Sri Aravinda Krishnan Thyagarajan
“RFP-010 Vector commitments”
Funder: Protocol Labs
Dena Haritos Tsamitis
“DoD Cyber Scholarship Program (DoD CySP)”
Funder: Sponsored by the Department of Defense (DoD) and administered by the National Security Agency (NSA)
Osman Yagan
“Secure, Distributed, and Continuous Machine Learn ing in Tactical Networks”

Funder: Office of Naval Research
Other CMU researchers on the grant: Virgil Gligor, Soummya Kar
CYLAB 2021-22 YEAR IN REVIEW | 27
FEATURED RECOGNITIONS
Alessandro Acquisti
Received the Best Senior Editor Award for his work on INFORMS’ journal, Management Science.
Received WISE Best Paper Award for his research “Information Frictions and Heterogeneity in Valuations of Personal Data.”
Finalist for the Best IS Paper in Manage ment Science Award for his work “An Experiment in Hiring Discrimination via Online Social Networks.”
Kathleen Carley
Received Richards Award at the 2021 International Network for Social Network Analysis Conference for her exceptional contribution to network science tools.
Yuejie Chi Named an IEEE Signal Processing Society Distinguished Lecturer.
Lorrie Cranor
Received an Honorary Doctorate in Informatics from the Università della Svizzera italiana.
Won Best Paper Honorable Mention at the 2022 ACM Conference on Human Factors in Computing Systems for “Un derstanding Challenges for Developers to Create Accurate Privacy Nutrition Labels.” Co-Authors include Tianshi Li, Kayla Reiman, Yuvraj Agarwal, Jason Hong.
Earned IAPP SOUPS Privacy Award for her work on “Is it a Concern of Prefer ence? An Investigation into the Ability of Privacy Scales to Capture and Dis tinguish Granular Privacy Constructs.” Co-authors include Jessica Colnago, Alessandro Acquisti, Kate Hazel Jain. Rotem Guttman
Received an Andy Award for his innovative and creative contributions.
Dena
Haritos Tsamitis
Was validated by the National Security Agency and committee of academic peers through 2027, allowing the Infor mation Networking Institute to con tinue participating in federally funded programs designed to strengthen the pipeline of highly skilled cybersecurity professionals who are dedicated to protecting national security.
Jason Hong
Earned the ICWSM Test of Time Award, for his research “Used geotagged social media to understand people’s behaviors in cities.” Co-authors include Justin Cran shaw, Raz Schwartz, Norman Sadeh.
Pravesh Kothari
Received the 2022 Sloan Fellowship, awarded by the Alfred P. Sloan Foun dation, Computational Complexity of Statistical Problems.
Swarun Kumar
Received the 2021 ACM Special Interest Group on Embedded Systems Early Career Researcher Award.
Earned the 2022 International Confer ence on Information Processing (IPSN) in Sensor Networks Best Paper Award for his work “SelfieStick: Towards Earth Imaging from a Low-Cost Ground Mod ule Using LEO Satellites.” Co-authors include Vaibhav Singh, Osman Yagan.
Earned the IPSN 2021 Best Paper Award for his research “Locating Everyday Objects using NFC Textiles.” Co-authors include Jingxian Wang, Junbo Zhang, Ke Li, Chengfeng Pan, Carmel Majidi.
Rohan Padhye
Earned the 2022 Amazon Research Award to support future work in “Coverage-Guided Property-Based testing of Concurrent Programs.
Bryan Parno
Received both the USENIX Distinguished Paper Award and 2nd place prize in the 2022 Internet Defense Prize Competi tion at the 31st USENIX Security Sym posium for the paper “Provably-Safe Multilingual Software Sandboxing using WebAssembly.” Co-authors include Jay Bosamiya and Wen Shih Lim.
Norman Sadeh
Received International AAAI Conference on Web and Social Media’s Test of Time Award for his work “The Livehoods Proj ect: Utilizing Social Media to Understand the Dynamics of a City.”
Marios Savvides
Received the 2022 Inventor of the Year Award from the Pittsburgh Intellectual Property Law Association.
Edward J. Schwartz
Earned a USENIX Distinguished Paper Award for the paper “Augmenting De compiler Output with Learned Variable Names and Types. Co-Authors include Qibin Chen, Jeremy Lacomis, Claire Le Goues, Graham Neubig, and Bogdan Vailescu.
Justine Sherry
Received the University of Washington College of Engineering’s Early Career Diamond Award.
Earned Intel’s Outstanding Researcher Award for her network intrusion detec tion system, Pigasus. Sherry shares the award with James Hoe and Vyas Sekar.
Gregory
Touhill
Named one of Security Magazine’s Top Cybersecurity Leaders of 2022.
Received the Baldridge Foundation Institute for Performance Excellence’s Cybersecurity Leadership Excellence Award.
28
2021-2022 GRADUATED PH.D. STUDENTS
Ainesh Bakshi, Ph.D. in Computer Science Advisors: Pravesh Kothari and David Woodruff
Thesis: Analytic Techniques for Robust Algorithm Design Defense: July, 2022
Sruti Bhagavatula Ph.D. in Computer Science Advisor: Lujo Bauer
Thesis: Measuring and Increasing the Reach of Security Information through Online Media Defense: September, 2021
Jessica Colnago, Ph.D. in Societal Computing Advisor: Lorrie Cranor
Thesis: Exploring the Adoption of Privacy-Protective Behaviors Defense: September, 2021
Justin Cranshaw, Ph.D. in Societal Computing Advisor: Norman Sadeh
Thesis: Depicting Places in Information Systems: Closing the Gap Between Representation and Experience Defense: May, 2022
Cori Faklaris, Ph.D. in Human-Computer Interaction Advisors: Laura Dabbish and Jason Hong
Thesis: Toward a Socio-Cognitive Stage Model of Cybersecurity Behavior Adoption Defense: May, 2022
Aymeric Fromherz Ph.D. in Electrical and Computer Engineering Advisors: Bryan Parno and Corina Pasareanu
Thesis: A Proof-Oriented Approach to Low-Level, High-Assurance Programming Defense: September, 2022
Haojian Jin, Ph.D. in the Human Computer Interaction Institute
Advisors: Jason Hong and Swarun Kumar
Thesis: Human/System Co-Design to Protect Data Privacy Defense: July, 2022
Aymeric Fromherz Ph.D. in Electrical and Computer Engineering Advisors: Bryan Parno and Corina Pasareanu
Thesis: A Proof-Oriented Approach to Low-Level, High-Assurance Programming Defe Defense nse: September, 2022
Jim Graves, Ph.D. in Engineering and Public Policy Advisor: Alessandro Acquisti Thesis: Empirical Analysis of Effects and Perceptions of Cybercrime Defense: December 2021
Hana Habib, Ph.D. in Societal Computing Advisor: Lorrie Cranor Thesis: Evaluating the Usability of Privacy Choice Mechanisms Defense: September, 2021
Dipan Pal, Ph.D. in Electrical and Computer Engineering Advisor: Marios Savvides
Thesis: Neural architectures for invariant representation learning Defense: December, 2021
Yichen Ruan, Ph.D. in Electrical and Computer Engineering Advisor: Carlee Joe-Wong
Thesis: Enabling Collaborative Use of Data for Mobile Devices under Physical and Privacy Constraints Defense: March, 2022
Daniel Smullen, Ph.D. in Software Engineering Advisor: Norman Sadeh Thesis: Informing the Design and Refinement of Privacy and Security Controls Defense: September, 2021
Peter Story, Ph.D. in Societal Computing Advisor: Norman Sadeh
Thesis: Design and Evaluation of Security and Privacy Nudges: From Protection Motivation Theory to Implementation Intentions Defense: August, 2021
Roykrong Sukkerd, Ph.D. in Software Engineering Advisors: David Garlan and Reid Simmons
Thesis: Improving Transparency and Intelligibility of Multi-Objective Probabilistic Planning Defense: April, 2022
Diana Zhang, Ph.D. in Electrical and Computer Engineering Advisor: Swarun Kumar
Thesis: Exploring Novel Sensing Paradigms for Existing Wireless Infrastructure Defense: July, 2021
CYLAB 2021-22 YEAR IN REVIEW | 29
2021-2022 PARTNERS AND SPONSORS SHAPING A SAFER FUTURE






















Carnegie Mellon CyLab is a world leader in innovative thinking and game-changing collaborations that make life more safe, secure and privacy-respecting. We welcome industry and government agencies to join us in what we do best: solving real-life problems through interdisciplinary research and education. From building visibility among students to gaining access to cutting-edge faculty research, upskilling your workforce, and launching new initiatives for social good, CyLab partnership opportunities offer both immediate and far-reaching results.



CyLab’s partners include a wide variety of businesses and institutions, ranging from companies focused on developing advanced technologies to science and government agencies in the USA and international





partner countries. These organizations have access to research and education opportunities that spur industry-wide advancement, propel employees’ skills, and transform promising ideas into marketplace triumphs. Our strategic focus initiatives include rethinking Future Enterprise Security through innovation, creating the knowledge and capabilities to build and implement Secure Blockchain systems “beyond-the-hype,” and improving the cybersecurity of financial systems in emerging economies through CyLab-Africa.
If you’re interested in working together to develop a collaborative plan that benefits both your team and CyLab, please contact Michael Lisanti, Director of Partnerships, at partnerships@cylab.cmu.edu.
30
STRATEGIC LEVEL PARTNERS/SPONSORS
BASE LEVEL PARTNERS
2021-2022 PARTNERS CONFERENCE
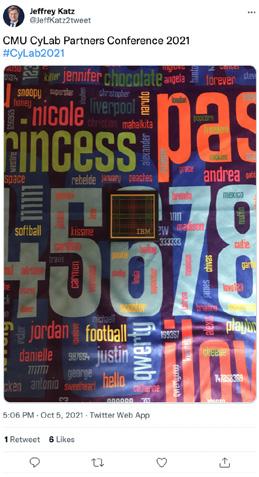




Our 2021 CyLab Partners Conference highlighted the latest research in security and privacy with an interactive forum between faculty, students, and industry. Over 35 faculty and students presented at the two-day event. Attendees received a blanket designed by CyLab Director Lorrie Cranor, featuring the most commonly used passwords revealed during a large data breach.

CYLAB 2021-22 YEAR IN REVIEW | 31
CYLAB NEWS BRIEFS
Read these news stories in their entirety at cylab.cmu.edu/news.
SEP14
CyLab’s Giulia Fanti named a 2021 Intel “Rising Star”
The prestigious award recognizes 10 promising early-career academic researchers who lead some of the most important technology research of our time.
SEP15
CyLab’s Elahe Soltanaghai named a “Rising Star”
The N2Women’s Rising Stars recognizes junior researchers—those with less than 10 years’ experience after Ph.D. com pletion—in the networking and commu nications field who have displayed an exceptional start to their careers.
SEP22
picoCTF impresses at the Women in Cybersecurity Conference
The team behind picoCTF, CyLab’s edu cational platform aiming to bring more people into the field of cybersecurity, made sure its platform was present at the 2021 Women in Cybersecurity conference.
SEP30
CyLab’s Maria Apostolaki named a “Rising Star”
The N2Women’s Rising Stars recognizes junior researchers—those with less than 10 years’ experience after Ph.D. com pletion—in the networking and commu nications field who have displayed an exceptional start to their careers.
OCT06
CyLab’s Jan Hoffmann receives Amazon Research Award
Amazon Research Awards provide fund ing, access to Amazon public datasets, and the use of artificial intelligence and machine learning services and tools.
OCT07
Protect your security and privacy with these tips from CyLab faculty CyLab faculty share tips they recom mend following to stay safe online.
OCT13
Collaboratory to share early research at the Eradicate Hate Global Summit
The Collaboratory Against Hate - Re search and Action Center took part in the inaugural Eradicate Hate Global Summit, a hybrid event focused on ex changing ideas around eradicating hate taking place at the David Lawrence Con vention Center in downtown Pittsburgh.
OCT21
Blair’s problem-solving vision created CMU’s Information Security Office CyLab’s Mary Ann Blair doesn’t wear a badge or a police uniform, but her mis sion is to protect and serve the Carnegie Mellon University community.
OCT26
How does “normal” Internet browsing look today? Now we know.
A CyLab study aims to capture what “normal” Internet browsing looks like to better understand how people are led to download malicious content, and to come up with ways to prevent that from happening.
OCT29
Visual AI company
Oosto partners
with CyLab Biometrics Center
The partnership focuses on early-stage research in object, body, and behavior recognition.
NOV04
Cisco announces strategic partner ship with Carnegie Mellon CyLab Cisco Research, the research arm of multinational tech leader Cisco Systems, has partnered with Carnegie Mellon University CyLab to foster research
collaborations with “the best university researchers in the field.”
NOV09
Are the recent Facebook revelations a “privacy Chernobyl?”
CyLab’s Alessandro Acquisti shares his thoughts around the privacy issues Facebook is facing today.
NOV19
Avoid a privacy nightmare with “Lean Privacy Review”
CyLab researchers have developed a fast, cheap, and easy-to-access method to catch privacy issues early in a sys tem’s development process.
NOV23
Beyond one server: decentralizing secure group messaging
In a study presented at the 2021 ACM CCS conference, Ph.D. student Matthew Weidner defined a new security protocol that could bring this idea of decentral ized secure group messaging to fruition.
DEC14
Eleanor Birrell wants to improve your experience with security and privacy Gaining a better understanding of how to study users in security contexts is exactly what brought Birrell to Carnegie Mellon.
DEC17
Play a video game, learn cybersecurity skills
“Katalyst” was featured in 2021’s pi coCTF, an annual cybersecurity competi tion for middle and high school students created and run by CyLab.
JAN20
CyLab paper receives Privacy Papers for Policymakers Award
The paper captured people’s privacy expectations and preferences in the age of video analytics.
32
JAN27
Why should we use password managers? We asked a security researcher. The most common passwords in 2021 were (1) 123456, (2) 123456789, and (3) qwerty. We sat down with a CyLab researcher to better understand why password managers are such useful tools in securing our accounts, and why more of us should use them.
FEB10
CMU hacking team competes in pentesting world finals
The competition pitted cybersecurity’s brightest students against one another to flex their technical, business, and communication prowess.
FEB15
CyLab faculty named Intel’s 2021 Outstanding Researchers
CyLab faculty Justine Sherry, Vyas Sekar, and James Hoe have been selected among the winners of Intel’s 2021 Out standing Researcher Award.
FEB22
Understanding the evolutionary roots of privacy Research co-authored by CyLab experts in the journal Science explores the concept of privacy not as a modern anomaly, but as a concept that spans time and space, social class, and degree of technological sophistication.
FEB28
Algorand Foundation becomes strategic partner
The Foundation will serve as a founding sponsor of Carnegie Mellon CyLab’s Secure Blockchain Initiative.
MAR03
The (un)importance of online interview modes for security and privacy studies
In a rigorous study published in the journal PLOS ONE, a team of CyLab researchers show that that there is little evidence to suggest that interviews with crowd workers about sensitive topics are significantly impacted by the chosen online interview mode.
MAR08 World’s largest online hacking competition
picoCTF, the annual free online cyber security competition run by hacking experts in Carnegie Mellon’s CyLab, aims to introduce young minds across the nation to the world of cybersecurity and to build a pipeline of talent to a much-needed cyber workforce.
MAR17
Crypto.com becomes strategic partner
The company will serve as a founding sponsor of Carnegie Mellon CyLab’s Secure Blockchain Initiative.
MAR25
CyLab researchers awarded AI security funding
CyLab’s Giulia Fanti, Corina Pasareanu, and Vyas Sekar were awarded research funding from the C3.ai Digital Transfor mation Institute.
APR06
VMware to sponsor CyLab’s Future Enterprise Security Initiative
VMware has become a founding sponsor of CyLab’s Future Enterprise Security Initiative, which has a mission of rethinking security across enterprise ecosystems through innovations in artificial intelligence, computer sci ence, engineering, and human factors research.
APR08
Ripple becomes a founding sponsor of the CMU Secure Blockchain Initiative
The announcement comes three years after CMU announced a partnership with Ripple’s University Blockchain Research Initiative.
APR21
NSF awards CMU researchers $3M to accelerate next-gen networking, computing
CyLab researchers will use nearly $3 million in funding from the Nation al Science Foundation (NSF) to help develop intelligent, resilient and reliable next-generation (NextG) networks..
MAY03
Aryaka becomes strategic partner
The company has become a founding sponsor of Carnegie Mellon’s Future Enterprise Security Initiative.
MAY09
Lorrie Cranor receives honorary doc torate
Cranor received the honorary degree “for her relentless pursuit of making privacy and security usable...”
MAY11
Microsoft expands its strategic partnership
Microsoft expanded its partnership with Carnegie Mellon University CyLab in becoming a founding sponsor of CyLab’s Future Enterprise Security Initiative.
JUN08
Two of three IEEE Test of Time Awards go to CyLab researchers
At the 2022 IEEE Symposium on Security and Privacy, two of three Test of Time Awards—among the most prestigious awards presented—were given to CyLab researchers.
CYLAB 2021-22 YEAR IN REVIEW | 33
JUN16
CyLab student studying cryptography receives INI award
Nikhil Lalit Vanjani received an Outstanding Student Service Award for a Research Assistant at the 2022 INI commencement.
JUN22
CyLab Ph.D. student receives honor for “highest quality” thesis
CyLab’s Aymeric Fromherz was recog nized with an A.G. Milnes Award for his Ph.D. thesis work “judged to be of the highest quality and which has had, or is likely to have, significant impact in his or her field.”
JUN24
CyLab’s Giulia Fanti receives 2022 Rising Star Award
ACM SIGMETRICS named CyLab’s Giulia Fanti the recipient of the 2022 Rising Star Research Award for her “fundamental and interdisciplinary research on scalable systems for data sharing that ensures security and privacy.”
JUL06
Researchers propose ephemeral approach to IoT privacy
A team of CyLab researchers has proposed a new model of IoT ownership to help alleviate issues of privacy.
JUL12
CyLab research leads to blockchain paradigm shift
Research out of CyLab lays the scientific foundation for studying decentralized mechanism design.
JUL21
Usable but not understood: a case study on chatbots and HIPAA
Achieving consent online is a challenge. Throw that into the context of healthcare, and it becomes enormously challenging.
A study by CyLab’s Sarah Pearman takes a deep dive.
JUL26
Study reveals iOS privacy labels miss the mark
A study from researchers at Carnegie Mellon’s Security and Privacy Institute shows users find Apple’s iOS privacy labels confusing, difficult to find.
AUG04
Algorand Foundation selects Carnegie Mellon to join ACE Program
CMU has been selected to as one of ten global winners to join its Algorand Center of Excellence (ACE) Program.
AUG05
CyLab well represented at SOUPS 2022
There was no shortage of Carnegie Mellon student and faculty participating at the 2022 Symposium on Usable Privacy and Security.
AUG09
iPhone security compromises prove difficult to detect
Mobile phones can be abused to enable stalking through methods like location tracking, account compromise and remote surveillance. While experts can help victims detect and recover from this type of technology abuse, researchers at CyLab say typical users aren’t equipped to identify and resolve these issues on their own.
AUG24
CMU hosts public hearing on cybersecurity and blockchain
Government officials, academics, and industry leaders gathered at Mill 19 to discuss the impact of cybersecurity and blockchain on government operations.
AUG26
Eliminating algorithmic complexity attacks
Ph.D. student Nirav Atre has developed an algorithm guaranteed to protect network systems against algorithmic complexity attacks.
AUG30
picoCTF celebrates competition winners at annual award ceremony
The 2022 event saw players from all 50 U.S. states and 169 countries who worked through 65 increasingly difficult challenges as they looked to take home this year’s crown.
SEP08
Transformational growth at CMU-Africa
A historic partnership with the Master card Foundation will expand the engi neering and technology research and entrepreneurship programs at CMUAfrica, helping to strengthen Africa’s technology, innovation, and research ecosystem.
SEP09
Study reveals third-party tracking abundant on abortion clinic sites
A study published in JAMA Internal Medicine reveals over 99 percent of abortion clinic web pages include third-party tracking, putting the privacy of those visiting these websites at risk.
SEP15
New model provides smishing protection in Swahili
Research about smishing (SMS phishing) from CMU-Africa and the Nelson Mandela Institute of Science and Technology was recently published in IEEE Access.
SEP27
A new initiative to drive financial inclusion in Africa
Funding from the Bill and Melinda Gates Foundation will bring together academia, government, and the private sector to make digital financial services more accessible.
34 CYLAB NEWS BRIEFS CONT.
CYLAB MEDIA MENTIONS
8.7.2021 On cookies:
“When advertisements became popular, especially with Google and all these ad markets, then there was more momentum toward finding and tracking data because the advertising had to be personalized.”
Rahul Telang, Trustee Professor and Ph.D. Program Chair, Heinz College


11.2.2021 On facial recognition: “Once your data is collected, you as the data subject effectively lose the ability to control its usage.”
Alessandro Acquisti, Trustee Professor of IT and Public Policy, Heinz College

5.31.2022 On privacy policies: “What’s most important to show to users is the stuff that will surprise them—the stuff that’s different than what every other company does.”
Lorrie Cranor, Director and Bosch Distinguished Professor in Security and Privacy Technologies, CyLab; FORE Systems Professor of Computer Science and of Engineering and Public Policy
10.5.2021 On Facebook outage:
“When I typed in the URL, I got an error that said NXDOMAIN, and that was the DNS telling me, ‘I don’t know what that domain name is, it doesn’t point to any address for me.”
Justine Sherry, Assistant Professor, Computer Science Department







11.1.2021 On dark web market:






“Anonymity always decreases with time. Just one slip up and you’re done. If your IP address is captured once, it is a disaster. And so, there is a perfectly rational behavior, which is to quit while you’re ahead.”
Nicolas Christin, Professor, Engineering and Public Policy, Software and Societal Systems
2.17.2022 On field of cybersecurity:
“The key distinguishing feature of cybersecurity is that we worry about computer systems performing as they should even when they are under attack by an adversary who tries to get at our data or break down our systems.”
Lujo Bauer, Professor, Electrical and Computer Engineering, Software and Societal Systems, CMU-Africa
6.7.2022 On social media bots: “I want to stress that the bots usually aren’t the source of the misinformation, they are usually spreading the information published by other websites.”
Kathleen Carley, Professor of Computation, Organizations, and Society, Software and Societal Systems
4.27.2022 On cybersecurity in Africa:
“As we are moving to include more people into the financial inclusion net, we should be mindful of the things that can hinder the successes of it such as cyber security attacks.”
Assane Gueye, Assistant Teaching Professor, CMU Africa

6.24.2022 On privacy post Roe v. Wade

“Your data could actually be all over the network at this point. And it’s really hard to track what’s going on.”
Jason Hong, Professor, HumanComputer Interaction Institute
CYLAB 2021-22 YEAR IN REVIEW | 35

CARNEGIE MELLON IS TOP RANKED , AGAIN! UNDERGRADUATE CYBERSECURITY PROGRAM 2021 • 2022 • 2023 Ranked #1 by US News and World Report for 3rd year in a row #






 Director and Bosch Distinguished Professor in Security and Privacy Technologies, CyLab FORE Systems Professor of Computer Science and of Engineering & Public Policy
Director and Bosch Distinguished Professor in Security and Privacy Technologies, CyLab FORE Systems Professor of Computer Science and of Engineering & Public Policy